TSPY_BANKER.PPI
Windows 2000, XP, Server 2003


Threat Type: Spyware
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It attempts to steal information, such as user names and passwords, used when logging into certain banking or finance-related websites.
TECHNICAL DETAILS
Arrival Details
This spyware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Autostart Technique
This spyware adds the following registry entries to enable its automatic execution at every system startup:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
{malware file name} = {malware path and file name}
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
{malware file name} = {malware path and file name}
Information Theft
This spyware monitors the Internet Explorer (IE) activities of the affected system, specifically the address bar. It recreates a legitimate website with a spoofed login page if a user visits banking sites with the following strings in the address bar and/or title bar:
- https://www.bradesconetempresa.com.br/ne/iniciasessao.asp
It attempts to steal information from the following banks and/or other financial institutions:
- Banco Bradesco
Other Details
Based on analysis of the codes, it has the following capabilities:
- Redirects users to http://{BLOCKED}caosite.com/ne/iniciasessao.htm when the user visits the website https://www.bradesconetempresa.com.br/ne/iniciasessao.asp
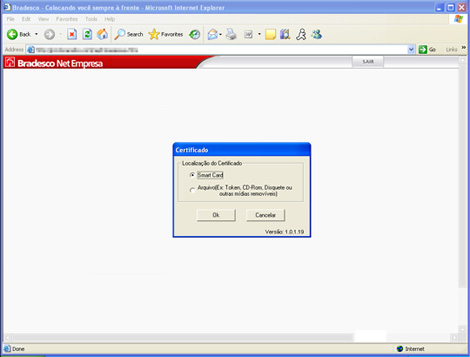
- Displays a window asking for the location of the digital signature file (*.crt).
- It asks for the user's personal password which is needed to open the certificate and the 6-digit bank token password.
It displays the following message boxes:
Variant Information
This spyware has the following MD5 hashes:
- 26d4e31b20cf9397561ce88bf1e83d5b
It has the following SHA1 hashes:
- 7f1cecb49d15e799294aac440a665099ff9ac2bd
SOLUTION
Step 1
For Windows XP and Windows Server 2003 users, before doing any scans, please make sure you disable System Restore to allow full scanning of your computer.
Step 2
Identify and terminate files detected as TSPY_BANKER.PPI
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 3
Delete this registry value
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- {malware file name} = {malware path and file name}
- {malware file name} = {malware path and file name}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- {malware file name} = {malware path and file name}
- {malware file name} = {malware path and file name}
Step 4
Scan your computer with your Trend Micro product to delete files detected as TSPY_BANKER.PPI. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.

