It’s that time of year again – our researchers have analyzed and reviewed the threats and attacks that occurred during the first half of 2021. Our report, Attacks From All Angles: 2021 Midyear Security Roundup, highlights many of the active attacks we saw, from APTs to ransomware to zero-day exploits.
I’d like to highlight an area where we are seeing increased activity: attacks against cloud infrastructures. I’ve spoken on this at a few events and asked my audiences how many have active cloud infrastructure projects going on, the answer is always most of them.
In our 1H’ 2021 Cyber Risk Index, we asked organizations what their top infrastructure risks are. Cloud security has been in the top two for the last few years. Obviously, many organizations are moving quickly to the cloud and, as such, need to be thinking about how to secure it. Below is an overview of what we’re seeing in cloud attacks.
Threats Impacting Cloud Environments
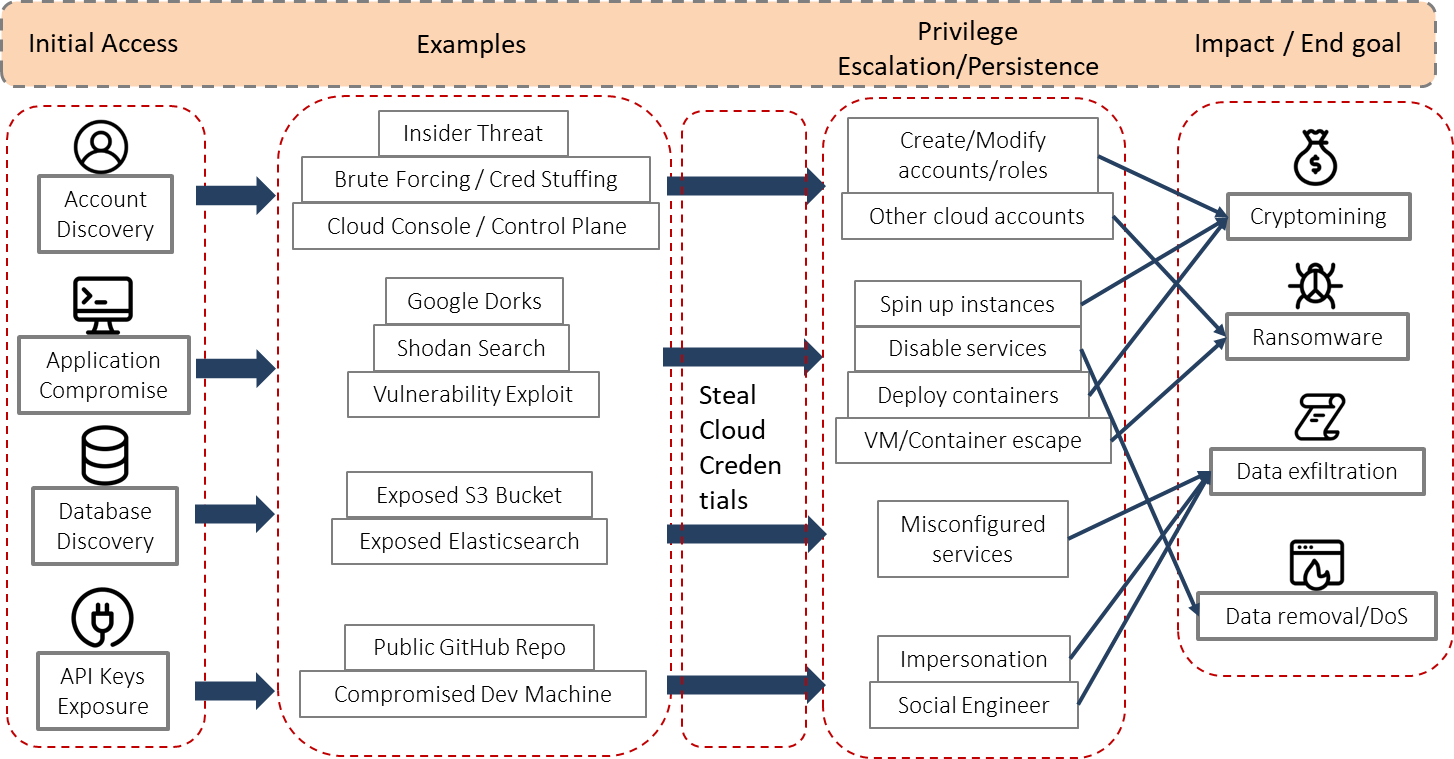
In our first half report, we highlight an APT group named TeamTNT that has been targeting clouds for quite a while now. They have focused most of their efforts on planting crypto-mining malware on cloud servers in an effort to mine Monero coins, but we have also seen them utilize DDoS IRC bots, steal cloud account credentials, and exfil data. As you can see from the above diagram, all of these are end goals for most attacks.
Speaking of data exfil, in the first half we saw APT actors utilize cloud-based file storage to exfiltrate their stolen data. For example, we found that Conti operators use the cloud storage synchronization tool Rclone to upload files to the Mega cloud storage service. Similarly, DarkSide operators used Mega client for exfiltrating files to cloud storage, 7-Zip for archiving, and PuTTY application for network file transfers. This use of known, legitimate tools is not new; we call that “living off the land” and have seen this tactic pick up recently, including usage by ransomware actors. Many organizations now need to look at ways of monitoring legitimate tools usage within their networks to identify any malicious uses.
Cloud Security Architecture
When developing your cloud security architecture and strategy, it is important to always keep the ends in mind. In this case, what are the motivation and end goals of an attacker?
As you see in the image above, most cloud attacks are going to fall into one of these areas. Depending on what you are doing as part of your cloud infrastructure, you should be able to identify if any or all of these end goals could be targeted in your environment. From there, you can work backwards to develop your strategy for protecting those initial access areas tied to the different attacks.
A challenge many organizations face is that the cloud isn’t simple, and many of the technologies that make up the cloud are new, with new features being deployed all the time. Understanding how these work and – more importantly – how to secure them can be very difficult. Utilizing a security platform approach can help build your cloud to be more secure, but educating your architects and administrators will also help. One key area is hardening your cloud account credentials, as these will be regularly targeted by malicious actors. Using multi-factor authentication to access all accounts can minimize this risk tremendously. Take a look at Trend Micro Cloud One, part of our complete cybersecurity platform, to learn more.
The cloud is only one aspect of our full 1H 2021 report. To get more details on all the different threats and attacks we observed, download and read the full report here.

