New Locky Variant Lukitus Distributed in 23 Million Emails
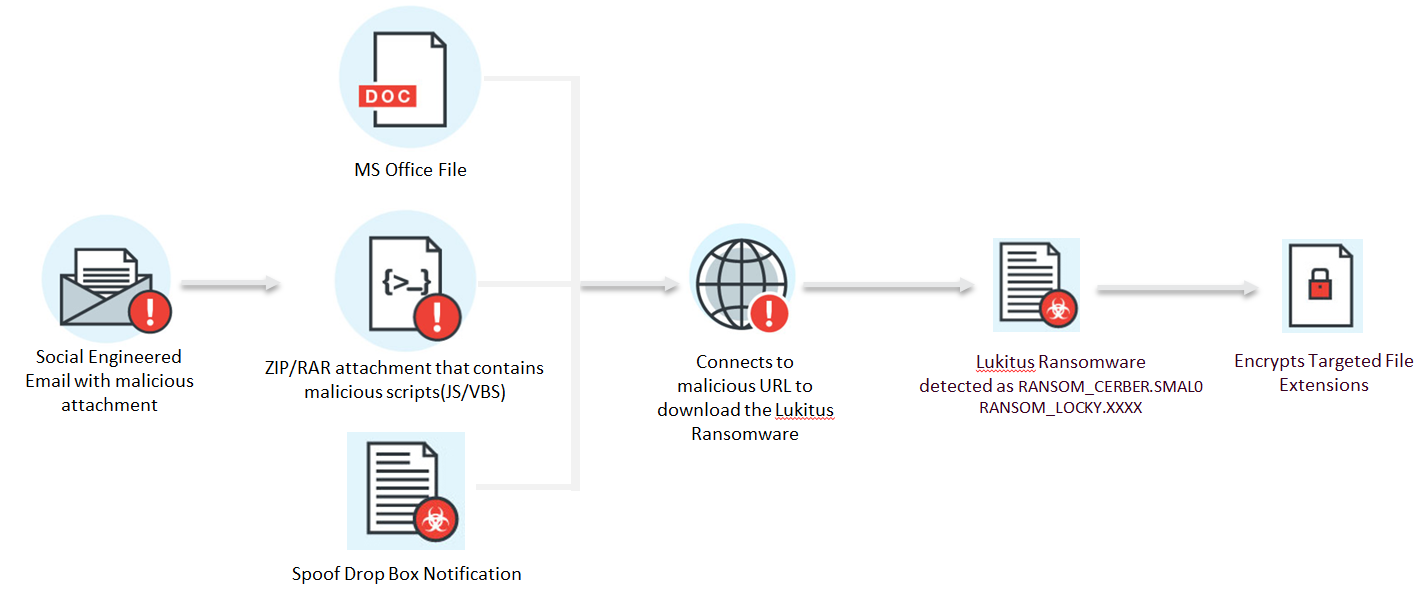
Figure 1. Lukitus infection diagram
Lukitus either arrives as an email with a ZIP compressed attachment that contains a Visual Basic Script (VBS) or JavaScript file (detected as JS_NEMUCOD.TH822 and JS_NEMUCOD.ELDSAUJM), a Microsoft Word document, or a spoofed Dropbox notification. The operators behind Lukitus were discovered sending spams that contain common subjects like "please print,” "documents,” "photo,” "images,” "scans," and "pictures.”
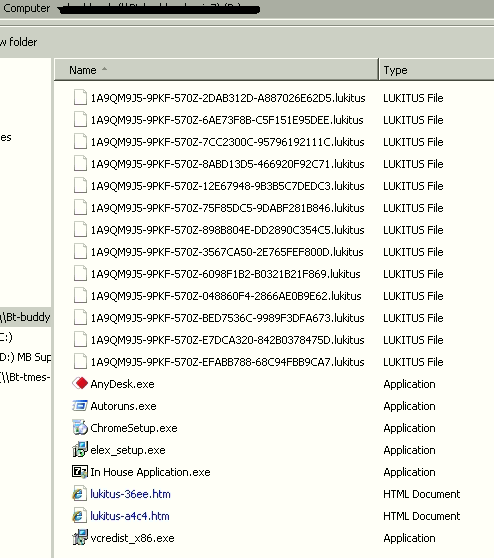
After one of the abovementioned files reaches the system, the VBS or JavaScript file initiates a downloader that reaches out to its C&C servers to download the ransomware. Using the RSA-2048 and AES-128 ciphers as its encryption algorithm, this variant encrypts local files and network shares, changing the names of the files into random characters and numbers. The encrypted files are also appended with a .lukitus extension name.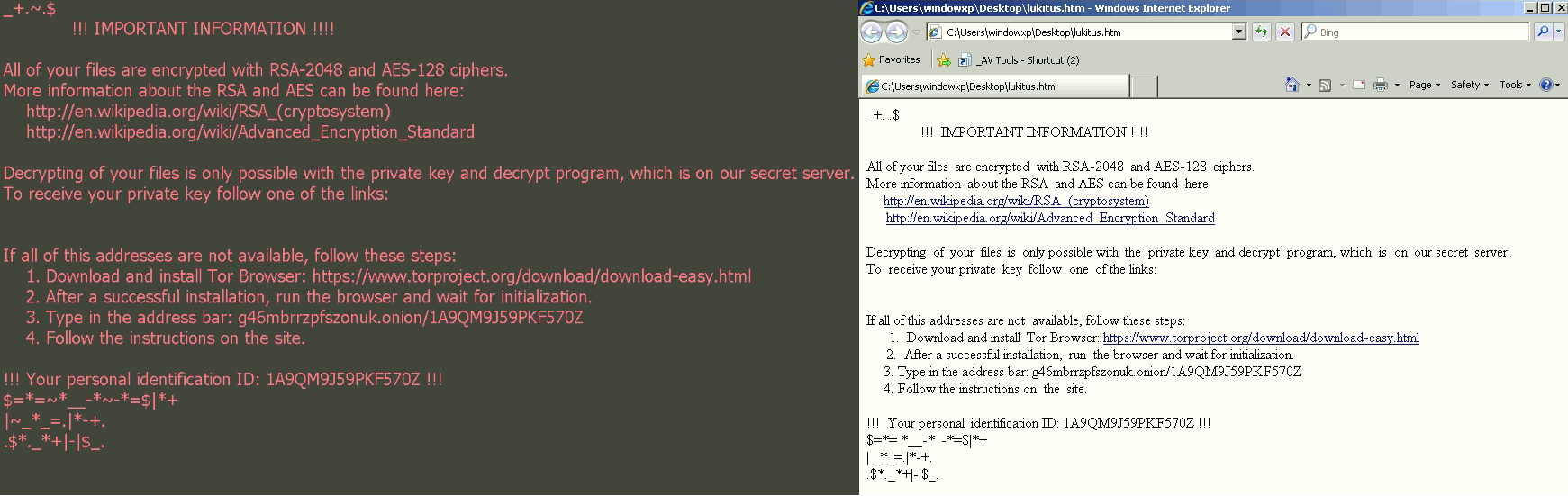
Spam was the top infection vector among the ransomware threats we detected and blocked in 2016, accounting for 79 percent of the total. It is highly recommended for users and enterprises to have an email security solution that checks for email reputation, web reputation of the embedded links, file attachments, as well as macros in Microsoft Office documents.
In addition, users and enterprises can adopt these best practices to lower or eliminate the risk of ransomware infection.
Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector and Deep Discovery Analyzer detect ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud. Trend Micro products’ use of Predictive Machine Learning also protects environments from unidentified threats and zero-day attacks. It performs a behavioral analysis on unknown or low-prevalence processes to determine if an emerging or unknown threat like Lukitus is attempting to infect your network.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.Find more in-depth information on Trend Micro detections and solutions for Trend Micro Deep Security, Vulnerability Protection, TippingPoint, and Deep Discovery Inspector in this technical support page.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Unconventional Attack Surfaces: Identity Replication via Employee Digital Twins
- Old Vulnerabilities, New AI Era, Amplified Risk: How Outdated Flaws Continue to Fuel the N-Day Exploit Market
- Ransomware Spotlight: Agenda
- Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
- Azure Control Plane Threat Detection With TrendAI Vision One™

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2
Cracking the Isolation: Novel Docker Desktop VM Escape Techniques Under WSL2 Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One
Stay Ahead of AI Threats: Secure LLM Applications With Trend Vision One