ANDROIDOS_RUSMS.A
Premium Service Abuser
Android OS


Threat Type: Trojan
Destructiveness: No
Encrypted:
In the wild: Yes
OVERVIEW
This malware is related to the SMS spam attack that affected users in Taiwan. Once installed, the malicious app may send SMS, as well as intercept incoming ones. As such, this may incur charges without the user's knowledge.
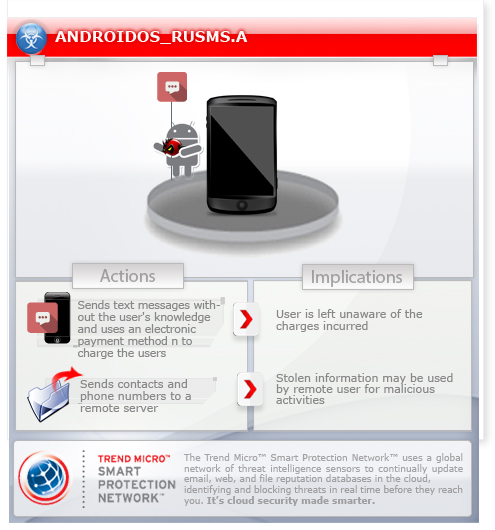
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives via SMS messages that contain the following details:
- http://goo.gl/W{BLOCKED}TBf
NOTES:
Once installed, it may send text messages without the user's knowledge and/or authorization. It uses an electronic payment method named Micropayment to charge the user of the affected device.
Since this malware intercepts certain incoming text messages, the user is left unaware of the charges incurred.
The malware blocks text messages from certain SMS addresses that contain the specific characters below. An SMS address is the originating address, or email address if the message came from an email gateway.
- 6279
- 1232111
- mopay
- boku
- 66245
- bezahlcode
- holyo
- 55498
- 55496
- 33235
- 46645
The blocked SMS is forwarded to http://{BLOCKED}.{BLOCKED}.13.43/sms/SMSHandler1.ashx.
It also sends contacts and phone numbers to a remote server.
SOLUTION
Step 1
Remove unwanted apps on your Android mobile device
Step 2
Trend Micro Mobile Security Solution
Trend Micro Mobile Security Personal Edition protects Android smartphones and tablets from malicious and Trojanized applications. The App Scanner is free and detects malicious and Trojanized apps as they are downloaded, while SmartSurfing blocks malicious websites using your device's Android browser.
Download and install the Trend Micro Mobile Security App via Google Play.
Did this description help? Tell us how we did.


