Privacy & Risks
Security Patch Management Strengthens Ransomware Defense
With thousands of applications to manage, enterprises need an effective way to prioritize software security patches. That calls for a contextualized, risk-based approach and good overall attack surface risk management.

Inundated with monthly, weekly, and even daily software patches, IT teams need a strategic approach to security patch management—one that lets them put risks into context, prioritize effectively, and manage their overall attack surface risk.
Enterprises today have a massive amount of software to manage and keep up to date—1,061 applications on average, according to the MuleSoft Research 2023 Connectivity Benchmark Report. At that scale, with many software vendors issuing security patches monthly, weekly, and sometimes even daily, IT teams need a strategic way to prioritize what to patch and when.
The first step is to establish a proper cybersecurity audit routine that provides a complete picture of the enterprise IT ecosystem—all devices and the software they run. With that in place, the next must-have is a contextualized, risk-based approach to assess which patches are needed most urgently and which can wait, in line with the organization’s overall attack surface risk management framework.
A constant flood of patches
Apart from the sheer volume of potential patches to apply, IT teams need to factor the time and effort each security patch requires. Many involve machine downtime, which affects the availability of IT assets and can hamper employee productivity. Knowing which patches are essential and which can wait is a practical necessity.
Traditionally, deciding which patches to apply has been based on the severity of the associated vulnerability, with each vulnerability assigned a ‘criticality value’ from zero to 10. It’s an undeniably objective technique, but also imprecise.
Some vulnerabilities may be highly critical—rating 9.8 on the scale, for example—and yet have low probability of being exploited because the attacks are too costly or complex to execute. Meanwhile, less severe attack types may already be active in the wild and pose real threats. Going by criticality rankings is like preparing a city to fight off an imaginary monster like Godzilla while ignoring legitimate and urgent risks such as floods and wildfires.
In making decisions about which security patches to apply, context is what organizations need most of all.
How to decide which security patch is a priority?
The full set of contextual factors that matter will be different for every organization, but there are common questions that can help evaluate the true risk a vulnerability represents. Some key ones include:
- Are these patches relevant to the application systems used in-house? Security teams should begin by narrowing down the list of CVEs released annually—which number in the tens of thousands—to only those relevant to your enterprise IT ecosystem. Don’t overlook outdated legacy applications, networks, systems, devices, and servers.
- Is the vulnerability already being exploited in the wild? Leverage the CISA Known Exploited Vulnerabilities catalog (some security tools will have this feature built in) and if the answer is yes, a security patch should be applied immediately.
- Is there a proof of concept (POC) for exploiting the vulnerability? A POC is the earliest implementation of a threat. Having a POC means cybercriminals don’t need to start from scratch to develop their own exploits: they can build off the POC as a base. Its availability makes a cyberattack more likely, so where a POC exists, patching sooner rather than later is wise.
- What does the vulnerability allow attackers to do? If unpatched software gives access to a siloed system with little exposure to other corporate resources and minimal privileges to execute actions, the risk of harm is relatively low. On the other hand, if it arms attackers with administrator privileges and remote control over systems and code, the security patch should be applied right away.
Continue reading the Ransomware Spotlight series:
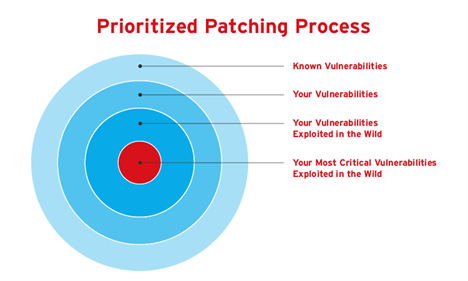
Combining these with other considerations unique to the enterprise and its business provides a more substantial, strategic, and nuanced risk score to guide patching decisions. Obviously, the answers aren’t found solely in the technical nature of the vulnerability itself. A broader understanding of the attack surface and threat environment is needed, which can be provided by combining current threat intelligence with AI and machine learning-based analytics.
Zero-day vulnerabilities are a growing risk
The importance of patching and keeping software up to date is not news: IT experts and analysts have been repeating the message for years. But changes in the threat landscape have shifted the types of vulnerabilities organizations need to focus on.
A known vulnerability that already has a security patch is classified as an ‘N-day vulnerability’, with N being the number of days the patch has been available publicly. Most organizations have become quite good at addressing N-day vulnerabilities. As a result, cybercriminals are concentrating more heavily on zero-day attacks.
Zero-day attacks target vulnerabilities for which no public security patch exists. Since these threats can still shift and evolve, they’re both more dangerous and more difficult to defend against—organizations could have a highly exploitable bug in their network without realizing it. Zero-day threats also tend to be more expensive for cybercriminals to mount.
In August 2022, Tech Monitor reported that an Apple zero-day vulnerability was on the market for 8 million euros. The package included a 12-month warranty in case the flaw gets patched, and a cloud-based code injection. Despite eye-watering costs, ransomware perpetrators and other bad actors are making enough money from their exploits that they can afford zero-day attacks fairly easily.
Forever-day attacks are another concern
The lack of a publicly available patch puts enterprises at a disadvantage with zero-day vulnerabilities. The same is true for ‘forever day’ vulnerabilities—exploitable weaknesses that will never be patched by the vendor. These arise when the software or operating systems involved are no longer supported by the developer, or when the underlying hardware has a short, intended service lifecycle and so—in theory—shouldn’t need patching, as can be the case with some internet of things (IoT) devices.
There are also situations, for example with certain medical and manufacturing devices, when the product makers prohibit software patches being applied by anyone but themselves to preserve device integrity. Some even go so far as to make it a term of sale that if a customer tries to apply a security patch themselves, they could invalidate their warranty.
The capability to consistently monitor for suspicious activity inside of networks is essential, especially with a solution that can leverage the latest global threat intelligence. But there are other ways an organization can mitigate the risk of zero-day and forever-day vulnerabilities.
Virtual patching is a good alternative
One convenient option is to resort to virtual patching. Virtual patches are developed and published by reputable providers often months ahead of public patches and can be applied without the need for a device reboot in many cases.
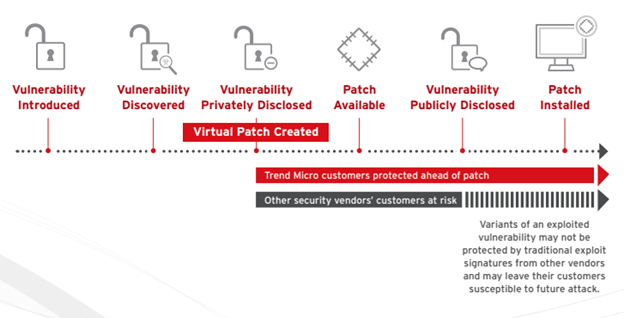
Virtual patches are usually flexible and can be turned off at a later point if a public patch comes out. While they can’t be applied in every circumstance, sometimes the network around the device that’s running vulnerable software can take a virtual patch, providing a layer of defense, especially when the device cannot support a security agent either.
Operational technologies (OT) are a prime case for virtual patching. Some OT systems have gone untouched and unsupported for upwards of 20 years, and Gartner predicts that by 2025 more threat actors will home in on these vulnerable legacy assets. Network-based virtual patches can help defend these increasingly common attack vectors.
Always consider cybersecurity risk in context
The key to sophisticated security patch management is leaving behind simplistic criticality scoring and instead evaluating risk in the context of business needs and the real-world threat environment. This supports better decision-making about which security patches need to be applied immediately.
As organizations migrate more to software-as-a-service (SaaS) consumption models for their applications, the burden of keeping pace with patching will diminish. SaaS vendors handle the whole process: when a vulnerability is found, it gets patched in the cloud and applied automatically to all users, sparing the customer organization any effort.
Still, sometimes even a good patch can temporarily take a system down and this could present a crisis for businesses that operate on a 24/7 basis. Organizations should consult their vendors about the possibility of rollbacks to previous versions of software. This could be a make-or-break consideration during a situation like the 2021 SolarWinds breach, when infected updates were unknowingly rolled out.
In the meantime, tools are becoming available to enable sophisticated risk-based decision-making about software vulnerabilities and security patches—contributing to more strategic and proactive enterprise attack surface risk management overall.

