Ransomware Recap: Tougher Tactics and Evasion Techniques
 Ransomware authors are nothing if not persistent. They continue to try new evasion techniques, new programming languages, new naming conventions, and even more forceful demand tactics to pressure victims into paying.
Ransomware authors are nothing if not persistent. They continue to try new evasion techniques, new programming languages, new naming conventions, and even more forceful demand tactics to pressure victims into paying.
One new technique involves packaging ransomware in RarSFX executable files. Last week we talked about a multi-component variant of Cerber (detected as RANSOM_CERBER) found packaged in a SFX file, a feature that helps it evade machine learning. This week, we saw CrptXXX (detected by Trend Micro as RANSOM_CRPTX.A) also in a SFX package—most likely for the same reason. This particular ransomware cannot execute fully without the correct parameters and other components inside its package.
If CrptXXX successfully infects a system, the victim receives a relatively straightforward ransom note. They are instructed to go to a specific .onion site and input their unique ID, then follow the payment instructions.
Tougher tactics
French Locker (detected by Trend Micro as RANSOM_LELEOCK.A) is a typical ransomware made by developers who want to get paid quickly. This ransomware displays a 10 minute timer and deletes one of the victim's encrypted files for every 10 minutes that passes.
It arrives through malicious sites or is dropped by other malware, and victims can choose between English or a French version. Initially, the ransomware will install an autostart registry for its dropped copy, which triggers its encryption routine once the machine reboots. Encrypted files are appended with the .lelele extension.
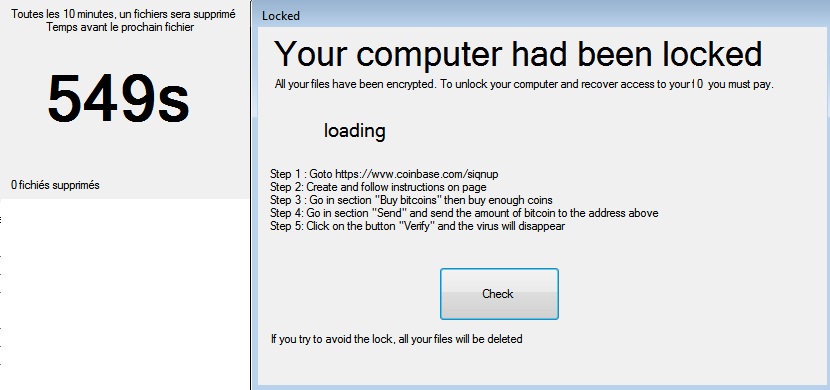
Figure 1. FrenchLocker ransom note
French Locker also scans the following processes and terminates them if they are running on the infected system:
- Processhacker
- Taskmgr
- Wireshark
- Chrome
- Firefox
- Skype
Old threats updated
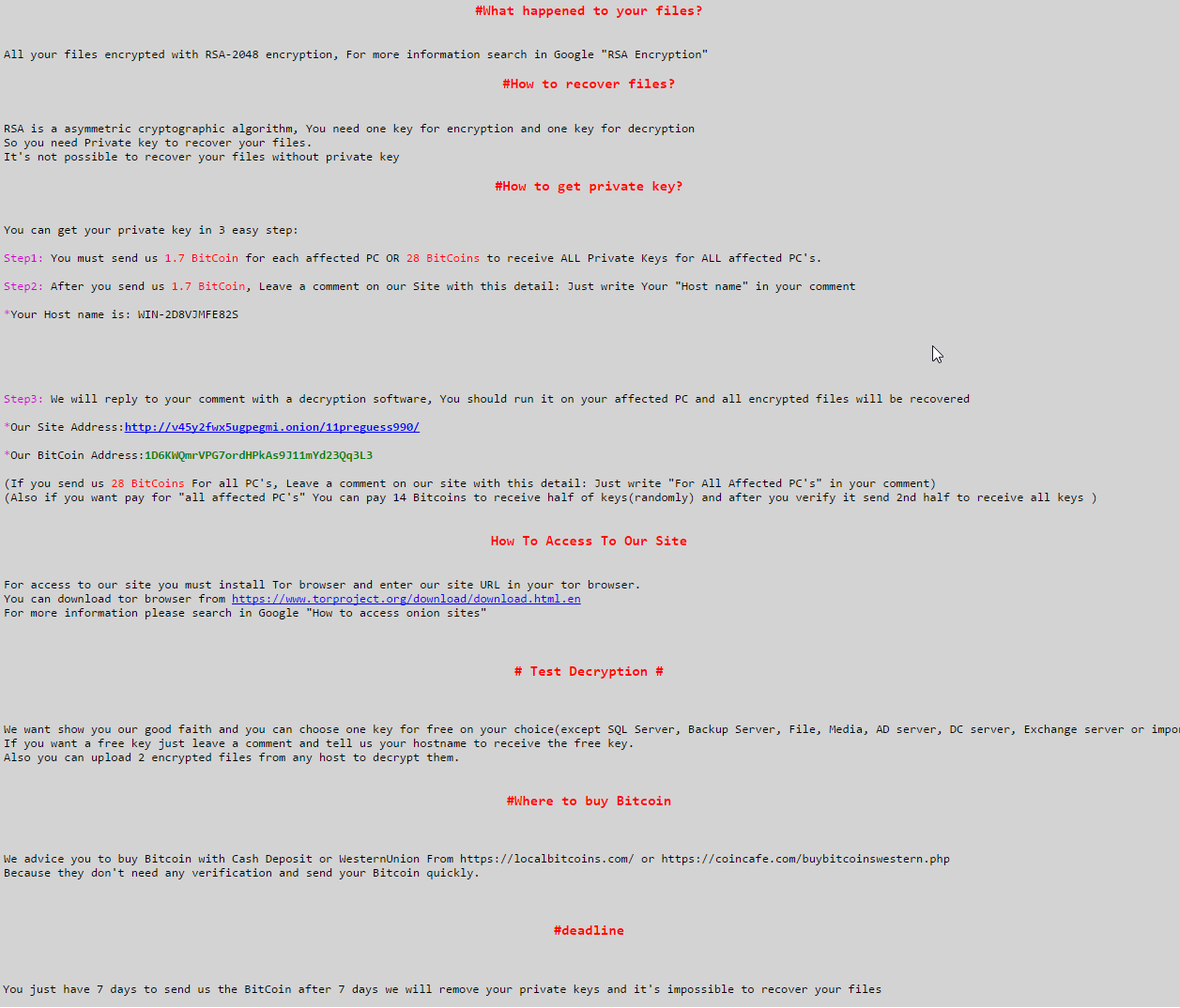
SAMSAM has been updated with a new variant (detected by Trend Micro as RANSOM_SAMAS.I).The previous version made waves in 2016 after it targeted vulnerable hospital servers. Traditionally, ransomware spreads through social engineering, malvertisments, or spam—SAMSAM set itself apart when it targeted the network infrastructure of certain healthcare facilities. The threat actors behind this ransomware gain access to the administrative rights of a network and pinpoint specific target hosts. They deploy to a sizeable portion of the victim’s network, causing essential systems and services to shut down, leaving the target facility little choice but to pay the ransom.
This is one of the latest variants of SAMSAM, though this ransomware family constantly changes its behavior when its threat indicators or IOCs are made public.
Leveraging GoLang
The first ransomware to be written in Google’s Go programming language was detected late last year, and now we have another to add to the list. Apart from the programming language used, BrainCrypt (detected by Trend Micro as RANSOM_BRAINCRYPT) is a relatively standard ransomware. There are no specific details in the ransom note, just simple instructions explaining the situation and telling the victim to email the threat actors.
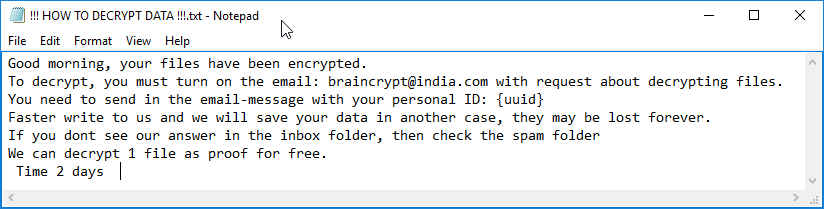
Figure 3. The ransom note from BrainCrypt
The continuing evolution of ransomware shows how cybercriminals quick to adopt the latest technology and techniques to make their malware more effective. Because of this, all users should stay vigilant and updated on the latest threat developments.
Ransomware Solutions:
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevents ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
последний
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation