Disk-Locking HDDCryptor/Mamba Ransomware Makes a Comeback
 A variant of the disk-encrypting ransomware HDDCryptor (detected by Trend Micro as RANSOM_HDDCRYPTOR.AUSE) reportedly infected a number of victims in Brazil and Saudi Arabia. This is the same family of disk-encrypting malware that hit San Francisco Municipal Transportation Agency (SFMTA) in November, 2016, forcing the public transport system to use hand-written route assignments and open the fare gates to prevent disruption.
A variant of the disk-encrypting ransomware HDDCryptor (detected by Trend Micro as RANSOM_HDDCRYPTOR.AUSE) reportedly infected a number of victims in Brazil and Saudi Arabia. This is the same family of disk-encrypting malware that hit San Francisco Municipal Transportation Agency (SFMTA) in November, 2016, forcing the public transport system to use hand-written route assignments and open the fare gates to prevent disruption.
HDDCryptor, also known as Mamba, first emerged in September last year. It can encrypt resources in network shares—drives, folders, files, printers, and serial ports via Server Message Block (SMB). It misuses a miscellany of freeware, open-source and commercially available software to scramble disks and mounted SMB drives, and locks the infected machine’s hard drive by overwriting its Master Boot Record (MBR) with a modified bootloader. Once an infected system restarts, it displays the ransom note instead of the normal log-in screen.
[From Trendlabs Security Intelligence Blog: A technical analysis of HDDCryptor]
Its infection vector is reminiscent of other families like Crysis and Erebus Linux ransomware that leveraged exploits to gain unauthorized administrator-level access to machines before the malware is dropped and executed. By late November, HDDCryptor was updated with more streamlined encryption routine as well as anti-sandbox and anti-debugging features to evade antivirus and other detection techniques better.
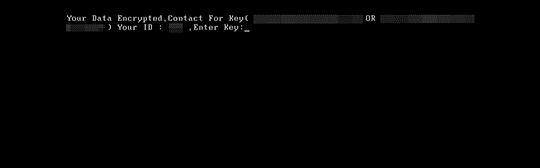
HDDCryptor modifies the infected system’s MBR to display a ransom note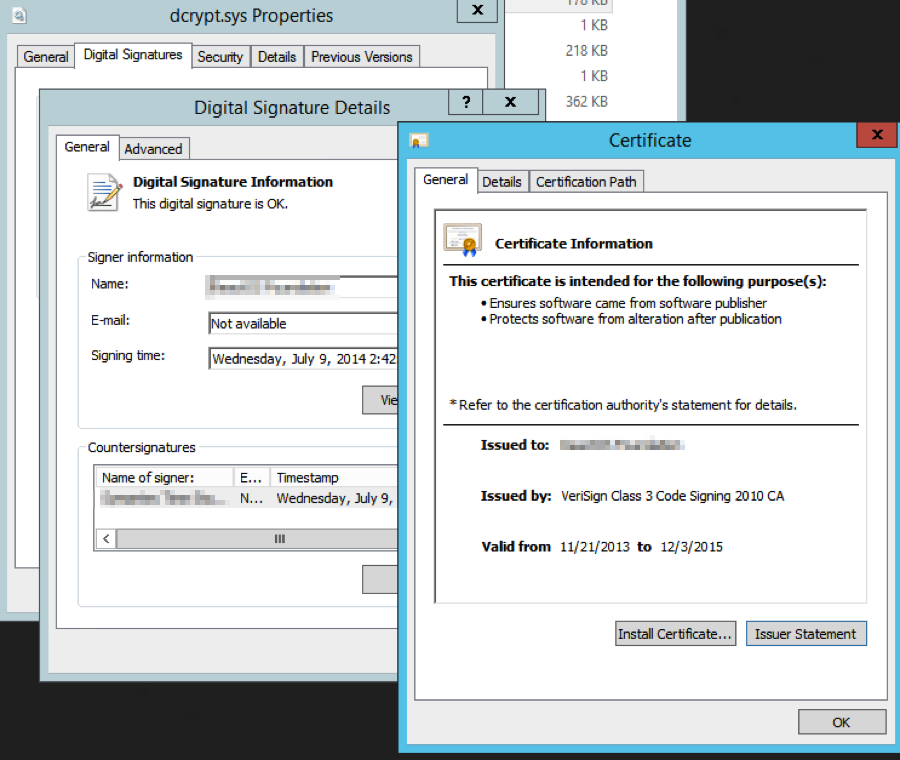
Certificate and signature properties of the open-source disk encryption software DiskCryptor, one of the tools HDDCryptor abuses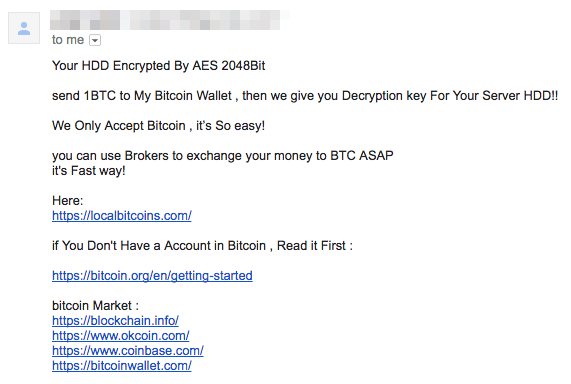
A sample email message from one of HDDCryptor’s operators that includes a ransom demand and instructions on how to pay with bitcoin
[READ: How HDDCryptor evolved]
Like Petya, the new variant of HDDCryptor employed PsExec to execute the ransomware on the compromised system. Of note are its changeable random demands; unlike other ransomware with fixed ransom amounts, HDDCryptor’s operators adjust the payment they demand from victims depending on the scale of infection. The feature was exemplified in the SFMTA attack, where the attackers extorted $73,000 worth of bitcoins instead.
HDDCryptor’s reemergence is a reflection of ransomware’s maturity in the threat landscape: more hard-hitting impact, targeted in scope, diverse in approach. And as echoed by the likes of WannaCry, Petya, and SOREBRECT families, there’s also the upward trend of abusing legitimate system and open-source tools. Another sign of increasing sophistication can be seen in the way attackers rehash leaks and dumps, like those released by the Shadow Brokers group, repurposing them to destructive effect.
As cybercriminals increasingly turn to targeting businesses for profit, enterprises must be equally proactive in securing their assets and platforms from which their mission-critical data change hands. Reduce your attack surface by adopting best practices against ransomware: regularly patch and secure the applications and gateways used, enforce the principle of least privilege, strengthen your credentials, and harden your remote connections. Additionally, restrict or disable administration tools (i.e. PsExec, PowerShell) to systems that do not need it. There is no silver bullet for addressing threats like ransomware, which is why implementing defense in depth—multilayered security countermeasures—is recommended.
Trend Micro Ransomware Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by ransomware. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro™ Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimize the impact of this threat. Trend Micro™ Deep Discovery Inspector™ detects and blocks ransomware on networks, while Trend Micro™ Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro™ Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware. For home users, Trend Micro™ Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of our free tools such as the Trend Micro™ Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Messages récents
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation