Ransomware Recap: BrainLag, Ransed, and a "Kind" Ransomware Take the Spotlight
 The open-source ransomware Hidden Tear continues to spawn more variants, and entries from other ransomware families also appeared this week. One variant describes itself as a “kind” ransomware, an MSIL-compiled ransomware displays a colorful Comic Sans ransom note, while the other, a newly-discovered variant, claims to be able to challenge Windows protection.
The open-source ransomware Hidden Tear continues to spawn more variants, and entries from other ransomware families also appeared this week. One variant describes itself as a “kind” ransomware, an MSIL-compiled ransomware displays a colorful Comic Sans ransom note, while the other, a newly-discovered variant, claims to be able to challenge Windows protection.
BrainLag and Oxar
BrainLag (detected by Trend Micro as Ransom_HiddenTearLag.A) is a variant of the Hidden Tear open-source project that uses the AES algorithm to encrypt files in the following Windows 7 directories: ‘\Public’, ‘\Desktop’, ‘\Contacts’, ‘\Documents’, ‘\Downloads’, ‘\Pictures’, ‘\Music’, ‘\OneDrive’, ‘\Saved Games’, ‘\Favorites’, ‘\Searches’, ‘\Videos’, and ‘\Links.’
BrainLag notably has a simple but stylish black and white lock screen, with a Grim Reaper graphic located in the upper right corner. It also has ‘Infected By BrainLag’ and ‘Venao – 2017’ written on it.
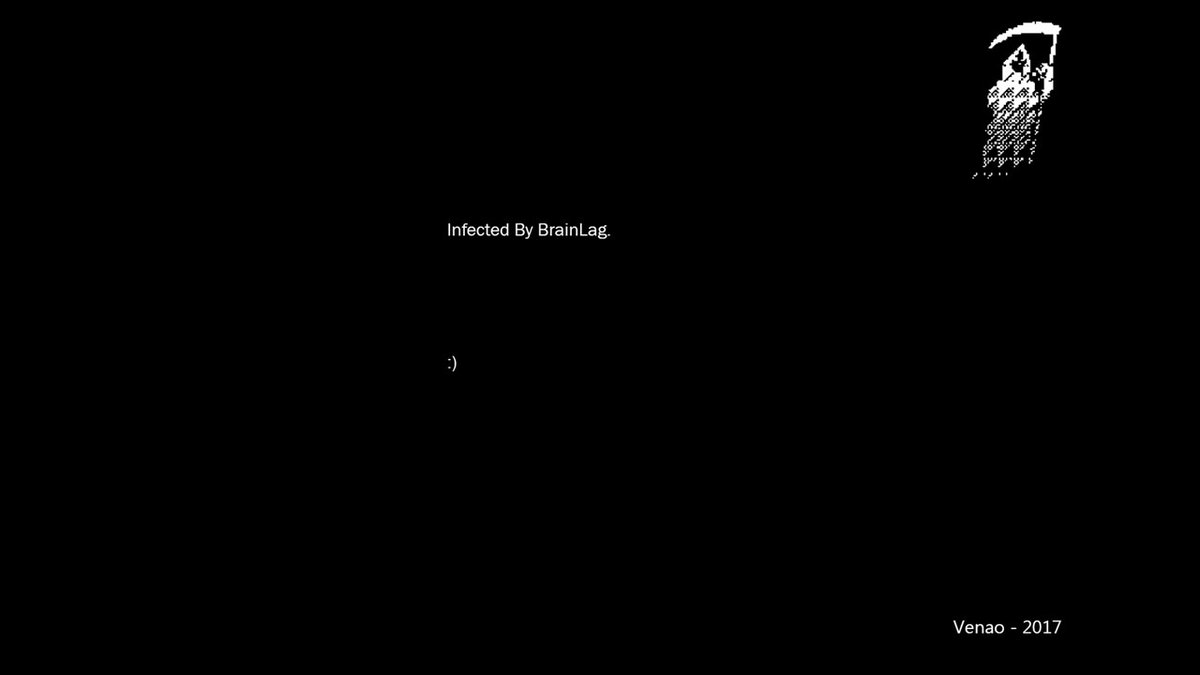 Figure 1. BrainLag lock screen
Figure 1. BrainLag lock screen
The Oxar ransomware (Ransom_HiddenTearOXAR.A) is another Hidden Tear variant that adds the .OXR file extension to files it encrypts. The variant's ransom note outlines three steps for affected users to follow to get their files back. The first step is to follow a link that will allow the victim to create a Bitcoin (BTC) wallet, followed by an instruction to buy US$100 worth of BTC. The last step involves sending the ransom payment to the specified URL.

Figure 2. Oxar ransom note
Ransed
Ransed (Ransom_RANSED.A) is an MSIL-compiled ransomware variant that arrives in the system as an Win32.exe file. The ransomware connects to a MySQL server to store victims’ data. It encrypts a variety of file types that include Microsoft Office documents, as well as audio and video file formats.
Its ransom note, which is written in colorful Comic Sans font, demands a ransom of $25 in BTC to recover the encrypted files.
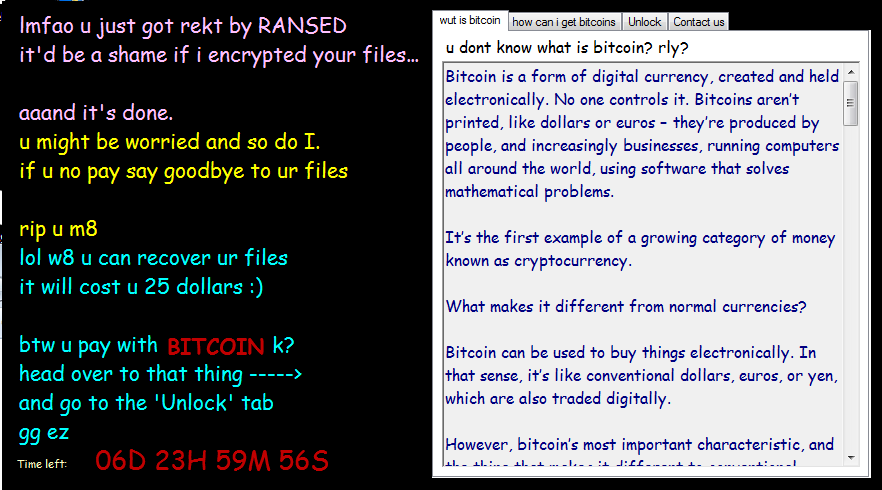 Figure 3. Ransed ransom note
Figure 3. Ransed ransom note
Blackout
Blackout (Ransom_FANTOMCRYPT.F117GJ) is a newly-discovered ransomware that claims to be a free open-source software in its ransom note. The variant was supposedly designed to test the protection of Windows OS.
Blackout encrypts files using the AES encryption algorithm and could be set to erase all the Shadow Volume Copies from the hard drive with the ‘vssadmin.exe delete shadows /all /Quiet’ command.
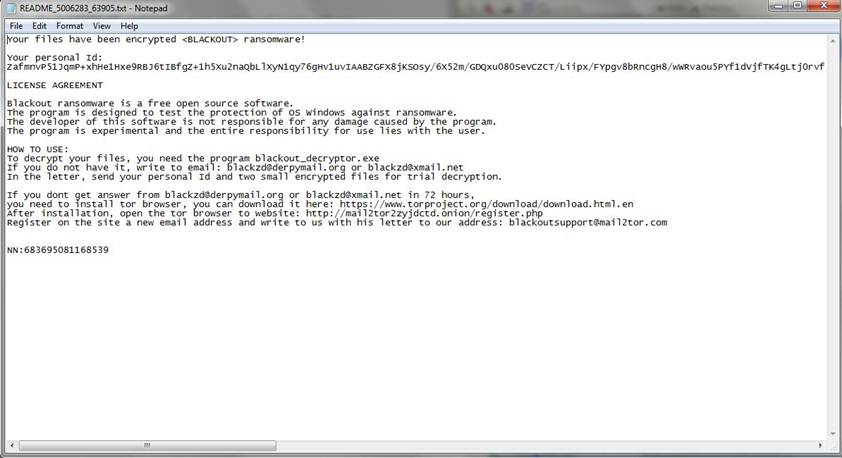 Figure 4. Blackout ransom note
Figure 4. Blackout ransom note
Purge
Describing itself as a "kind ransomware" that will not delete files, Purge (Ransom_STUPURGE.A) demands a ransom of US$250 for a decrypt key. If by kindness, it meant easily decrypting files using an already available unlock code, which is ‘TotallyNotStupid’, then the irony will be lost.
The ransomware spreads mostly through spammed e-mail messages that contain malicious attachments posing as legitimate files.
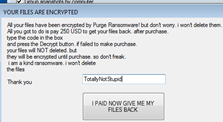
Figure 5. Purge ransom note
Fakeglobe
First detected early this year, the re-emerging Fakeglobe ransomware (RANSOM_FAKEGLOBE.F117BE) appends the .crypt extension to affected files using the AES encryption algorithm. It is distributed through spam emails posing as legitimate invoices or automated responses.
In exchange for a decryptor and how-to guidelines, Fakeglobe demands victims to send a screenshot of their 0.5 BTC payment to an email address indicated on the lock screen.
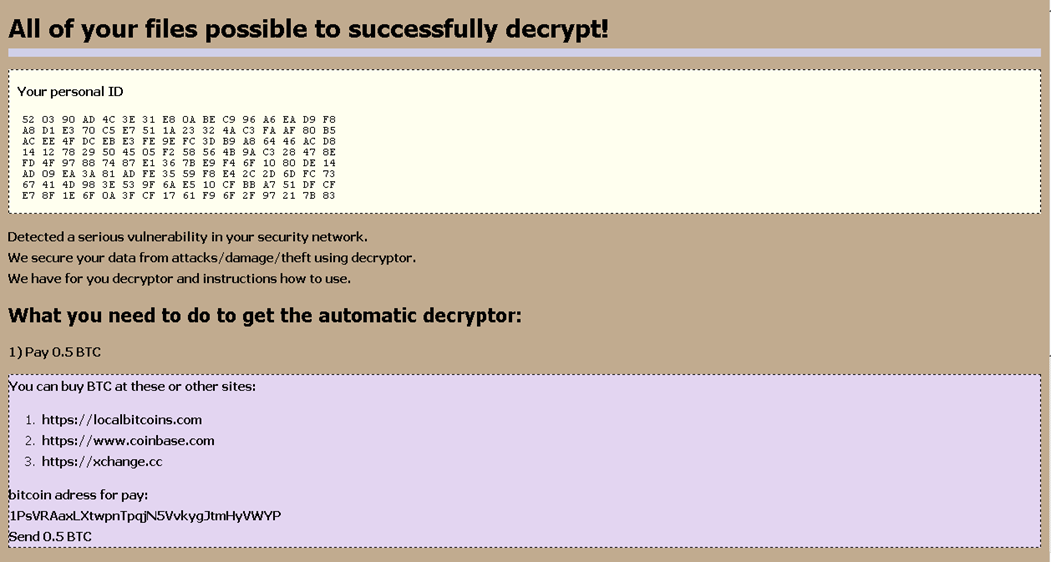 Figure 6. Fakeglobe ransom note
Figure 6. Fakeglobe ransom note
Trend Micro Ransomware Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
End users and enterprises can also benefit from multilayered mobile security solutions such as Trend Micro™ Mobile Security for Android™ (available on Google Play), and Trend Micro™ Mobile Security for Apple devices (available on the App Store). Trend Micro™ Mobile Security for Enterprise provide device, compliance and application management, data protection, and configuration provisioning, as well as protect devices from attacks that leverage vulnerabilities, preventing unauthorized access to apps, as well as detecting and blocking malware and fraudulent websites.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation