1H 2020 Cyber Security Defined by Covid-19 Pandemic
Malicious actors have always taken advantage of big news to use as lures for socially engineered threats, but these events tend to be fairly short news cycles. When Covid-19 started making headlines in early 2020, we started seeing new threats using this in the attacks.
When we published our 2020 Predictions report in December, we didn’t realize there was a global pandemic brewing that would give cybercriminals an almost daily news cycle to take advantage of in their attacks against people and organizations around the world. Malicious actors have always taken advantage of big news to use as lures for socially engineered threats, but these events tend to be fairly short news cycles.
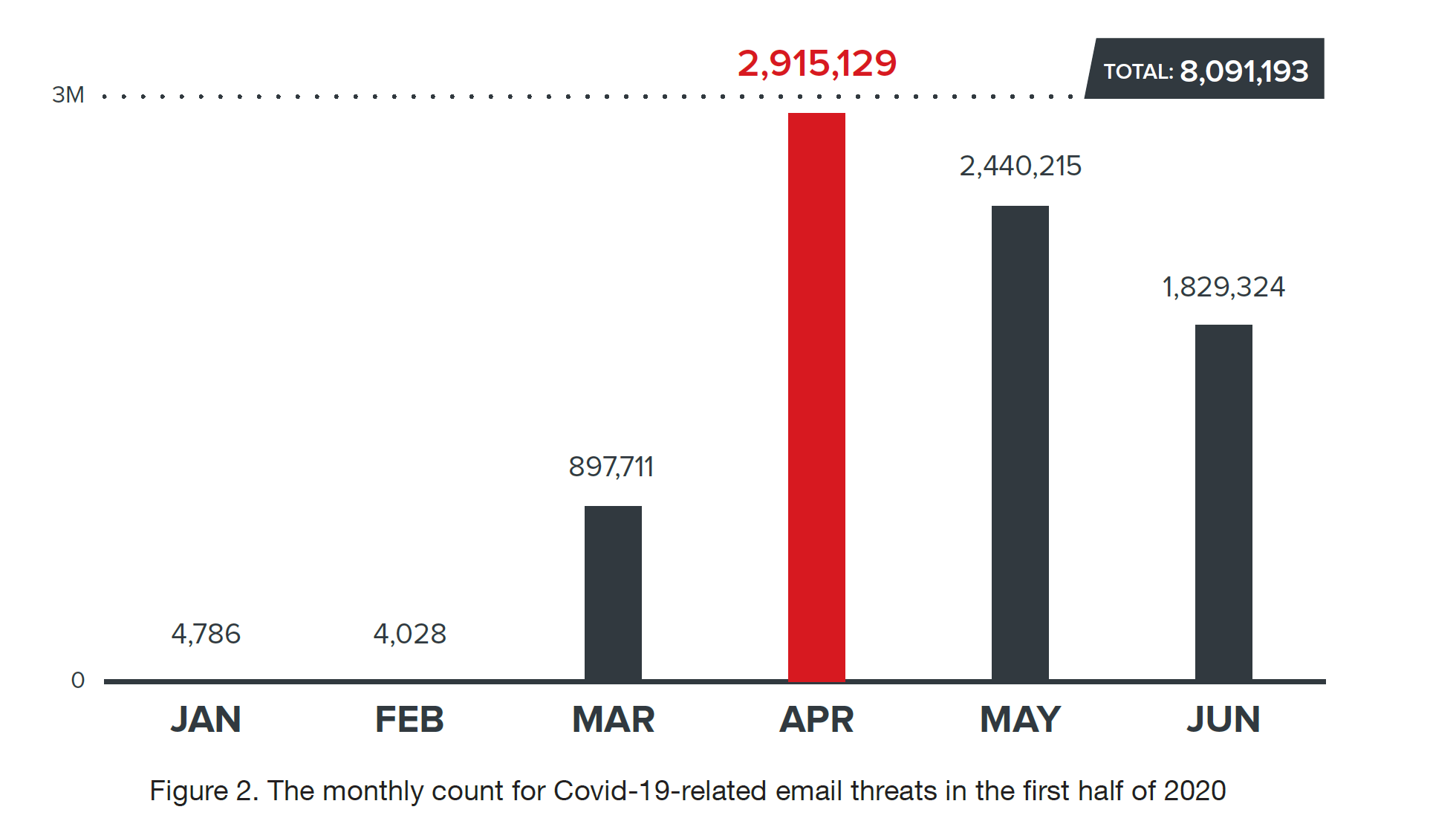
When Covid-19 started making headlines in early 2020, we started seeing new threats using this in the attacks. As you see below, April was the peak month for email-based Covid-19 related threats.
The same was true for phishing URLs related to Covid-19, but for files using Covid-19 in their naming convention, the peak month in the first half was June.
Impact on Cybercrime
The constant 24x7 news around cases, cures and vaccines makes this pandemic unique for cybercriminals. Also, the shift to remote working and the challenges posed to supply chains all gave cybercriminals new content they could use as lures to entice victims into infecting themselves.
As we’ve seen for many years now, email-based threats were the most used threat vector by malicious actors, which makes sense as the number one infection vector to penetrate an organization’s network is to use a socially engineered email against an employee.
We even saw malicious mobile apps being developed using Covid-19 as a lure, as you see below.
In this case it was supporting potential cures for the virus, which many people would have wanted.
Other Highlights in 1H 2020
While Covid-19 dominated the threat landscape in the 1H 2020, it wasn’t the only thing that defined it. Ransomware actors continued their attacks against organizations, but as we’ve been seeing over the past year, they’ve become much more selective in their victims. The spray and pray model using spam has been shifted to a more targeted approach, similar to how nation-state actors and APT groups perform their attacks. Two things showcase this trend:
1. The number of ransomware detections has dropped significantly from 1H 2019 to 1H 2020, showing that ransomware actors are not looking for broad infection numbers.
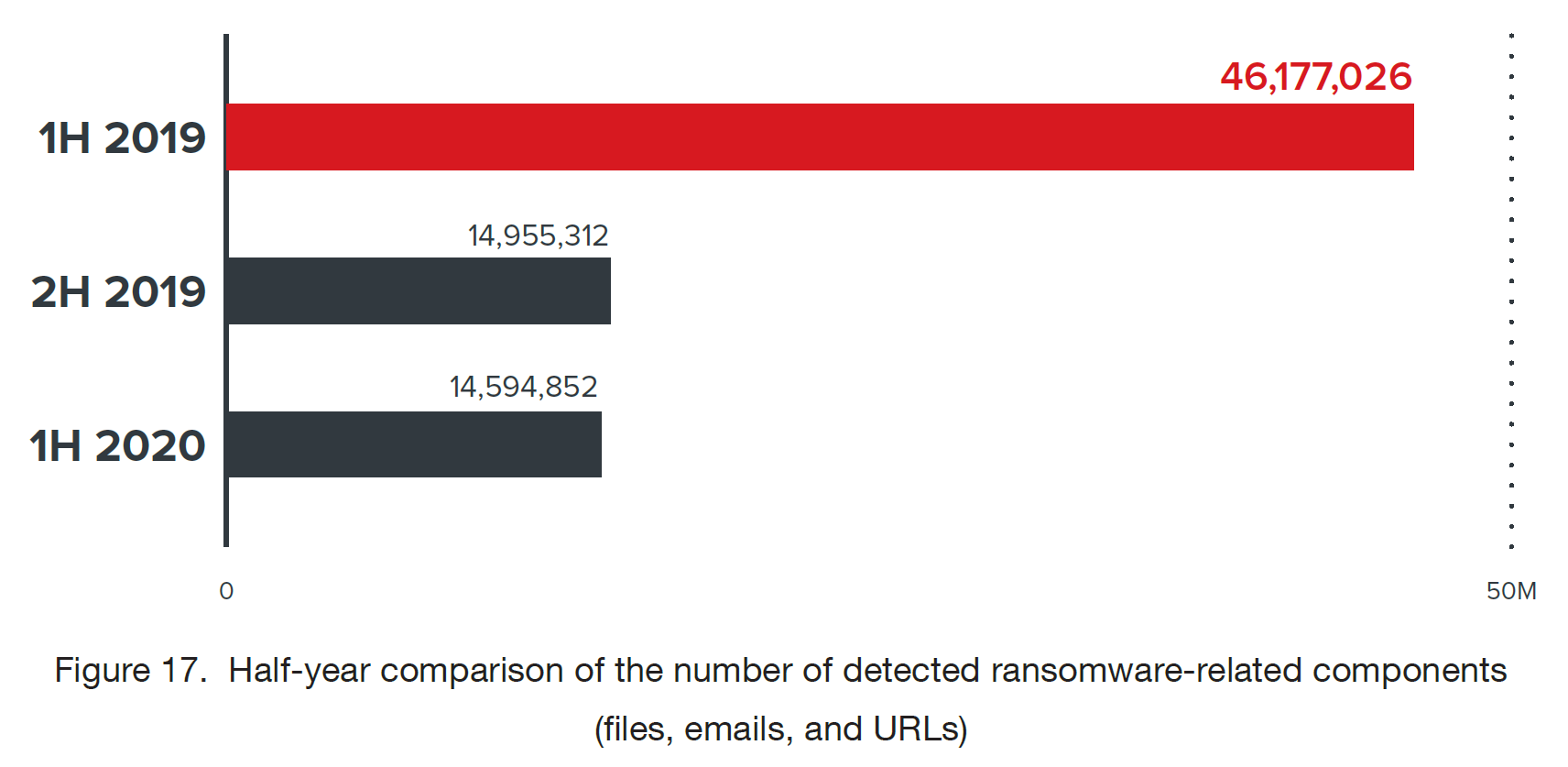
2. The ransom amounts have increased significantly over the years, showing ransomware actors are selecting their victims around how much they feel they can extort them for and whether they are more likely to pay a ransom.
Home network attacks are another interesting aspect of the threat landscape in the first half of this year. We have millions of home routers around the world that give us threat data on events coming into and out of home networks.
Threat actors are taking advantage of more remote workers by launching more attacks against these home networks. As you see below, the first half of 2020 saw a marked increase in attacks.
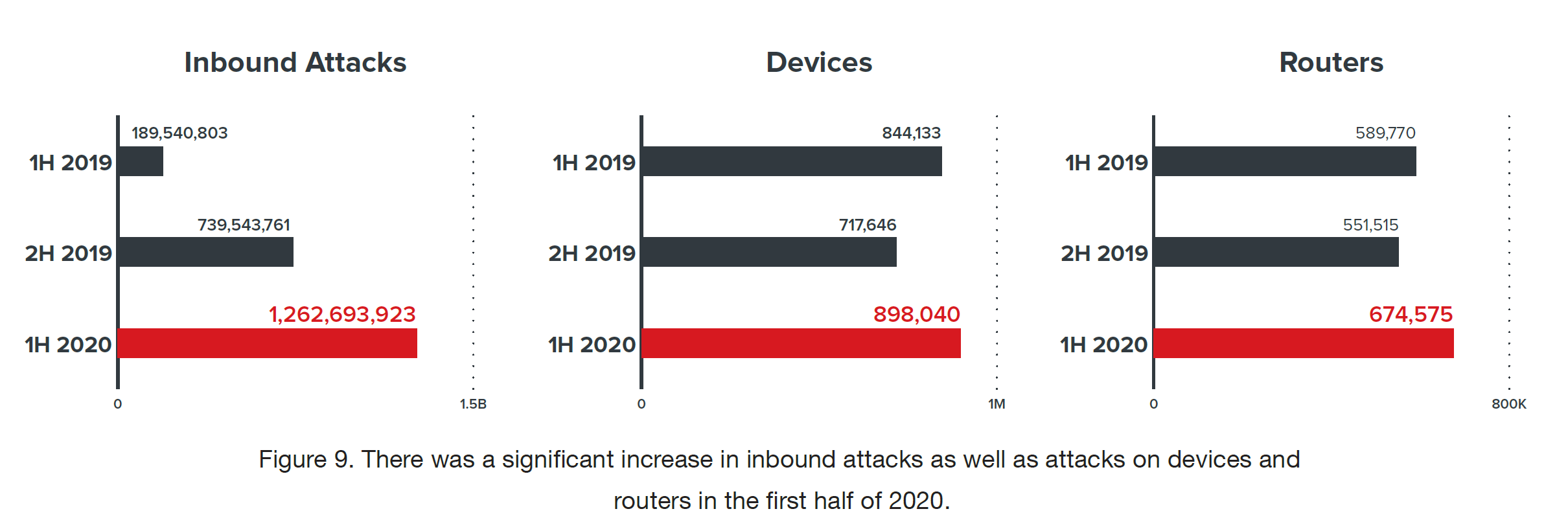
Many of these attacks are brute force login attempts as actors try to obtain login credentials for routers and devices within the home network, which can allow them to do further damage.
The above are only a small number of security events and trends we saw in just six months of 2020. Our full roundup of the security landscape so far this year is detailed out in our security roundup report – Securing the Pandemic-Disrupted Workplace. You can read about all we found to help prepare for many of the threats we will continue to see for the rest of the year.

