Inteligencia artificial (IA)
Claude Code Packaging Error Remains a Lure in an Active Campaign: What Defenders Should Do
Threat actors leveraged Anthropic’s Claude Code npm release packaging error to distribute Vidar, GhostSocks, and PureLog Stealer. This blog details immediate steps organizations can take and best practices to prevent further risk.
Key takeaways:
- Attackers rapidly leveraged the Claude Code packaging error incident to distribute credential-stealing malware using fake GitHub repositories. This demonstrates how quickly threat actors can exploit public attention following a software supply chain incident.
- Vidar, GhostSocks, and PureLog Stealer were observed to have been distributed through the malicious GitHub releases; these payloads enable credential theft, cryptocurrency wallet exfiltration, session hijacking, and residential proxy abuse across Windows.
- TrendAI Vision One™ detects and blocks the IoCs provided at the end of this blog. TrendAI™ customers can also access tailored hunting queries, threat insights, and intelligence reports to better understand and proactively defend against this campaign.
TrendAI™ Research is continuously monitoring an active campaign that continues to leverage the packaging error in Anthropic's Claude Code npm release to distribute Vidar, GhostSocks, and PureLog Stealer payloads.
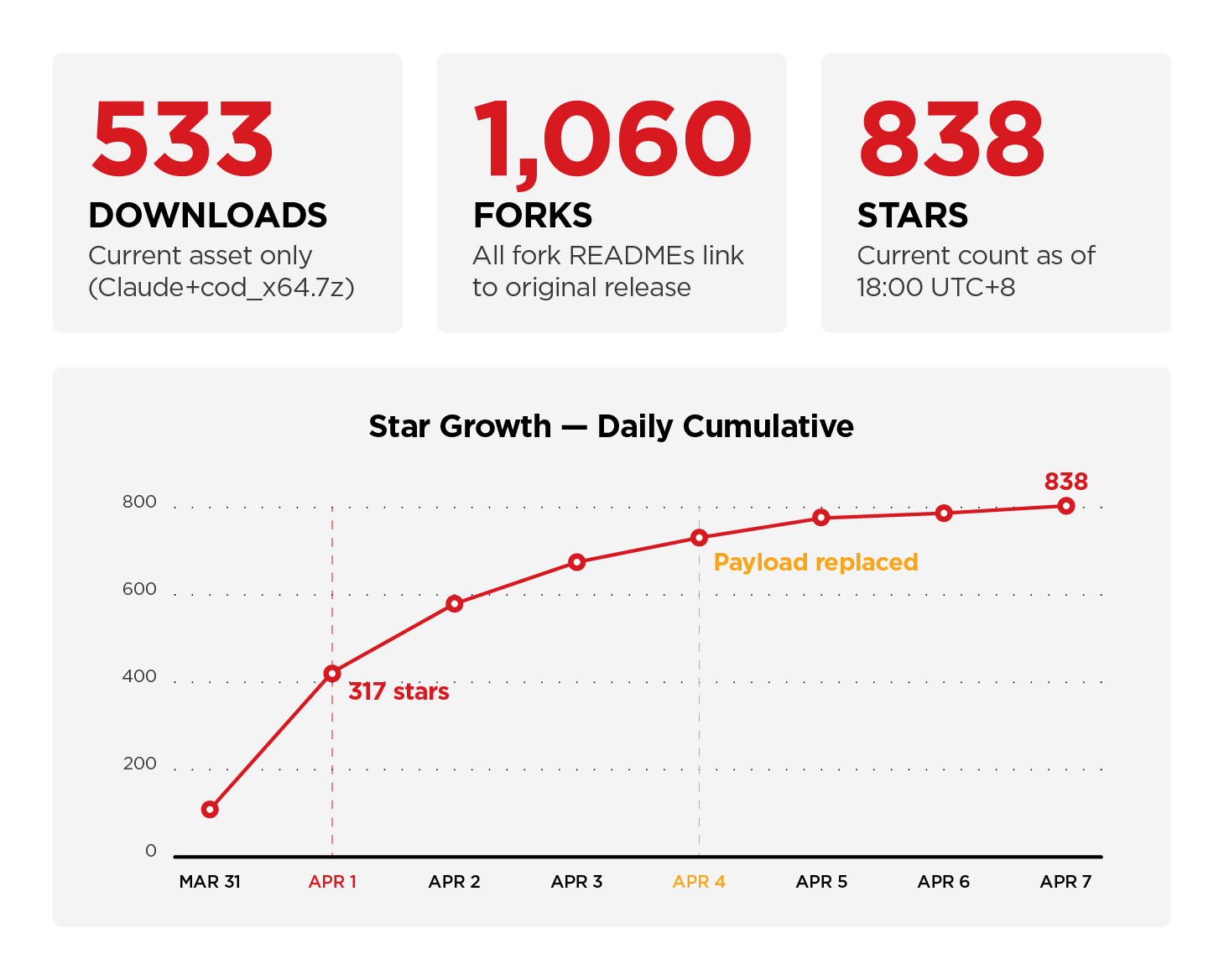
The distribution hub for the leaked Claude Code brand lure campaign was identified as https://github[.]com/leaked-claude-code/leaked-claude-code. It is operated by a GitHub account identified as idbzoomh1, who used the legitimate Claude Code source map leak incident as a lure to deliver payloads via a release asset. A previous account, idbzoomh, has been blocked by GitHub. As of publishing there are no other identified repositories connected to the campaign; TrendAI™ Research will update this blog in the event of new findings.
| Type | Value |
| Threat actor email | blactethe1061@outlook.com |
| Threat actor GitHub account | idbzoomh1 |
| Current Download URL | hxxps[:]//github[.]com/leaked-claude-code/leaked-claude-code/releases/download/leaked-claude-code/Claude_code_x64[.]7z |
| Payload (replaced) | ClaudeCode_x64.7z (active from 2026-03-31 14:05 PST to 2026-04-04 18:00 UTC+8) |
| Payload (replaced) | Claude-Code_x64.7z (active from 2026-04-04 17:36 PST to 2026-04-04 18:00 UTC+8) |
| Payload (current) | Claude_code_x64.7z (533 downloads as of 2026-04-07 18:00 UTC+8) |
Table 1. Threat actor identifiers and distribution artifacts
The social engineering threat became a part of a broader malware distribution campaign that has been active since February 2026. We have observed cycling through more than 25 software brands (e.g., AI tools, crypto bots, and creative software) across trojanized archives, delivering a Rust-compiled dropper payload.
Payloads delivered and impact scope
Different malware payloads were observed to have been distributed through the malicious GitHub releases:
- Vidar is a stealer known to perform multi-threaded data theft targeting browser-stored credentials, cryptocurrency wallets, session tokens, and system information. Stolen data is exfiltrated to attacker-controlled C&C infrastructure resolved through dead drop profiles on Steam Community and Telegram.
- GhostSocks has been observed in previous campaigns to establish a SOCKS5 proxy on the victim's machine, allowing the threat actors to tunnel network traffic through compromised hosts. This effectively turns infected machines into residential proxy infrastructure for further operations.
- PureLog Stealer is a .NET information stealer known to harvest Chrome credentials, browser extensions, cryptocurrency wallets, and system information. It executes entirely in memory using a multi-stage fileless loader chain to evade detection.
The combined functionality of the malware payloads enables credential theft, cryptocurrency wallet exfiltration, session hijacking, and residential proxy abuse across Windows, giving the operators multiple monetization paths from a single infection.
As of April 7, 2026, 18:00 UTC+8, there are 838 stars, 1,060 forks, and 533 confirmed downloads of the new payload archive. It should be noted that there have been previous download links that have been deleted or replaced; the download counts for which cannot be retrieved anymore. The actual download numbers will likely continue to rise.
What organizations should do
TrendAI™ protections
Organizations can take advantage of TrendAI Vision One™, which is equipped with pattern updates, behavioral detections, and web reputation blocks that can help provide protection against this campaign, as well as hunting tools that can be used by customers to investigate potential exposure.
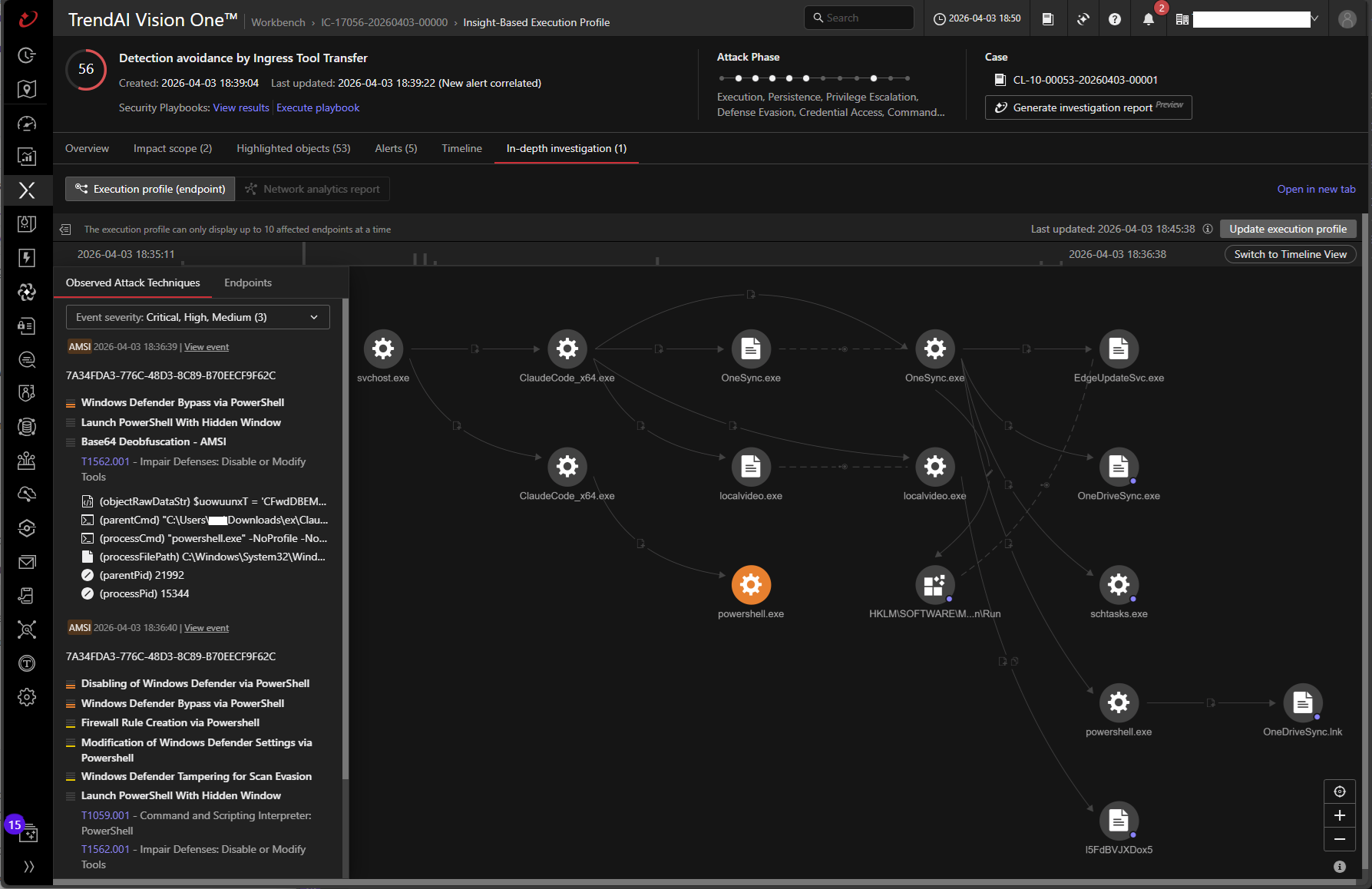
Utilizing Observed Attack Techniques (OAT)
TrendAI Vision One™ customers that use endpoint and server protection solutions may go into the Observed Attack Techniques section of the TrendAI Vision One™ console to look for suspicious activity that may indicate the detection of malicious behavior associated with this threat.
Potential indicators include:
- Execution of Claude with Leaked Version
- Possible Claude Code Related File Download
- AWS Claude Leak UserAgent
- TrojanSpy Malware Detection [F2021]
- Malware Detection [F4986]
- Predictive Machine Learning Detection [F2039]
- Threat Type Prioritization Trojan Detection [F3592]
- File Detection for Amadey [F3362]
- URL Access Blocked - C&C Server
- URL Access Blocked - Malware Accomplice
- URL Access Blocked - Disease Vector
TrendAI Vision One™ Workbench Alerts
The Workbench serves as a crucial tool for monitoring and responding to security alerts.
- Suspicious Execution from Possible Leaked Claude Code Binary
- URL Access Detection by Web Reputation Service
Patterns, models, and signatures
TrendAI™ solutions that utilize different pattern, behavior monitoring and other advanced detection technology can also detect and protect against the following known malicious components associated with this campaign:
- TrojanSpy.Win64.VIDAR.SMCLX (Smart Scan Agent Pattern 20.863)
- Trojan.Win64.VIDAR.CLX (Smart Scan Agent Pattern 20.863)
- Trojan.Win32.GHOSTSOCKS.SM - (Smart Scan Agent Pattern 20.871)
- TrojanSpy.Win64.VIDAR.SMCX - (Smart Scan Agent Pattern 20.871)
- AG.FLS.ISB.7403T: Prevents spawning of encoded PowerShell.
- AG.3200T: Prevents suspicious self-propagation and persistence.
- 2015Q_CQ: Detects process injection behavior
- TRX5656Q: Trigger AI-assisted detection layer
- 1478T: Detects non-whitelisted processes that exhibit self-propagation and persistence via autorun
- 1770T: Detects non-whitelisted processes that exhibit self-propagation
TrendAI Vision One™ Web Reputation Services (WRS)
TrendAI Vision One™ is also blocking several known C&C servers and Disease Vector IPs and domains known to be associated with this campaign. Verified malicious GitHub repositories and leaked code download links are blocked as Illegal or Prohibited Content.
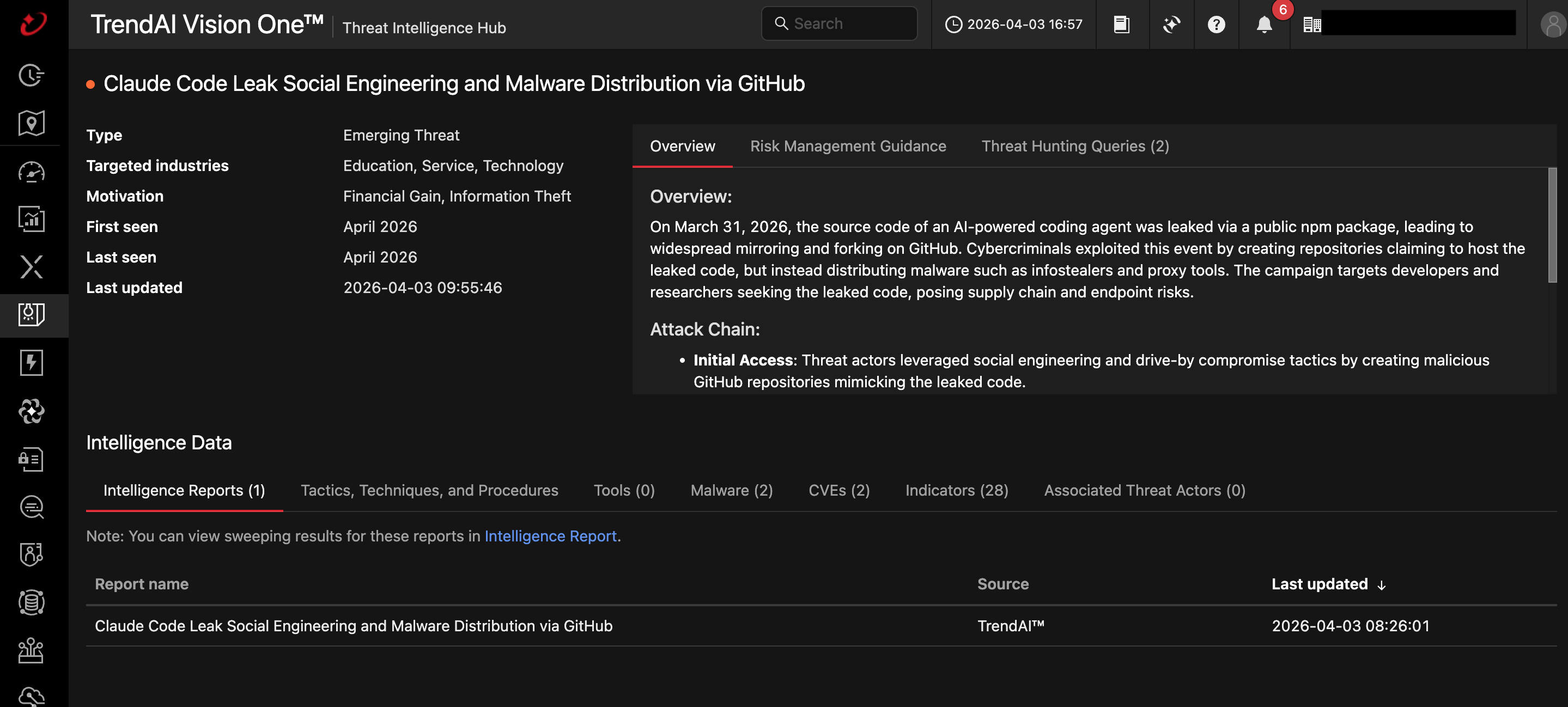
TrendAI Vision One™ Threat Intelligence Hub
TrendAI Vision One™ Threat Intelligence Hub provides the latest insights on emerging threats and threat actors, exclusive strategic reports from TrendAI™ Research, and TrendAI Vision One™ Threat Intelligence Feed in the TrendAI Vision One™ platform.
Emerging Threats: Claude Code Leak Social Engineering and Malware Distribution via GitHub
Intelligence Reports (IOC Sweeping)
Hunting Queries
TrendAI Vision One™ Search App
TrendAI Vision One™ customers can use the Search App to match or hunt the malicious indicators mentioned in this blog post with data in their environment.
Detection of Vidar and GhostSocks malware components
malName: *VIDAR* OR *GHOSTSOCKS* and eventName: MALWARE_DETECTION
Detection of Vidar C&C communication
eventSubId:204 AND dst:("rti.cargomanbd.com")
More hunting queries are available for TrendAI Vision One™ customers with Threat Intelligence Hub entitlement enabled.
Additional mitigation guidance
The following best practices are also recommended to secure enterprises systems from the threats discussed in this blog:
- Secure developer workstations. As AI and Agentic Systems are increasingly adopted, enterprises must log developer workstation source code, intellectual property, cloud tokens, API keys, and GitHub credentials with a good EDR with behavioral protection. Developer workstations should only be used for official business to minimize risk.
- Enforce a zero trust strategy for shared or downloaded code. Never assume that everything shared is "safe,” and inspect developer ranking and history before downloading code. In this campaign where egress and direct proxy abuse (GhostSocks) was used monitoring the network for developer and access is also good practice. Trend Vision One™ Zero Trust Secure Access (ZTSA) products can bolster existing network restrictions.
- Ensure development happens in a safe environment. Use VM-based development environments and non-privileged containers and monitor access of developers for network access, credentials, and keys; this makes it easier to contain a developer breach happens in the event of one.
- Restrict tools to those what are allowed. Only use licensed tools and applications to limit exposure to vulnerabilities. Licensed tools and applications guarantee access to secure updates, vendor support, and verified code. Enterprise environments have licensed tools and applications.
- Rotate developer credentials. Ensure that browser tokens, GitHub credentials, cloud API keys, local config files are short-lived by rotating them. This minimizes risk and limits the damage from compromise by reducing the exposure making stolen credentials useless shortly after they are acquired.
This incident underscores that security compromise is not limited to software vulnerabilities: it can also come from human and organizational gaps that can be exploited by tried-and-tested social engineering techniques that prey on alarm and urgency. This gap is widened as organizations increasingly adopt agentic environments. That’s why TrendAI™ is designing solutions as an Agentic Governance Gateway, which can empower organizations to discover, observe, understand, detect, and enforce governance over agentic AI behaviors and environments, ensuring safe and reliable adoption of autonomous AI.
This entry will be updated as new information emerges from our monitoring and analysis.
Indicators of Compromise (IoCs)
The updated list of IoCs can be found here.