Access to Corporate Remote Desktops Sold for $3 in the Dark Web
 Security researchers found several dark web marketplaces selling credentials that can access corporate remote desktop protocol (RDP) servers for as little as US$3. The report shed light into a prominent marketplace called Ultimate Anonymity Services (UAS), which has been found selling RDPs sourced from organizations in healthcare, education, and government.
Security researchers found several dark web marketplaces selling credentials that can access corporate remote desktop protocol (RDP) servers for as little as US$3. The report shed light into a prominent marketplace called Ultimate Anonymity Services (UAS), which has been found selling RDPs sourced from organizations in healthcare, education, and government.
Of note are 35,000 brute-forced RDPS being offered, 7,200 of which were from China, 6,100 from Brazil, 3,000 from India, 1,300 from Spain, and 900 from Colombia. UAS purveyors also sold 300 US-based RDPs, namely from California, Ohio, Oregon, and Virginia. Prices range between $3 and $10. Compared to competitors such as xDedic that sell similar wares for as much as $100, the researchers note that UAS’s lower prices owe to its increasing popularity among cybercriminals.
[Related: WannaCry ransomware sold in the Middle Eastern and North African Underground for $50]
The report complements the recent bevy of data breaches and ransomware-related incidents, as access to these systems and networks enables cybercriminals and threat actors to steal or hold data hostage. Brute-forced RDPs were Crysis ransomware’s main infection vector and entry point, for instance. Even point-of-sale malware like MajikPOS combined compromised RDPs with remote access Trojans to steal credit card data, which were then sold in underground forums.
[READ: How your data can be used against you]
Indeed, the underground is rife with illicit wares as well as stolen data and malware that purveyors often rehash depending on the demand. But as exemplified by the Middle Eastern and North African underground, their monetary value can also be influenced by the unique culture that drives its participants.
In fact, several malware and access to certain systems and networks are offered for free in Middle Eastern and North African underground marketplaces. These range from crypters, keyloggers, SQL injection tools, and malware builders to SCADA port numbers. RDPs cost as little as $8, and e-commerce credentials are sold for as little as $1.
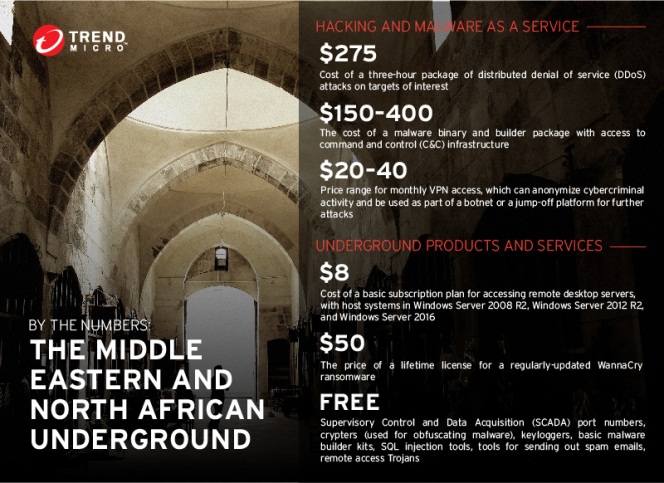
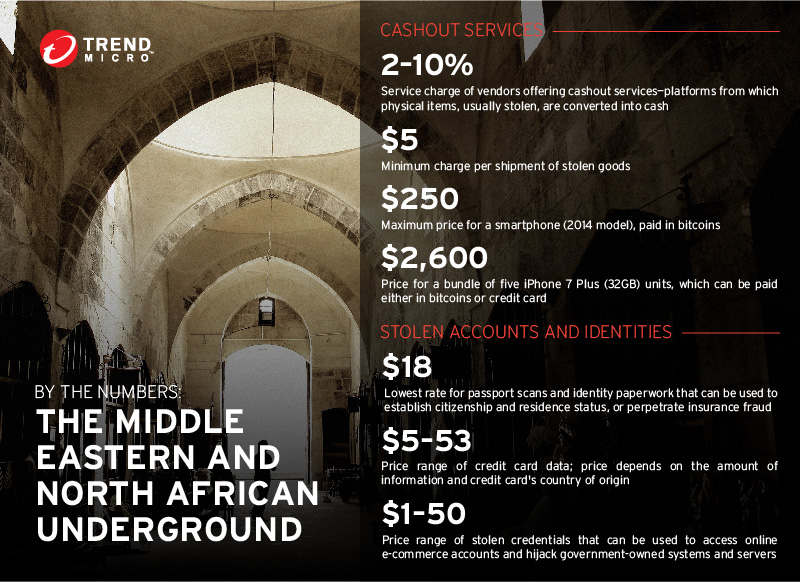
Prices of some of the wares offered in the Middle Eastern and North African underground
[READ: The cybercriminal underground: how the regional underground scenes differ]
Given how compromised remote desktops can be an attacker’s doorway to an organization’s crown jewels, the ease with which attackers find keys to them highlights the significance of securing them. Here are some countermeasures:
- Restrict RDP access if possible, or change RDP ports to non-standard ones, to deter attackers from breaching computers connected to it
- Harden the RDP against brute force attacks: strengthen the credentials used to access them, and implement two-factor authentication, account lockout policies, and user permissions
- Utilize encryption channels to prevent hackers from snooping in on remote connections
- Keep the RDP client and server updated and patched to prevent vulnerabilities from being exploited
- Regularly back up data and ensure its integrity
- Reduce the RDP’s exposure to attacks by disabling or limiting access to shared drives
- Proactively monitor the network for any suspicious activities or red flags such as brute-force logins
Trend Micro Solutions
Trend Micro XGen™ security provides a cross-generational blend of threat defense techniques against a full range of threats for data centers, cloud environments, networks, and endpoints. It features high-fidelity machine learning to secure the gateway and endpoint data and applications, and protects physical, virtual, and cloud workloads. With capabilities like web/URL filtering, behavioral analysis, and custom sandboxing, XGen™ protects against today’s purpose-built threats that bypass traditional controls, exploit known, unknown, or undisclosed vulnerabilities, and either steal or encrypt personally-identifiable data. Smart, optimized, and connected, XGen™ powers Trend Micro’s suite of security solutions: Hybrid Cloud Security, User Protection, and Network Defense.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation