Trends and Shifts in the Underground N-Day Exploit Market
 Download The Rise and Imminent Fall of the N-Day Exploit Market in the Cybercriminal Underground
Download The Rise and Imminent Fall of the N-Day Exploit Market in the Cybercriminal Underground
The cybercriminal underground is host to a vast market of zero-day and N-day exploits, where the price for an exploit is often dictated by how long it has been out (the newer, the more expensive) and whether a patch for the exploited vulnerability is forthcoming (zero-day) or has already been released (N-day). Over the past two calendar years, we scoured underground forums for N-day exploits to determine how long they stayed in the market. We also examined their life cycle to see whether malicious actors strictly favored newer exploits or also had uses for older ones.
The life cycle of an exploit
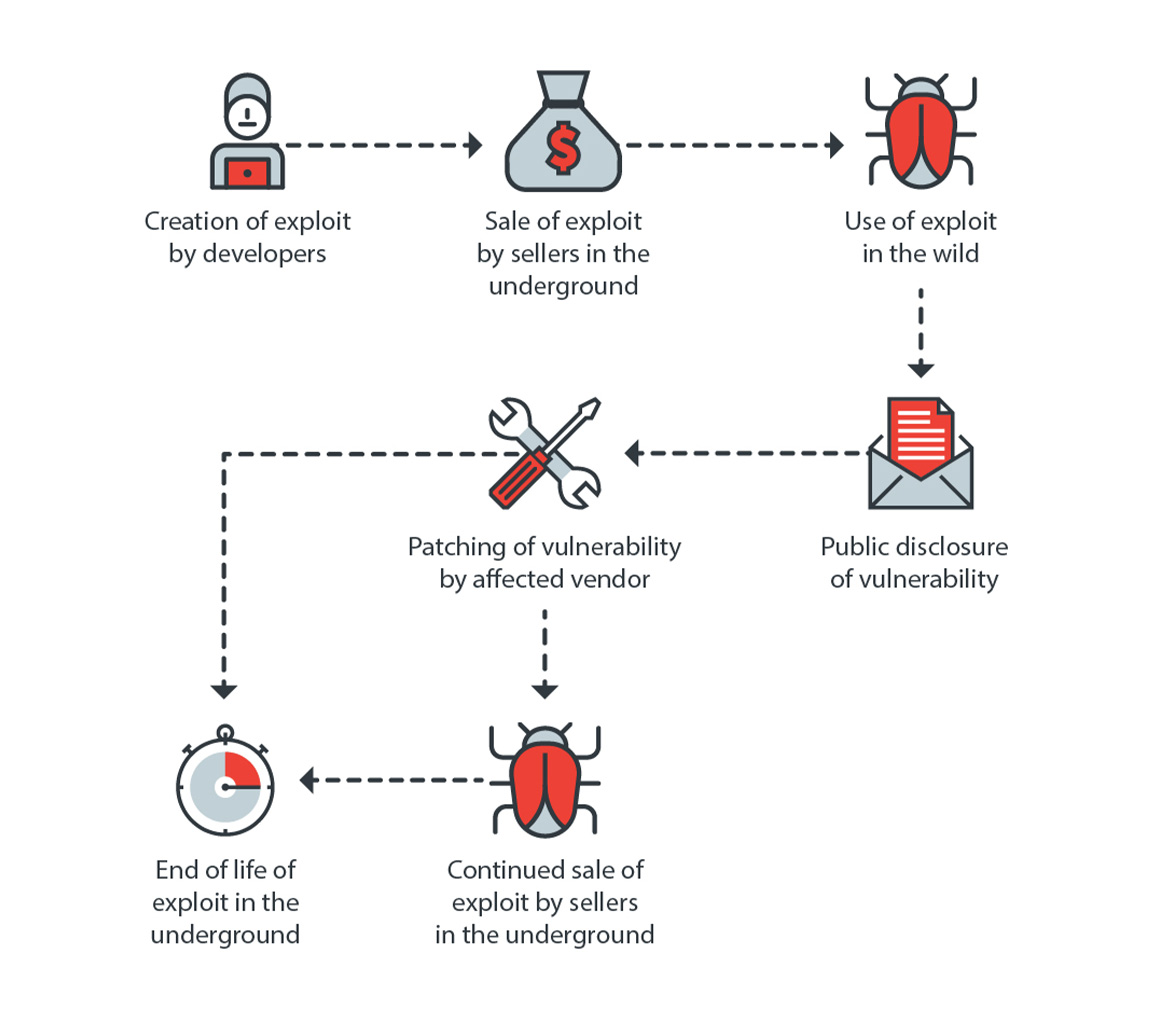
Figure 1. The typical life cycle of an exploit in the cybercriminal underground
The life of an exploit starts with its creation by a developer, either as an already working exploit or as a proof of concept that other developers could build upon. Once it can be weaponized, it is sold in the underground. If it is a zero-day exploit, it can command a very high price. After a patch for the affected vulnerability is released, the price inevitably drops for what is now an N-day exploit. This does not mean, however, that the exploit has become obsolete, as it can still be sold in the underground for years and can even be bundled with other old exploits.
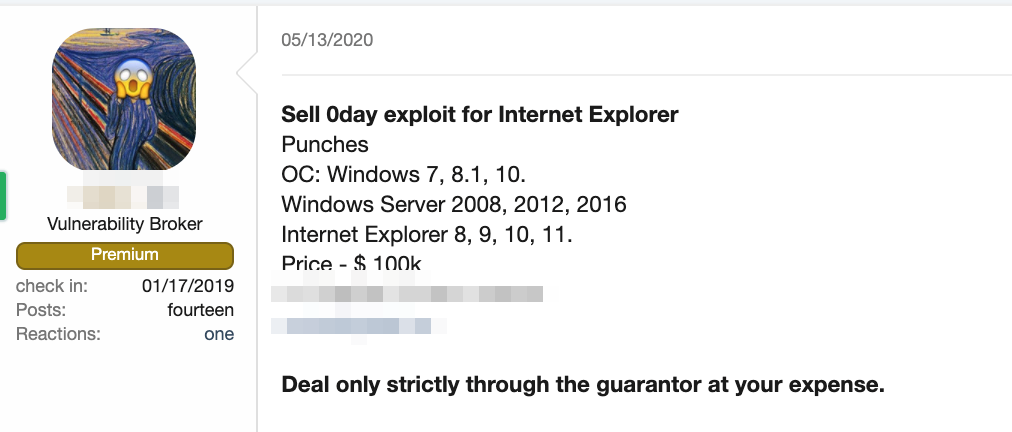
Figure 2. A forum post advertising an exploit for a zero-day Internet Explorer vulnerability
Aside from selling exploits on underground forums, actors can also choose to submit vulnerabilities to bug bounty programs. This has proved to be a viable option for those who do not want to go through the hassle of developing and selling exploits on underground forums. Surprisingly, we even found guides on how to submit vulnerabilities to bug bounty programs on some forums — further proof that these programs have become a legitimate option for vulnerability hunters or erstwhile exploit developers.
Figure 3. A forum post by a user promoting guides on how to submit exploits to bug bounty programs
The continued relevance of old exploits
Although newer exploits are understandably more sought after, there is still a market for seemingly outdated exploits. For example, we found forum posts mentioning exploits for 20-year-old vulnerabilities, including a post made in 2019 requesting an exploit for CVE-1999-0021. Old exploits are also sometimes offered for free on underground forums.
Arguably the most prominent example of an old exploit that remains in use is EternalBlue, which was most notably used in the infamous WannaCry ransomware outbreak of 2017. The persistence of EternalBlue is evidenced by the prevalence of WannaCry itself, which still emerged as the top malware family in Trend Micro’s detections in 2020.
Subscription services for exploits are also available as an alternative to less experienced actors who do not have the technical knowledge to properly implement exploits. These services often include bundles of old exploits that are already built and automated into the vehicles used in attacks, such as Microsoft Word or Excel documents. An exploit builder we found, for example, bundled exploits for the vulnerabilities CVE-2017-8570, CVE-2017-11882, and CVE-2018-0802 into a single subscription service for a monthly fee of US$1,150. Some services also promise their subscribers periodic updates on their offerings
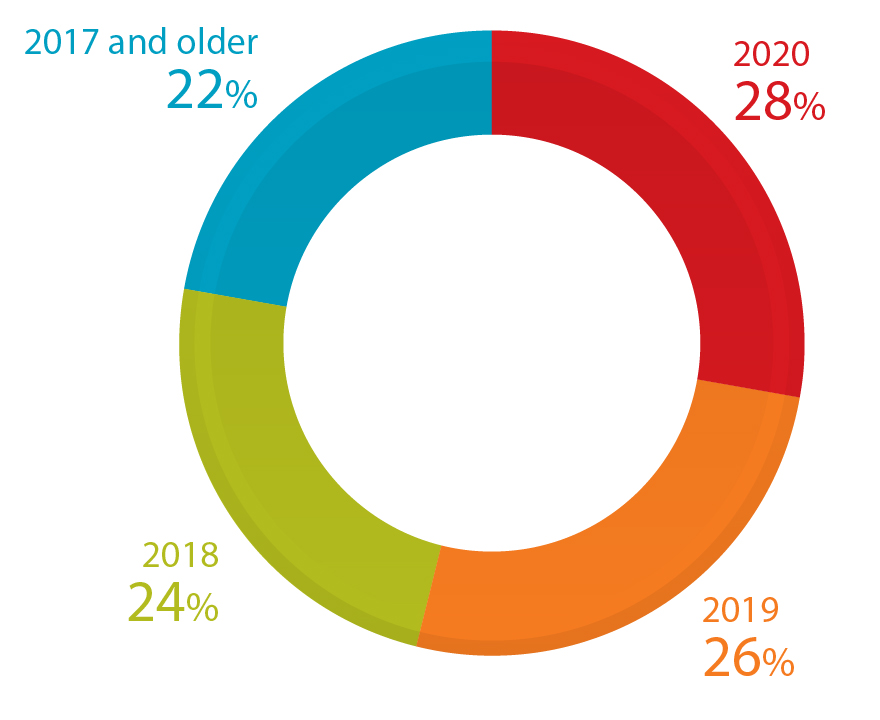
Figure 4. The distribution of exploits sold by users on cybercriminal underground forums based on the years of disclosure of the vulnerabilities they are for
The rise of access-as-a-service
Perhaps the development in recent years that has been most disruptive to the underground exploit market is the rise of the access-as-a-service model, where vendors provide remote access to entire corporate networks.
Because they bypass the need for setting up complicated infrastructure to compromise a target system, access-as-a-service offerings typically command higher prices, which many customers are willing to pay because of the ease of use and transparency afforded by the model. While some access-as-a-service sellers are less experienced and merely rely on being able to find and capitalize on working exploits, there are other sellers who consider access-as-a-service a more professional operation, offering a wide range of products and services complete with portfolios.
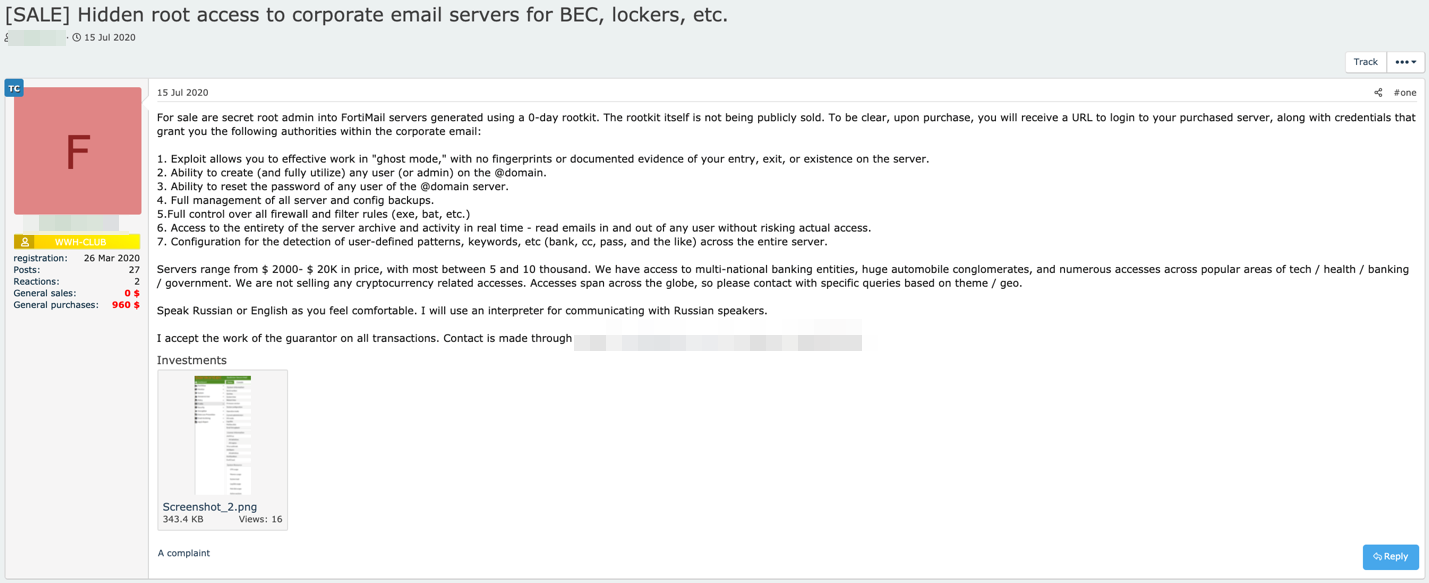
Figure 5. A forum post advertising access, using a zero-day rootkit, to email servers
The importance of patching in thwarting exploits
That the underground exploit market continues to thrive means that organizations should ensure that patches are applied and systems are updated in a timely manner. However, patching multiple machines, let alone a whole system, is not as easy as it sounds. Implementing updates takes time, especially for large organizations. One way of bridging the gap during the time it takes to fully implement security patches is virtual patching, which protects systems and networks from exploits via an additional security layer.
Our paper “The Rise and Imminent Fall of the N-Day Exploit Market in the Cybercriminal Underground” expounds on this security recommendation. In it we detail our two-year research into the underground N-day exploit market, including in-depth discussions of the kinds of exploits that are offered and the types of actors who participate in it.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation