Is There a Budding West African Underground Market?
 View Cybercrime in West Africa: Poised for an Underground Market
View Cybercrime in West Africa: Poised for an Underground Market
Ever received an email supposedly from a Nigerian prince informing you that you’re an heir to his family’s fortune? Chances are you’ve encountered an advance-fee scam (aka a Nigerian prince scam). It is one of the oldest, most common tricks used by West African cybercriminals.
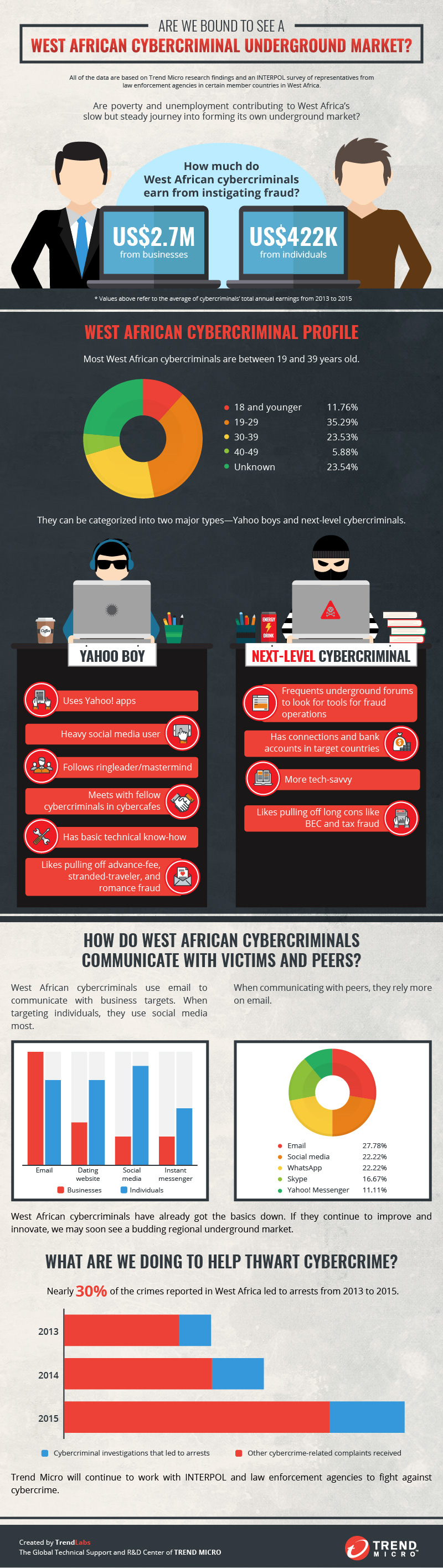
While West Africa has no underground market yet to speak of, a surge in cybercriminal activity reports in the region suggest that it is going toward that direction. The most probable reasons? Poverty and unemployment.
The INTERPOL survey conducted for the joint research with Trend Micro revealed that cybercriminals steal an average US$2.7 million from businesses and an average of US$422,000 from individuals each year.
Profiling West African Cybercriminals
Unlike their French counterparts who are cautious and wary of even their peers, West African cybercriminals willingly share their technical know-how and best practices. They constantly communicate with one another and even work in tight-knit groups via email and social media.
[READ: The French Underground: Under a Shroud of Extreme Caution]
There are two major types of West African cybercriminals—Yahoo boys and next-level cybercriminals.
Yahoo boys are typically 20−29 years old and like to brag about their ill-gotten gains on social media, particularly on Facebook. They have been dubbed such due to their use of Yahoo! Apps in the not-so-recent past. These days, they more heavily rely on social media for both communication and their criminal operations. They have basic technical know-how and typically work as part of a group supervised by a ringleader and mastermind.
Yahoo boys are likely to pull off the following scams:
- Advance-fee scam: Scammer pretends to be a member of a royal family seeking help with regard to the transfer of wealth. Other variations include the scammer informing the victim that he/she has won the lottery.
- Stranded-traveler scam: Scammer masquerades as a victim of a very unfortunate circumstance (an “emergency”) while traveling abroad and seeks the victim’s immediate financial assistance.
- Romance scam: Scammer leverages the trust and romantic relationship he/she has built with the target users to ask for financial support.
Next-level cybercriminals, meanwhile, are the complete opposite of Yahoo boys. They are relatively older (around 30 or older) and more technically adept. They frequent and purchase their tools (keyloggers and remote access tools/Trojans [RATs]) from underground forums. They also have ties, financial accounts, and networks in the countries their targets reside in. This helps them more smoothly carry out operations.
Next-level cybercriminals prefer to pull off “long cons,” more often related to more complex scams like:
- Business email compromise (BEC) scam: Scammer compromises the email account of an executive and tricks the company’s finance department to wiring large sums of money to an account he/she controls. BEC scammers have amassed US$3 billion from October 2013 to May 2016 from pulling off this type of scam.
- Tax scam: Scammer pretends to be an executive of the target company asking for W2 information from its human resources department in hopes of stealing tax returns intended for certain employees.
[READ: Billion-Dollar Scams: The Numbers Behind Business Email Compromise]
Working Hand in Hand to Combat Cybercrime
 View infographic: Are We Bound to See a West African Cybercriminal Underground Market?
View infographic: Are We Bound to See a West African Cybercriminal Underground Market?
The West African threat landscape is currently rife with cybercriminals conducting simple scams. But as our research showed, they are well on their way to pulling off more and more complex scams (i.e., BEC and tax scams).
As cybercriminals worldwide continue to evolve, private-public partnerships will become increasingly crucial. Trend Micro will continue to collaborate with law enforcement agencies like INTERPOL to combat cybercrime. In fact, around 30% of the crimes reported in West Africa led to arrests.
To know more about the West African threat landscape, read “Cybercrime in West Africa: Poised for an Underground Market.” For a quick look at the goings-on in the region, download our infographic, “Are We Bound to See a West African Cybercriminal Underground Market?”
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
последний
- The Hidden Risk in Your AI Rollout: Your Endpoints
- When AI Becomes a Zero-Day Machine: What Public Sector Organizations Need to Know
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation