WannaCry/Wcry Ransomware: How to Defend against It
An unprecedented wave of ransomware infections is hitting organizations in all industries around the world. The culprit: the WannaCry/WCry ransomware (detected by Trend Micro as RANSOM_WANA.A and RANSOM_WCRY.I).
Trend Micro has been tracking WannaCry since its emergence in the wild in April 2017. Trend Micro™ XGen™ security has been protecting users from this and other threats using techniques like behavioral analysis and high fidelity machine learning. Here’s what users and enterprises need to know about this widespread threat and what can be done to defend against it.
What happened?
Several firms in Europe were the first to report having their mission-critical Windows systems locked, showing a ransom note. This quickly developed into one of the most widespread ransomware outbreaks currently affecting a large number of organizations around the world. Some affected organizations had to take their IT infrastructure offline, with victims in the healthcare industry experiencing delayed operations and forced to turn away patients until processes could be re-established.
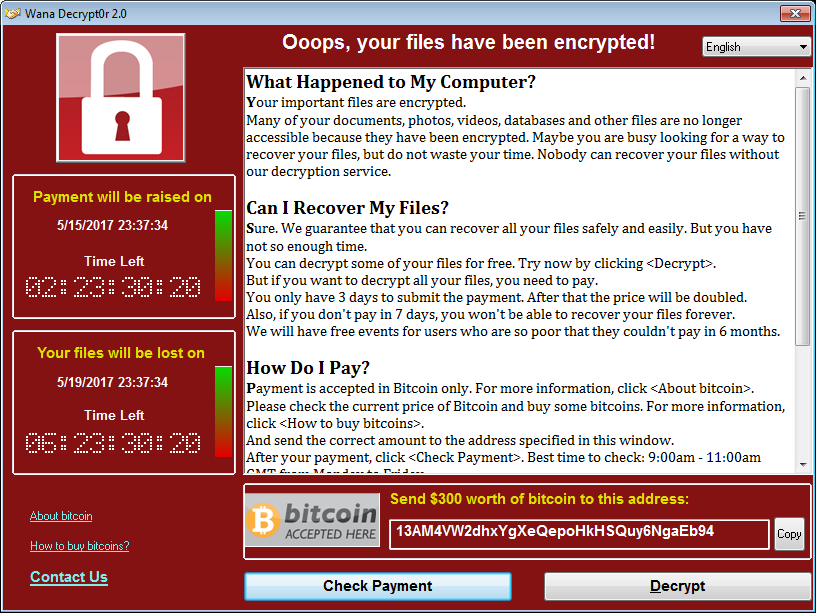
Figure 1: One of WannaCry’s ransom notes
Who is affected?
This variant of the WannaCry ransomware attacks older Windows-based systems, and is leaving a trail of significant damage in its wake. Based on Trend Micro’s initial telemetry, Europe has the highest detections for the WannaCry ransomware. The Middle East, Japan, and several countries in the Asia Pacific (APAC) region showing substantial infection rates as well.
WannaCry’s infections were seen affecting various enterprises, including those in healthcare, manufacturing, energy (oil and gas), technology, food and beverage, education, media and communications, and government. Due to the widespread nature of this campaign, it does not appear to be targeting specific victims or industries.
[READ: A technical overview of the WannaCry/Wcry ransomware]
What does WannaCry ransomware do?
WannaCry ransomware targets and encrypts 176 file types. Some of the file types WannaCry targets are database, multimedia and archive files, as well as Office documents. In its ransom note, which supports 27 languages, it initially demands US$300 worth of Bitcoins from its victims—an amount that increases incrementally after a certain time limit. The victim is also given a seven-day limit before the affected files are deleted—a commonly used fear-mongering tactic.
WannaCry leverages CVE-2017-0144, a vulnerability in Server Message Block, to infect systems. The security flaw is attacked using an exploit leaked by the Shadow Brokers group—the “EternalBlue” exploit, in particular. Microsoft’s Security Response Center (MSRC) Team addressed the vulnerability via MS17-010 released March, 2017.
What makes WannaCry’s impact pervasive is its capability to propagate. Its worm-like behavior allows WannaCry to spread across networks, infecting connected systems without user interaction. All it takes is for one user on a network to be infected to put the whole network at risk. WannaCry’s propagation capability is reminiscent of ransomware families like SAMSAM, HDDCryptor, and several variants of Cerber—all of which can infect systems and servers connected to the network.
[READ: Shadow Brokers Leaks Hacking Tools: What it Means for Enterprises]
What can you do?
WannaCry highlights the real-life impact of ransomware: crippled systems, disrupted operations, marred reputations, and the financial losses resulting from being unable to perform normal business functions—not to mention the cost of incident response and clean up.
[Infographic: A multilayered defense against ransomware]
Here are some of the solutions and best practices that organizations can adopt and implement to safeguard their systems from threats like WannaCry:
- The ransomware exploits a vulnerability in SMB server. Patching is critical for defending against attacks that exploit security flaws. A patch for this issue is available for Windows systems, including those no longer supported by Microsoft. When organizations can’t patch directly, using a virtual patch can help mitigate the threat
- Deploying firewalls and detection and intrusion prevention systems can help reduce the spread of this threat. A security system that can proactively monitor attacks in the network also helps stops these threats
- Aside from using an exploit to spread, WannaCry reportedly also uses spam as entry point. Identifying red flags on socially engineered spam emails that contain system exploits helps. IT and system administrators should deploy security mechanisms that can protect endpoints from email-based malware
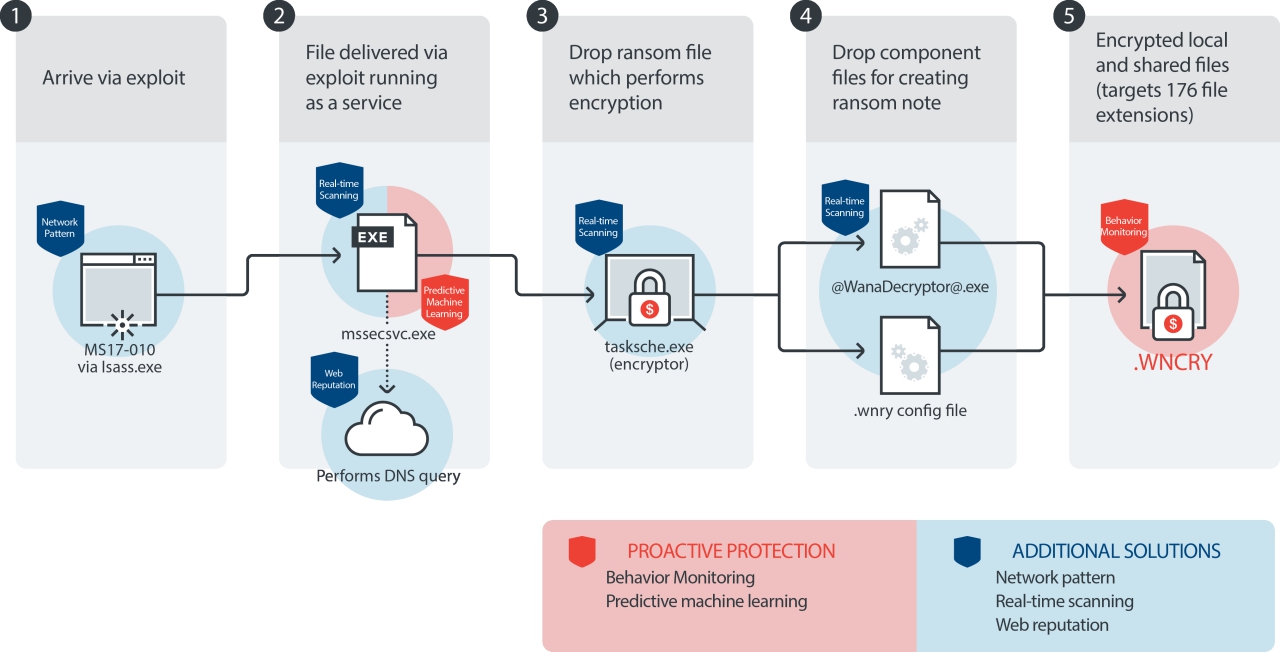
- WannaCry drops several malicious components in the system to conduct its encryption routine. Application control based on a whitelist can prevent unwanted and unknown applications from executing. Behavior monitoring can block unusual modifications to the system. Ransomware uses a number of techniques to infect a system; defenders should do the same to protect their systems
- WannaCry encrypts files stored on local systems and network shares. Implementing data categorization helps mitigate any damage incurred from a breach or attack by protecting critical data in case they are exposed
- Network segmentation can also help prevent the spread of this threat internally. Good network design can help contain the spread of this infection and reduce its impact on organizations
- Disable the SMB protocol on systems that do not require it. Running unneeded services gives more ways for an attacker to find an exploitable vulnerability
Trend Micro XGen Security detects and blocks all of WannaCry ransomware's infection stages
Trend Micro Ransomware Solutions
Enterprises should use a multi-layered approach to mitigate the risks brought threats like ransomware.
Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security can prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–regardless if they’re physical, virtual, or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of Trend Micro’s free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware. Trend Micro Crypto-Ransomware File Decryptor Tool can decrypt files affected by certain crypto-ransomware variants without having to pay the ransom in exchange for the decryption key.
Find more in-depth information on Trend Micro detections and solutions for Trend Micro Deep Security, Vulnerability Protection, TippingPoint, and Deep Discovery Inspector in this technical support page.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One