PUA.Win64.PCHunter.A
Windows

Threat Type:
Potentially Unwanted Application
Destructiveness:
No
Encrypted:

In the wild::
Yes
OVERVIEW
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Elimina archivos para impedir la ejecución correcta de programas y aplicaciones.
Se conecta a un sitio Web para enviar y recibir información.
TECHNICAL DETAILS
Detalles de entrada
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Instalación
Este malware infiltra el/los siguiente(s) archivo(s):
- {Malware Path}\{Malware Filename}ak.sys
Técnica de inicio automático
Elimina las siguientes claves de registro asociadas a aplicaciones antivirus y de seguridad:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\{Malware Filename}ak
Otras modificaciones del sistema
Elimina los archivos siguientes:
- {Malware Path}\{Malware Filename}ak.sys
Agrega las siguientes entradas de registro:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\{Malware Filename}ak
Type = 1
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\{Malware Filename}ak
ErrorControl = 1
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\{Malware Filename}ak
Start = 1
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\
services\{Malware Filename}ak
ImagePath = \??\{Malware Path}\{Malware Filename}ak.sys
Rutina de puerta trasera
Se conecta a los sitios Web siguientes para enviar y recibir información:
- http://www.ep{BLOCKED}t.com
- http://www.e{BLOCKED}t.com/PCHunter_StandardV1.4={MAC Address}
- http://www.e{BLOCKED}t.com/pchunter/pchunter_free
- {BLOCKED}.{BLOCKED}.158.231
Robo de información
Recopila los siguientes datos:
- MAC Address
- Running Processes
- Computer Files
- User Accounts
- System Registries
- Process Modules
- Kernel Modules
- Startup Information
- Network Connections
- Firewall Rules
Otros detalles
Hace lo siguiente:
- It loads the dropped file as a driver
- {Malware Path}\{Malware Filename}ak.sys
- It displays the following image:
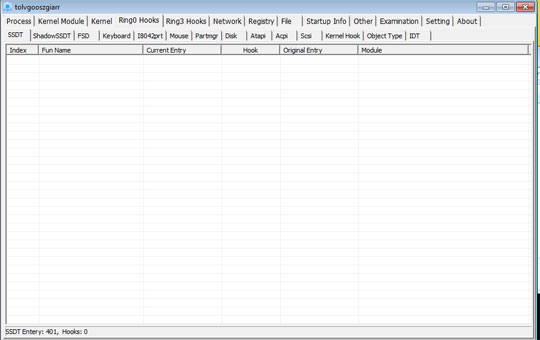
- It can view and display system process and process threads
- It can terminate, suspend and resume processes and threads
- It displays current network connections, including the local and remote addresses and state of TCP connections
- It displays and can edit system registry
- It displays and can delete files and folders
- It can view file properties information
- It displays autorun entries
- It can delete and edit autorun entries
- It displays and can delete user accounts
- It displays affected machine’s firewall rules
- It can delete a firewall rule
SOLUTION
Step 1
Los usuarios de Windows ME y XP, antes de llevar a cabo cualquier exploración, deben comprobar que tienen desactivada la opción Restaurar sistema para permitir la exploración completa del equipo.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Reiniciar en modo seguro
Step 4
Eliminar este valor del Registro
Importante: si modifica el Registro de Windows incorrectamente, podría hacer que el sistema funcione mal de manera irreversible. Lleve a cabo este paso solo si sabe cómo hacerlo o si puede contar con ayuda de su administrador del sistema. De lo contrario, lea este artículo de Microsoft antes de modificar el Registro del equipo.
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\{Malware Filename}ak
- Type = 1
- Type = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\{Malware Filename}ak
- ErrorControl = 1
- ErrorControl = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\{Malware Filename}ak
- Start = 1
- Start = 1
- In HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\{Malware Filename}ak
- ImagePath = \??\{Malware Path}\{Malware Filename}ak.sys
- ImagePath = \??\{Malware Path}\{Malware Filename}ak.sys
Step 5
Explorar el equipo con su producto de Trend Micro para eliminar los archivos detectados como PUA.Win64.PCHunter.A En caso de que el producto de Trend Micro ya haya limpiado, eliminado o puesto en cuarentena los archivos detectados, no serán necesarios más pasos. Puede optar simplemente por eliminar los archivos en cuarentena. Consulte esta página de Base de conocimientos para obtener más información.
Did this description help? Tell us how we did.