 Download Caught in the Act: Running a Realistic Factory Honeypot to Capture Real Threats
Download Caught in the Act: Running a Realistic Factory Honeypot to Capture Real Threats
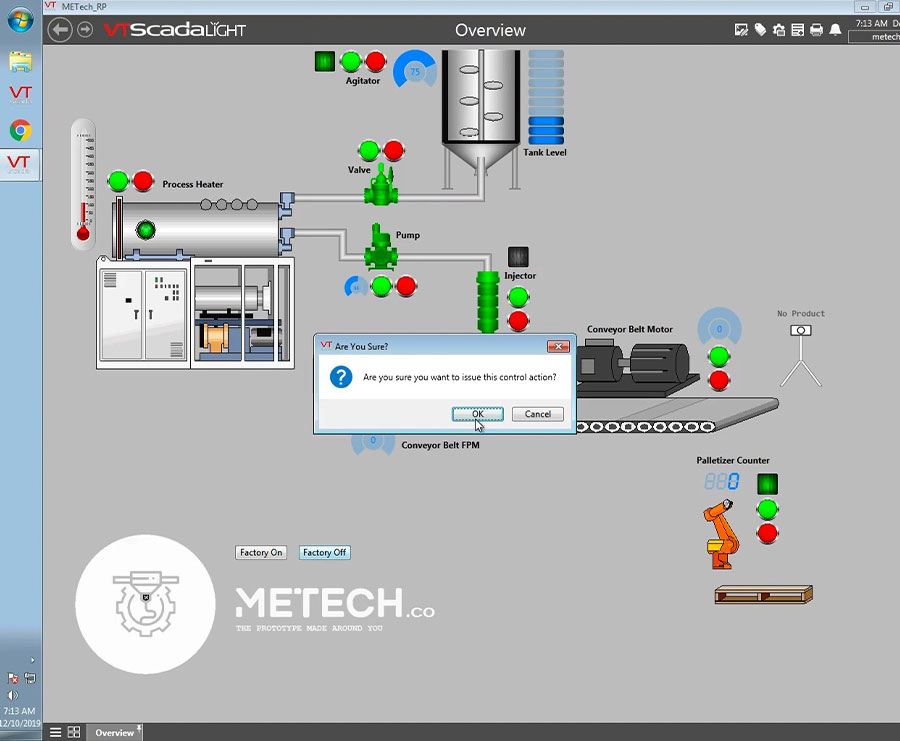
In a fully functioning smart factory, every process must begin and end with precision and uninterrupted operation so that it can weave seamlessly into the facility’s production line. However, behind the normal hum of a smart factory’s day-to-day business lurks the possibility of attacks from threat actors.
To determine how knowledgeable and ingenious threat actors could be in compromising a manufacturing facility, we conducted a research in 2019 that essentially had us simulating a factory of our own. Using our most realistic honeypot to date, we created an environment that could lure cybercriminals into carrying out attacks and at the same time give us an all but unimpeded look at their actions.
We designed our pure-production honeypot to mimic a real system, including programmable logic controllers, a human-machine interface (HMI), and other components of an industrial control system (ICS). We then created a cover company for this faux factory: a rapid prototyping consultancy firm with ostensibly real human employees, working contact channels, and a client base composed of large anonymous organizations from critical industries. This ruse proved effective, as shown by the different types of attacks our honeypot attracted.
Our research paper, “Caught in the Act: Running a Realistic Factory Honeypot to Capture Real Threats,” contains the full details of our honeypot, from its conceptualization to the description of noteworthy attacks we encountered on it. Here we recount some of the highlights of our honeypot’s monthslong run.
Our honeypot went live on May 6. We exposed its HMI machine online through Virtual Network Computing (VNC) without control access and used the same password for several workstations. To further attract attacks, we made our system seem like it had been hacked by posting “leaked” information about it.

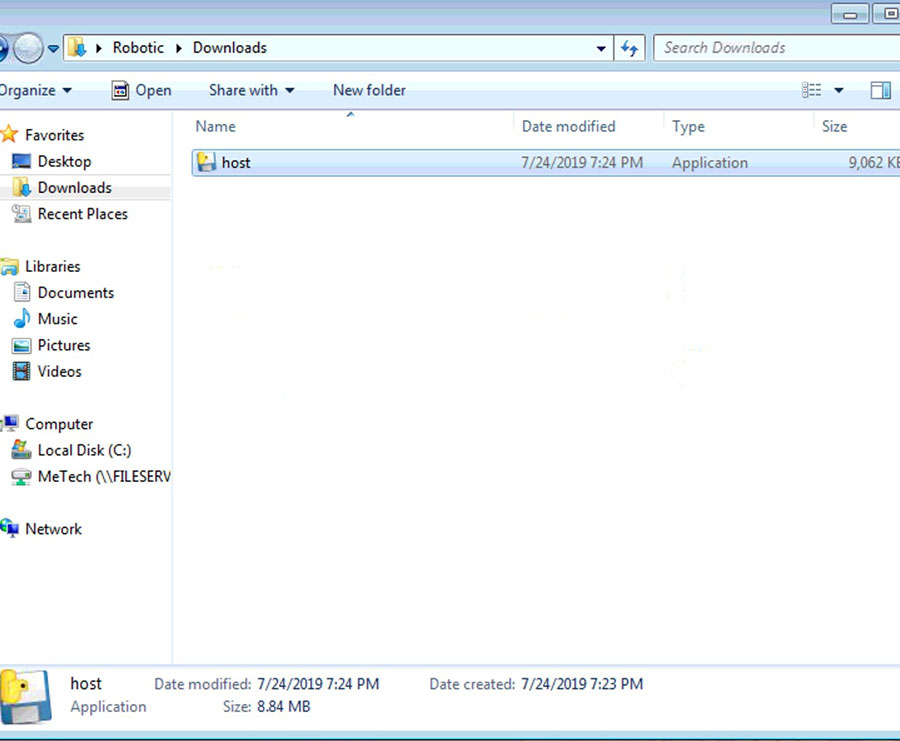
More than two months after going live, on July 24, our efforts began to show some success. An attacker came into the system and downloaded a cryptocurrency miner. Over the next few months, the threat actor behind this attack would keep returning to our system to relaunch their miner.
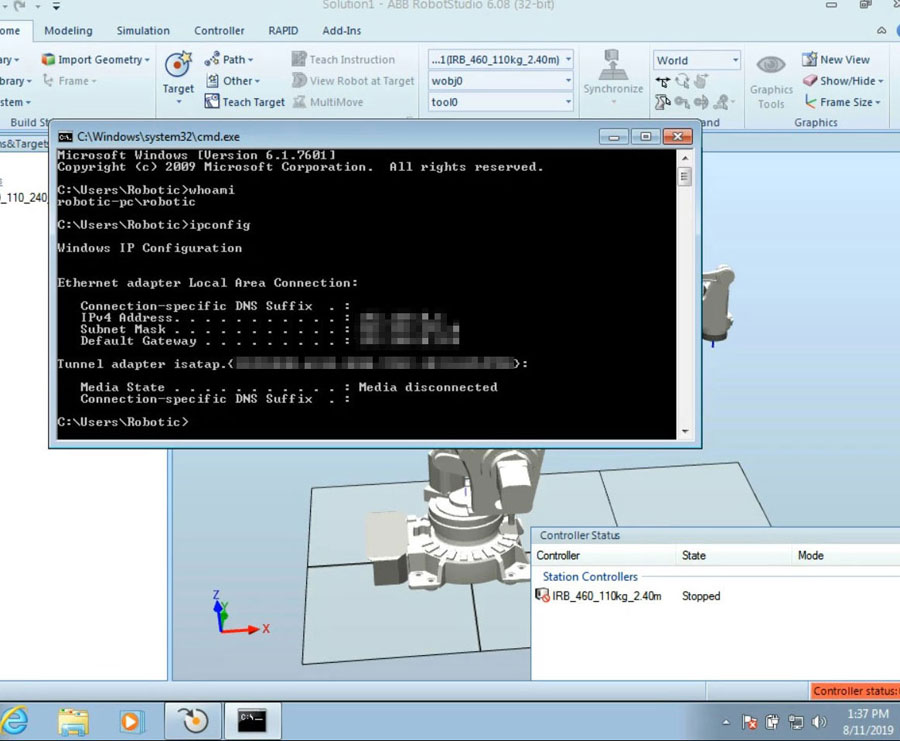
After a few months online, our honeypot had already seen different threat actors entering the system, including ones who performed reconnaissance activities and a few who caused system shutdowns.
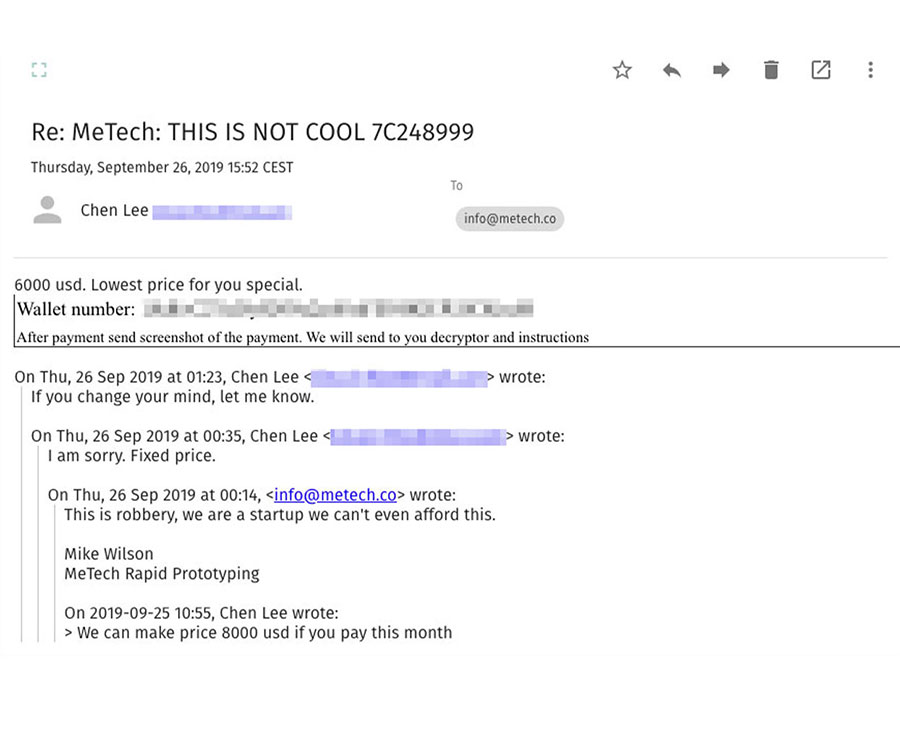
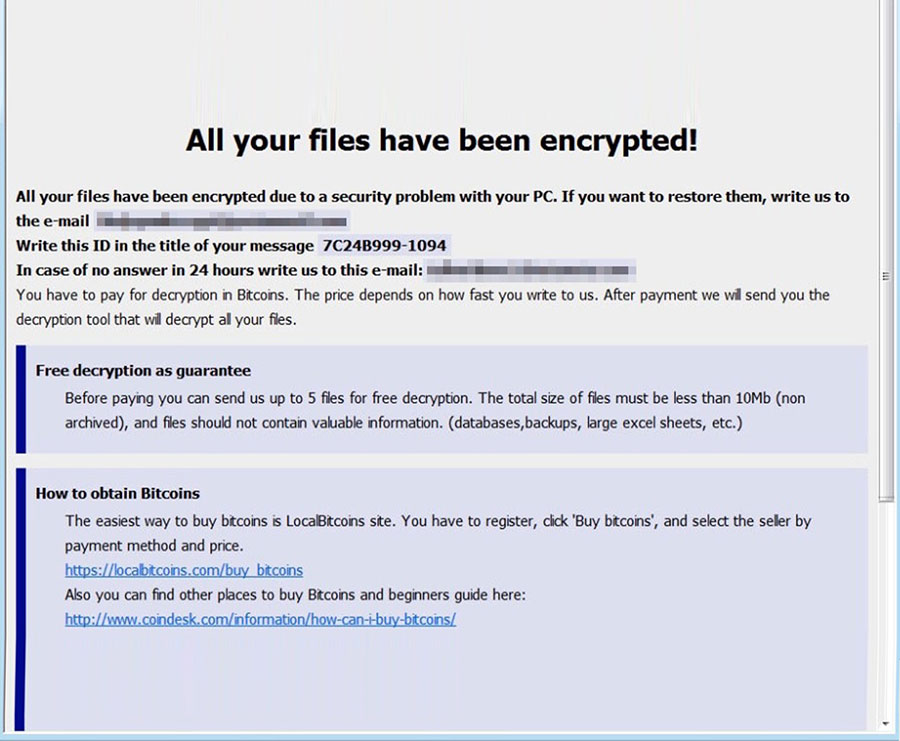
More hackers appeared on our system. One of the most notable was behind a Crysis ransomware infection on Sept. 22. We watched as this threat actor downloaded the ransomware through TeamViewer and continued with their routine, up to the point they left the ransom note. We even interacted and haggled with the threat actor through an exchange of emails.
By now, intruders had been entering our system on a regular basis. On Oct. 16, one even made our robotics workstation send out a beacon, possibly as part of their lateral movement. This was interrupted, however, by a second ransomware attack on Oct. 21, which used a Phobos variant.
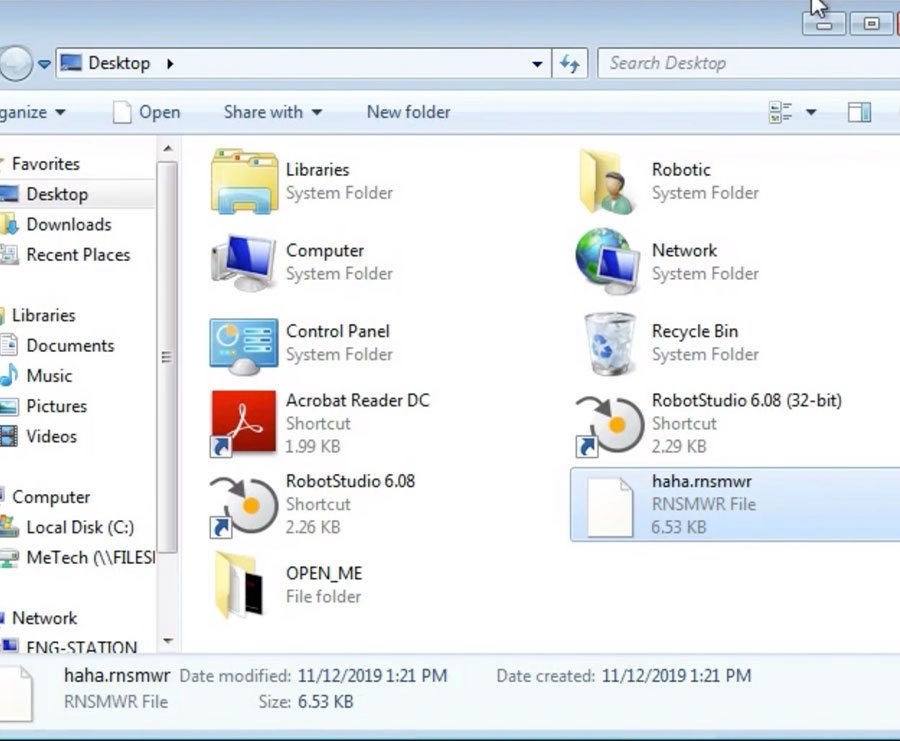
On Nov. 1, a hacker came into our system with good intentions: They left a note advising us to put a password on our VNC. On Nov. 12, we saw an interesting attack that disguised itself as a ransomware campaign, when in fact the threat actor behind it had simply renamed our files. Two days later, on Nov. 14, this threat actor came back to the system to delete files and leave open tabs of a porn site on our desktop.
Between attacks, we had to restart our virtual machine, specifically after each ransomware attack. The last activities we saw were by a few intruders who simply looked around the factory before logging off and exiting the system.
As the research progressed, more and more threat actors found their way into our system, the weak security inviting them into what was potentially a lucrative opportunity. Their attacks were largely possible because our factory did many things wrong in terms of security. However, these conscious “oversights” were all within the limits of what is believable for a working company to have so as not to blow our cover.
Our findings from this honeypot experiment should serve as cautionary examples for organizations, particularly those that run ICSs and smart factories, to ensure that adequate security measures are in place on their systems.
Read our full research paper, “Caught in the Act: Running a Realistic Factory Honeypot to Capture Real Threats,” for more details and insights about our honeypot and the attacks it attracted.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Unconventional Attack Surfaces: Identity Replication via Employee Digital Twins
- Old Vulnerabilities, New AI Era, Amplified Risk: How Outdated Flaws Continue to Fuel the N-Day Exploit Market
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One