Ransomware Recap: Dark Web Ransomware Economy on Fire
According to a security firm’s research, 2017 has seen a 2,502 percent growth in the ransomware dark web economy. The same research also found over 6,300 places where cybercriminals had advertised ransomware services, along with over 45,000 ads.
The researchers that delved into the dark web for ransomware operators or ransomware related services found that the dark web's ransomware economy grew from $249,287.05 in 2016 to $6,237,248.90 in 2017. The booming ransomware economy can be attributed to the emergence of Bitcoin for ransom payment, and the obscure nature of Tor, which helps cybercriminals mask their illegal activities. Since the transaction flow of Bitcoin is almost untraceable, identifying the account holder is nearly impossible. These two factors have allowed ransomware operators to hide underground, ultimately contributing to the growing ransomware economy.
In addition, the research also finds ransomware entrepreneurs earning as much as $100,000 yearly by selling their product. That amount is a far cry from the roughly $69,000 that legitimate software developers earn, according to figures from PayScale.com.
Here are the other notable ransomware stories:
WannaCry and CTB-Locker Sold in the Middle Eastern and North African Underground
Trend Micro discovered that a supposed lifetime license to upgradeable variants of WannaCry could be sold for $50 in the Middle Eastern and North African underground. The advertisement was seen posted in an Arabic-speaking underground forum on May 14; two days after a WannaCry outbreak started spreading across the globe.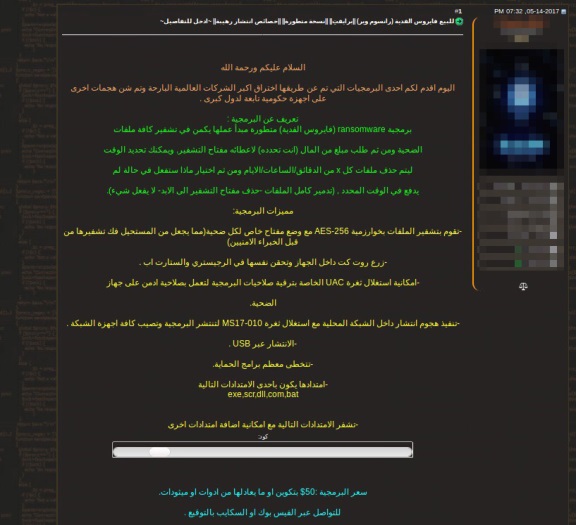
Critroni or Curve-Tor-Bitcoin (CTB) Locker or CTB-Locker ransomware was also seen being peddled in a Turkish underground forum by a Russian cybercriminal going by the handle Fizik. This malware notably utilizes elliptic curve cryptography instead of the commonly used RSA or AES. Moreover, CTB-Locker uses Tor to mask its C&C communications to hide from law enforcement agencies.
Locky’s Mean Streak
The Locky spam campaign is still spreading the ransomware, as two new samples of Locky-ridden spammed emails were discovered. The first one used the subject line 'Emailed Invoice - [Random Number]' while the second one comes with the subject 'New Doc [yyyy-mm-dd] - Page [Random Number].' Both arrive with zipped archive attachments that start the infection routine when opened.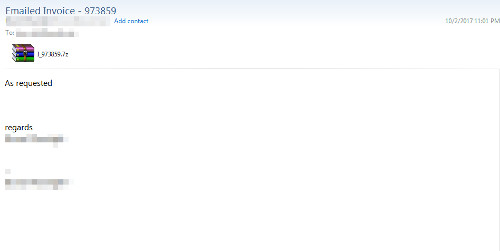
Figure 2. Screenshot of the Locky-carrying spam email
Another variant was also discovered arriving in spam emails that contain HTML attachments. The email subject is about a delivered invoice, with a message that tells the recipient to open the attached file. The HTML attachment has the filename of 'A_[Random Numbers].html', and is already detected as 'HTML_IFRAME.YYRU.’
BTCWare
A new BTCWare ransomware variant is reportedly making the rounds, targeting victims by hacking into poorly protected remote desktop services and then manually installing the ransomware. Appending encrypted files with a .[email]-id-id.payday extension name, this variant uses a new key generation feature that makes the affected files impossible to crack.
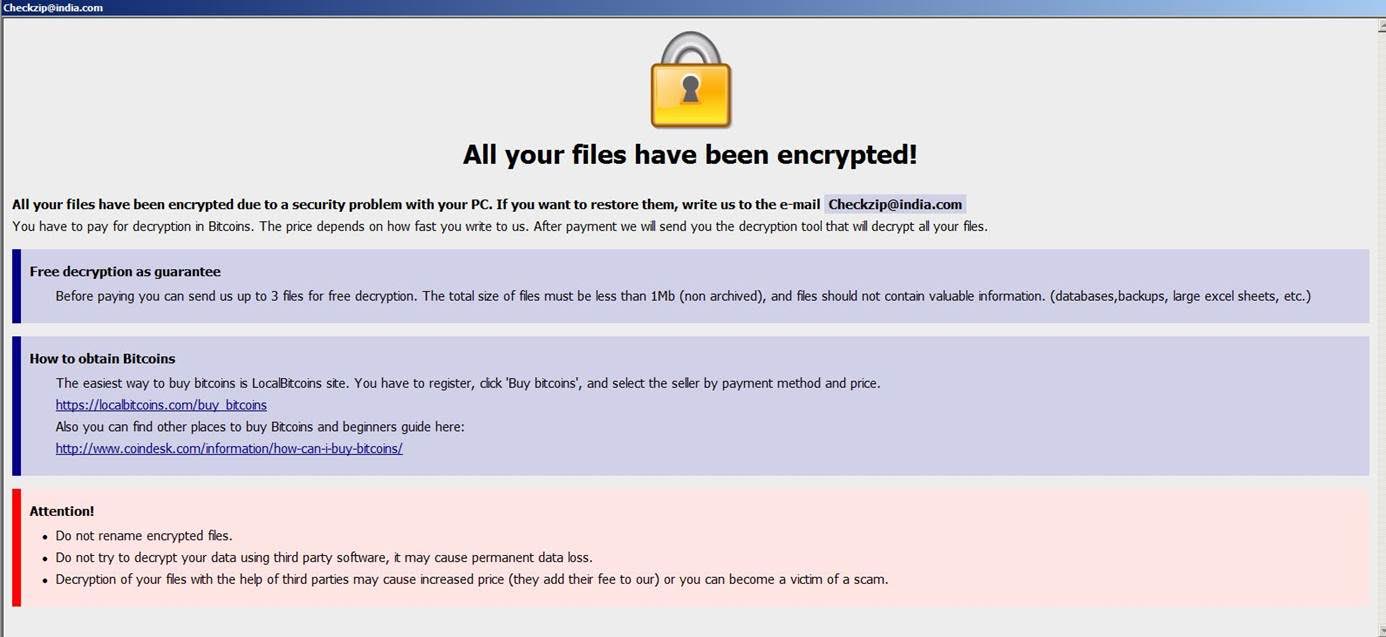
Figure 3. BTCWare ransom note
BTCWare’s ransom note advises victims to pay a certain amount in bitcoin to regain access to the encrypted files; the specific price will depend on how fast they write to the ransomware operator. The note also warns victims to avoid attempting to decrypt their files with the help of third parties as it could increase the amount of the ransom payment.
Ender and Polsky
Detected as Ransom_ENDER.A, Ender is a screenlocker that is still under development. While it doesn’t encrypt files, this variant demands a ransom of 1 bitcoin to regain access to the affected computer.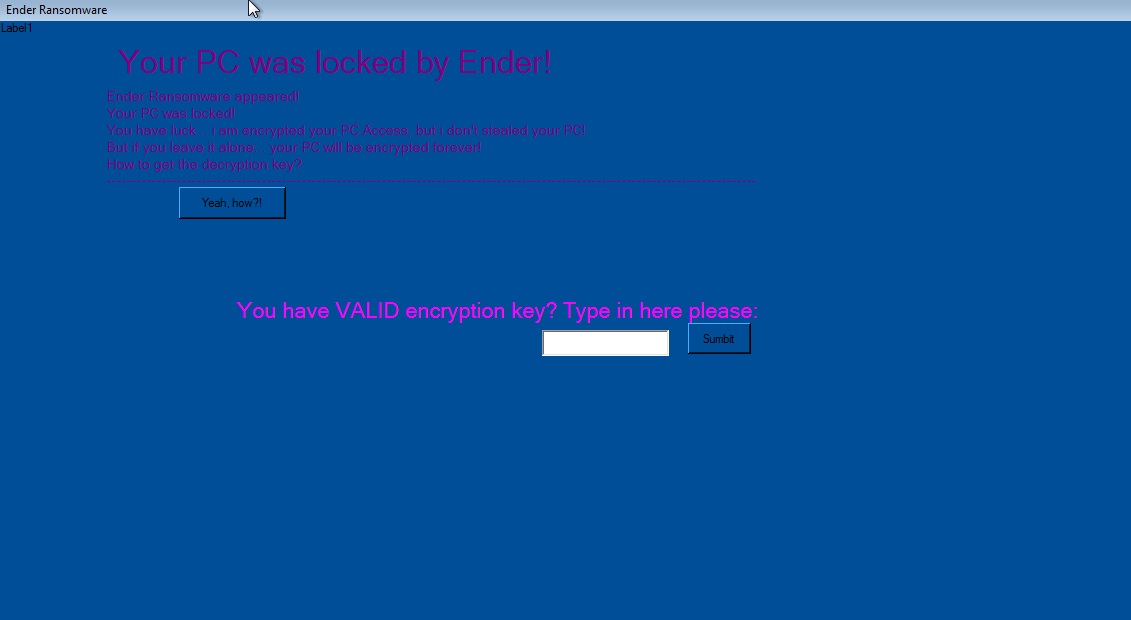
Figure 4. Ender ransom note
Meanwhile, Polsky (detected as Ransom_POLSKY.A) is a new ransomware variant written in Polish. Encrypting files via the AES-256 algorithm, Polsky demands $100 for the necessary decrypt key. The variant also warns that the ransom payment will double to $200 if the ransom is not paid within four days.
Users and enterprises can adopt ransomware best practices to lower or eliminate the risk of ransomware infection.Trend Micro Solutions
Enterprises can benefit from a multi-layered, step-by-step approach in order to best mitigate the risks brought by these threats. Email and web gateway solutions such as Trend Micro™ Deep Discovery™ Email Inspector and InterScan™ Web Security prevent ransomware from ever reaching end users. At the endpoint level, Trend Micro Smart Protection Suites deliver several capabilities like high-fidelity machine learning, behavior monitoring and application control, and vulnerability shielding that minimizes the impact of this threat. Trend Micro Deep Discovery Inspector detects and blocks ransomware on networks, while Trend Micro Deep Security™ stops ransomware from reaching enterprise servers–whether physical, virtual or in the cloud.
For small businesses, Trend Micro Worry-Free Services Advanced offers cloud-based email gateway security through Hosted Email Security. Its endpoint protection also delivers several capabilities such as behavior monitoring and real-time web reputation in order detect and block ransomware.
For home users, Trend Micro Security 10 provides strong protection against ransomware by blocking malicious websites, emails, and files associated with this threat.
Users can likewise take advantage of our free tools such as the Trend Micro Lock Screen Ransomware Tool, which is designed to detect and remove screen-locker ransomware; as well as Trend Micro Crypto-Ransomware File Decryptor Tool, which can decrypt certain variants of crypto-ransomware without paying the ransom or the use of the decryption key.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Ultime notizie
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter
- 2025 APT Report: Staying Ahead of the Modern Threat Landscape

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation