Exploits & Vulnerabilities
Update Now: PaperCut Vulnerability CVE-2023-27350 Under Active Exploitation
Two vulnerabilities in PaperCut have been found, and one of them is being actively exploited in the wild. This blog entry provides a summary of the vulnerabilities, and includes security guidance for IT and SOC professionals.
Updated on April 27, 2023 10:40 p.m. EDT: We updated the entry to include information on the discovery of LockBit as the malicious payload and add Trend Micro Cloud One™ solutions.
Updated on April 26, 2023, 4:12 a.m. EDT where we added details on an observed instance through Trend Micro Managed XDR where we believe the vulnerabilities detailed in this blog were abused by threat actors. We also added Trend Micro Deep Discovery Inspector rules which can help protect against potential exploitation of the vulnerabilities discussed.
Trend Micro’s Zero Day Initiative (ZDI) discovered two vulnerabilities, CVE-2023-27350 and CVE-2023-27351, in Papercut, a print management software solution that is used by over 100 million users globally. Evidence was found that one of these two vulnerabilities, CVE-2023-27350, is being actively exploited by malicious actors for remote code execution (RCE). This blog entry provides an overview of the vulnerabilities and includes information that IT and SOC professionals need to know.
How can CVE-2023-27350 be exploited?
CVE-2023-27350, which affects PaperCut MF and NG products, was found to have been exploited in the wild (ITW) in the middle of April. This vulnerability is also identified as ZDI-23-233.
The critical-rated CVE-2023-27350 has a vulnerability severity score of 9.8. It can be abused by an unauthenticated attacker to perform RCE on an unpatched PaperCut Application Server.
On April 18, 2023, a PaperCut customer reported suspicious activity, which suggested that unpatched servers are being exploited through CVE-2023-27350. Based on PaperCut's investigation, the earliest suspicious activity that's possibly related to CVE-2023-27350 dates back to April 14, 2023.
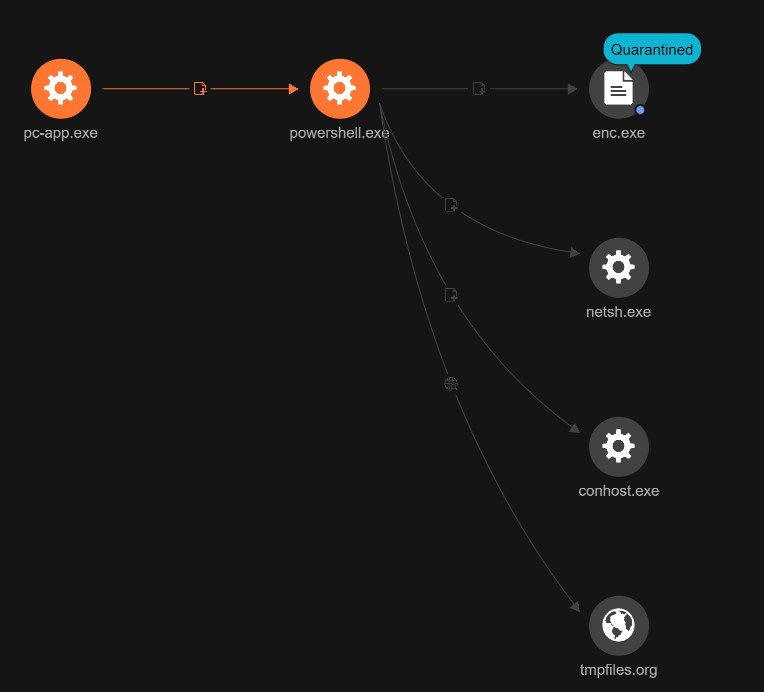
Trend Micro Managed XDR observed an instance wherein this vulnerability is believed to have been abused by malicious actors. Upon the successful exploitation of the vulnerability, pc-app.exe (PaperCut NG/MF) can be used for RCE. In this case, the malicious actors chose to run a PowerShell script via the exploited app. This PowerShell script downloaded and ran a malicious payload, and used netsh.exe to circumvent the firewall. The malicious actors used a temporary hosting site for the malicious payload, one that conveniently deletes all uploaded files after 60 minutes.
Our analysis indicates that the malicious payload enc.exe is the LockBit ransomware (detected by Trend Micro as Ransom.Win32.LOCKBIT.SMYXCJN), based on the binary found in the user Downloads folder that the malicious actor created. LockBit, which is the most prevalent ransomware family according to our Q4 2022 Ransomware Report, continues to dominate as the most active ransomware-as-a-service (RaaS) provider. Considering the previous intrusions that the malicious actors behind LockBit have deployed, we will continue to observe this active threat as it targets more potential victims with possibly even more payloads.
What can threat actors steal when exploiting CVE-2023-27351?
The other PaperCut vulnerability, CVE-2023-27351, can allow unauthorized attackers to potentially extract user account information, such as usernames, full names, email addresses, office and department information, and payment card numbers, that is stored within a customer’s PaperCut MF and NG servers. This vulnerability is also identified as ZDI-23-232.
Malicious actors exploiting this vulnerability can also retrieve hashed passwords from internal PaperCut-created user accounts. It is important to note that cybercriminals won’t have access to any password hashes for users synchronized from external directory sources, such as Microsoft 365 and Google Workspace.
According to PaperCut, there is no evidence that CVE-2023-27351 is being used in the wild. CVE-2023-27351 has a severity rating of 8.2.
Which PaperCut products are affected?
The following PaperCut versions and components are affected by CVE-2023-27350:
- PaperCut MF or PaperCut NG version 8.0 or later, on all OS platforms
- PaperCut MF or PaperCut NG Application Servers
- PaperCut MF or PaperCut NG Site Servers
Meanwhile, the following PaperCut versions and components are affected by CVE-2023-27351:
- PaperCut MF or PaperCut NG version 15.0 or later, on all OS platforms
- PaperCut MF or PaperCut NG ApplicationServer
PaperCut components or products that are not included in the aforementioned lists are not affected by the two vulnerabilities discussed in this blog entry.
What can organizations do to prevent and mitigate the risks associated with CVE-2023-27350 and CVE-2023-27351?
Both these vulnerabilities have been fixed in PaperCut MF and NG versions 20.1.7, 21.2.11, and 22.0.9. Organizations can find instructions on how to update their PaperCut versions via PaperCut’s vulnerability bulletin.
Because the original submission of these vulnerabilities was done through Trend Micro’s Zero Day Initiative, Trend Micro has also released rules and filters that can help provide protection against the potential exploitation of these vulnerabilities.
Trend Micro Cloud One - Network Security & TippingPoint Protection Filters
- 42626: HTTP: PaperCut NG SetupCompleted Authentication Bypass Vulnerability (ZDI-23-233)
- 42258: HTTP: PaperCut NG SecurityRequestFilter Authentication Bypass Vulnerability (ZD-23-232)
Trend Micro Cloud One - Workload Security & Deep Security IPS Rules
- 1011731 - PaperCut NG Authentication Bypass Vulnerability (CVE-203-27350)
- 1011732 - PaperCut NG Authentication Bypass Vulnerability (CVE-2023-27351)
Trend Micro Deep Discovery Inspector
- Rule 4835: CVE-2023-27350 - PaperCut MF/NG Authentication Bypass Exploit - HTTP (REQUEST)
- Rule 4836: CVE-2023-27351 - PaperCut MF/NG Authentication Bypass Exploit - HTTP (REQUEST)
Trend Micro is monitoring this ongoing campaign and will be updating this blog entry as more information becomes available.

