ELF_TSUNAMI.R
Linux/UNIX


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Linux backdoor has increased potential for damage, propagation, or both, that it possesses. Specifically, it is capable of carrying brute force attacks or exploit on the D-Link Internet router.
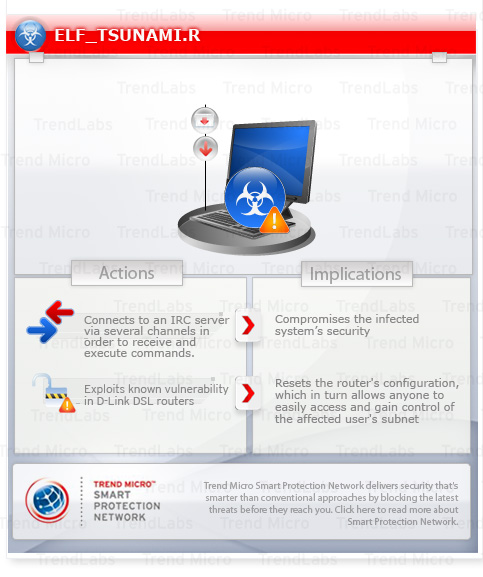
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
This backdoor may be dropped by other malware. It may be unknowingly downloaded by a user while visiting malicious websites.
It connects to Internet Relay Chat (IRC) servers.
TECHNICAL DETAILS
Arrival Details
This backdoor may be dropped by other malware.
It may be unknowingly downloaded by a user while visiting malicious websites.
Backdoor Routine
This backdoor connects to any of the following Internet Relay Chat (IRC) servers:
- {BLOCKED}.{BLOCKED}.81.114
- {BLOCKED}.{BLOCKED}.52.185
- {BLOCKED}.{BLOCKED}.51.77
- vexaa.{BLOCKED}th.cx
It joins any of the following IRC channel(s):
- #kleber
- #kaiten
- #kromex
- #dlink
- #dlink_key
Download Routine
This backdoor downloads updated copies of itself from the following websites:
- {BLOCKED}.{BLOCKED}.52.22
NOTES:
This backdoor is capable of receiving and executing the following commands from an IRC server:
- .login {password} - this logs in the bot's to the party-line
- .logout - this logs out the bot from the party-line
- .exec {command} - this executes a system command
- .clone {URL} {malware file name} - this clones hydra from new binary (HTTP)
- .upgrade {URL} {malware file name} - this upgrades the binary from a specified HTTP URL
- .version - this shows the current version of the bot
- .status - this shows the status of the bot
- .help - this shows a specific help message
- .advscan {a} {b} {user} {password} - scanner/exploit with user:passwd values
- .advscan {a} {b} - scanner/exploit with auto user:passwd values
- .recursive - advscan with local addr (A.B-range)
- .recrd - advscan with local addr (B-range random())
- .stop - this stops scan/flood actions
- .synflood {host} {port} {secs} - this is the standard command to perform a SYN flood
- .ircflood {nick} {number} {type} - this is the standard command to perform an IRC flood (type: 0=PRIVMSG, 1=CTCP)
- .join {channel} {password} - this connects the bot in selected channel using a specified password
- .part {channel} - this removes the bot from a specified channel
- .quit - this disconnects the bot from the server
Other variants have been noted to use the following commands:
- TSUNAMI {target} {secs} - this triggers the bot to perform a denial of service (DoS) attack on a specific target by sending packets at n seconds interval
- UNKNOWN {target} {secs} - this performs a non-spoof UDP flood to a specific target at n seconds interval
- PAN {target} {port} {secs} - this performs an advanced SYN flood to a specific target at n seconds interval
- UDP {target} {port} {secs} - this performs a UDP flood to a specific target at n seconds interval
- GETSPOOFS - this prevents anyone from tracking the source of the DoS attack
- SPOOFS {subnet} - changes spoofing to a subnet
- GET {HTTP address} {save as} - this downloads and saves a file
- IRC {command} - this sends commands to the IRC server
- SH {command} - this executes commands
Based on this backdoor's code, it has the ability to check if an Internet router is using a standard password by using a brute force attack. It is found, however, that there is no list of user names and passwords that it uses for the attack. Furthermore, it can check if the router is vulnerable to the following vulnerability:
SOLUTION
Scan your computer with your Trend Micro product to delete files detected as ELF_TSUNAMI.R. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


