By Christopher Boyton (Senior Adversary Hunter, TrendAI™ Research), David Sancho (Senior Threat Researcher, TrendAI™ Research), and with the help of Bakuei Matsukawa (Principal Threat Researcher, TrendAI™ Research)
Key Insights
- Infostealers are adopting ransomware-style specialization and affiliate models, signaling a structural shift in how credential theft operations are organized and monetized.
- Passkeys and phishing-resistant authentication are reducing the resale value of passwords, forcing attackers to turn toward session theft and broader identity ecosystem abuse.
- Automation and AI are lowering the barrier to managing identity abuse at scale, accelerating the transition from fragmented campaigns to managed systems.
Identity data has never been more valuable. The unprecedented surge in credential theft throughout 2025 reflects more than increased attacks, it signals an underlying transformation in how identity compromise is organized, monetized, and scaled.
A market once built on mass infection and password reuse is reorganizing into a more structured, affiliate-driven ecosystem optimized for speed and precision.
Stronger defenses are forcing this shift as much as attacker innovation. Password reuse is declining, multi-factor authentication (MFA) is now the standard, session controls are tighter, and phishing-resistant passkeys are gaining traction and limiting the reuse of stolen credentials. At the same time, automation and AI are reducing the cost of coordinating complex attack chains.
As static credentials lose replay value, infostealer attackers are prioritizing higher-fidelity identity artifacts: session tokens, authentication cookies, and recovery workflows that remain exploitable in hardened environments.
Credential theft is not disappearing. It is becoming more structured, more selective, and increasingly systematized.
Infostealers are no longer just malware. They are becoming systems: coordinated workflows that connect collection, analysis, and monetization into a continuous process.
Introduction: From Tools to Systems
To understand why this shift matters, it helps to explain how infostealers traditionally operated and why that model is now under strain.
For years, infostealers operated within a straightforward criminal model built on scale. Campaigns focused on mass infection, bulk data collection, and resale. But this model is now buckling under sustained security pressure. Changes in authentication, market saturation, and law enforcement activity are reshaping how credential theft is organized and monetized.
This security pressure now permeates the ecosystem. Password reuse is declining, MFA is widespread, and passkeys are beginning to reduce the replay value of stolen credentials. Log markets are crowded, resale margins are tightening, and automation is entering more stages of the workflow.
In response, the infostealer ecosystem began restructuring. Roles that were once bundled together are separating. Log markets increasingly resemble structured trading platforms rather than dump boards. Tasks that once required manual sorting or validation are becoming automated.
What was once a loose collection of actors using shared tools is beginning to resemble a coordinated system.
TrendAI™ Research examines this transition. It outlines how infostealer operations are moving from volume-driven harvesting toward workflow-driven models, how changes in authentication are reshaping criminal economics, and how automation is accelerating this shift.
Infostealers are no longer just malware. They are becoming infrastructure.
Structural Comparison
The shift in the infostealer ecosystem is best understood as a structural transition from a volume-driven model to a workflow-driven one. Rather than maximizing how much data is stolen, attackers are prioritizing how identity is accessed, prioritized, and monetized.
Table 1 contrasts the defining characteristics of the former volume era with the emerging systems-driven model. The change is easier to see when you compare how the model actually operates.
| Dimension | Old model (Volume era) | Emerging model (Systems era) |
|---|---|---|
| Primary objective | Mass credential harvesting | Monetizable identity access |
| What's stolen | Passwords, autofill, cookies | Session tokens, full logs, context-rich data |
| Operational focus | Scale | Precision + speed |
| Campaign model | Opportunistic mass infection | Targeted + workflow-driven |
| Delivery methods | Bulk phishing, exploit kits, botnets | Multi-channel, staged delivery |
| Monetization model | Bulk resale | Selective exploitation + resale |
| Pricing logic | Volume-based | Value-based |
| Automation role | Limited (delivery-focused) | Embedded across the workflow |
| Market structure | Fragmented actors | Layered ecosystem |
| Key constraint | Infection scale | Time-to-monetization |
| Competitive edge | Distribution reach | Workflow efficiency |
Table 1. Comparison of the old and emerging infostealer economy models
The key difference is not what is stolen; it is how quickly and efficiently that data is turned into usable access.
Reorganization in Practice
Having established why infostealers are shifting, this section focuses on how this shift is unfolding, namely through affiliate models, operational specialization, and managed infrastructure.
The Infostealer Affiliate Model
In 2025, we observed a significant development in the infostealer ecosystem: the emergence of affiliate models that closely mirror that of ransomware-as-a-service (RaaS) operations.
In this emerging model, affiliates are recruited with the promise of a share of the proceeds generated from successful infostealer infections. Operators provide the infrastructure and malware builds, retaining a percentage of the revenue — a structure reminiscent of RaaS operations.
Revenue splits can reach 70 to 80% in favor of the affiliate. This model relies on a broader support ecosystem, including crypting services, malware developers, and initial access brokers (IABs). Unlike purchasing malware directly from an operator, affiliates can directly execute infections through a managed and controlled setting without any upfront cost. This model does not require a paid subscription. This is effectively ransomware economics applied to infostealers: operators build the platform, affiliates scale distribution, and specialization increases efficiency.
We have found a few examples of infostealer developers with affiliate models, the latest of which are the CLR Team and the Roku Team.
The CLR Team case dates to October 2025, when an actor using the handle Detools advertised their web-based management panel and Telegram bot to recruit affiliates, as shown in Figure 1. The advertisement promoted a fully supported affiliate program offering
- A landing page for build distribution
- An 85/15 revenue split, in favor of the affiliate
- Manual crypting service for active users
- Access to a proprietary loader
- SEO support for top-performing affiliates
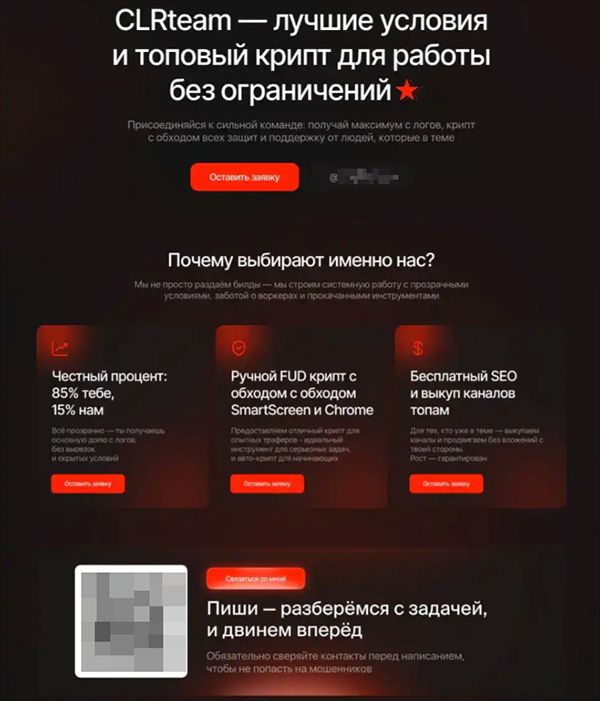
Figure 1. CLR Team’s advertisement for recruiting affiliates
The process of joining the panel and creating a malware build demonstrated how easily low-skilled criminals could carry out attacks that would otherwise require good technical knowledge. The main barrier to entry was a set of filtering questions posed by the Telegram bot, as shown in Figure 2. These questions were intended to assess the applicant’s experience, the amount of time they were willing to commit, and the existence of an active forum account to establish the applicant’s credibility.
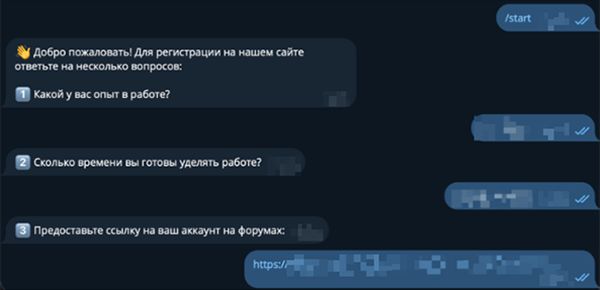
Figure 2. Filtering questions posed to prospective affiliates before allowing them access to the panel
Once the administrator is satisfied with the answers, they send login details for the panel. This gatekeeping step appears to be designed to filter out inexperienced criminals, researchers, and law enforcement. It also prevents fully automated interactions with the bot by ensuring that a human remains in the verification loop. Access to the panel provides affiliates a list of FAQs, build-generation functionality (Figure 4), and tools to track active infections.
Figures 3 and 4 show translated versions of the FAQ and the build-management panel, respectively.
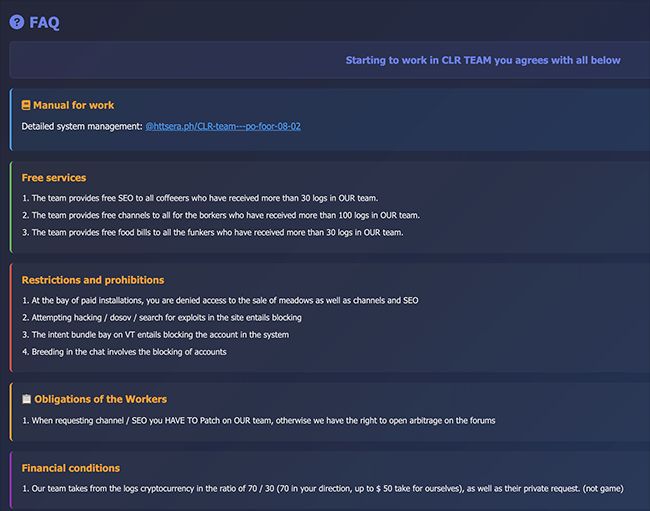
Figure 3. Information on services, rules, and how criminal proceeds are distributed
The build management panel allows users to generate customized, encrypted payloads. Early versions supported multiple infostealers, including Lumma Stealer and Vidar. Following a joint Europol-Microsoft operation that disrupted Lumma’s infrastructure, it was removed from the panel and replaced with Rhadamanthys.
This pattern was repeated after Operation Endgame 3.0, when Rhadamanthys was also affected by law enforcement activity. Rather than altering its underlying function, the panel adapted by rotating available payloads.
As shown in Figure 4, users can generate both encrypted and non-encrypted builds for the currently supported families, such as Rhadamanthys and Vidar.
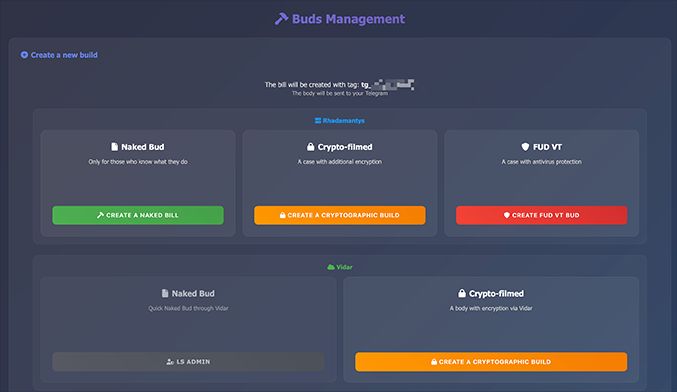
Figure 4. The build-management pane
Another benefit of this affiliate program is that the operators maintained the updates for the infostealers available through the panel. For example, when a new version of Vidar was released, the operators provided affiliates with instructions on generating updated malware builds.
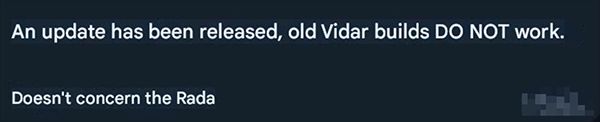
Figure 5. Operators providing an update about a new version of Vidar
This setup enabled the execution of a complete infection lifecycle, from build generation to data exfiltration, within a controlled environment.
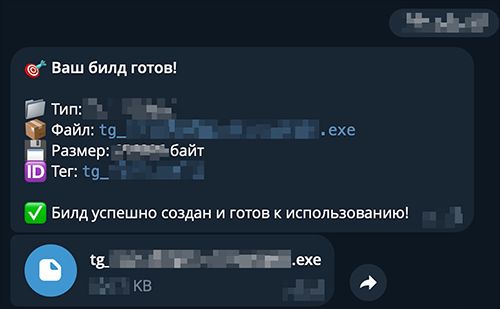
Figure 6. A build available for download on the Telegram channel
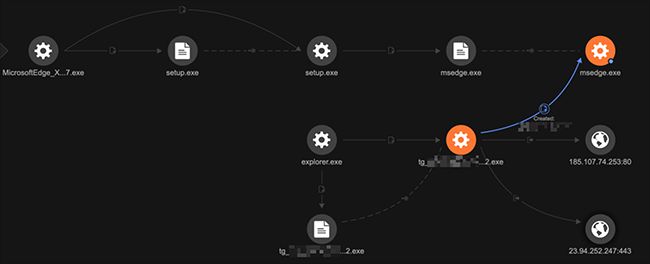
Figure 7. Build execution reaching out to confirmed Rhadamanthys C&C (results taken from a test lab using TrendAI Vision One™)
Affiliate models change who can operate and how fast campaigns scale. To assess the operational impact of the shift to this model, we examined victimization patterns and activity metrics from a live affiliate program.
Scale and Victimization Metrics
Taking the CLR Team’s affiliate program as an example, the impact of these groups is clear. The affiliate program had more than 150 users and collected over 30,000 log packages in a six-month period. The associated public log channel allowed further investigation of the victimology, with individual log entries containing the user, victim IP address, victim country, and details of the stolen information.
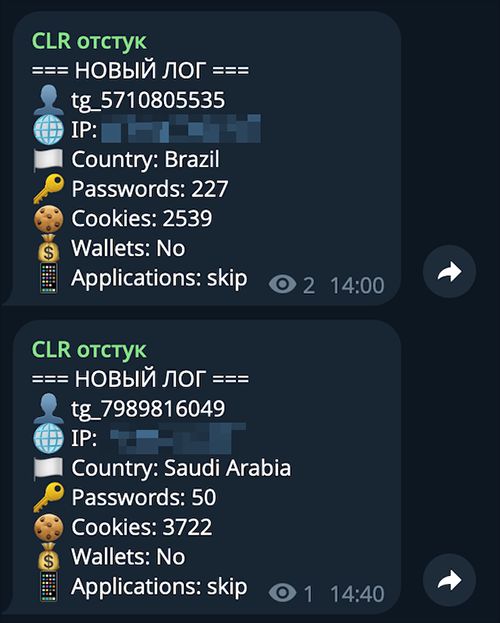
Figure 8. Excerpt from CLR Team log stream
Examining the data from the public log channel helped us identify the most targeted countries. The resulting distribution of countries loosely correlates with population size and internet user bases and does not appear to be highly targeted compared to the distribution we would see with ransom affiliates were explicitly prohibited from targeting CIS countries. Accordingly, those countries do not appear in Figure 9.
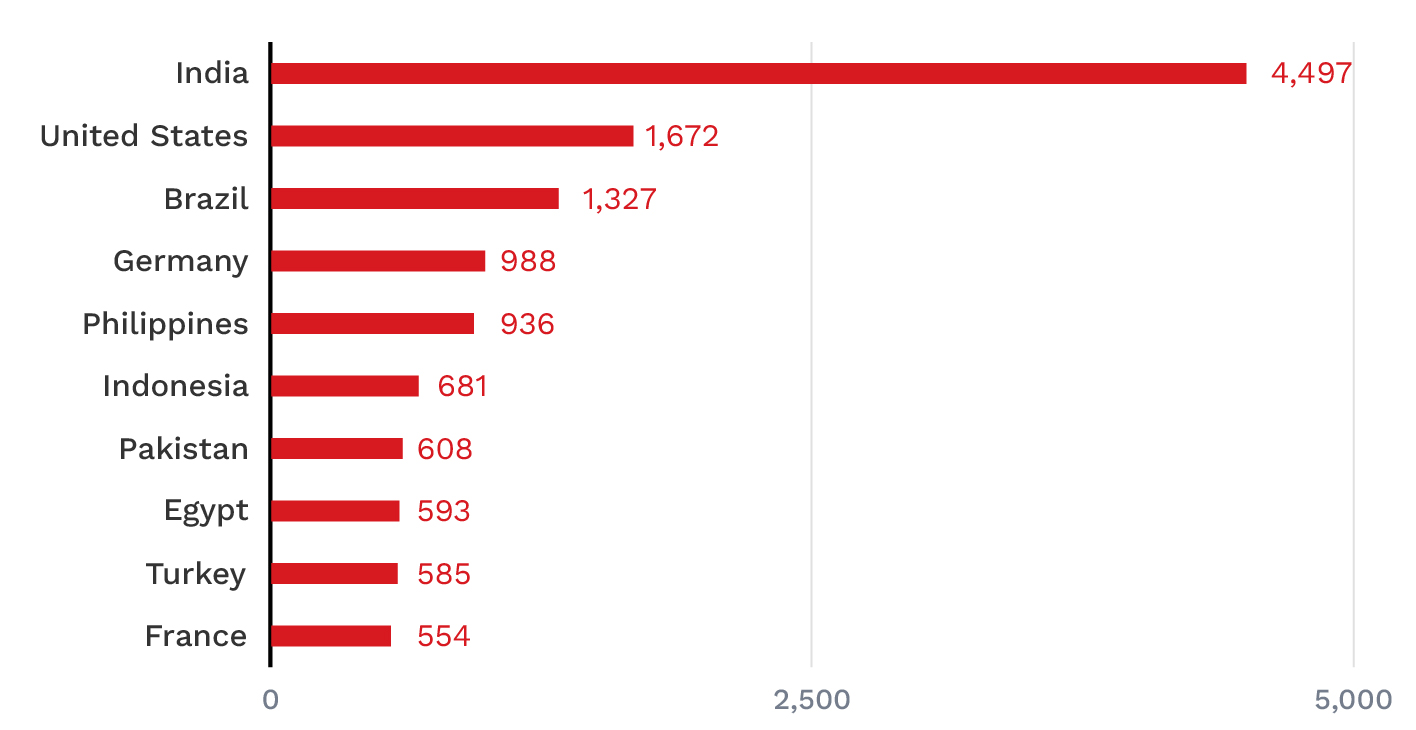
Figure 9. Top 10 countries with the highest number of recorded victims in the CLR Team affiliate program (August 2025 to February 2026).
The data also allowed us to examine campaign clustering based on user handles and message timestamps. Analysis of activity patterns showed that the users could be classified into three main groups:
- Burst: Accounted for 5% of users and were characterized by high-intensity activity, resulting in more than 200 victims in less than three days.
- Short: Represented 77% of users; it involved operations that were short term campaigns that ran between four to 14 days.
- Sustained: Comprised the remaining 18% of users and involved persistent, long-running campaigns that lasted longer than 14 days.
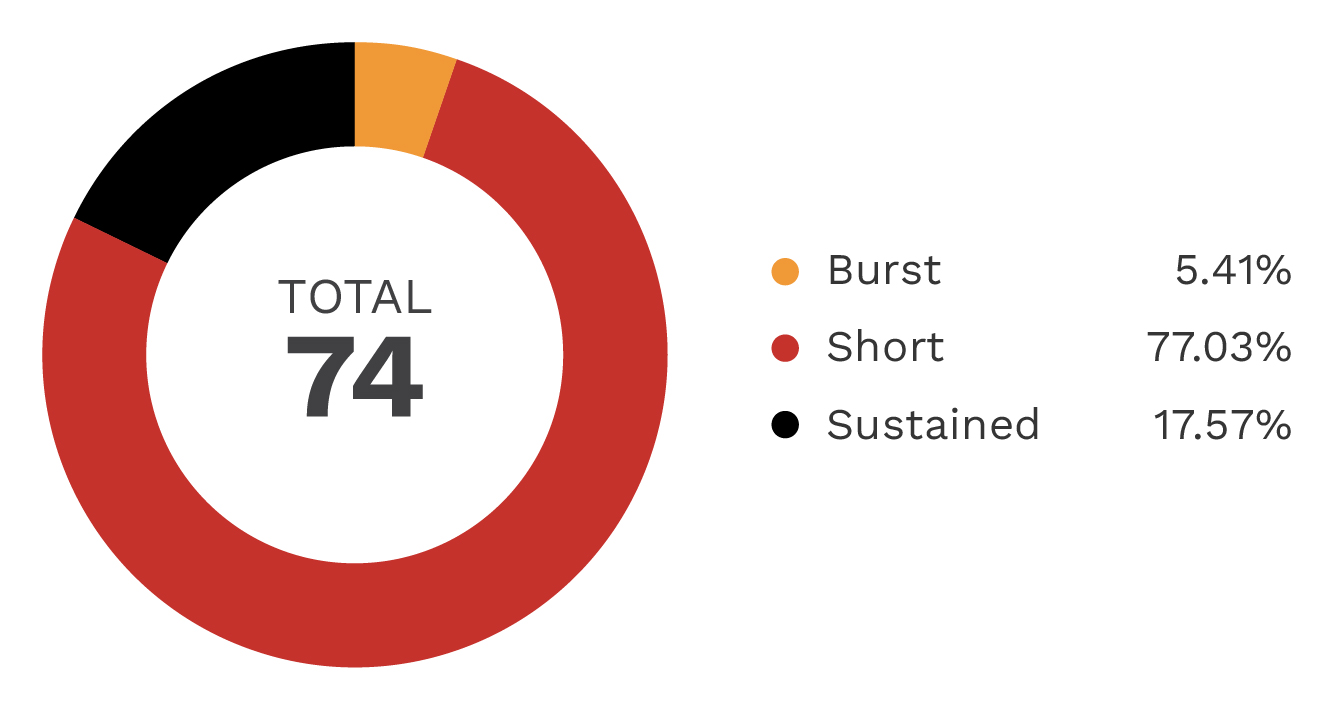
Figure 10. Distribution of affiliate users based on their activity pattern
Operational Specialization
These activity patterns are not random. They reflect differences in operational roles, infrastructure access, and campaign objectives across the affiliate base. Some actors concentrate on short, high-volume bursts. Others run slower campaigns that rely on persistence and repeat targeting. This varied distribution reflects a maturing ecosystem rather than the work of isolated actors. As with ransomware, the market appears capable of supporting affiliates with different operating models, from high-volume campaigns to more selective, margin-driven approaches.
The evolution of infostealers is no longer limited to payload capability; it is increasingly organizational. What was once a relatively straightforward model of infecting systems — harvesting data, dumping logs, and reselling access — is fragmenting into a layered ecosystem of specialized roles and services.
Dedicated marketplaces have emerged to trade what stealers produce: structured logs of stolen credentials, session tokens, and contextual victim data. Platforms such as RussianMarket and 2easy facilitate the sale of curated log datasets, allowing buyers to search and purchase validated access with minimal friction. These are not simple dump boards, but structured trading environments with searchable inventories, defined pricing, and clear product categories. TrendAI™ Research observed the early emergence of this shift as far back as 2020 in their analysis of underground log markets. What was emerging then is now standard across the ecosystem.
The scale and resilience of these markets reinforce the shift. Even after high-profile law enforcement actions, including the takedowns of the Cracked and Nulled marketplaces in March 2025, underground log markets continued to expand, with documented growth in available logs and supporting tools. Additional secondary services have also emerged, including escrow systems, preorder functionality, and log-parsing tools that help buyers extract functioning credentials from raw datasets.
The result is structural rather than just cosmetic transformation. Developers, distributors, access brokers, and marketplace operators now act as distinct nodes within a coordinated value chain. Infostealers increasingly resemble organized platforms rather than standalone malware families. As authentication hardens and margins narrow, specialization becomes a rational economic adaptation, explaining why the traditional credential harvesting model is beginning to lose efficiency.
Why Attackers Are Being Forced To Evolve
For much of the past decade, credential harvesting has been a volume business. Botnets distributed phishing and malware campaigns, while automated credential-stuffing attacks attempted millions of logins across exposed services. The model relied on scale: more infections yielded more credentials, and more credentials translated into broader resale potential.
That model is becoming less effective.
Stolen passwords and reused credentials once formed the backbone of account takeover activity and fueled much of the infostealer economy. Advances in email filtering and endpoint detection, however, have shortened the lifespan of indiscriminate campaigns and increased the cost of sustaining them. At the same time, the resale environment has shifted. While credential abuse remains a major component of breach activity, the conditions under which those credentials can be reliably monetized have narrowed.
The defensive baseline has also evolved. MFA is now standard across many high-value services, reducing the effectiveness of single-factor password compromise. Large-scale phishing operations have adapted by intercepting authentication sessions and bypassing weaker MFA implementations, but these techniques require more operational effort and introduce friction that did not exist in the era of simple credential replay. Scale is no longer effortless.
Organizations are also tightening session management and authentication policies, limiting cross-device reuse and replay opportunities. Static password dumps — once broadly monetizable — are increasingly situational assets rather than universally exploitable datasets.
This reduction in utility directly affects infostealer return on investment. Password-only logs carry diminishing value as replay success rates decline. In response, stealer operators are expanding beyond raw credentials, prioritizing session cookies, authentication tokens, and contextual victim data that retain value in hardened environments.
In short, the infostealer business model is adapting to preserve profitability, as volume alone no longer guarantees profit. Password-only logs are losing value because they fail more often.
The Passkey Effect
One development accelerating this shift is the rise of passkeys. Passkeys target the core mechanic that made password theft profitable: replay. Built on FIDO2 and WebAuthn standards, passkeys use asymmetric cryptography. The private key remains bound to the user’s device, while the public key resides with the service. No shared secret traverses the network, and credentials cannot be reused across domains. Because passkeys are cryptographically tied to the original service that registered them, phishing pages cannot capture and replay them in the same way passwords allow.
This architectural change constrains the scalability of credential stuffing and replay attacks. Even when endpoints are compromised, attackers are far more likely to obtain session artifacts than extract reusable private keys. The credential itself resists commoditization.
However, passkeys do not eliminate account takeover. They relocate it. As password replay loses reliability, adversaries move outward toward recovery workflows, session theft, device enrollment abuse, and cross-platform trust manipulation. The passkey era reshapes attacker economics. Success depends less on harvesting reusable secrets and more on exploiting the broader identity ecosystem that surrounds modern authentication.
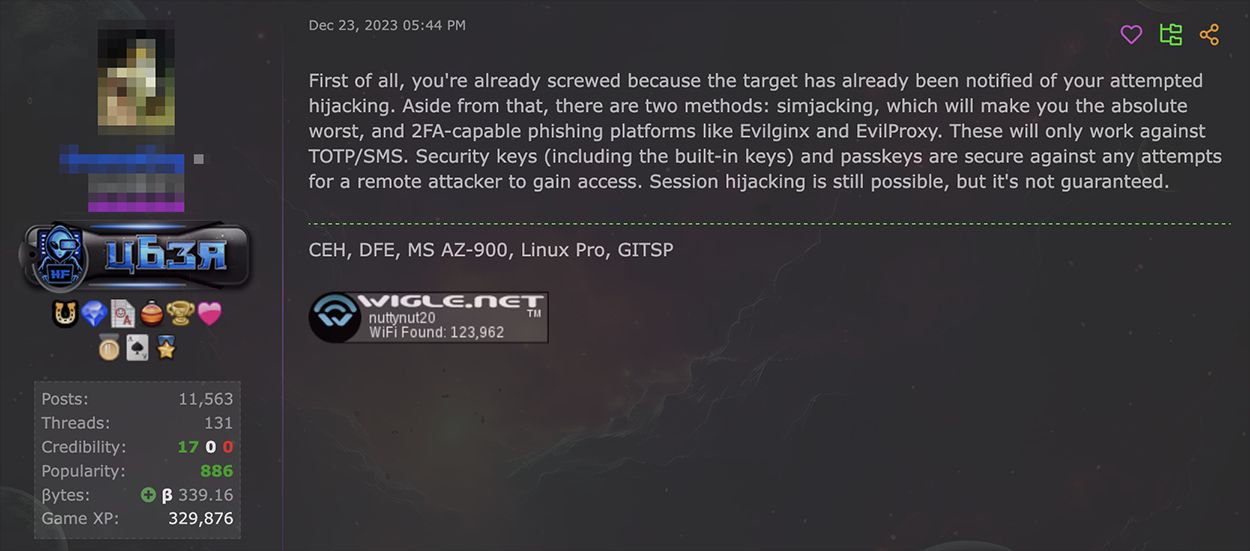
Figure 11. Criminal underground chatter on passkeys and their security.
Underground Friction and Complaints
The pressure to change is also evident within the infostealer ecosystem itself. As infostealers have grown in scale and visibility, they have also drawn sustained law enforcement attention. Enforcement actions now produce immediate operational effects, with affiliates often shifting quickly to whichever competing tool appears most stable.
One example came in October 2024, when the Dutch National Police, the FBI, and Europol, conducted Operation Magnus against RedLine and META Stealer. RedLine dominated the infostealer market for years, yet its removal did not reduce overall activity. Instead, infections rebounded as operators redistributed across competing platforms. The ecosystem proved highly resilient: pressure on one stealer quickly shifted activity toward others. Only coordinated actions targeting multiple families, such as Operation Endgame, have the potential to produce broader ecosystem disruption.
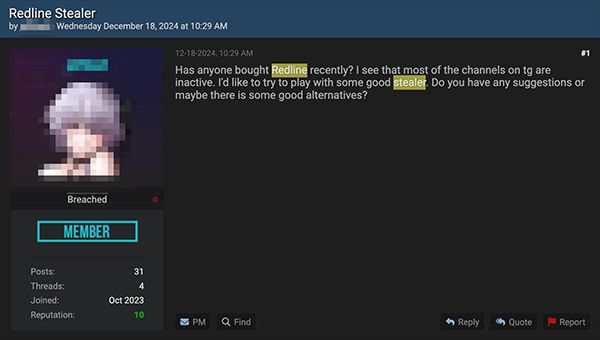
Figure 12. BreachForums post seeking alternatives shortly after Operation Magnus
Lumma Stealer rose to prominence after RedLine’s disruption, becoming the most prolific infostealer of choice. When Lumma itself became a target, it demonstrated a more resilient response. Although its activity briefly declined following the seizure of approximately 2,300 domains, operators frantically rebuilt their infrastructure, resuming operations and returning to their typical tempo in a matter of days. While the operation continued, it did lose customers as they migrated to other infostealers such as Rhadamanthys, Vidar, and StealC. Underground discussion reflected this uncertainty, with posts discussing whether Lumma was still active and seeking alternative options.
Figure 13. Underground discussion about whether Lumma Stealer is still active
In November 2025, Operation Endgame launched another phase targeting Rhadamanthys, VenomRAT, and the Elysium botnet. Beyond domain seizures, the operation also aimed to damage the reputation of the Rhadamanthys operator by suggesting they were siphoning higher-value logs from customers. This campaign introduced visible distrust into the ecosystem and helped prevent a rapid recovery like the one previously observed following Lumma Stealer’s disruption.
Competition within the infostealer market remains intense. When Rhadamanthys was disrupted, discussions across underground channels showed little sympathy for the operator. As illustrated in Figure 14, one actor reacts openly, and with apparent amusement, to the takedown of Rhadamanthys panels and the reported move to certificate-based server access. In the exchange, an actor remarked in Russian that “everything broke badly,” suggesting operational disruption. Another reply responded with skepticism, questioning the source and credibility of this information. The overall tone is amused and dismissive. Most reactions focused on whether competing tools would benefit from the disruption rather than the takedown itself.
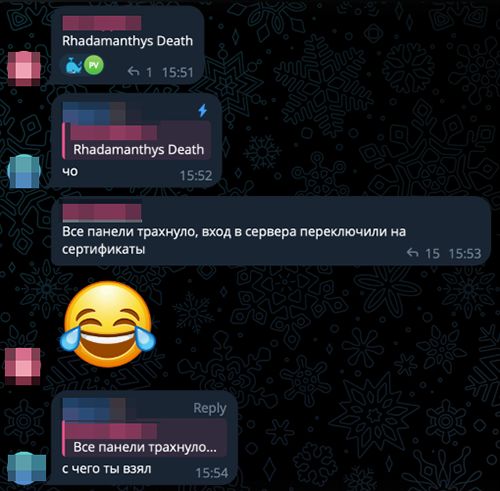
Figure 14. Telegram channel discussion showing the actor’s reaction to law enforcement action against Rhadamanthys.
A forum post by the actor Loadbaks shortly after the operation appeared to reinforce this dynamic, stating simply that they “continue to operate successfully.”
Figure 15. A forum post by the Vidar operator on the BeachForums claiming their operation was unaffected, using resilience to law enforcement action to distinguish itself from competitors
The Old Model Is Breaking
These reactions highlight a deeper structural problem. The infostealer ecosystem was built on a simple idea: infect as many machines as possible, harvest credentials and browser data, and sell the resulting logs in bulk. Commodity malware made harvesting easy, while marketplaces such as Russian Market and 2easy handled resale. For years, the economics worked. Infection was cheap, and the stolen data retained high resale value.
But that balance is beginning to erode.
MFA has reduced the usefulness of harvested plaintext credentials, while buyers increasingly require additional artifacts or tools to convert stolen data into usable access. At the same time, the log markets are showing signs of saturation. Large volumes of stolen data are now widely available, driving prices down and forcing operators to differentiate through targeting, freshness guarantees, or specialization in specific sectors.
The result is a model under strain. A system designed for maximum volume is encountering diminishing returns. As the resale value of generic credentials declines, operators are shifting their focus from scale to quality and exploitability.
Automation and AI offer one path forward. These tools can enable the rapid triage of stolen logs, enrich them with contextual information, and identify victims more likely to produce immediate returns. By reducing the time between theft and monetization, automation helps offset the weakening economics of bulk credential harvesting.
From Operations to Systems
As economic pressure increases and monetization windows narrow, operations are being reorganized around quality and exploitability over scale. This section focuses on how early automation and AI are beginning to transform credential theft and infostealers into more structured systems that better answer the demands of shifting times.
Early Automation and AI Integration
This shift toward more targeted operations is not theoretical. It is already underway. Parts of the infostealer workflow are becoming automated.
Social engineering to deliver infostealers now incorporates AI-generated content. Operators can quickly produce customized messages tailored to specific industries, regions, or themes without writing them manually. The result is faster campaign preparation and more convincing lures, reducing the preparation required to launch new operations
Profiling tools are also becoming more common. Stolen logs can be automatically sorted and enriched with publicly available information. Victims may be ranked by geography, device type, platform usage, or likely financial value. Rather than manually reviewing large datasets, operators can filter for accounts that appear more profitable.
Automation frameworks help connect these individual steps. Log ingestion, validation scripts, enrichment tools, and marketplace listings can be linked together into simple pipelines, reducing the time between infection, analysis, and resale.
While these systems are not fully autonomous, human-guided targeting and workflows are becoming faster and more structured. As profits from simple password dumps decline, efficiency becomes critical. Automation helps close the gap between data theft and monetization. This is no longer theoretical. AI-assisted tooling is already being used to generate phishing lures, process stolen data, and accelerate campaign setup.
The direction is clear. Infostealer operations are shifting from manual processing toward integrated systems.
The Agentic Transition
What previously required multiple actors — distribution, log processing, targeting — can increasingly be handled within a single workflow. Early signs of this shift are already visible outside the criminal ecosystem. Technology analyst Nate B. Jones has described a “phase change” in autonomous coding, noting that sessions that failed within minutes a year ago can now run for weeks and produce production-grade software. The architectural leap is significant, and its implications extend beyond legitimate development.
The criminal infostealer model has long been constrained by labor. Operators must configure stealers, manage distribution infrastructure, process logs, validate credentials, and decide what to monetize and where. Each stage introduces friction. Each bottleneck limits scale.
Agentic systems reduce those constraints. An agent capable of sustained, multi-step execution can identify targets, generate convincing phishing lures, deploy and rotate infrastructure, ingest and triage credential logs, cross-reference high-value services, and trigger downstream fraud with minimal human oversight. The model shifts from labor-intensive coordination across coders, distributors, and processors to a more continuous and self-directed workflow.
The implications are straightforward: as barriers to entry decline, volume scales without a proportional increase in cost and effort. The shorter timeline between compromise and monetization forces defenders to confront an ecosystem operating faster and with greater adaptability than before.
Vibecrime and Criminal Orchestration
A recent TrendAI™ study, “The Next Phase of Cybercrime Agentic AI and the Shift to Autonomous Criminal Operations,” highlights the shift from human-coordinated operations toward agentic, system-level orchestration. The research draws parallels between vibecoding in software development (where high-level intent is translated into working systems by autonomous agents) and what it calls “vibecrime” in the criminal ecosystem.
Vibecrime describes more than AI-assisted attacks, but points to a structural change in who can run operations and at what scale.
Agentic systems introduce an orchestration layer that directs specialized functions such as phishing, reconnaissance, and payload deployment. This mirrors the division of labor already visible in infostealer affiliate programs. Where affiliate models like the CLR Team required separate human roles — managing distribution, payloads, and monetization — agentic workflows collapse them into a single coordinated process. This shift is especially relevant as volume-based credential theft operates under tightening margins.
Agentic systems do more than accelerate existing operations — they change the economics of models already under strain. TrendAI frames this dynamic through what it calls the “Three Laws of Cybercrime Adoption:” rapid uptake follows when an established model weakens and a clearly more efficient alternative appears. Both conditions are now present. Affiliate-driven workflows may represent the last human-centered stage before broader system-level adoption, with the next phase of credential theft resembling systems engineering than traditional malware operations.
This shift is best understood as a loop rather than a sequence: automation increases efficiency, efficiency reshapes attacker economics, and changing economics further promotes system-level operations.
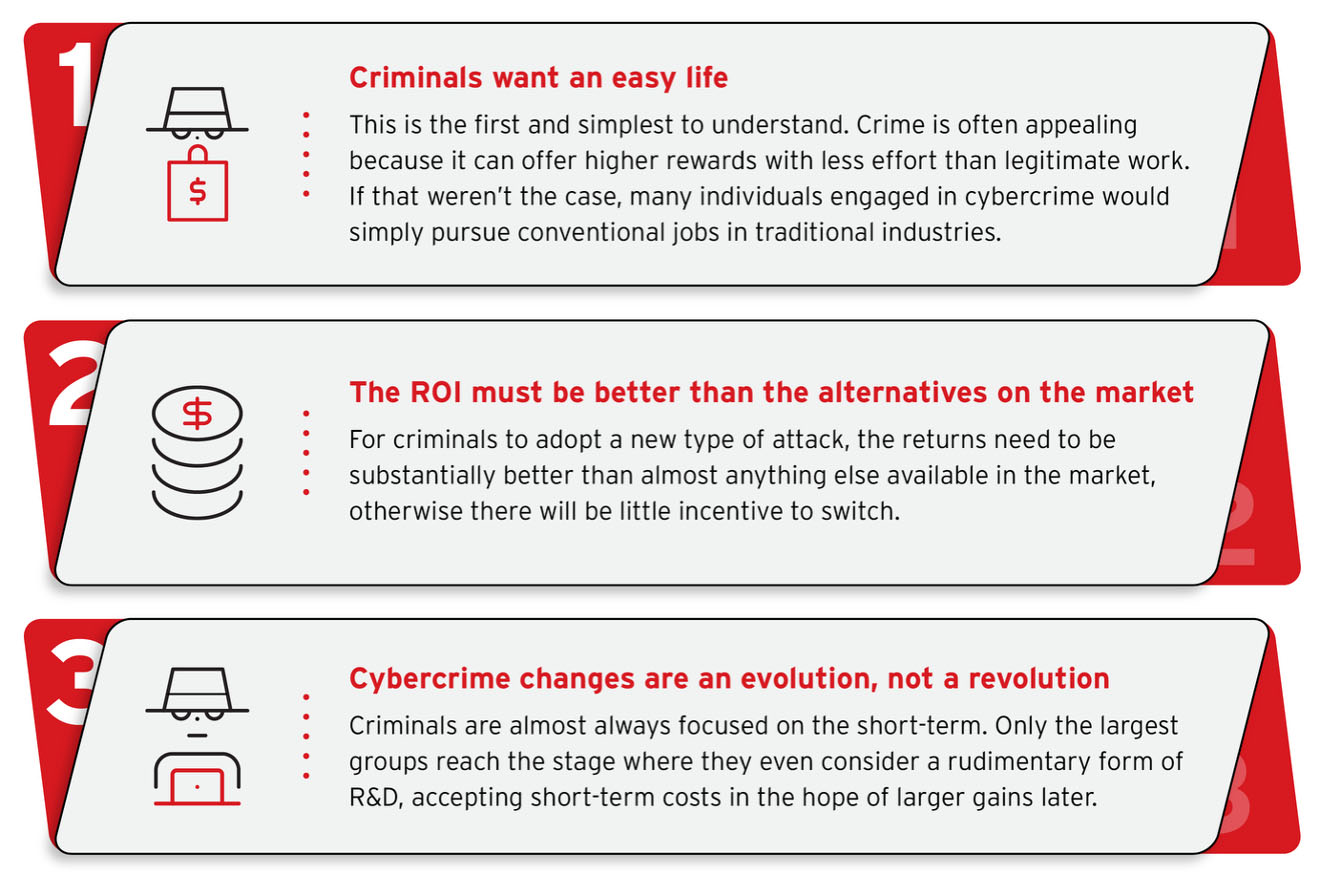
Figure 16. The three laws of cybercrime adoption
The Autonomous Identity Attack Loop
Infostealer-driven operations are increasingly organized around a repeatable cycle: collect, analyze, decide, execute, and learn. Each stage already exists in fragmented form. Automation is now beginning to link them into more cohesive workflows.
Collection remains the entry point. Infostealers continue to supply credentials, session tokens, and contextual data at scale. However, raw logs alone are no longer enough. Value now depends on what can be extracted and how fast this access can be acted on.
Analysis follows. Stolen data can be automatically enriched with public information, behavioral indicators, and platform-specific signals. This allows operators to identify higher-value targets and prioritize them for exploitation. Instead of reviewing logs manually, workflows increasingly rely on automated filtering and scoring.
Decision-making and execution are becoming tightly linked. Once targets are identified, systems can trigger phishing campaigns, infostealer delivery lures, session hijacking
attempts, or account recovery workflows with minimal delay. Compared to manual handling, these actions are faster and more consistent.
The final stage is learning. Outcomes are fed back into the system. Successful lures, effective targeting patterns, and profitable victim profiles shape future activity, with this feedback loop reinforcing efficiency over time.
These stages, summarized in Figure 17, describe an emerging operating model. Infostealers are no longer just collection tools; they are inputs into managed identity attack systems. That shift has direct implications for defenders.
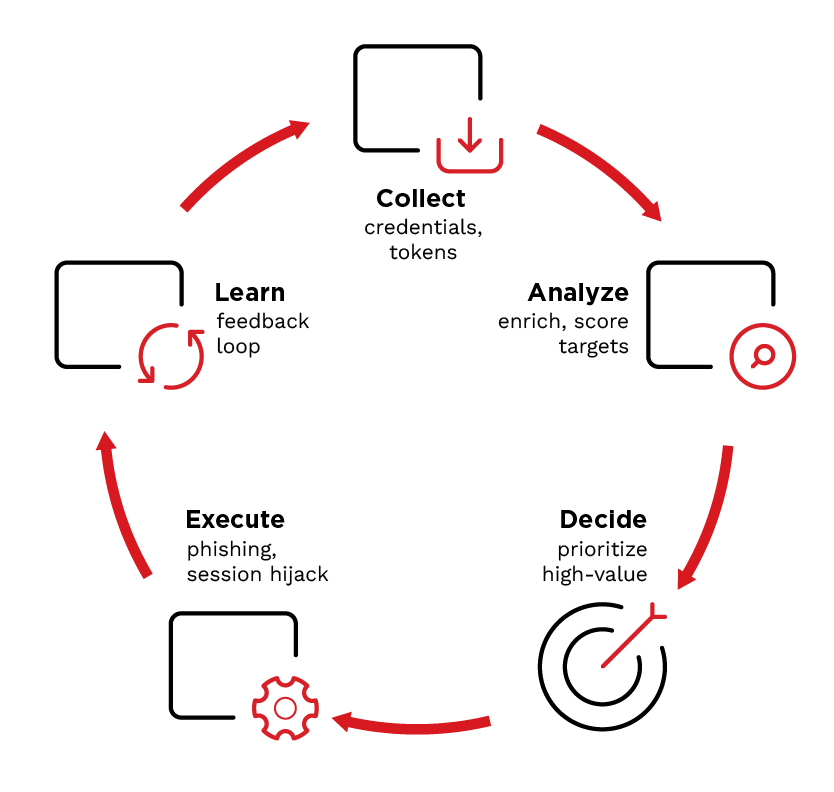
Figure 17. Infostealer attack loop illustrating the repeatable, monetization-focused workflow used in modern operations.
Conclusion: What This Means for Defenders
The evolution of infostealers reflects a broader shift in cybercrime. Operations that once depended on manual effort are becoming structured systems shaped by economics, automation, and changing authentication models. For defenders, this requires a change in focus.
These shifts highlight the need to rethink defensive priorities around identity, session integrity, and response speed. We outline key areas where defenders can most effectively disrupt infostealer-driven workflows and reduce their operational impact.
Key Priorities for Defenders
- See identity use in context
Credential theft is no longer the objective. It is the entry point. Detection must focus on how identities are used after compromise, including session behavior, authentication patterns, and recovery workflows. These signals provide earlier and more reliable indicators of abuse than traditional alerts. - Connect signals across domains
Endpoint activity, phishing exposure, and identity events are often investigated in isolation. In practice, they form a single attack chain. Disconnected visibility slows response and obscures attacker intent. Correlated telemetry enables reconstruction of access paths and identification of downstream risk. - Prioritize based on attacker value
Attackers do not treat all access equally. They focus on identities and access paths that can be monetized quickly. Defenders must apply the same logic. Prioritization should reflect the likelihood of exploitation and business impact, not alert volume. - Interrupt the system, not the symptom
Point remediation is insufficient. Resetting credentials or isolating devices does not remove access if sessions, tokens, or alternate paths remain active. Response must remove all viable access paths before monetization occurs. - Close the loop through learning
Each incident exposes how access was obtained and exploited. That information must feed back into detection, identity posture, and exposure management. Without this feedback loop, the same attack paths remain open.
These requirements define what modern defense must look like in practice. Disrupting identity-driven attack systems depends on the ability to connect signals across identity, endpoint, and communication layers, prioritize risk based on attacker intent, and respond fast enough to interrupt monetization before it occurs.
Effectively doing so requires a coordinated security model that must:
- Correlate activity across identity, endpoint, and communication layers
- Identify high-risk identities and access paths
- Prioritize based on attacker outcomes
- Enable response across all relevant control points
- Continuously reduce exposure based on observed attack patterns
Platforms that unify these capabilities allow defenders to move from reactive investigation to system-level disruption. Translating this into practice requires changes in how security teams operate.
TrendAI Vision One™ is designed to support this model, integrating identity, endpoint, email, exposure management, and threat intelligence into a single operational view to help organizations detect, prioritize, and disrupt identity-driven attack systems.
As attack operations become systems, defense must do the same.
Infostealers are not disappearing. But as these operations become more system-driven, the advantage will increasingly favor defenders who adapt just as quickly.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
HttpContext.GetGlobalResourceObject("ES","RecentPosts")%>
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation