500 Million Yahoo Users Affected by Data Breach – Password Change Recommended
Yahoo has confirmed a massive breach that compromised the personal information of 500 million of its users, affecting account holders of Yahoo Mail, Yahoo Finance, Yahoo Fantasy Sports, and Flickr. The tech giant was quick to issue a plan of action, with Yahoo chief information security officer Bob Lord posting an announcement on Tumblr on September 22. The post outlines the investigation, a protection plan, and security recommendations. Yahoo also confirms that user account information was stolen in late 2014, and the data may have included names, passwords, security questions and answers, as well as other personal information like dates of birth and email addresses. Lord’s report noted that there is no evidence to suggest that user payment card data or bank account information was compromised—the system housing that information is believed to be unaffected.
[READ: Data Breaches 101: Everything you need to know]
The Yahoo breach could count as one of the biggest—if not the biggest—breaches in terms of the number of records stolen. The past decade has seen a number of large-scale and high profile data breaches, from the AOL incident in 2005 where an insider leaked sensitive data, to the Target breach in 2014 where nearly 40 million debit and credit card credentials were exposed to fraud. In 2015, healthcare companies like Anthem, and government agency OPM were hit with breaches, all of which suffered a staggering amount of stolen information. This year, 45 million user records were leaked online in the VerticalScope breach and before that, personal details of users who accessed the Acer Online Store were exposed to cybercriminals.
[READ: Follow the Data: Dissecting Data Breaches and Debunking the Myths]
How to respond to a data breach
Yahoo users are advised to immediately reset all passwords linked to Yahoo, especially if the password has not been changed since 2014. Account holders should also note that since users’ security questions and answers were also compromised, Yahoo has invalidated unencrypted security questions and answers so they cannot be used to access an account.
The Yahoo team has put up FAQs and user-friendly guides on their Yahoo Mail page. Users are prompted to reset their passwords and read the guide on recognizing a legitimate Yahoo security notice.
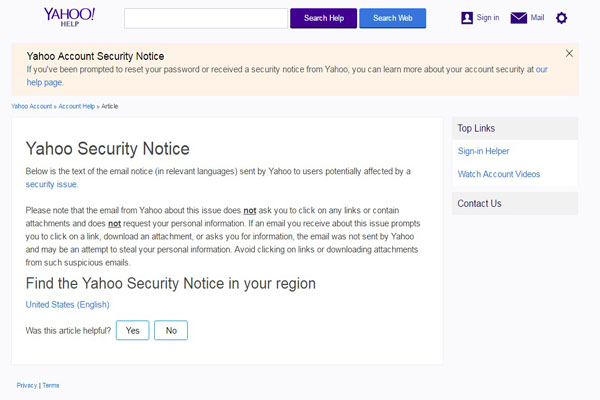
Potentially affected users are asked to change their passwords and given a guide on legitimate security notices
As shown in previous incidents, data breaches can result in a number of consequences for affected users, including the theft of private records and sensitive data. Stolen data doesn't just impact the affected organization, but everyone whose personal information may have been stolen. The following practices below can mitigate potential damage caused by a data breach:
Change your passwords regularly.Change your passwords periodically, at least three times a year. And make sure that you use a strong password—one that includes at least 12 characters, with both uppercase and lowercase letters, numbers, and special characters.
Use different passwords for online accounts.Use unique passwords for different accounts so that in case a breach happens, other accounts won't be affected.
Enable two-factor authentication (2FA). Yahoo and other sites give users the option to use 2FA for online accounts. The security feature requires the use of two types of identification to log into an account, adding an extra layer of security.
Secure all your devices.Laptops, mobile devices, desktops—ensure that they are protected by security software and are always updated.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™
- Forecasting Future Outbreaks: A Behavioral and Predictive Approach to Proactive Cyber Risk Management
- Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
- The Industrialization of Botnets: Automation and Scale as a New Threat Infrastructure

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 The AI-fication of Cyberthreats: Trend Micro Security Predictions for 2026
The AI-fication of Cyberthreats: Trend Micro Security Predictions for 2026 Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One