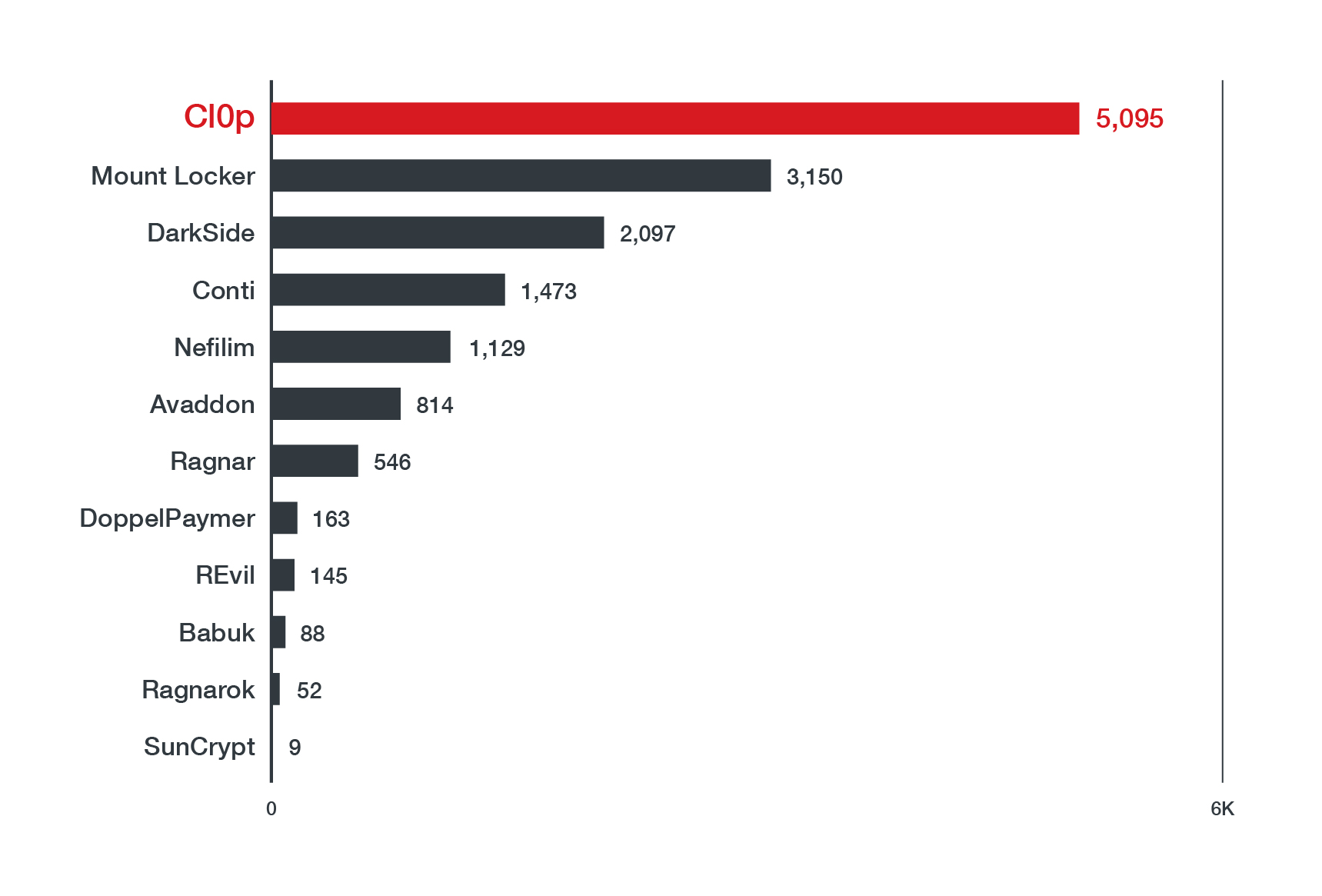
Ransomware has a long history with big business, as malicious actors have been known to set their sights on targets with deeper pockets in hopes of a lucrative payout: A recent spate of high-profile modern ransomware attacks on enterprises highlights how online extortionists can cause wide-scale operational disruptions and upset global supply chains. In May, Colonial Pipeline, which runs the largest petroleum pipeline in the US, were forced to take some of their systems offline to contain a ransomware outbreak perpetrated by the cybercrime group DarkSide — an attack that pilfered 100 GB of their data. The world’s biggest beef supplier, JBS, suffered a similar attack from the REvil group that debilitated their computer systems just weeks later. Based on Trend Micro's latest report on modern ransomware, REvil and DarkSide rank among the ransomware actors that have stolen and leaked the largest amounts of data online, as shown in Figure 1.
Blue-chip businesses are not the only ones that have been hit hard by the recent ransomware strikes. Threats to business continuity can have rippling effects on consumers as well, as evidenced by the mass fuel hoarding that followed the temporary shutdown of Colonial Pipeline’s petrol pipeline; meanwhile, there were speculations of meat shortages when several JBS plants halted production to investigate the cyberattack. Both were quick to resume operations, but neither came out on the other side unscathed. Colonial Pipeline had initially forked over US$4.4 million to DarkSide, a bulk of which they were able to recover. However, JBS decided to pay REvil US$11 million to protect their customers, even after recovering most of their systems on their own.
In light of the ongoing pandemic, some threat operators pledged to ease up on healthcare companies last year, but not all are as obliging, as attacks on hospitals and healthcare providers have continued to surface since then. Ransomware infection is costly for companies not only because of the high payment demanded by the threat actors behind the operation, but also because of the losses in revenue that they rack up, not to mention the decline in productivity during the resulting downtime. However, these disasters are avoidable if industry players take steps to shore up defences around their IT infrastructure. Here, we outline some best practices and countermeasures to avert any shakedowns at the hands of cybercriminals:
Develop and test a formal incident response plan
Cybercriminal groups count on catching their victims unawares, so enterprises should be prepared with a playbook that can guide their response team in the event of a cyberattack. The playbook ought to detail the procedures that the team will take to validate, analyse, and contain an infection so that their organisation can get back on its feet as soon as possible. Many have modelled their own playbooks after incident response frameworks such as that of the National Institute of Standards and Technology (NIST) and SysAdmin, Audit, Network, and Security. Companies can also put their playbooks to the test by proactively running drills, wherein their security team would be tasked with tackling simulated breaches and other emergency scenarios. These exercises will evaluate their response readiness and give them ample time to come up with alternative recommendations should parts of their contingency plan be found lacking.
Implement a least-privileged approach
To prevent unauthorised users from snooping around their networks, companies need to take stock of the access rights of their employees, as well as those of other stakeholders like clients and vendors. Sticking to the principle of least privilege ensures that when workers log in to the company's network, their account permissions are limited to only what they need to perform their tasks. Additionally, it's important for companies to routinely conduct entitlement reviews in order to keep tabs on who has access to which systems. User access has to be carefully managed, as privileges might need to be granted or modified depending on a person’s role in the company, or else revoked when they leave.
Patch any vulnerabilities in the enterprise’s network
Unpatched computers are an easy mark for ransomware operators. Businesses must immediately implement security updates that are released for business-critical endpoints and servers, as these include the latest fixes to any newly discovered bugs. Installing patches for enterprise-level systems could involve some maintenance downtime, so it is important to note that any delays present threat actors with a window of opportunity to capitalise on these vulnerabilities. Virtual patching can also be used to secure legacy systems for which patches are not yet available.
Remove any outdated systems
By minimising their network’s attack surface, enterprises are in a better position to safeguard critical company assets. The Colonial Pipeline breach was traced back to an inactive VPN account that was compromised, underscoring how easily exploits on outdated systems go unnoticed when companies fail to clean house. Part of network hardening means being vigilant about monitoring all possible entry points to an enterprise’s systems: Any that are out-of-date, superfluous, or no longer in use need to be isolated from the rest of the network, if not removed entirely, before malicious actors can take advantage of them.
Practise the 3-2-1 backup rule
A multilayered defence against ransomware includes a solid backup strategy, in case cybercriminals ever manage to encrypt a company’s important information and threaten to expose it. It has become an industry standard for enterprises to maintain at least three copies of their data in two different formats, with one air-gapped copy located off-site. Storing multiple copies of up-to-date data is essential for companies to bounce back from any breaches, much like how most of JBS’ systems were promptly restored, thanks in part to the company’s backup servers. However, these strategies still need to be routinely tested to ensure that there are no errors or delays in the backup process, and also so that the preserved data remains retrievable and complete.
Secure employees’ work-from-home (WFH) setup
More employees are now transitioning to remote work, which calls for enterprises to set and strictly enforce IT policies that are tailored to the needs of a distributed workforce. Potential security gaps in home offices, like the use of unsecured personal devices or residential networks, can put an entire company at risk of data loss and theft — if compromised, these can be weaponised as attack vectors. Ideally, workers will have access to company-issued devices and VPNs that make it easier for them to adhere to data protection standards while they’re on the clock.
Thwart phishing attempts that trick employees into downloading ransomware
Phishing, one of the most prevalent online scams around, is a common means for threat attackers to gain a foothold into a company’s network. Phishing emails entice a receiver to click on malicious links and attachments that can secretly deploy malware or collect credentials that cybercriminals use to infiltrate a network. Because it’s such an oft-used delivery method for ransomware, employees need to be made aware of how to spot red flags indicating that a message could be fraudulent. To beef up their defences, companies can also make use of security solutions, such as Trend Micro Cloud App Security, that are capable of identifying and blocking suspicious emails.
Ultimately, prevention is still the best strategy for dealing with modern ransomware. For enterprises, a strong security posture relies not on a single measure, but rather on a comprehensive, coordinated effort that can withstand the evolving tools and resources at threat actors’ disposal. Solutions like the Trend Micro Vision One™ platform, which effectively tracked malware like the Conti ransomware by correlating and flagging malicious activity in a system, can help security teams stop cybercriminals before they can initiate their attacks.

