RANSOM_BADRABBIT.A
Ransom:Win32/BadRabbit (MICROSOFT); W32/Diskcoder.D!tr.ransom (FORTINET)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This ransomware, also known as Bad Rabbit, reportedly spread to networks of some high profile companies located in Ukraine and Russia. It spreads via network shares. It also modifies the Master Boot Record (MBR) of an affected system.
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It encrypts files with specific file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
- {Drive letter}:\Readme.txt ← Ransom note
- %All Users Profile%\dispci.exe ← overwrites MBR and decrypts files. Drops in %All Users Profile% if McAfee products are found.
- %Windows%\cscc.dat ← Normal file used by dispci.exe.
- %Windows%\dispci.exe ← overwrites MBR and decrypts files. Drops in %Windows% if no McAfee products are found.
- %Windows%\{random hex value}.tmp ← Mimikatz, gathers username and password. Deleted afterwards.
- %Desktop%\DECRYPT.lnk ← Shortcut file for %Windows%\dispci.exe
- %All Users Profile%\DECRYPT.lnk ← Shortcut file for %Windows%\dispci.exe
(Note: %All Users Profile% is the All Users folder, where it usually is C:\Documents and Settings\All Users on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\ProgramData on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.. %Windows% is the Windows folder, where it usually is C:\Windows on all Windows operating system versions.. %Desktop% is the desktop folder, where it usually is C:\Documents and Settings\{user name}\Desktop in Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\Desktop in Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It drops and executes the following files:
- %Windows%\infpub.dat ← Deleted afterwards.
(Note: %Windows% is the Windows folder, where it usually is C:\Windows on all Windows operating system versions.)
Other System Modifications
This Ransomware adds the following registry entries:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\cscc
DependOnService = "FltMgr"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\cscc
DisplayName = "Windows Client Side Caching DDriver"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\cscc
ErrorControl = 3
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\cscc
Group = "Filter"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\cscc
ImagePath = "cscc.dat"
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\cscc
Start = 0
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\
services\cscc
Type = 1
Information Theft
This Ransomware gathers the following data:
- Username
- Password
Other Details
This Ransomware does the following:
- This Ransomware encrypts files.
- It does not rename the encrypted files.
- It will instead append a file marker string "encrypted" to the end of every encrypted file.
- This ransomware overwrites the affected system's Master Boot Record (MBR).
- Executes the following command:
- %System%\rundll32.exe %Windows%\infpub.dat,#1 15
- "%Windows%\{random hex value}.tmp" \.\pipe\{GUID}
- This ransomware adds the following scheduled tasks:
- rhaegal - Executes dispci.exe on system startup
- drogon - Restarts the system after 18 minutes of the malware execution.
- viserion_{number} - Restarts the system at a certain amount of time.
- This ransomware is capable spreading via the SMB file sharing protocol.
- It attempts to brute force any administrative shares it finds.
- If successful it drops a copy of itself into these shares.
- If these bruteforce attacks fails, it uses an exploit targeting the EternalRomance SMB vulnerability resolved in MS17-010.
- This ransomware is capable of disk encryption.
Ransomware Routine
This Ransomware encrypts files with the following extensions:
- .3ds
- .7z
- .accdb
- .ai
- .asm
- .asp
- .aspx
- .avhd
- .back
- .bak
- .bmp
- .brw
- .c
- .cab
- .cc
- .cer
- .cfg
- .conf
- .cpp
- .crt
- .cs
- .ctl
- .cxx
- .dbf
- .der
- .dib
- .disk
- .djvu
- .doc
- .docx
- .dwg
- .eml
- .fdb
- .gz
- .h
- .hdd
- .hpp
- .hxx
- .iso
- .java
- .jfif
- .jpe
- .jpeg
- .jpg
- .js
- .kdbx
- .key
- .mdb
- .msg
- .nrg
- .odc
- .odf
- .odg
- .odi
- .odm
- .odp
- .ods
- .odt
- .ora
- .ost
- .ova
- .ovf
- .p12
- .p7b
- .p7c
- .pem
- .pfx
- .php
- .pmf
- .png
- .ppt
- .pptx
- .ps1
- .pst
- .pvi
- .py
- .pyc
- .pyw
- .qcow
- .qcow2
- .rar
- .rb
- .rtf
- .scm
- .sln
- .sql
- .tar
- .tib
- .tif
- .tiff
- .vb
- .vbox
- .vbs
- .vcb
- .vdi
- .vfd
- .vhd
- .vhdx
- .vmc
- .vmdk
- .vmsd
- .vmtm
- .vmx
- .vsdx
- .vsv
- .work
- .xls
- .xlsx
- .xml
- .xvd
- .zip
It avoids encrypting files with the following strings in their file path:
- \AppData
- \ProgramData
- \Program Files
- \Windows
NOTES:
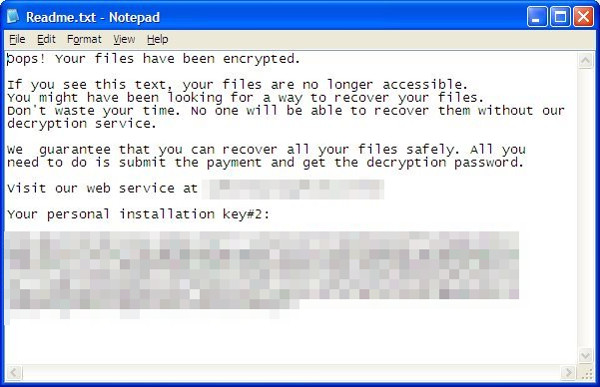
This ransomware drops the following ransom note named "Readme.txt" which contains the following:
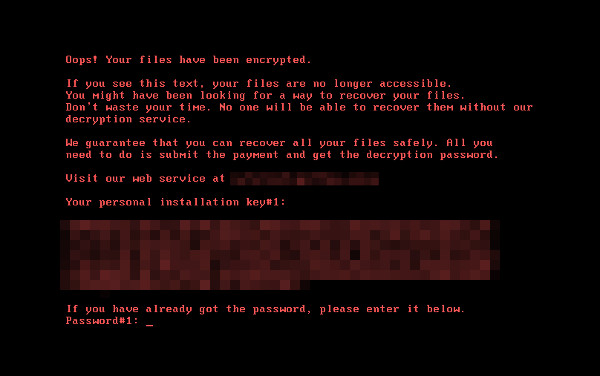
After rebooting the system, it then displays the following:
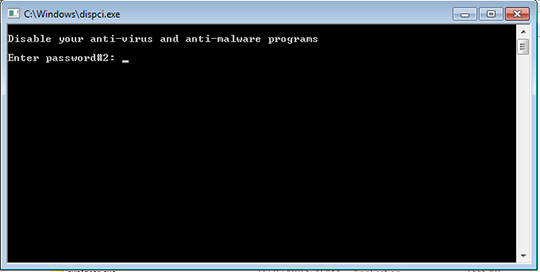
It displays the following window after clicking DECRYPT.lnk:
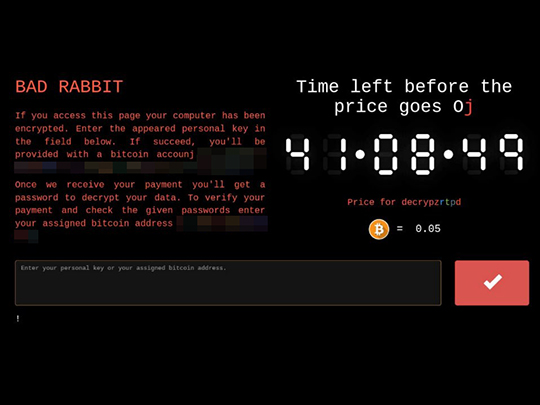
It also displays the following after accessing its payment site:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Restore your system's Master Boot Record (MBR)
To restore your system's Master Boot Record (MBR):
• On Windows 2000, XP, and Server 2003:
- Insert your Windows Installation CD into your CD drive then restart your computer.
- When prompted, press any key to boot from the CD.
- On the Main Menu, type r to enter the Recovery Console.
(Note for Windows 2000: After pressing r, type c to choose the Recovery Console on the repair options screen.) - Type the number that corresponds to the drive and folder that contains Windows (usually C:\WINDOWS) and press Enter.
- Type your Administrator password and press Enter.
- In the input box, type the following then press Enter:
fixmbr {affected drive} - Type exit and press Enter to restart the system normally.
• On Windows Vista, 7, and Server 2008:
- Insert your Windows Installation DVD into the DVD drive, then press the restart button on your computer.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to choose the installation language. On the Install Windows window, choose your language, locale, and keyboard layout or input method. Click Repair your computer.
- Select Use recovery tools that can help fix problems starting Windows. Select your installation of Windows. Click Next.
- If the Startup Repair window appears, click Cancel, Yes, then Finish.
- In the System Recovery Options menu, click Command Prompt.
- In the Command Prompt window, type the following then press Enter:
BootRec.exe /fixmbr - Type exit and press Enter to close the Command Prompt window.
- Click Restart to restart your computer normally.
• On Windows 8, 8.1, and Server 2012:
- Insert your Windows Installation DVD in the DVD drive, then restart your computer.
- When prompted, press any key to boot from the DVD.
- Depending on your Windows Installation DVD, you might be required to select the keyboard layout. Then on the Windows Setup window, choose your language, locale, and input method. Click Next, then click Repair your computer.
- Click Troubleshoot>Advanced Options>Command Prompt.
- In the Command Prompt window, type the following then press Enter:
BootRec.exe /fixmbr - Type exit and press Enter to close the Command Prompt window.
- Click Continue to restart the system normally.
Step 4
Restart in Safe Mode
Step 5
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services
- cscc
- cscc
Step 6
Search and delete these files
- %All Users Profile%\DECRYPT.lnk
- %Desktop%\DECRYPT.lnk
- %Windows%\cscc.dat
- %Windows%\dispci.exe
- %Windows%\infpub.dat
- %Windows%\{random hex value}.tmp
- {Drive letter}:\Readme.txt
Step 7
Restart in normal mode and scan your computer with your Trend Micro product for files detected as RANSOM_BADRABBIT.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 8
Restore encrypted files from backup.
Step 9
Scan your computer with your Trend Micro product to delete files detected as RANSOM_BADRABBIT.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.



