Do Online Mainframes Compomise Business Processes?
Exposing a mainframe online, even unintentionally, can be detrimental to the security not only of the company’s crown jewels, but also their customers. This is what we found using data from Shodan, a search engine for internet-connected devices.
Legacy mainframes are still used by enterprises to handle big data transactions across a range of industries, from financial institutions, telecoms, and internet service providers (ISPs) to airlines and government agencies.
Why are they still in use? As the saying goes: “if it ain’t broke, don’t fix it”. But what if they’re not necessarily “broken”—but unsecure? Exposing a mainframe online, even unintentionally, can be detrimental to the security not only of the company’s crown jewels, but also their customers. This is what we found using data from Shodan, a public search engine for internet-connected devices.
Exposed mainframes can lead to business process compromise
Mainframes—the “big irons” of businesses—are high-speed computers serving as the backbone of an enterprise’s workstations, peripherals, and other connected devices. Unlike supercomputers that are used for high-speed computing and data crunching, mainframes serve other business-oriented purposes, such as transaction processing and handling of server data.
Mainframes are used to handle and manage large-scale data and transactions in real time and in a scalable manner. They serve a wide range of purposes, and are used in banking, airline and hotel bookings, sending and receiving SMS messages, handling ATM transactions, administering payroll, retrieving electronic health records.
There are significant repercussions if the mainframes that process these services are compromised. Among them: tampering the actual data (via middleware), spying on a target’s transactions, exfiltrating customer metadata, even disrupting and delaying transactions. It can even endanger devices connected to an exposed mainframe, such as servers and the data stored on them.
Attacks and vulnerability exploits in mainframes as well as Customer Information Control System (CICS) hacking have already been demonstrated by researchers Philip Young, Bart Kulach, and Ayoub Elaassal. They’ve illustrated how exposed mainframes are prone to distributed denial-of-service (DDoS) and brute force attacks as well as CICS hacking. These security gaps can then be leveraged to compromise an exposed mainframe, which can plausibly result in business process compromise (BPC).
BPC entails targeting an organization’s mission-critical processes, functions, and systems in a way that favors the attacker’s motive—typically financial gain. Recent cases of BPC include the cyber heist on Bangladesh’s central bank and similar operations that targeted banks in Vietnam and Ecuador, which involved compromised SWIFT-related processes. The hack on a container tracking system in Belgium’s Antwerp Seaport is also an example of BPC.
So why are these mainframes exposed? It’s likely that these mainframes weren’t protected by frontline security mechanisms to begin with, making them discoverable in Shodan, and in turn easily accessible. It’s also possible that their security settings were poorly configured, or perhaps the machines were left exposed—intentionally or unintentionally—to the internet for some reason.
Analyzing Shodan data
Shodan data showed that legacy mainframes, particularly the IBM OS/390 (zSeries) and IBM AS/400 (iSeries) as well as their corresponding FTP and web servers, were exposed. The data also revealed that telecoms and ISPs were the industries with the most number of exposed/online legacy mainframes.
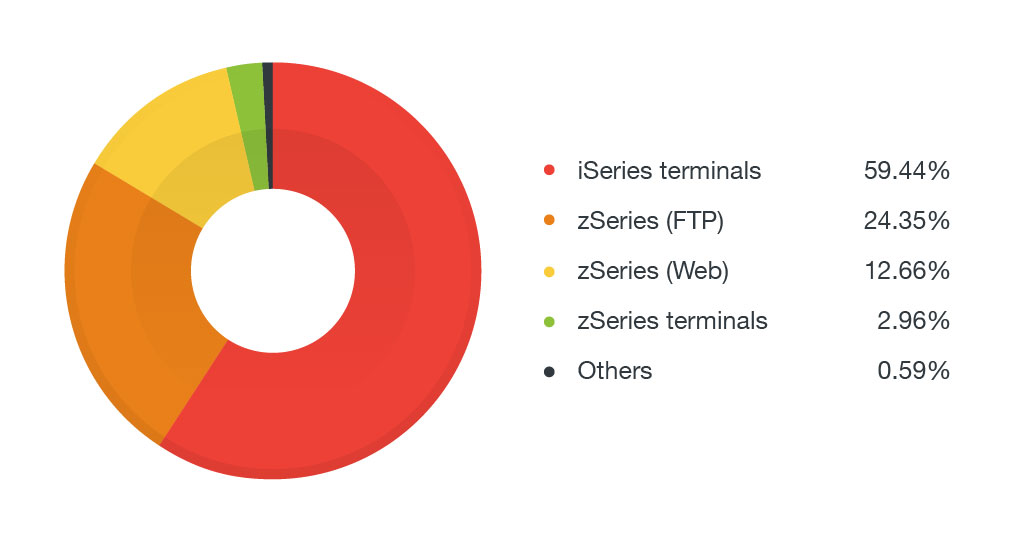 Figure 1: Exposed mainframes and related services by model
Figure 1: Exposed mainframes and related services by model
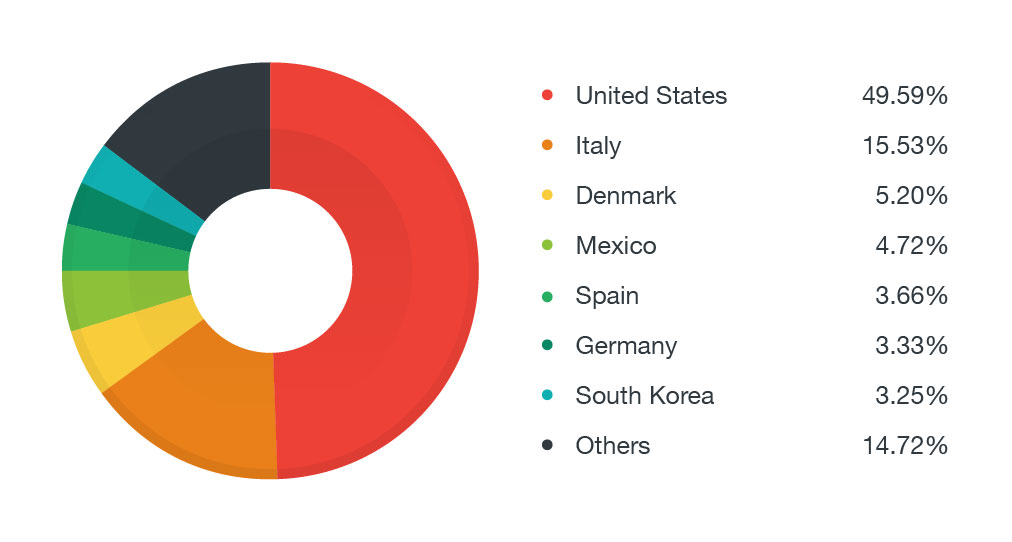 Figure 2: Top countries with exposed mainframes and related services
Figure 2: Top countries with exposed mainframes and related services
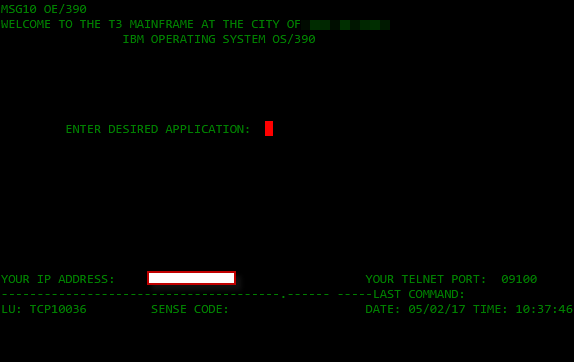
Figure 3: Exposed zSeries terminal
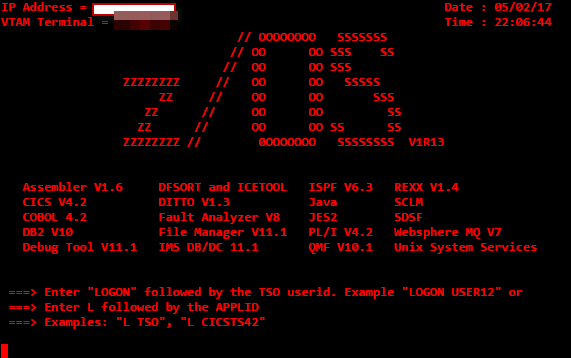
Figure 4: Exposed z/OS VTAM terminal
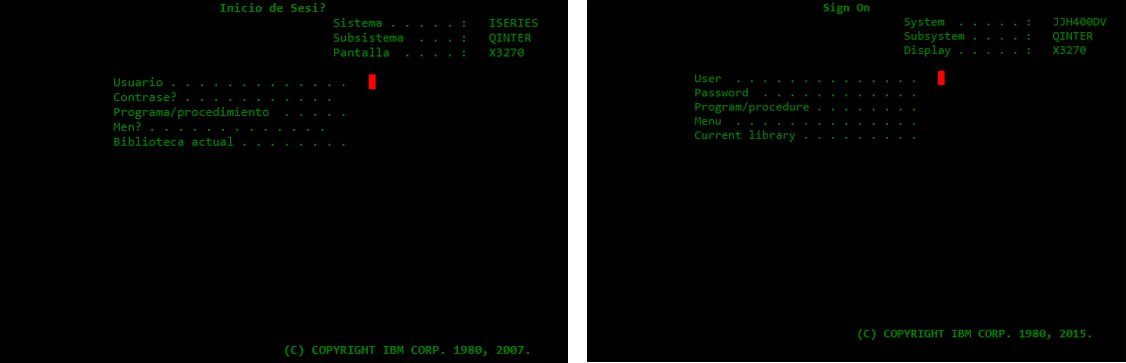 Figure 5: Exposed AS/400 terminals
Figure 5: Exposed AS/400 terminals
It’s worth noting that while the number of exposed mainframes increased during our one-month Shodan search, some of the exposed mainframes we saw during our initial Shodan queries were no longer accessible online. This indicates that its administrators were able to determine that their terminals were exposed and was able to take them off the internet.
Vulnerabilities exacerbate the risks to exposed mainframes
The risk of attacks on an exposed mainframe increases with vulnerabilities. Security flaws in CICS, a middleware designed to support raid and high-volume online transactions and processes, can also be compromised to perpetrate BPC.
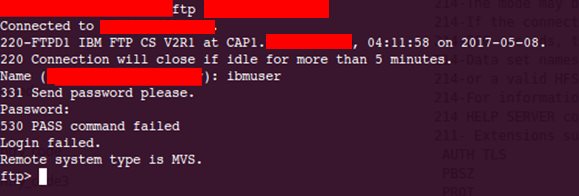
An unsecure FTP also serves as entry points from which attackers can gain unauthorized access to services running in mainframes. FTPs are typically used to upload transaction commands in the mainframe, such as Job Control Language (JCL), which is equivalent to a bash script in Linux or batch file in Windows, and Restructure Extended Executor (REXX), which is similar to Python. If an FTP is successfully compromised and accessed, attackers can upload a malicious JCL program. If given executable permission to run it and with enough privileges in the terminal, it can execute arbitrary commands to infiltrate a mainframe server.
A more practical approach for attackers is to use a vulnerable FTP server to exfiltrate mainframe data by hacking the network via tailored JCL or REXX scripts, or downloading sensitive data already on the FTP server. Regardless of the methods, their endgame is the same: exfiltrating sensitive data, creating backdoors to access the mainframes, or snooping in on the mainframe’s transactions.
Figure 6: Screenshot of an exposed FTP (header)
Here are some of the notable vulnerabilities affecting IBM mainframes:
- CVE-2012-5951 – a privilege escalation vulnerability that can elevate a compromised account into a superuser (system administration-level access). An example would be the use of a JCL file containing an implementation of another security flaw, CVE-2012-5955, which was linked to the Logica mainframe breach reported in 2013. An exploit for this became publicly available.
- CVE-2007-2026 – a vulnerability that, when exploited, will cause the affected machine to consume excessive CPU resources, resulting in denial of service (DoS).
- CVE-2013-5385 – a vulnerability related to how the Open Shortest Path First (OSPF) routing protocol is implemented in z/OS on zSeries servers (6.1 and 7.1), and how it’s not validated on Networking Operating System (NOS). Exploiting this vulnerability can cause routing disruptions/DoS or allow an attacker to gain sensitive packet data. CVE-2013-0149 is a similar security flaw.
There are 8 known/publicly disclosed vulnerabilities affecting AS/400 models, all of which were reported between 2002 and 2008. These security flaws expose the system to risks that include DoS, DoS overflow, cross-site scripting (XSS), bypassing of firewall rules, privilege escalation, and information theft. There are also a number of reported and publicly known vulnerabilities affecting IBM applications and firmware, including server and OS-related products. Though we have not seen attacks that actively exploit these vulnerabilities, these security flaws can also serve as doorways from which attackers can compromise exposed mainframes. Many of these applications can actually be connected to mainframes and run in Linux OS on top of newer z/OS mainframes, like LinuxONE.
Attackers can also brute force a terminal’s credentials. TSO Brute is a tool for doing this on a terminal with Time Sharing Option (TSO), granting attackers unauthorized access to TN3270 (a terminal emulator used for connecting to mainframe consoles). An attacker can then leverage a vulnerability to change user permissions, such as elevating a restricted account to a superuser. This can be mitigated with a properly configured monitoring system that can detect these kinds of attacks, since all login attempts are recorded.
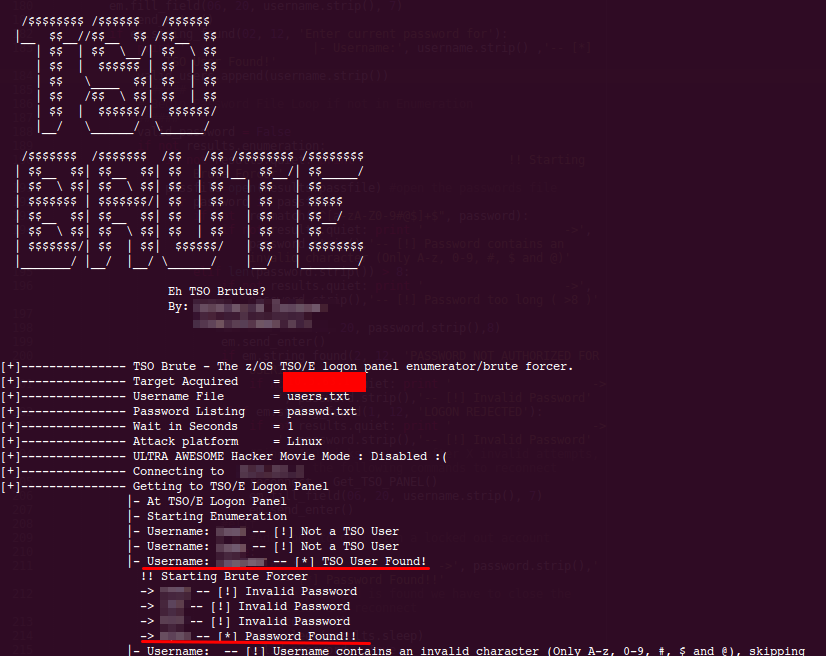 Figure 7: A sample TSO brute force tool
Figure 7: A sample TSO brute force tool
Mind your gaps
An exposed environment can draw cybercriminal attention. Given how mainframes are the cogwheels that steer a lot of enterprise operations, organizations understand that securing them means staying in business. So what can they do?
Be preemptive. Intrusion detection and prevention systems help monitor networks and mainframes connected to them for any incursion attempts. These can be deployed on top of firewalls and IP filtering to limit access to networks and prevent attacks from the inside.
IT/system administrators should also be more prudent. Using Virtual Private Networks (VPNs), adding authentication policies for accessing mainframe terminals, and implementing a strong auditing process that proactively sets a baseline for security policies and restrictions, are just some the best practices they can adopt. More importantly, follow your manufacturer’s recommendations; IBM has guidelines and documentation on how to further protect mainframes and better secure their communication and networking architecture.
Many of the major vulnerabilities are relatively dated, with patches that have long been available. Other unreported vulnerabilities often tend to be related to services deployed in mainframes, such as security flaws in web-based services or FTP servers. Why are these services still vulnerable? Put simply, they’re old. That won’t deter hackers though, as there are existing, publicly available tools that can be used to exploit these vulnerabilities. Even hacked/leaked credentials can also be used in brute force attacks to access exposed mainframe terminals.
Indeed, mainframes are far from being legacy servers and are, in fact, still vital to the business processes they underpin, which when compromised can have significant impact. Ultimately, putting them out of cybercriminals’ reach is a must: mitigate the lapses in your mainframe’s security, patch their vulnerabilities, and enforce proactive security policies in your mainframe.