By Mayra Rosario Fuentes [Senior Threat Researcher, TrendAI™ Research] and Vincent Lee [Senior Manager, TrendAI™ Zero Day Initiative™ (ZDI)]
Key takeaways
- Old vulnerabilities remain operationally valuable. Over two-thirds (70.14%) of requested exploits were for vulnerabilities more than two years old and nearly 8% were for vulnerabilities 10 to 15 years old, confirming that exploit value persists long after disclosure.
- Exploit demand aligns with real-world active exploitation. Nearly one-third (31%) of requested exploits appear in CISA’s Known Exploited Vulnerabilities (KEV) catalog, indicating attackers prioritize flaws with proven real-world impact.
- Patch management failures are systemic, not isolated. The continued demand for legacy CVEs highlights persistent challenges in timely patching, even for vulnerabilities publicly designated as high-risk.
- Global exposure to known CVEs remains dangerously high. As of February 2026, more than 270,000 systems remained exposed to SMBGhost (CVE-2020-0796), a six-year-old flaw, highlighting how long-known vulnerabilities continue to pose a global threat when left unaddressed.
- Persistent failure to remediate known vulnerabilities is the primary driver of risk. Attackers continue to monetize long-disclosed CVEs because they remain operational and exposed at scale. This sustains a stable, low-cost exploitation economy in which n-day exploits remain profitable, predictable, and repeatable.
Introduction
Organizations may be grappling with significant changes in the dawning age of AI. Yet their biggest risk may come from a far more familiar and yet overlooked source: old vulnerabilities. As our observations show, no vulnerability (CVE) is ever too old to attract cybercriminal interest, and exploits remain one of the most common points for system compromise.
TrendAI™ Research’s 2021 analysis of the cybercriminal underground revealed a slowdown in the exploit market, but this proved short-lived; the market has since rebounded in the years following Covid. This resurgence warranted renewed scrutiny.
In this latest study, we reviewed activity across the cybercriminal underground from January 2023 to January 2026 and found sustained demand for n-day exploits, reinforcing the reality that old vulnerabilities remain operationally valuable to cybercriminals.
Threat actors routinely seek vulnerabilities long after their public disclosure. In fact, the oldest exploit request identified in our research targeted a vulnerability disclosed in 2011. Consistent with this pattern, most exploits circulating in the market focus on high-severity vulnerabilities, as reflected in their CVSS scores. These old flaws carry new implications and can hold organizations back, particularly as they advance into the age of AI.
AI as a new force in vulnerability creation and exploitation
Amid this evolution of the exploit market, AI is emerging as another critical force shaping its future. AI coding assistants have rapidly progressed from experimental tools to mainstream components of modern software development. Today, many organizations routinely deploy machine-generated or machine-assisted code across production environments, often at a pace that exceeds traditional security review processes. While these tools deliver significant productivity advantages, AI-generated code introduces new risks. Because large language models (LLMs) are trained on extensive public datasets that include unsecure coding practices, their outputs frequently replicate well-known vulnerabilities and unsafe design patterns. This increases the likelihood that exploitable flaws are introduced into applications at scale.
Beyond unsecure code generation, AI-powered services themselves present attractive targets for exploitation. Attackers can abuse weaknesses in AI-driven systems to execute unauthorized code, bypass sandboxing and isolation controls, and exploit flaws in error-handling logic or input validation. Successful exploitation can lead to data breaches, unauthorized data transfers, and persistent access within execution environments. And as AI becomes more deeply embedded into business-critical workflows, the potential blast radius of exploits only continues to grow.
Related research
TrendAI™ Research’s 2021 report, “The Rise and Imminent Fall of the N-Day Exploit Market in the Cybercriminal Underground,” showed that long-disclosed vulnerabilties continued to be bought, sold, and used in attacks, even as the market itself showed signs of slowing down. Revisiting this report highlights how that market has shifted in recent years.
AI also heralds a new era of cybercrime. Criminal adoption of AI tools reflects a rapidly evolving threat landscape. Although widespread attacks directly stemming from compromised AI platforms have not yet been observed, multiple critical vulnerabilities and proof-of-concept (PoC) exploits affecting popular AI tools and frameworks underscore the seriousness of the risk. These early indicators suggest that adversaries are actively probing AI ecosystems, refining techniques, and preparing for broader exploitation opportunities. With AI-driven applications rapidly integrating into sectors such as finance, healthcare, legal services, and technology, the potential impact of successful attacks only grows more substantial.
AI acceleration and the trust gap
Industry data highlights both the speed and scale of AI adoption. The 2025 Stack Overflow Developer Survey, based on over 49,000 responses from developers across 177 countries, found that 84% of respondents were either using or planning to use AI tools in their development process, up from 76% in 2024. Nearly half of all developers reported using AI tools daily and, among professional developers, 51% relied on them every day. Yet, despite this widespread adoption, confidence in AI-generated outputs remained low: Only 3% of respondents reported high trust, 29.6% expressed moderate trust, and 46% expressed some degree of distrust in AI-produced code.
This gap between adoption and confidence reflects a growing tension, as organizations become increasingly dependent on AI-driven development while continuing to grapple with fundamental security and reliability concerns.
Converging risks
These trends show that the exploit market remains resilient and highly adaptive, even as AI continues to expand the attack surface and amplifies the potential impact of vulnerabilities. As AI-generated code and AI-driven services become fundamental components of modern software ecosystems, organizations should expect increased exploitation activity to proactively adjust their security strategies. Without deliberate action to address these emerging risks, attackers will be able to leverage AI at scale, using it not only as a tool for exploitation but also as a source of new and systemic weaknesses.
Exploit demand and availability
Our research examined advertisements for exploits offered for sale within the cybercriminal underground, with a focus on filtering out listings that appeared to be from scammers or low-reputation actors. We analyzed activity over the last three years both in English- and Russian-language cybercriminal forums. In addition to supply-side activity, we reviewed demand by identifying the exploits that users were actively seeking to purchase, effectively capturing a “wish list” of vulnerabilities of interest. As in our previous 2021 analysis, higher priced exploits continued to appear predominantly in Russian-language forums.
It is important to note that while the exploits cited in this report are advertised for sale on cybercriminal forums, they cannot be confirmed to work without purchase, though the reputation of certain actors or sellers suggests that many are likely functional.
Wish list for outdated CVEs
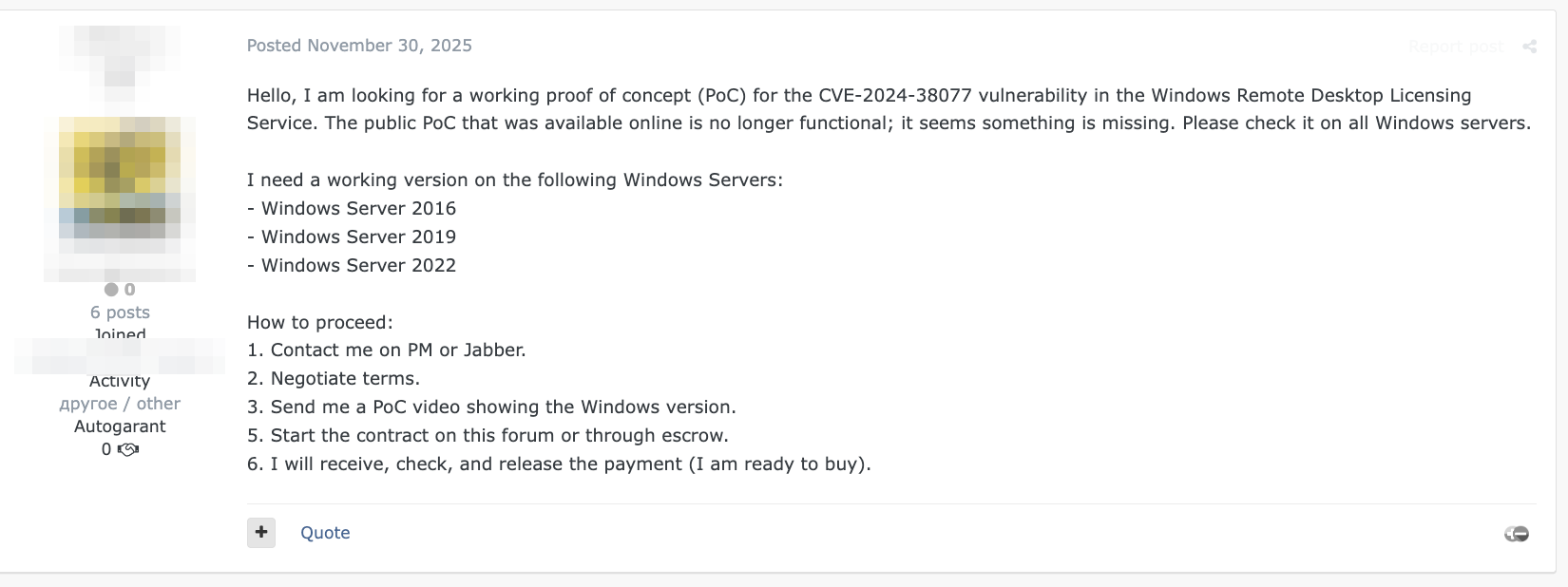
Our analysis shows a clear preference for high- or critical-severity vulnerabilities in underground demand. More than half of the requested exploits were associated with vulnerabilities scoring 7.5 or higher on the Common Vulnerability Scoring System (CVSS) — such as the one mentioned in the request shown in Figure 1, CVE-2024-38077, which has a CVSS score of 9.8.
Figure 1. Forum post requesting to purchase an exploit for CVE-2024-38077, a critical-severity vulnerability
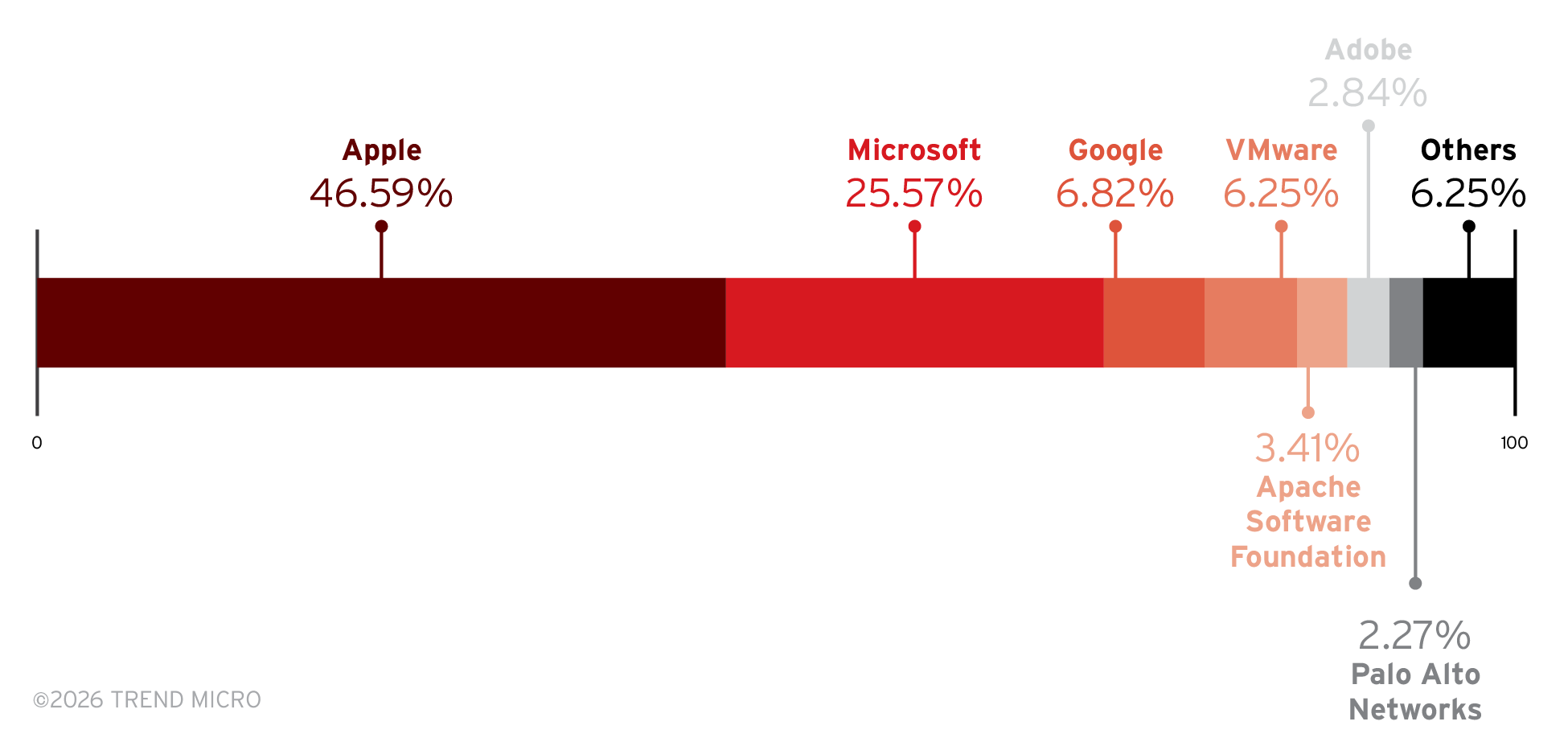
As shown in Figure 2, exploits targeting Apple products emerged as the most frequently requested, accounting for 46.59% of observed demand, followed by Microsoft at 25.57%. This distribution marks a notable shift from our 2021 findings, when Microsoft products dominated exploit requests. However, Microsoft remains a highly sought-out target due to its enterprise prevalence and the high-value exploitation opportunities it provides, reflected in the fact that Microsoft-related exploits remain the most sold, as detailed later in this report.
Figure 2. Distribution of exploits requested on cybercriminal underground forums based on the affected products
Notably, most buyers who listed a price were willing to pay US$5,000 or more for an outdated CVE. One user was even willing to pay US$50,000 for vulnerabilities in Microsoft Outlook, WordPress, and Fortinet products. Beyond these high-value requests, secondary demand clusters appeared around major infrastructure and software vendors, including Google at 6.82% and VMware at 6.25%.
The following are some of the oldest CVEs requested, along with their descriptions and CVSS scores:
- CVE-2011-2688: SQL injection, 7.5
- CVE-2011-3416: ASP.NET forms authentication bypass, 8.5
- CVE-2014-2383: Unauthenticated Dompdf local file inclusion, 6.8
- CVE-2015-7036: SQLite database remote code execution (RCE), 7.5
- CVE-2015-9251: JQuery cross-site scripting, 6.1
A notable example is the high-severity SQL injection vulnerability CVE-2011-2688, a 15-year-old vulnerability that was observed being exploited by FinStealer, a mobile banking malware targeting Indian banks. This case demonstrates how even decade-old exploits can still be leveraged for significant damage.
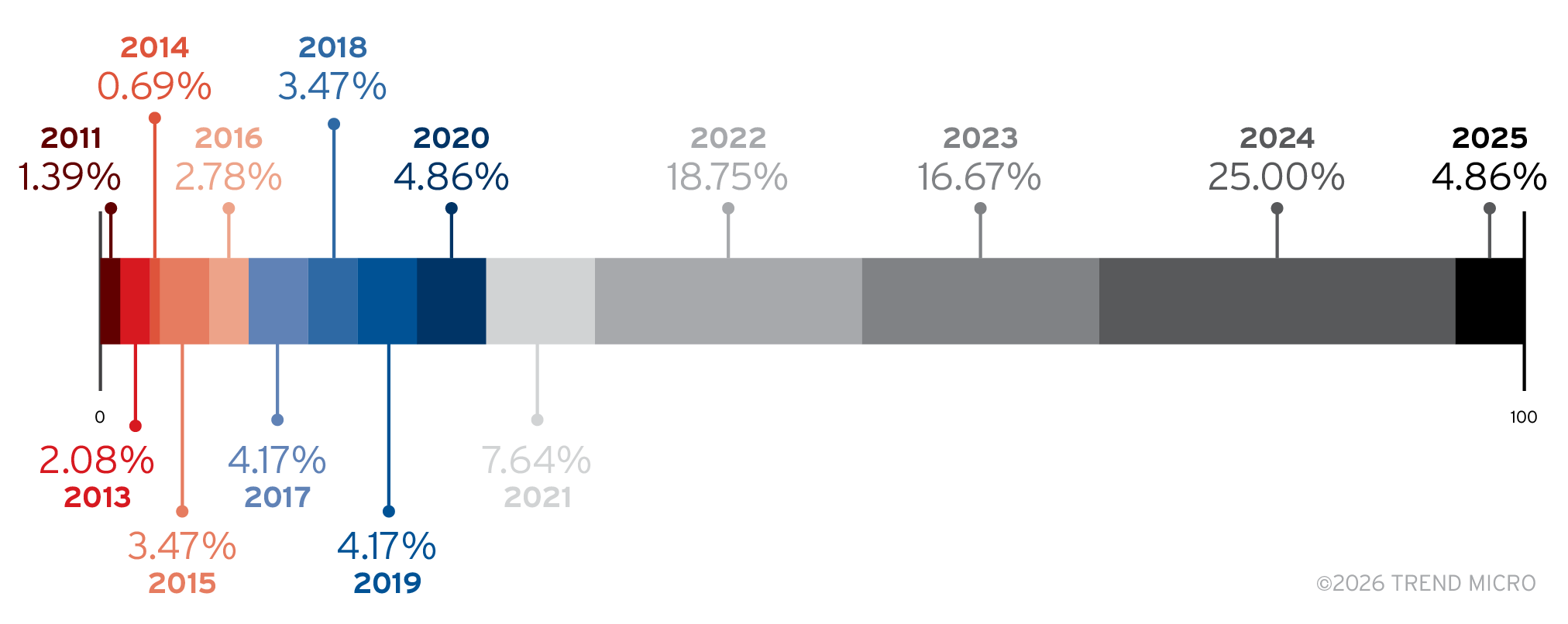
The highest concentrations for requested exploits were for vulnerabilities published in 2024 (25%) and 2022 (18.75%). Overall, over two-thirds (70.14%) of requested exploits were for vulnerabilities over two years old and nearly 8% were associated with vulnerabilities between 10 and 15 years old.
Figure 3. Distribution of exploits requested on cybercriminal underground forums based on the years of vulnerability discovery
Additionally, 31% of the vulnerabilities on the exploit wish list appear in CISA’s Known Exploited Vulnerabilities (KEV) catalog. The KEV catalog is a publicly maintained list of software and hardware flaws that CISA has confirmed to be actively exploited in the wild, serving as a critical resource for organizations in determining where to focus their patching efforts. The concentration of exploit demand around older vulnerabilities and their inclusion in CISA’s KEV catalog suggest that known, actively exploited CVEs continue to present a systemic risk. We examine this exposure in greater detail in a later section.
Sales listings
While wish list posts reflect the vulnerabilities attackers want, the sales listings reveal what is actually available and how these exploits are valued in the underground market.
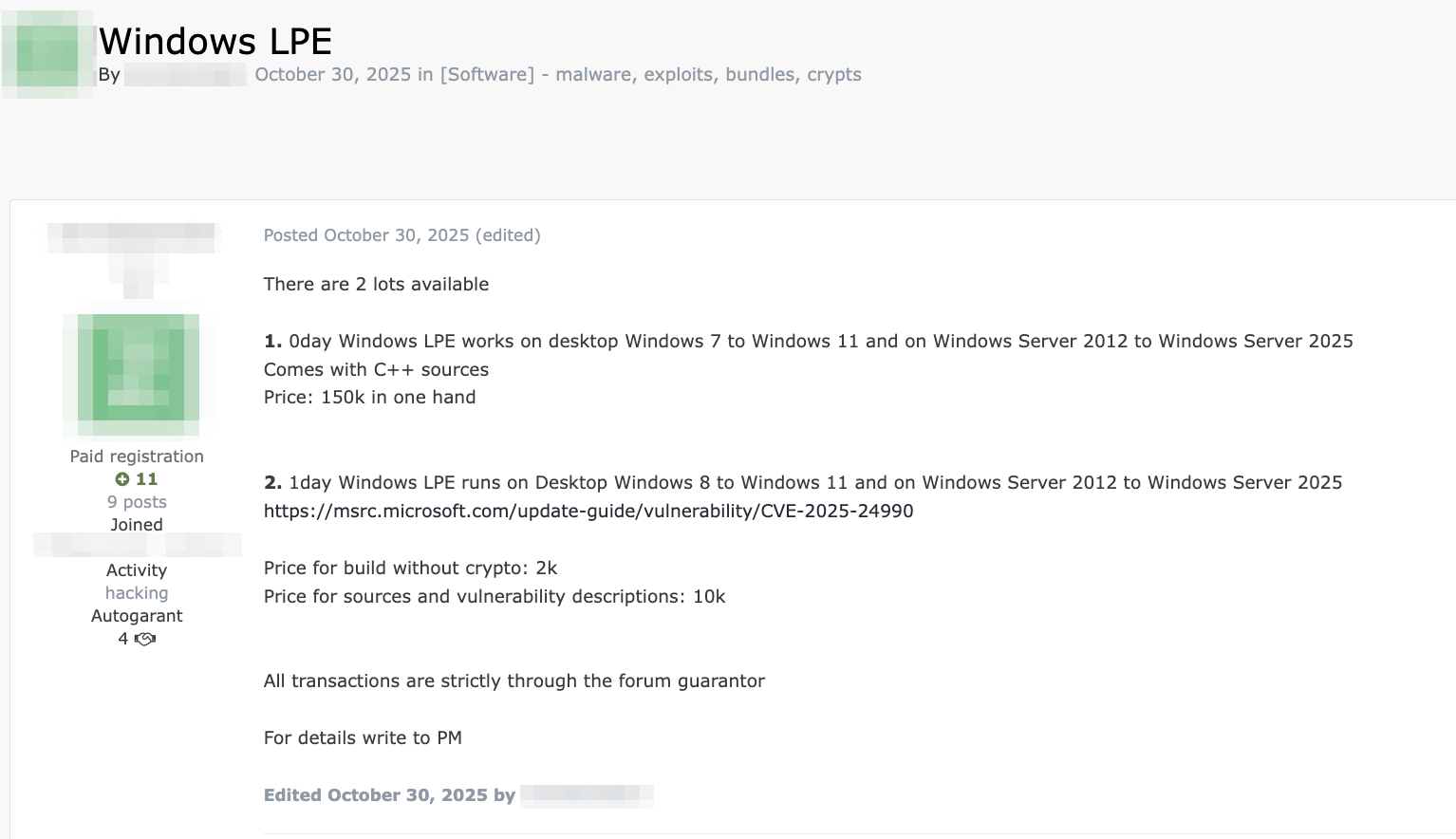
Based on the sales listings included in this study, the prices for exploits ranged from US$500 to US$115,000 per copy. We found that 68.18% of exploits offered for sale were exploited in the wild as of December 2025, according to CISA’s KEV catalog. This is notably higher than the 31% observed on attacker wish lists and request posts that appear in the same catalog. Microsoft-related exploits commanded some of the highest prices, averaging roughly US$100,000, as exemplified by the post shown in Figure 4, selling an exploit for the Microsoft Windows vulnerability CVE-2025-24990.
Figure 4. Forum post selling an exploit for a Microsoft Windows vulnerability (CVE-2025-24990) for US$10,000, along with a zero-day Windows vulnerability for US$150,000
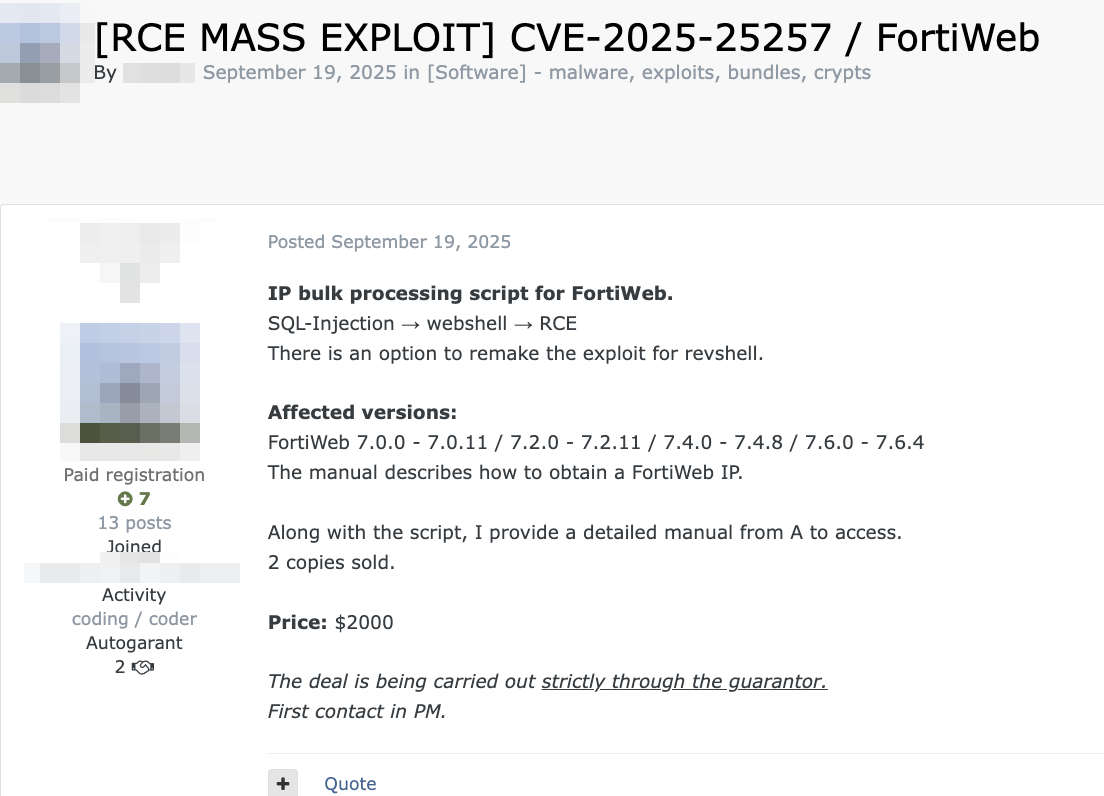
Lower-priced exploits — those typically below US$5,000 — included those for FortiWeb, FTP servers, and printers. These tend to be priced lower due to their limited impact, the high availability of their exploits, or both. For example, we saw an exploit for a FortiWeb vulnerability, CVE-2025-25257, listed for US$2,000 in a Russian forum, as shown in Figure 5.
Figure 5. Forum post selling an exploit for CVE-2025-25257 for US$2,000
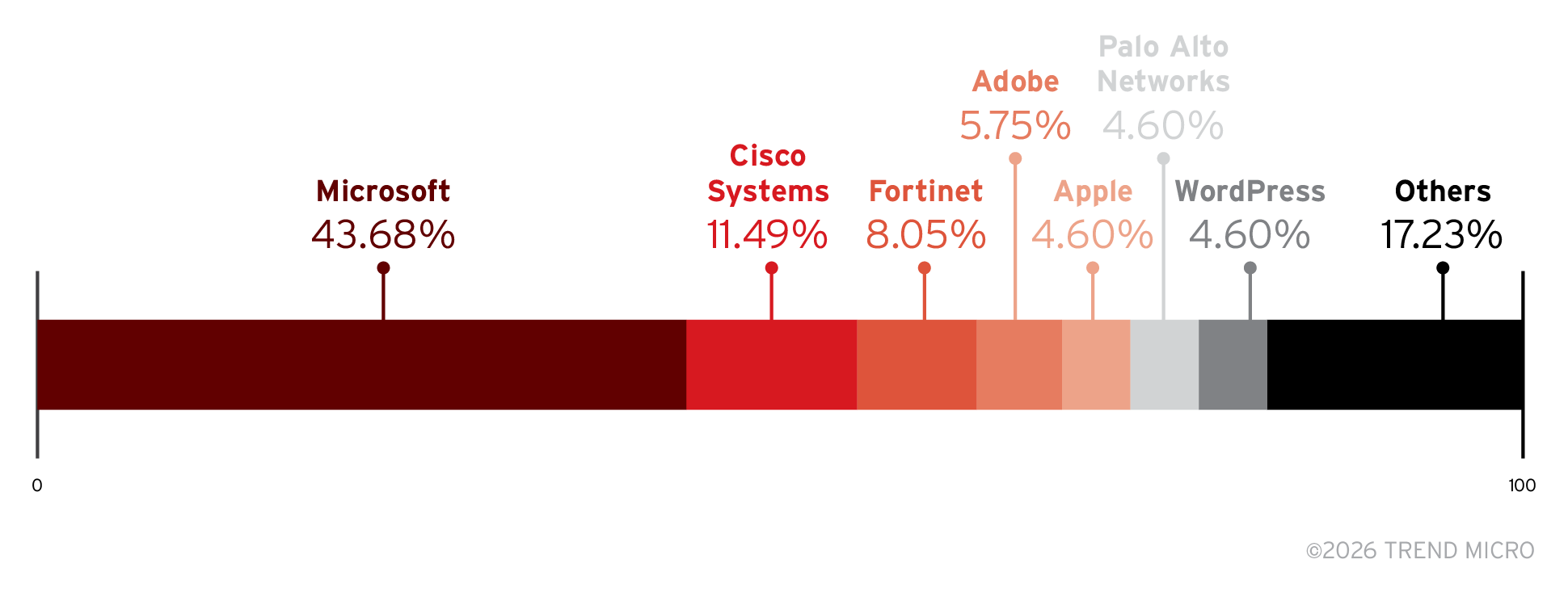
Overall, there are notable differences between the vulnerabilities requested in wish list posts and those offered for sale on underground forums. More than half of the exploits sold are known to be exploited in the wild, reflecting a clear market preference for vulnerabilities with demonstrated effectiveness. Exploits for Microsoft products mostly dominate the marketplace both in volume and in price, underscoring their broad deployment and the premium placed on exploits with wide attack surfaces. This concentration is illustrated in Figure 6 and Table 1.
Figure 6. Distribution of exploits sold on cybercriminal underground forums based on the affected products
| Affected product | Average price/Price range |
|---|---|
| VMware ESXi | Over US$1,000,000 |
| Cisco | US$10,000–US$150,000 |
| Microsoft Office | US$100,000 |
| Microsoft SharePoint | US$100,000 |
| Android | US$80,000–US$100,000 |
| Firefox | US$5,000–US$100,000 |
| Magento | US$20,000 |
| Stripe | US$10,000 |
| Zyxel VPN | US$5,000–US$10,000 |
| Fortinet | US$3,000–US$10,000 |
| FTP | US$5,000 |
| Printers | US$2,500 |
Table 1. Typical prices for n-day exploits sold on cybercriminal underground forums for commonly affected products
Exposure and value of outdated CVEs
To better understand the real-world impact of persistent exposure and to add further context to the valuation of exploits, we examined current internet-facing systems to assess how widely these vulnerabilities remain deployed.
We used Shodan, a search engine for internet-connected devices, to assess the current global exposure of several outdated CVEs as of Feb. 18, 2026. Our goal was to illustrate the ongoing importance of timely patching and demonstrate how cybercriminals continue to exploit long-known vulnerabilities.
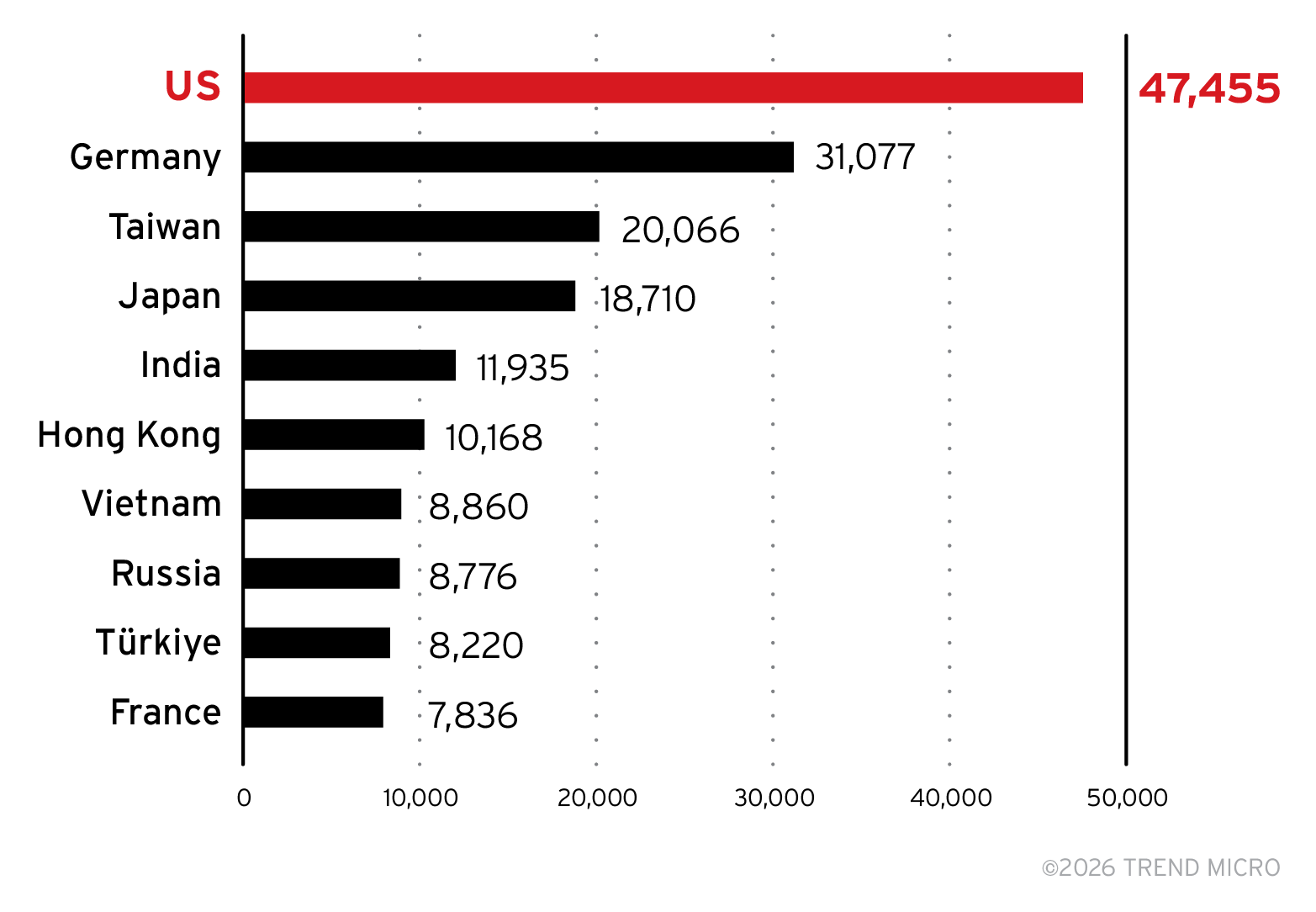
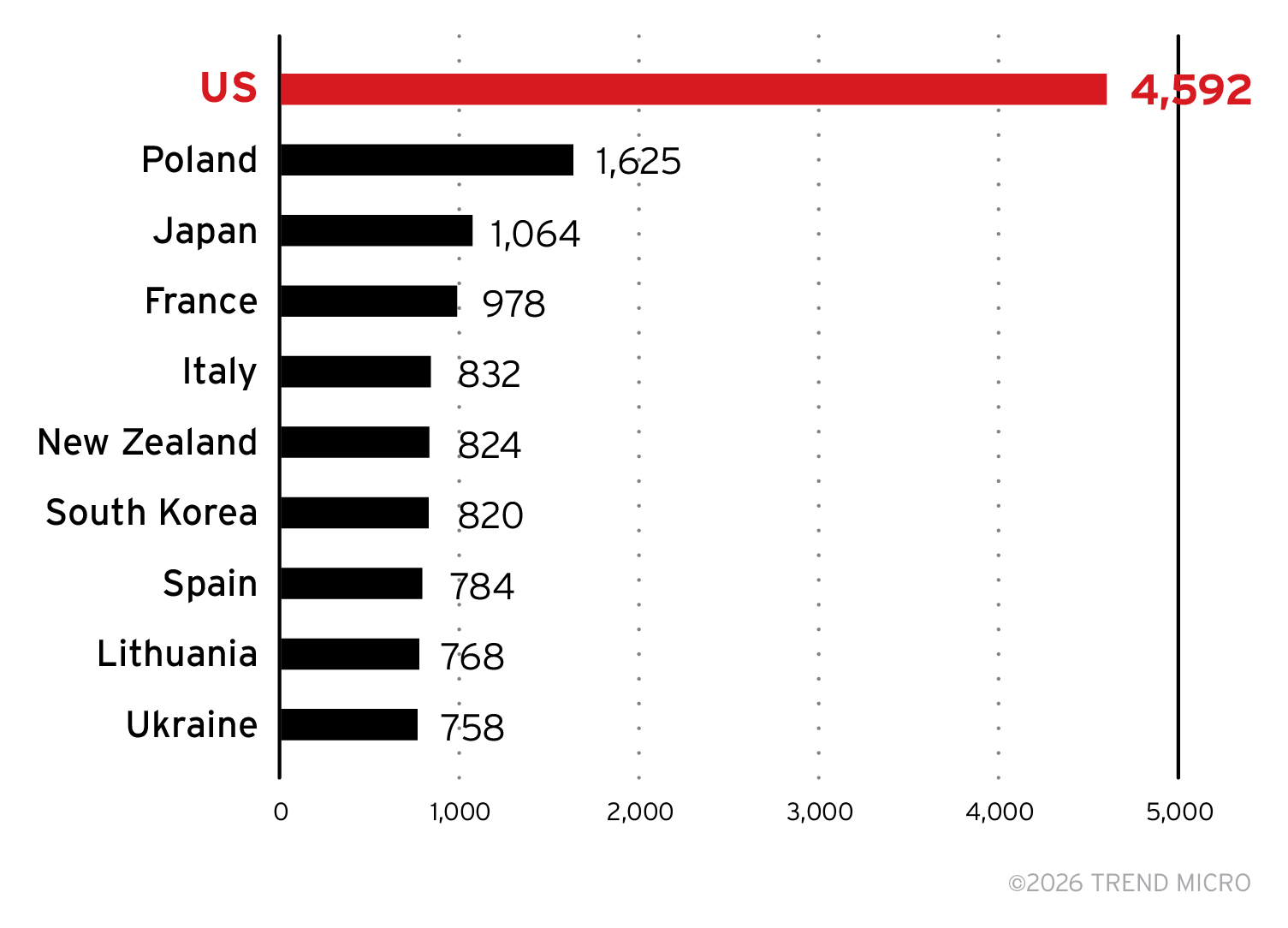
The analysis showed that SMBGhost (CVE-2020-0796), a critical-severity RCE vulnerability in Microsoft Server Message Block (SMB), remained the most prevalent vulnerability across more than 20 countries or regions, with the top 10 shown in Figure 7. Even six years after its discovery, over 270,000 systems worldwide were still exposed to this vulnerability, underscoring the persistent global risk posed by unpatched systems.
Figure 7. Top 10 countries or regions by number of systems exposed to SMBGhost (CVE-2020-0796) in mid-February 2026
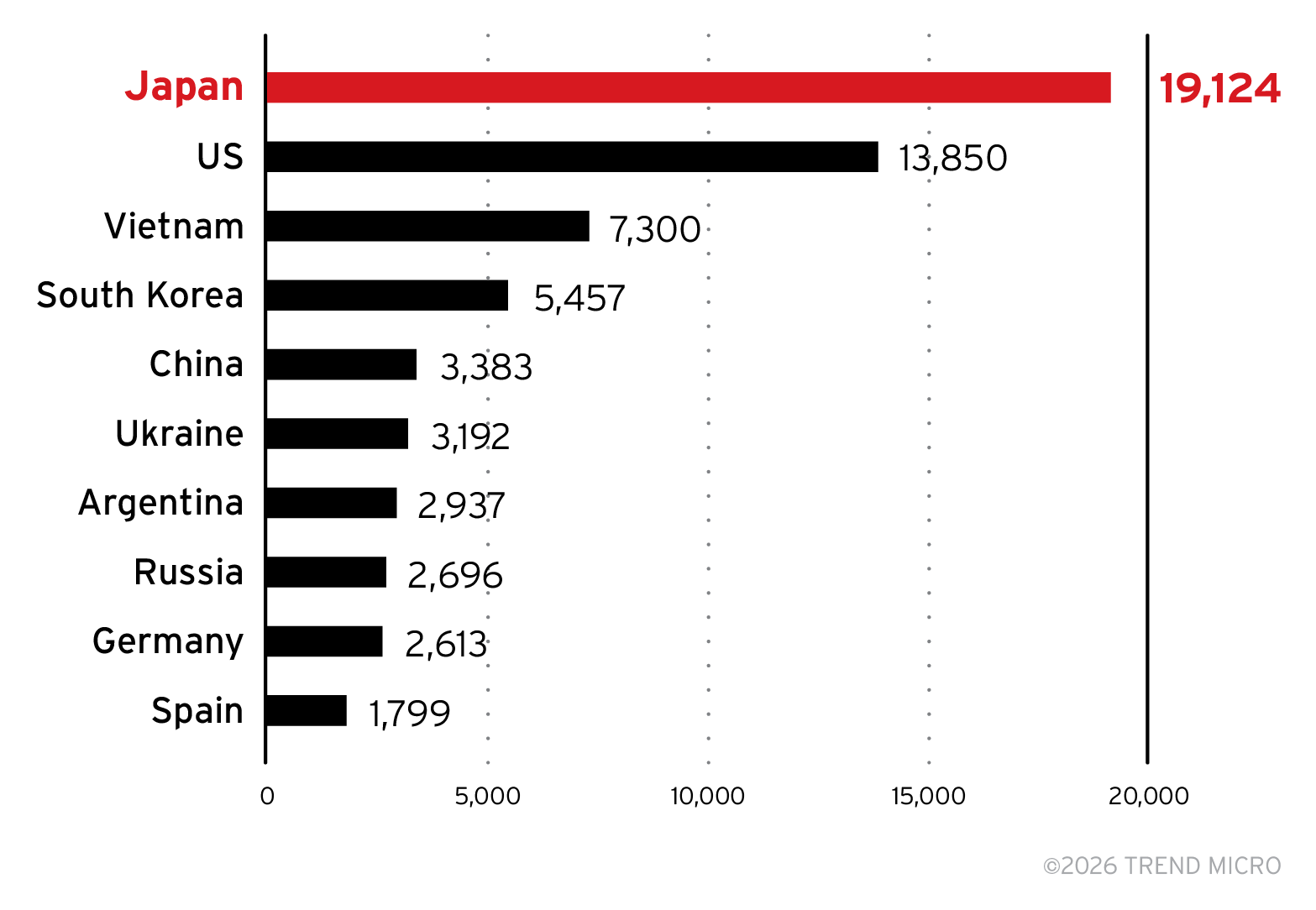
The Heartbleed vulnerability (CVE-2014-0160), which carries a high CVSS score of 7.5, also remained widely exposed, with 88,652 systems still vulnerable as of mid-February 2026. Figure 8 shows a breakdown of the top 10 countries with systems exposed to Heartbleed. These findings demonstrate that even decade-old vulnerabilities continue to present significant risk when left unpatched.
Figure 8. Top 10 countries by number of systems exposed to Heartbleed (CVE-2014-0160) in mid-February 2026
A more recent example: Although CVE-2025-53770 was patched in July 2025, Shodan still detected more than 18,000 vulnerable systems seven months later — despite the vulnerability carrying a critical CVSS score of 9.8. This vulnerability is a code injection flaw in Microsoft SharePoint servers that allows an unauthorized attacker to execute code over a network. Figure 9 shows the distribution of systems exposed to CVE-2025-53770 across the 10 countries with the most affected systems.
Figure 9. Top 10 countries by number of systems exposed to CVE-2025-53770 in mid-February 2026
This persistent exposure is not merely theoretical. Rather, it constitutes a real and immediate risk.
In 2025, unidentified threat actors publicly compromised Microsoft Exchange servers by injecting malicious code into login pages to harvest user credentials. These attacks leveraged several outdated vulnerabilities — including CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065, CVE-2021-31207, CVE-2021-34473, and CVE-2021-34523 — and targeted organizations across 26 countries worldwide. This campaign demonstrates how legacy CVEs continue to be actively exploited at scale. Shodan data showed that at least 100 systems were vulnerable to each of the mentioned vulnerabilities.
In January 2026, CISA added a 17-year-old vulnerability, CVE-2009-0556, to its list of actively exploited CVEs in the wild. This addition underscores that there is really no predictable limit to how long old flaws can present relevant risks or continue to attract interest from cybercriminals.
Recognizing the reality of ongoing exposure also helps contextualize the economics of the underground market that was discussed in the previous section. Exploit buyers willingly pay premium prices for vulnerabilities, even old ones, because they remain highly exploitable at scale.
Real-world valuation vs. underground market pricing
In this section, we examine how payouts from TrendAI™ Zero Day Initiative™ (ZDI) compare with the pricing observed in the cybercriminal underground market from 2023 to 2026. This comparison provides a deeper view into how underground actors value vulnerabilities in contrast to legitimate disclosure programs.
TrendAI™ ZDI is the world’s largest vendor-agnostic bug bounty program, established to promote responsible disclosure of zero-day vulnerabilities to affected vendors by financially rewarding researchers. TrendAI™ ZDI continues to lead the global vulnerability disclosure landscape, accounting for 73% of vulnerability disclosures in 2024. Discussions on cybercriminal forums occasionally mention selling exploits to vendor bug bounty programs such as TrendAI™ ZDI as an alternative to illicit activity.
Among all the listings, pricing for Microsoft-related exploits (advertised typically at US$100,000) aligned the most with TrendAI™ ZDI’s bug bounty market valuation.
| Affected product | Cybercriminal underground market average price/price range | TrendAI™ ZDI average price/price range |
|---|---|---|
| VMware ESXi | Over US$1,000,000 | US$100,000–US$150,000 |
| Microsoft Office | US$100,000 | US$100,000 |
| Microsoft SharePoint | US$100,000 | US$100,000 |
| Firefox | US$5,000–US$100,000 | US$50,000–US$100,000 |
| Printers | US$2,500 | US$7500–US$10,000 |
Table 2. Typical prices for n-day exploits sold on cybercriminal underground forums for commonly affected products compared with approximate zero-day pricing in the TrendAI™ ZDI program
The contrast in pricing demonstrates that the underground market is dictated by real operational value for attackers, rather than theoretical severity alone.
Conclusion and recommendations
Our findings make clear that the n-day exploit market is not a declining relic, but a mature, adaptive economy fueled by persistent exposure, delayed patching, and expanding technological complexity. Unless organizations prioritize the remediation of known exploited vulnerabilities, they will continue to face avoidable compromise, systemic exposure, and escalating operational risk, regardless of advances in detection technologies or defensive tooling.
To reduce risk from n‑day exploits in the AI era, organizations should focus on the following actions:
- Prioritize vulnerabilities based on real‑world exploitation, not age or severity alone. Actively track which CVEs are known to be exploited in the wild and ensure these are remediated first, regardless of when they were disclosed or how long they have existed in the environment.
- Continuously reassess exposure to legacy vulnerabilities. Treat older CVEs as an ongoing risk condition by regularly validating patch status, monitoring for configuration drift, and reassessing exposure as systems, assets, and business priorities change.
- Enforce remediation accountability for known‑exploited vulnerabilities. Assign clear ownership and remediation timelines for vulnerabilities with confirmed exploitation, with visibility into exceptions, delays, and compensating controls.
- Reduce attack surface where patching is not immediately possible. Isolate, restrict access to, or decommission systems that cannot be promptly patched, particularly those that are internet‑facing or business‑critical.
- Integrate security controls into AI‑assisted development workflows. Apply secure coding standards, automated vulnerability testing, and governance checks to machine‑generated code, and ensure AI‑enabled services undergo the same security review, monitoring, and patch management as traditional applications.
These measures help disrupt repeatable initial access paths, limit long‑term exposure to known weaknesses, and prevent legacy vulnerabilities from compounding the risks introduced by AI‑driven development.
TrendAI Vision One™ provides several capabilities that help organizations address persistent exposure from long‑standing vulnerabilities and the growing risks introduced by AI-driven development:
- TrendAI Vision One™ Cyber Risk Exposure Management (CREM): CREM delivers continuous, real-time visibility into an organization’s attack surface and prioritizes remediation based on actual risk impact. CREM’s Vulnerability Management module identifies, assesses, and contextualizes both newly disclosed and long-standing vulnerabilities. By correlating exploitability, exposure, and threat actor activity, CREM guides security teams toward the issues most likely to be targeted in real-world attacks.
- TrendAI Vision One™ Threat Intelligence Hub: Threat Intelligence Hub enriches an organization’s detection and response capabilities with deeper insights into threat actors, exploited CVEs, and active attack campaigns. By correlating vulnerabilities with adversaries known to use them, it helps teams prioritize defensive action with greater precision and understand the evolving tactics behind n-day exploit demand.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
последний
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter


 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation