ANDROIDOS_TORBOT.A
Information Stealer
Android OS


Threat Type: Trojan
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This is the first Android malware discovered to abuse the TOR network in order to conceal its connection to its C&C server. Users affected by this malware may find the security of their mobile devices compromised.
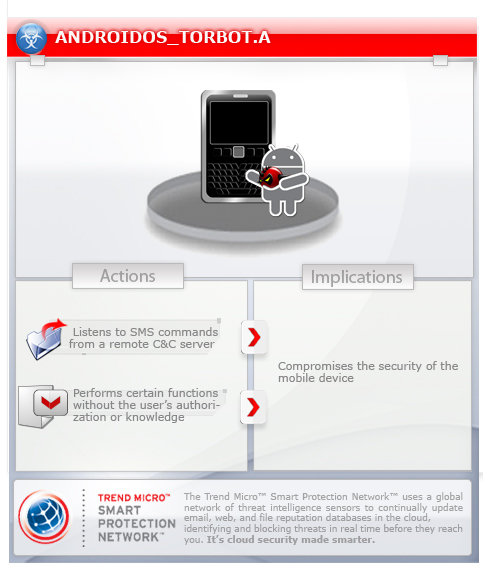
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
This malware leverages the TOR network to connect with a remote server. It may be installed manually by a user.
TECHNICAL DETAILS
NOTES:
This malware leverages the TOR network to connect with a remote server.
After installation, it shows the following common Android icon:

It runs at every system boot up. When first executed, it requests an administrator level permission and hide its icon from launcher.
It listens to SMS command from a remote C&C server. Based on the command, this malware may perform the following routines:
- Send out all the installed apps
- Start/stop steal sms
- Make phone call
- Start/stop intercept and steal SMS
- Send SMS to a certain number provided by remote command
- Update C&C number
All the responses of these commands are sent out via TOR network to the remote server.
SOLUTION
Step 1
Trend Micro Mobile Security Solution
Trend Micro Mobile Security Personal Edition protects Android and iOS smartphones and tablets from malicious and Trojanized applications. It blocks access to malicious websites, increase device performance, and protects your mobile data. You may download the Trend Micro Mobile Security apps from the following sites:
Step 2
Remove unwanted apps on your Android mobile device
Did this description help? Tell us how we did.



