WORM_FEODO.A
Windows 2000, XP, Server 2003


Threat Type: Worm
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
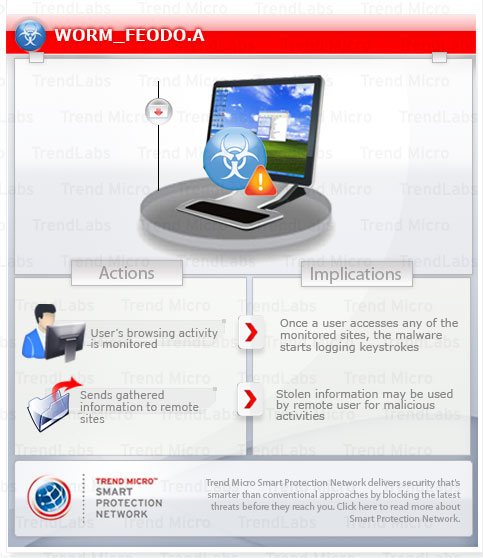
Trend Micro has flagged this worm as noteworthy due to the increased potential for damage, propagation, or both, that it possesses. Specifically, this worm is capable of monitoring bank-related sites and sending gathered information to its command and control (C&C) server.
To get a one-glance comprehensive view of the behavior of this Worm, refer to the Threat Diagram shown below.
This worm may be downloaded by other malware/grayware/spyware from remote sites. It may be unknowingly downloaded by a user while visiting malicious websites.
It drops copies of itself in all removable drives. It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
It attempts to steal information, such as user names and passwords, used when logging into certain banking or finance-related websites.
It deletes itself after execution.
TECHNICAL DETAILS
Arrival Details
This worm may be downloaded by other malware/grayware/spyware from remote sites.
It may be unknowingly downloaded by a user while visiting malicious websites.
Installation
This worm drops the following copies of itself into the affected system:
- %System%\svrwsc.exe
(Note: %System% is the Windows system folder, which is usually C:\Windows\System on Windows 98 and ME, C:\WINNT\System32 on Windows NT and 2000, or C:\Windows\System32 on Windows XP and Server 2003.)
It is injected into the following processes running in memory:
- Explorer.exe
Autostart Technique
This worm registers itself as a system service to ensure its automatic execution at every system startup by adding the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SvrWsc
Type = 10
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SvrWsc
Start = 2
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SvrWsc
ErrorControl = 0
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SvrWsc
ImagePath = %System%\svrwsc.exe
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SvrWsc
DisplayName = Windows Security Center Service
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SvrWsc
ObjectName = LocalSystem
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SvrWsc
Description = The service provides COM APIs for independent software vendors to register and record the state of their products to the Security Center service.
Other System Modifications
This worm adds the following registry entries as part of its installation routine:
HKEY_USERS\.DEFAULT\Software\
Microsoft\Windows\CurrentVersion\
Internet Settings
ProxyEnable = 0
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
SvrWsc = ""
It adds the following registry keys as part of its installation routine:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
DirectX\MSA
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
DirectX\MSB
Propagation
This worm drops copies of itself in all removable drives.
It drops an AUTORUN.INF file to automatically execute the copies it drops when a user accesses the drives of an affected system.
The said .INF file contains the following strings:
[AutoRun]
open={random folder name}\{random file name}.exe
shell\Open\Command={random folder name}\{random file name}.exe
shell\Open\Default=1
shell\Explore\Command={random folder name}\{random file name}.exe
shell\Autoplay\command={random folder name}\{random file name}.exe
Information Theft
This worm monitors the Internet Explorer (IE) activities of the affected system, specifically the address bar or title bar. It recreates a legitimate website with a spoofed login page if a user visits banking sites with the following strings in the address bar or title bar:
- */Common/SignOn/Start.asp*
- */inets/*
- */inets/Login*
- */sbuser/*
- *ACH*
- *PassMarkRecognized.aspx*
- *addisonavenue.com*
- *bankonline.umpquabank.com*
- *business.macu.com*
- *businesslogin*
- *bxs.com*
- *cashmgt.firsttennessee*
- *ceowt.wellsfargo.com*
- *chsec.wellsfargo.com*
- *cibng.ibanking-services.com*
- *cnbank.com*
- *cnbsec1.cnbank.com*
- *comerica.com*
- *ebanking.eurobank.gr*
- *ebc_ebc1961*
- *efirstbank*
- *enterprise2.openbank.com*
- *express.53.com*
- *fundsxpress.com*
- *global1.onlinebank.com*
- *hbcash.exe*
- *hillsbank*
- *homebank.nbg.gr*
- *hsbc*
- *ibanking-services.com*
- *itreasury.regions.com*
- *metrobankdirect.com*
- *mystreetscape*
- *mystreetscape.com*
- *nsbank.com*
- *online.ccbank.bg*
- *otm.suntrust.com*
- *scottvalleybank*
- *secure.ally.com*
- *secure.fundsxpress.com*
- *securentry*
- *securentry.calbanktrust.com*
- *servlet/teller*
- *site-secure.com*
- *springbankconnect.com*
- *telepc.net*
- *treasurypathways.com*
- *umpquabank.com*
- *webcash*
- *webexpress*
- *wellsoffice.wellsfargo.com*
- *wire*
- *www2.firstbanks.com/olb*
It attempts to steal information from the following banks and/or other financial institutions:
- Addison Avenue
- BXS
- Business Macu
- CCBank
- CNBank
- California Bank & Trust
- Comerica
- Efirst Bank
- Eurobank
- Fifth Third
- First Tennessee
- Funds Express
- HSBC
- Hillsbank
- Metrobank Direct
- Mystreetscape
- NSbank
- Open Bank
- Openbank
- Scottvalley Bank
- Springbank Connect
- Suntrust
- Umpquabank
- Wells Fargo
- iTreasury
Stolen Information
This worm sends the gathered information via HTTP POST to the following URL:
- http://{BLOCKED}m.ru/wbc/avg/index.php
Other Details
This worm deletes itself after execution.
Variant Information
This worm has the following MD5 hashes:
- 557597074df3d3ce0e1674285ef19732
It has the following SHA1 hashes:
- ec2856823201125ab90a3ae38ef925b0d06c2056
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Restart in Safe Mode
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- SvrWsc =
- SvrWsc =
- In HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings
- ProxyEnable = 0
- ProxyEnable = 0
Step 4
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectX
- MSA
- MSA
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectX
- MSB
- MSB
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services
- SvrWsc
- SvrWsc
Step 5
Search and delete AUTORUN.INF files created by WORM_FEODO.A that contain these strings
[AutoRun]
open={random folder name}\{random file name}.exe
shell\Open\Command={random folder name}\{random file name}.exe
shell\Open\Default=1
shell\Explore\Command={random folder name}\{random file name}.exe
shell\Autoplay\command={random folder name}\{random file name}.exe
Step 6
Scan your computer with your Trend Micro product to delete files detected as WORM_FEODO.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



