W2KM_BARTALEX.EU
W97M/Downloader.adx(McAfee), Troj/DocDl-EU(Sophos),
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This is macro-based malware that employed a bogus Air Canada e-ticket with an attached .DOC file. The said .DOC file attachment pretends to contain airline information. Once users open this .DOC file, it leads to a document with a malicious macro.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
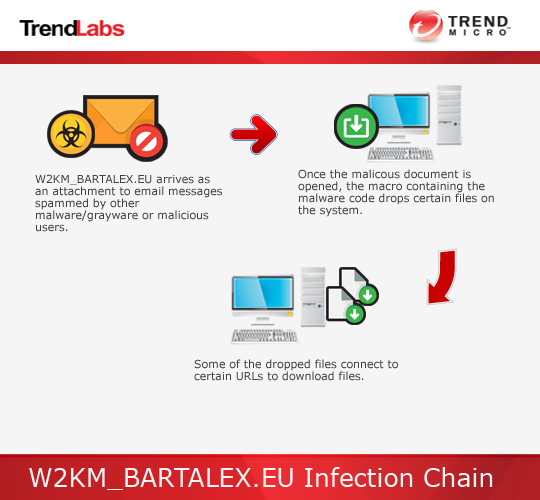
This Trojan arrives as an attachment to email messages mass-mailed by other malware/grayware or malicious users.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives as an attachment to email messages mass-mailed by other malware/grayware or malicious users.
NOTES:
Once the malicous document is opened, the macro which contains the malware code executes and drops the following files:
- For OS versions XP and below:
- %Temp%\adobeacd-update.bat
- %Temp%\adobeacd-updatexp.vbs
- For OS versions Vista and above:
- %User Temp%\adobeacd-update.vbs
- %User Temp%\adobeacd-update.bat
- %User Temp%\adobeacd-update.ps1
The file adobeacd-updatexp.vbs and adobeacd-update.ps1 accesses the following links to download files:
- http://{BLOCKED}c.su/5229109.png (For OS Version XP and below)
- http://{BLOCKED}c.su/5220917.png (For OS Version Vista and above)
- http://{BLOCKED}.{BLOCKED}.131.73/ca/file.pif
The malware saves the file using the following filename:
- %Temp%\444.exe - For OS Verion XP and below (Detected as TROJ_HANCITOR.VVQB)
- %User Temp%\444.exe - For OS Verion Vista and above (Detected as TROJ_HANCITOR.VVQB)
- %User Temp%\444.jpg - For OS Version Vista and above
For OS versions XP and below, the file adobeacd-update.bat executes adobeacd-updatexp.vbs and the downloaded file %Temp\444.exe%. It also deletes itself after execution.
For OS versions Vista and above, the file adobeacd-update.bat executes adobeacd-update.vbs, which in turn, executes adobeacd-update.ps1. The file adobeacd-update.ps1 ensures that the downloaded file is executed and deletes all dropped files after execution.
SOLUTION
Step 1
Remove the malware/grayware file that dropped/downloaded W2KM_BARTALEX.EU. (Note: Please skip this step if the threat(s) listed below have already been removed.)
-
TROJ_HANCITOR.VVQB
Step 2
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 3
Search and delete these components
- %Temp%\adobeacd-update.bat (For OS Version XP and below)
- %Temp%\adobeacd-updatexp.vbs (For OS Version XP and below)
- %User Temp%\adobeacd-update.vbs (For OS Version Vista and above)
- %User Temp%\adobeacd-update.bat (For OS Version Vista and above)
- %User Temp%\adobeacd-update.ps1 (For OS Version Vista and above)
Step 4
Scan your computer with your Trend Micro product to delete files detected as W2KM_BARTALEX.EU. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check the following Trend Micro Support pages for more information:
Did this description help? Tell us how we did.


