Twitter Now Allows Open Direct Messaging: Time to Rethink Your Privacy Settings
 If you don’t want to receive direct messages from other random Twitter users, now’s the time to opt out. Twitter recently announced an overhaul on how their direct messaging feature works. The service now allows anyone to send direct messages (DM) to anyone else, regardless if they are connected or not. By default, Twitter direct messaging happens only between users who follow each other, making it difficult to communicate if only one person followed the other.
If you don’t want to receive direct messages from other random Twitter users, now’s the time to opt out. Twitter recently announced an overhaul on how their direct messaging feature works. The service now allows anyone to send direct messages (DM) to anyone else, regardless if they are connected or not. By default, Twitter direct messaging happens only between users who follow each other, making it difficult to communicate if only one person followed the other.
According to the update, this new messaging system makes it easier for you to communicate one-on-one or with a chosen group of people anywhere in the world. This current implementation has some privacy implications for those who are a little bit more concerned about receiving DMs from strangers. Because of this new DM capability, users no longer need to virtually shake hands in order to send direct messages to each other, allowing for more unwanted DMs, or potential private abuse and nuisances.
Previous security flaws have made many users increasingly worried about their privacy and security. In 2010, a Twitter security flaw exploited thousands of Twitter accounts, redirecting users to third-party websites, and opening unwanted pop-ups without their consent. The flaw uses a JavaScript function called “onMouseOver” , which creates an event when the mouse falls on a chunk of text. The exploit could be used to redirect users to third-party websites, including porn sites.
On the one hand, the new DM update could be useful to celebrities (verified accounts), or for brands and organizations that want a convenient line of communication with the public, as well as companies who use the platform for customer support without having to send a public tweet. On the other hand, it could be an annoyance for ordinary users, making the original DM setup more ideal as it not only created a personal DM space, but it served as a good barrier against spam as well.
[READ: How to Improve Your Privacy and Security on Social Media #SecurityNow]
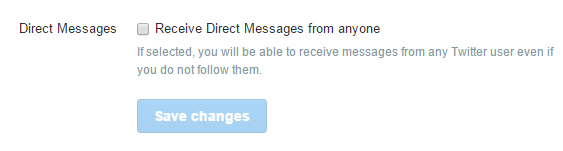
While the update might serve as a good opportunity for some, it could be overwhelming for others. The good news is, if you’re part of the latter, you can adjust your DM settings and choose to keep your messages private. If you want to “opt in” in the future, you can switch to the new DM update feature.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation