BKDR_DLDR.A
Windows 2000, Windows XP, Windows Server 2003


Threat Type: Backdoor
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This backdoor arrives as a dropped malware. It is an Enfal/Lurid malware that has been used in other targeted attacks in the past. This backdoor's dropper, TROJ_ARTIEF.SDY, comes as a .DOC file attachment to spammed email about the Hurricane Sandy devastation.
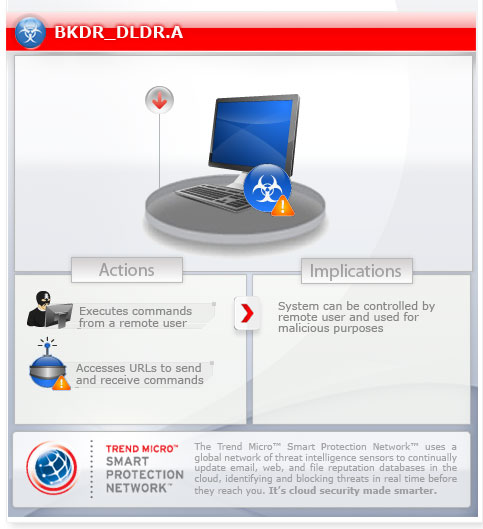
To get a one-glance comprehensive view of the behavior of this Backdoor, refer to the Threat Diagram shown below.
For the related story, you may read the blog post NATO's NSHQ Targeted by Attack Leveraging Hurricane Sandy
This backdoor may be dropped by other malware.
It executes commands from a remote malicious user, effectively compromising the affected system.
TECHNICAL DETAILS
Arrival Details
This backdoor may be dropped by the following malware:
- TROJ_ARTIEF.SDY
Installation
This backdoor drops the following copies of itself into the affected system and executes them:
- %User Temp%\adobeupd.exe
(Note: %User Temp% is the current user's Temp folder, which is usually C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, XP, and Server 2003, or C:\Users\{user name}\AppData\Local\Temp on Windows Vista and 7.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- HTTPS-GNIK
- MAINHTTPS
- RMTCURR
Autostart Technique
This backdoor drops the following shortcut pointing to its copy in the User Startup folder to enable its automatic execution at every system startup:
- %User Startup%\Adobe Center.lnk
- All Users' %User Startup%\Adobe Center.lnk
(Note: %User Startup% is the current user's Startup folder, which is usually C:\Windows\Profiles\{user name}\Start Menu\Programs\Startup on Windows 98 and ME, C:\WINNT\Profiles\{user name}\Start Menu\Programs\Startup on Windows NT, and C:\Documents and Settings\{User name}\Start Menu\Programs\Startup.)
Backdoor Routine
This backdoor executes the following commands from a remote malicious user:
- Download files from C&C server
- Upload files to C&C server
- Enumerate drives
- Get drive information
- Enumerate files/folders
- Find files/folders
- Get file information
- Create files/folders
- Modify files/folders
- Copy files/folders
- Delete files/folders
- Execute files
- Terminate processes
- Get time zone information
- Perform remote shell
- Sleep for a specified amount of time
It connects to the following URL(s) to send and receive commands from a remote malicious user:
- https://domain.{BLOCKED}2.us
It posts the following information to its command and control (C&C) server:
- Host name
- MAC address
- OS version information
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 3
Identify and terminate files detected as BKDR_DLDR.A
- Windows Task Manager may not display all running processes. In this case, please use a third-party process viewer, preferably Process Explorer, to terminate the malware/grayware/spyware file. You may download the said tool here.
- If the detected file is displayed in either Windows Task Manager or Process Explorer but you cannot delete it, restart your computer in safe mode. To do this, refer to this link for the complete steps.
- If the detected file is not displayed in either Windows Task Manager or Process Explorer, continue doing the next steps.
Step 4
Search and delete this file
- %User Startup%\Adobe Center.lnk
- All Users' %User Startup%\Adobe Center.lnk
Step 5
Scan your computer with your Trend Micro product to delete files detected as BKDR_DLDR.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Did this description help? Tell us how we did.


