How Operation Tropic Trooper Infiltrates Secret Keepers
 View research paper: Operation Tropic Trooper - Infiltrating Networks via Exploit-Laced Images
View research paper: Operation Tropic Trooper - Infiltrating Networks via Exploit-Laced Images
Taiwan and the Philippines are targets of “Operation Tropic Trooper,” an ongoing campaign that has been found to be using old infiltration tactics—two commonly exploited Windows vulnerabilities, social engineering methods, and basic steganography—to steal state and industry secrets since 2012.
Operation Tropic Trooper attackers specifically targeted government institutions, military agencies, and companies in the heavy industry in the countries mentioned. Note that the successful infiltration of many of their targets using tried-and-tested techniques could have been prevented or prepared for using proactive methods and technologies like vulnerability patching, security training, and antimalware detection.
Threat actors of the said campaign are familiar with their target organizations’ networks and know which hooks to use to bait them. They crafted spear-phishing emails attached with seemingly interesting documents that hint at planned bombings, resumes, or government budget. The attached documents attack two commonly exploited Windows vulnerabilities, CVE-2010-3333 and CVE-2012-0158 to be able to run a Trojan.
[Read: Most Commonly Exploited Vulnerabilities Related to Targeted Attacks]
The Trojan, TROJ_YAHOYAH, eventually downloads and decrypts a malicious image or decoy file. The downloaded images appear harmless and look similar to default wallpapers in Windows XP systems. However, encrypted into them via simple steganography is BKDR_YAHAMAM, a malware that steals data from the system, kills processes and services, deletes files and directories, puts systems to sleep, and performs other backdoor capabilities.
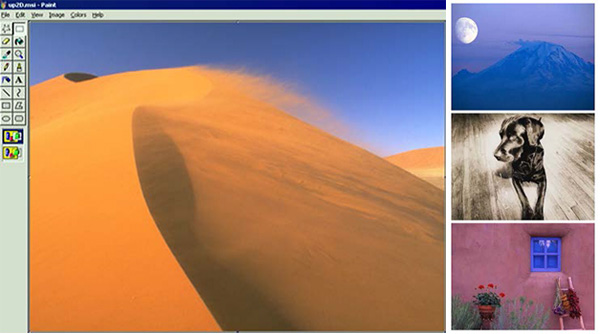
Samples of images used by Operation Tropic Trooper
Defending Against Operation Tropic Trooper
The motivations around this three-year campaign remain unclear. Historically, threat actors attack government organizations and major industries to gather intelligence, steal secrets, or gain a competitive advantage.
Government agencies, military organizations, and heavy industries all harbor secrets that may prove detrimental if destroyed or stolen. The routines found in Operation Tropic Trooper are relatively less sophisticated compared to other targeted attack campaigns, but it has shown that similar targets may still be successfully infiltrated using the same old tactics. Unfortunately, even old threats may work against networks that store highly sensitive information.
The paper recommends building threat intelligence and establishing a custom defense strategy for network administrators to not be victimized by Operation Tropic Trooper.
Technical details of the operation, as well as tactics that can be used to defend against these types of attacks, can be found in the paper “Operation Tropic Trooper: Relying on Tried-and-Tested Flaws to Infiltrate Secret Keepers”.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
HttpContext.GetGlobalResourceObject("ES","RecentPosts")%>
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation