Previous posts
- Overlooked attack vectors
- Security risks of industrial application stores
- Trojanized libraries for Industrial IoT devices
- MES database compromises
On May 11, 2020, Trend Micro released a paper showing the results of proof-of-concept research on new security risks associated with smart factories. In this series of 5 columns, based on the results of this research, we look at the security risks to be aware of when promoting smart factories by examining overlooked attack vectors, feasible attack scenarios, and recommended defense strategies. We are wrapping up this series by examining recommended security strategies and countermeasures to secure smart factories and to keep operations running.
IT/OT crossover skills: Knowing the OT environment and cybersecurity techniques
Let's take a look back at the 3 attack scenarios that were validated in this research.
- We found vulnerabilities in application stores provided by manufacturers. Manufacturers' clouds can be a malware intrusion route. We notified the manufacturers of the vulnerabilities via ZDI, and they have already been fixed.
- More industrial IoT devices are being installed in smart factories, and open source libraries are being used more frequently in software development. Tampering with such libraries can cause device malfunctions. It is becoming more difficult to manage the entire software supply chain.
- Tampering with the MES database can cause defective products to be produced. Since the MES completely trusts the MES database, the MES cannot notice any changes in the data.
Table 1 summarizes the results of these experiments for each attack scenario from the perspective of attack vectors and damage.
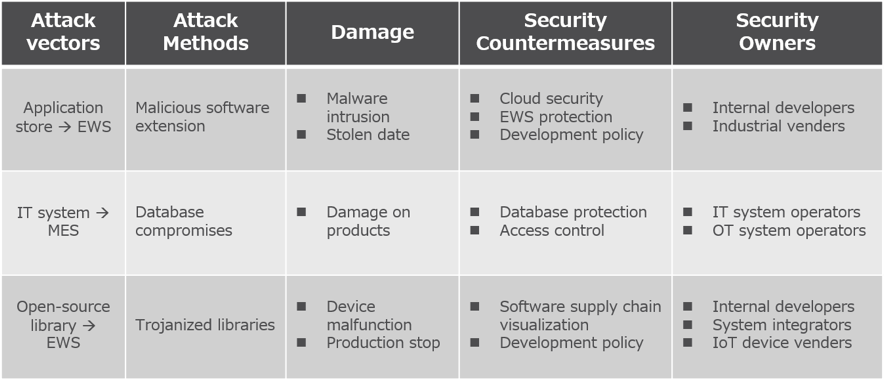
<Table 1> Research result matrix
This research has led to the discovery of new vulnerabilities and revealed overlooked cybersecurity risks. As you can see from Table 1, every attack scenario has a significant impact on production activities, and the security measures to be taken differ depending on the relevant attack scenario's characteristics. This means that as new technologies are implemented in factories, new security technologies must be implemented as well. Regarding application store vulnerabilities, it is necessary to strengthen the development process policy on the user side as well as the manufacturer's measures. Database protection is effective to prevent tampering with the MES database, which means that strengthening security on the IT system side also indirectly strengthens factory security. Also, when deploying IoT devices, it is important to be highly aware of the software supply chain. As the environment changes, smart factories will need to implement higher levels of security technology. To that end, it is important for all enterprises to secure experts with crossover skills who are well-versed in both IT and OT.
Zero trust in the factory: Software management from the development phase
In addition to technical expertise, as you can see from the "Security Owner" column in Table 1, it is necessary to re-recognize that smart factory security involves many specialists and companies. As factories get smarter, the software supply chain becomes more complex. The construction and operation of a smart factory is an effort that involves many departments and people within the company, and it is achieved in combination with the power of external, reliable partners. Furthermore, manufacturers, their developers, and open communities are connected at the end of the process. Smart factories can be said to be created through a linked, trusted relationship (Fig. 1).
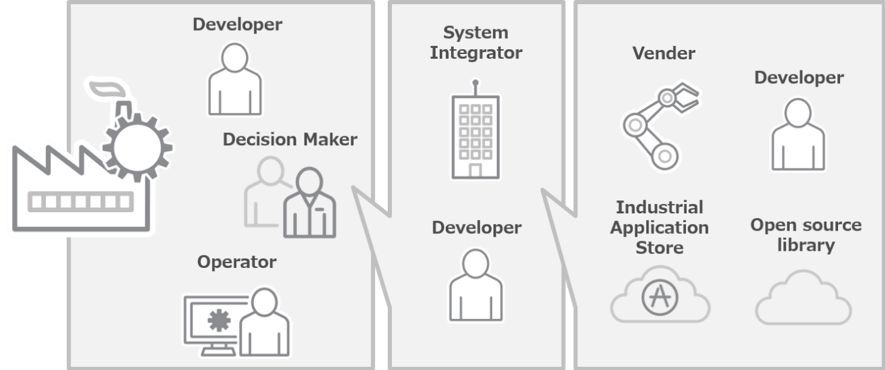
<Fig. 1> The complicated smart factory ecosystem
The attacks demonstrated in this experiment revealed the effects of the trust relationship between the beads. In order to reduce the risk of such attacks, it is necessary to take industry-wide measures related to smart factories and to improve the overall security level. Making factories smarter means achieving a software evolution in factories. Manufacturers, integrators, and user companies with smart factories are creating a complex, intricate ecosystem. As software is created and distributed everywhere within this ecosystem, it is becoming increasingly difficult to determine where malicious software is created and where it enters. In such an environment, manufacturers and integrators that provide factory equipment should design their products on the assumption that the products may be misused. The best strategy for a user company is to assume that they always face the risk of entry by malicious software. This means that the smarter a factory becomes, the more a zero-trust approach is the solution.
The roadmap: Beginning with concepts
Security measures are all about determining how to manage risks. Therefore, it is important to analyze what kind of risks you should prepare for, and this analysis should be based on the concepts of "security by design" and "zero trust." And, in order to prepare for the risks that enterprises need to pay attention to, the organization must allocate resources for risk management. Treating security as a management issue helps security teams formulate security plans with continuity. In addition, it is also effective to comply with the industry standard IEC62443, which can form a foundation for common understanding within the ecosystem. Then, finally, individual security measures can be implemented. This is a good roadmap for implementing smart factory security (Figure 2).
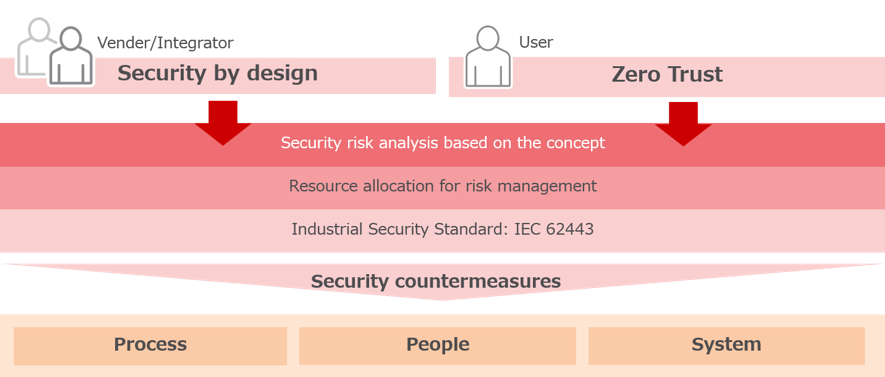
<Fig. 2> Concept-based roadmap for smart factory security
In particular, dealing with vulnerabilities (security issues peculiar to software) will become more important in the future. It goes without saying that we need to handle individual vulnerabilities by patching, and creating internal vulnerability-management processes is also necessary to effectively resolve vulnerability issues. In addition, it is important to nurture experts who can oversee not only OT systems but also IT systems (including the cloud) as well as the selection of security partners.
Cybersecurity risks in the factory are no longer a black swan
As factories get smarter, the software supply chain and entry points become more complex and diverse. Cybersecurity risks in the factory are no longer a black swan. The strategy that treats cyber security risks as being non-existent or something that rarely happens is reaching its limit. The ICS environment, which has not seen a major update for 20 years, is now about to change.
Manufacturing sites today are full of uncertainty. It is hard to predict whether your factory will be attacked tomorrow, and if so, what kind of attack it will be. In such circumstances, the system needs to be flexible and elastic rather than robust. The key is to increase your system's flexibility, rather than to anticipate events that could harm your system. To develop this idea, intense leadership that drives change is essential. The most important resource for future factory security is the understanding and support of the leadership team. We hope our research has helped you to involve your leadership team and contributes to the security of your smart factory.

