Ransom.Win32.CELANCYC.SMYXDJA
Ransom:Win64/BlackShadow.YAA!MTB (MICROSOFT)
Windows


Threat Type: Ransomware
Destructiveness: No
Encrypted: No
In the wild: Yes
OVERVIEW
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
It drops files as ransom note. It avoids encrypting files with the following file extensions.
TECHNICAL DETAILS
Arrival Details
This Ransomware arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Ransomware drops the following files:
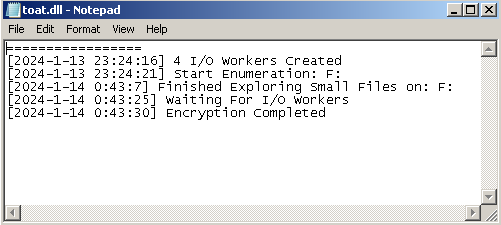
- {Malware Path}\toat.dll → text file containing logs of the ransomware
It drops and executes the following files:
- %ProgramData%\tkec.exe → if the parameter "-power {restart | shutdown}" is used
- It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Global/FSWiper
- It drops the following files after encryption:
- {Drive Letter}:\0F3LWP.tmp
- Its size increases by 524,288 bytes continuously by padding.
- If the drive has no enough free space left, it deletes the file afterwards.
- It accepts the following parameters:
- /RESTART → enables restarting the system
- /SHUTDOWN → enables turning off the system
- It adds the following processes:
- cmd.exe /c ping 127.0.0.1 -n 5 > nul & del "%ProgramData%\tkec.exe" → deletes itself after approximately 5 seconds if no parameter is used
- cmd.exe /c ping 127.0.0.1 -n 5 > nul & del "%ProgramData%\tkec.exe" & shutdown /r /t 0 → deletes itself and restarts the system after approximately 5 seconds if /RESTART parameter is used
- cmd.exe /c ping 127.0.0.1 -n 5 > nul & del "%ProgramData%\tkec.exe" & shutdown /s /t 0 → deletes itself and turns off the system after approximately 5 seconds if /SHUTDOWN parameter is used
- It adds the following mutexes to ensure that only one of its copies runs at any one time:
(Note: %ProgramData% is a version of the Program Files folder where any user on a multi-user computer can make changes to programs. This contains application data for all users. This is usually C:\ProgramData on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit), or C:\Documents and Settings\All Users on Windows Server 2003(32-bit), 2000(32-bit) and XP.)
It adds the following processes:
- "%System%\cmd.exe" /c SCHTASKS.exe /Create /RU "NT AUTHORITY\SYSTEM" /sc onstart /TN "Windows Update BETA" /TR "'{Malware Path}\{Malware Filename}' {Parameters | Empty}" /F → creates a scheduled task for persistence and if the parameter "path {Path}" is not used
- "%System%\cmd.exe" /c rd /s /q P:\$RECYCLE.BIN,Q:\$RECYCLE.BIN,R:\$RECYCLE.BIN,S:\$RECYCLE.BIN,T:\$RECYCLE.BIN,U:\$RECYCLE.BIN,V:\$RECYCLE.BIN,W:\$RECYCLE.BIN,X:\$RECYCLE.BIN,F:\$RECYCLE.BIN,G:\$RECYCLE.BIN,K:\$RECYCLE.BIN,L:\$RECYCLE.BIN,M:\$RECYCLE.BIN,N:\$RECYCLE.BIN,O:\$RECYCLE.BIN,Y:\$RECYCLE.BIN,Z:\$RECYCLE.BIN,A:\$RECYCLE.BIN,B:\$RECYCLE.BIN,C:\$RECYCLE.BIN,D:\$RECYCLE.BIN,E:\$RECYCLE.BIN,H:\$RECYCLE.BIN,I:\$RECYCLE.BIN,J:\$RECYCLE.BIN → empties Recycle Bin in drives A: - Z: when running on Windows Vista or newer versions
- "%System%\cmd.exe" /c rd /s /q P:\Recycler,Q:\Recycler,R:\Recycler,S:\Recycler,T:\Recycler,U:\Recycler,V:\Recycler,W:\Recycler,X:\Recycler,F:\Recycler,G:\Recycler,K:\Recycler,L:\Recycler,M:\Recycler,N:\Recycler,O:\Recycler,Y:\Recycler,Z:\Recycler,A:\Recycler,B:\Recycler,C:\Recycler,D:\Recycler,E:\Recycler,H:\Recycler,I:\Recycler,J:\Recycler → empties Recycle Bin in drives A: - Z: when running on Windows XP or older versions
- powershell -inputformat none -outputformat none -NonInteractive -Command Remove -Item 'd:\$RECYCLE.BIN','c:\$RECYCLE.BIN' -Recurse -Force → empties Recycle Bin in drives C: and D: when running on Windows Vista or newer versions
- "%System%\cmd.exe" /c FOR / F "delims=" %I IN ('WEVTUTIL EL') DO (WEVTUTIL CL "%I") → clears all event logs
- "%System%\cmd.exe" /c vssadmin.exe delete shadows /all /quiet&&wbadmin delete catalog -quiet && bcdedit.exe /set {current} nx AlwaysOff && wmic SHADOWCOPY DELETE → deletes all shadow copies and backup catalog, and disables Data Execution Prevention (DEP) security feature
- "%System%\cmd.exe" /c powershell -inputformat none -outputformat none -NonInteractive -Command Add-MpPreference -ExclusionPath "%s" → adds an exclusion path to the preferences of Windows Defender
- "%System%\cmd.exe" /c powershell -inputformat none -outputformat none -NonInteractive -Command Remove-WindowsFeature Windows-Defender&&powershell -inputformat none -outputformat none -NonInteractive -Command Windows-Defender-GUI&&powershell -inputformat none -outputformat none -NonInteractive -Command New-ItemProperty -Path "HKLM:SOFTWAREPoliciesMicrosoftWindows Defender" -Name DisableAntiSpyware -Value 1 -PropertyType DWORD -Force → attempts to remove Windows Defender feature and disables Windows Defender anti-spyware functionality through registry modification
- "%System%\cmd.exe" /c powershell -inputformat none -outputformat none -NonInteractive -Command Get-Service WinDefend | Stop-Service -PassThru | Set-Service -StartupType Disabled&&powershell -inputformat none -outputformat none -NonInteractive -Command Set-MpPreference -DisableRealtimeMonitoring $true → disables Windows Defender service and Windows Defender real-time monitoring
- "%System%\cmd.exe" /c SCHTASKS.exe /Delete /TN "Windows Update BETA" /F → deletes the created scheduled task named Windows Update BETA after encryption
- "%System%\cmd.exe" /c ping 127.0.0.1 -n 5 > nul & del "{Malware Path}\{Malware Filename}" → deletes itself after approximately 5 seconds if the parameter "-nodel" is not used
- "%System%\cmd.exe" /c "%ProgramData%\tkec.exe" /RESTART → if the parameter "-power restart" is used
- "%System%\cmd.exe" /c "%ProgramData%\tkec.exe" /SHUTDOWN → if the parameter "-power shutdown" is used
(Note: %System% is the Windows system folder, where it usually is C:\Windows\System32 on all Windows operating system versions.. %ProgramData% is a version of the Program Files folder where any user on a multi-user computer can make changes to programs. This contains application data for all users. This is usually C:\ProgramData on Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) and 10(64-bit), or C:\Documents and Settings\All Users on Windows Server 2003(32-bit), 2000(32-bit) and XP.)
It adds the following mutexes to ensure that only one of its copies runs at any one time:
- Global\TisakMutex
Other System Modifications
This Ransomware uses Windows Management Instrumentation (WMI) to delete volume shadow copies:
- SELECT * FROM Win32_ShadowCopy where Win32_ShadowCopy.ID={Shadow Copy ID}
Other Details
This Ransomware does the following:
- It enables the following privileges to allow access to restricted actions in the system:
- SeDebugPrivilege
- SeRestorePrivilege
- SeBackupPrivilege
- SeTakeOwnershipPrivilege
- SeAuditPrivilege
- SeSecurityPrivilege
- SeIncreaseBasePriorityPrivilege
- It empties the Recycle Bin of all drives.
- It terminates the running process of a file and its related files before encrypting it.
- It avoids terminating the following processes if found running in the affected system's memory:
- nativeproxy
- googledrivesync
- AnyDesk
- TeamViewer
- Yandex
- googledrive
- OneDrive
- DropBox
- GoogleDriveFS
- YandexDisk2
- Kerio
- VPN Client
- Radmin
It accepts the following parameters:
- -path {Path} → encrypts all files in the specified path
- -skip {Bytes} → number of bytes to be skipped during encryption
- -power {restart | shutdown} → restarts or turns off the system after encryption
- -nomutex → does not create a mutex
- -nonetdrive → excludes network drive from encryption
- -nodel → skips deleting the malware itself after encryption
- -priority {on | any string} → specifies the priority level of the ransomware
- on → enables the priority setting
- any string → disables the priority setting
- -mode {full | fast | split | custom} → encryption settings
- full → encrypts all data of each of the files
- fast → encrypts only the first 1,048,576 bytes of data of each of the files
- split → encrypts each file from a specific offset and requires the "-skip" parameter
- custom → encrypts each file using a custom offset range and requires the "-skip" parameter
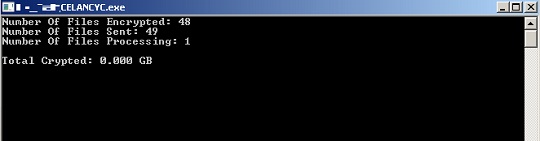
- -console → shows a console window containing encryption details:
It adds the following scheduled tasks:
- If the parameter "-path {Path}" is not used
- Location: {Scheduled Task Root Directory}
Name: Windows Update BETA
Trigger: At startup
Action: Start a program → {Malware Path}\{Malware Filename} {Parameters | Empty}
- Location: {Scheduled Task Root Directory}
Ransomware Routine
This Ransomware avoids encrypting files with the following strings in their file name:
- BOOTNXT
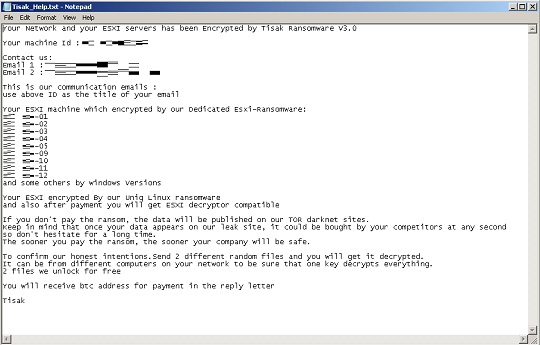
- Tisak_Help.txt
- WinSCP.ini
- YandexDisk2.exe
- autorun.inf
- boot.ini
- bootfont.bin
- bootmgr
- bootsect.bak
- desktop.ini
- iconcache.db
- ntldr
- ntuser.dat
- ntuser.dat.log
- ntuser.ini
- rdp
- thumbs.db
- tkec.exe
- toat.dll
- tvb.mp
It avoids encrypting files found in the following folders:
- $RECYCLE.BIN
- $Windows.~bt
- $windows.~ws
- .sync
- AVAST Software
- AVG
- All Users
- Anydesk
- Boot
- BrowserManager
- Cisco
- Comms
- Config.Msi
- DVD Maker
- Default
- Drive File Stream
- DriveFS
- EPSON Software
- ESET
- Foxit Reader
- Foxit Software
- InstallShield Installation Information
- Intel
- Internet Explorer
- JC - WebClient
- KMSAuto
- KMSAutoS
- Kaspersky Lab
- Kerio
- MSBuild
- MSOCache
- MegaRAID Storage Manager
- Microsoft Analysis Services
- Microsoft Help
- Microsoft OneDrive
- Microsoft SDKs
- Microsoft Visual Studio 16.0
- Microsoft Visual Studio 8
- Microsoft.NET
- Mozilla
- Mozilla Firefox
- Opera
- Opera Software
- Package Cache
- PerfLogs
- Radmin Viewer 3
- RaiDrive
- Reference Assemblies
- SearchBand
- SoftwareDistribution
- System Volume Information
- USOPrivate
- USOShared
- Uninstall Information
- VPN Client
- Web Components
- WinSCP
- Windows
- Windows Defender
- Windows Journal
- Windows Photo Viewer
- Windows Portable Devices
- Windows Sidebar
- WindowsApps
- WindowsPowerShell
- WireGuard
- Yandex.Disk.2
- Yandex.Notes
- Yandex.Telemost
- YandexBrowser
- YandexDisk2
- microsoft
- qmlcache
- radmin
- tor browser
- windows nt
- windows.old
- yapin
It appends the following extension to the file name of the encrypted files:
- .Tisak
It drops the following file(s) as ransom note:
- {Path to Encrypt}\Tisak_Help.txt
It avoids encrypting files with the following file extensions:
- .386
- .Tisak
- .adv
- .ani
- .bat
- .cab
- .cmd
- .com
- .cpl
- .cur
- .deskthemepack
- .diagcab
- .diagcfg
- .diagpkg
- .dll
- .drv
- .exe
- .hlp
- .hta
- .icl
- .icns
- .ico
- .ics
- .idx
- .ldf
- .lnk
- .lock
- .mod
- .mpa
- .msc
- .msi
- .msp
- .msstyles
- .msu
- .nls
- .nomedia
- .ocx
- .pdb
- .prf
- .ps1
- .rdp
- .rom
- .rtp
- .scr
- .search-ms
- .shs
- .spl
- .sys
- .theme
- .themepack
- .wpx
SOLUTION
Step 1
Trend Micro Predictive Machine Learning detects and blocks malware at the first sign of its existence, before it executes on your system. When enabled, your Trend Micro product detects this malware under the following machine learning name:
- TROJ.Win32.TRX.XXPE50FFF075
Step 2
Before doing any scans, Windows 7, Windows 8, Windows 8.1, and Windows 10 users must disable System Restore to allow full scanning of their computers.
Step 3
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 4
Restart in Safe Mode
Step 5
Deleting Scheduled Tasks while in Safe Mode
- Still in safe mode, the following {Task Name}-{Task to be run} listed should be used in the steps identified below:
- {Task Name}: Windows Update BETA
- {Task to be run}: Start a program → {Malware Path}\{Malware Filename} {Parameters | Empty}
- For Windows 7 and Server 2008 (R2) users, click Start>Computer.
- For Windows 8, 8.1, 10, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
- %System%\Tasks\{Task Name}
- Once located, select the file then press SHIFT+DELETE to delete it.
- Open Registry Editor. To do this:
- For Windows 7 and Server 2008 (R2) users, click the Start button, type regedit in the Search input field, and press Enter.
- For Windows 8, 8.1, 10, and Server 2012 (R2) users, right-click on the lower left corner of the screen, click Run, type regedit in the text box
- In the left panel of the Registry Editor window, double-click the following:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tree>{Task Name}
- Locate the created entry and take note of the registry value's data:
- ID={Task Data}
- After taking note of the data, delete the registry key:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tree>{Task Name}
- In the left panel of the Registry Editor window, double-click the following:
- HKEY_LOCAL_MACHINE>SOFTWARE>Microsoft>Windows NT>CurrentVersion>Schedule>TaskCache>Tasks
- Still in the left panel, locate and delete the registry key with the same name as the located Task Data in step #6:
- ={Task Data}
- Close Registry Editor.
Step 6
Search and delete these files
- {Malware Path}\toat.dll
- %ProgramData%\tkec.exe
- {Drive Letter}:\0F3LWP.tmp
- {Encrypted Paths}\Tisak_Help.txt
Step 7
Restart in normal mode and scan your computer with your Trend Micro product for files detected as Ransom.Win32.CELANCYC.SMYXDJA. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 8
Restore encrypted files from backup.
Did this description help? Tell us how we did.


