WORM_DORKBOT.XYT
Trojan:Win32/Dynamer!ac (Microsoft), a variant of Win32/AutoRn.IRCBot.JG worm (ESET)
Windows 2000, Windows Server 2003, Windows XP (32-bit, 64-bit), Windows Vista (32-bit, 64-bit), Windows 7 (32-bit, 64-bit)


Threat Type: Worm
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This worm arrives as an attachment to email messages spammed by other malware/grayware or malicious users. It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
However, as of this writing, the said sites are inaccessible. It deletes the initially executed copy of itself.
TECHNICAL DETAILS
Arrival Details
This worm arrives as an attachment to email messages spammed by other malware/grayware or malicious users.
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This worm drops the following copies of itself into the affected system and executes them:
- %User Profile%\M-90480246729040580245\winsvc.exe
(Note: %User Profile% is the current user's profile folder, which is usually C:\Documents and Settings\{user name} on Windows 2000, XP, and Server 2003, or C:\Users\{user name} on Windows Vista and 7.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Knot
Autostart Technique
This worm adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
Microsoft Windows Driver = "%User Profile%\M-90480246729040580245\winsvc.exe"
Other System Modifications
This worm creates the following registry entry(ies) to bypass Windows Firewall:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
Services\SharedAccess\Parameters\
FirewallPolicy\StandardProfile\AuthorizedApplications\
List
%User Profile%\M-1-25-8784-4125-7572\winsvc.exe = "%User Profile%\M-1-25-8784-4125-7572\winsvc.exe:*:Enabled:Microsoft Windows Driver"
Download Routine
This worm accesses the following websites to download files:
- http://{BLOCKED}x.su/icons/small/.x/l.exe
It then executes the downloaded files. As a result, malicious routines of the downloaded files are exhibited on the affected system.
Other Details
This worm connects to the following URL(s) to get the affected system's IP address:
- http://api.wipmania.com
It does the following:
- sends copies of itself via IM applications:
- Yahoo Messenger
- Skype
However, as of this writing, the said sites are inaccessible.
It deletes the initially executed copy of itself
NOTES:
It terminates itself if the following libraries are found loaded on the affected computer:
- sbiedll.dll
- sbiedllx.dll
It terminates itself if found running in a virtual environment by checking the following strings:
- qemu
- virtual
- vmware
It connects to the following site to report its infection:
- http://{BLOCKED}x.su/icons/small/.x/bot.php?n=1
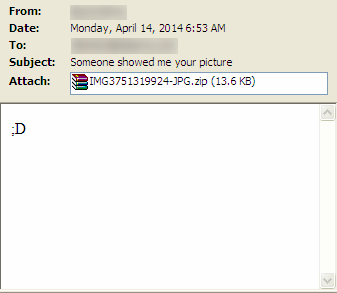
This worm sends email messages containing a copy of itself named as IMG{random number}-JPG.scr, which is contained in an attachment IMG{random number}-JPG.zip:
The worm accesses the following site to download list of email addresses:
- http://{BLOCKED}x.su/icons/small/.x/{number}.txt
The downloaded list is temporarily stored in the following location:
- %User Temp%\{random number}.jpg
The email it sends out has the following characteristics:
- It uses the combination of the following strings as display names:
- Jenkins
- Coleman
- Henderson
- Ross
- Barnes
- Wood
- Bennett
- Price
- Sanders
- Kelly
- Brooks
- Watson
- James
- Ramirez
- Gray
- Peterson
- Torres
- Ward
- Howard
- Cox
- Richardson
- Cooper
- Rivera
- Bailey
- Murphy
- Bell
- Morgan
- Cook
- Reed
- Rogers
- Morris
- Sanchez
- Stewart
- Collins
- Edwards
- Evans
- Parker
- Campbell
- Phillips
- Turner
- Roberts
- Perez
- Mitchell
- Carter
- Nelson
- Gonzalez
- Baker
- Adams
- Green
- Scott
- Hill
- Lopez
- Wright
- King
- Hernandez
- Young
- Allen
- Hall
- Walker
- Lee
- Lewis
- Rodriguez
- Clark
- Robinson
- Martinez
- Garcia
- Thompson
- Martin
- Harris
- White
- Jackson
- Thomas
- Anderson
- Moore
- Wilson
- Miller
- Davis
- Brown
- Jones
- Williams
- Johnson
- Smith
- Terra
- Teri
- Teresa
- Terence
- Teddy
- Ted
- Taylor
- Tasha
- Tara
- Tanya
- Tanner
- Tanisha
- Tania
- Ines
- Ina
- Imogene
- Imelda
- Ilene
- Ila
- Ignacio
- Ida
- Ian
- Hunter
- Hung
- Humberto
- Hugo
- Hugh
- Delia
- Delbert
- Deirdre
- Deidre
- Deena
- Dee
- Debra
- Deborah
- Debora
- Debbie
- Deanne
- Deanna
- Deann
- Brady
- Bradly
- Bradley
- Bradford
- Brad
- Boyd
- Boris
- Booker
- Bonnie
- Bonita
- Bobby
- Bobbie
- Bobbi
- Bob
- Blanche
- Blanca
- Blake
- Blair
- Blaine
- Billy
- Billie
- Bill
- Bianca
- Beverly
- Beverley
- Beulah
- Aisha
- Aimee
- Aileen
- Aida
- Ahmed
- Ahmad
- Agustin
- Agnes
- Adrienne
- Adriana
- Adrian
- Adolph
- Adolfo
- Gordon
- Gonzalo
- Goldie
- Gloria
- Glenna
- Glenn
- Glenda
- Glen
- Gladys
- Giovanni
- Gino
- Ginger
- Gina
- Gilda
- It uses any of the following subjects:
- Please rate
- Do you think she is pretty?
- Do you know her?
- Do you know him?
- Do you know this person?
- Unbelievable
- Seen this?!
- Have you seen this?!
- I love this picture!
- Pretty or ugly?
- You got busted
- Take a look at my new photo
- Keep it secret
- Only For You
- You will be shocked!
- Private photo
- My private photo for you
- Is this really your photo?
- Seen this picture?
- Your opinion needed
- Do you think I'm 'pretty or ugly?
- Please rate my picture
- Do you think I'm attractive?
- Check out this picture
- You look terrible on this photo
- Shame on you
- Your picture is all over the web
- I found this photo of you
- Someone told me it's your picture
- Should I upload this picture on facebook?
- What you think of this picture?
- Take a look at my new picture please
- You should take a look at this picture
- You look so beautiful on this picture
- I love your picture!
- Someone showed me your picture
- This is the funniest picture ever!
- Tell me what you think of this picture
- Photo of you?
- Picture of you?
- Is this you?
- The body contains any of the following messages:
- hahaha
- ;)
- :D
- :p
- :)
- LOL
- ;D
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Restart in Safe Mode
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- Microsoft Windows Driver = "%User Profile%\M-90480246729040580245\winsvc.exe"
- Microsoft Windows Driver = "%User Profile%\M-90480246729040580245\winsvc.exe"
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List
- %User Profile%\M-1-25-8784-4125-7572\winsvc.exe = "%User Profile%\M-1-25-8784-4125-7572\winsvc.exe:*:Enabled:Microsoft Windows Driver"
- %User Profile%\M-1-25-8784-4125-7572\winsvc.exe = "%User Profile%\M-1-25-8784-4125-7572\winsvc.exe:*:Enabled:Microsoft Windows Driver"
Step 5
Restart in normal mode and scan your computer with your Trend Micro product for files detected as WORM_DORKBOT.XYT. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

