ANDROIDOS_TIGERBOT.EVL
Spying Tool
Android OS


Threat Type: Spyware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Android backdoor can be controlled via SMS or phone calls.
To get a one-glance comprehensive view of the behavior of this Spyware, refer to the Threat Diagram shown below.

This application is installed only on the applications list and is not displayed as an icon on the main menu.
It waits for specially-crafted SMS messages to perform its intended routines.
This spyware may be unknowingly downloaded by a user while visiting malicious websites. It may be manually installed by a user.
TECHNICAL DETAILS
Arrival Details
This spyware may be unknowingly downloaded by a user while visiting malicious websites.
It may be manually installed by a user.
NOTES:
Upon installation, this application is only be visible in the installed applications list and not displayed as an icon on the main menu compared to normal applications:

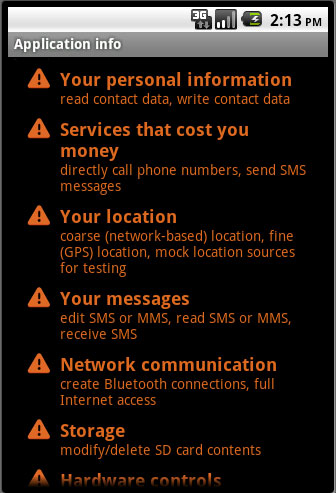
Below are some of the permissions it requires:
It waits for specially-crafted SMS messages to be able to perform any of the following routines:
- Change network settings
- Capture screenshots and upload the image
- Determine the current GPS location
- Kill processes except:
- Process name is any of the following:
- com.android.phone
- com.google.android.lifestyle (the malware process)
- system
- Process name starts with any of the following:
- com.htc.
- com.google.
- android.
- com.android.
- Process name is any of the following:
- Reboot affected device
- Record calls and upload the audio
- Retrieve contacts list
SOLUTION
Step 1
Trend Micro Mobile Security Solution
Trend Micro Mobile Security Personal Edition protects Android smartphones and tablets from malicious and Trojanized applications. The App Scanner is free and detects malicious and Trojanized apps as they are downloaded, while SmartSurfing blocks malicious websites using your device's Android browser.
Download and install the Trend Micro Mobile Security App via Google Play.
Step 2
Remove unwanted apps on your Android mobile device
Did this description help? Tell us how we did.

