Ransomware Spotlight: Agenda
What organizations need to know about the Agenda ransomware
Despite the broad range of industries that the Agenda ransomware has been observed to attack, TrendAI™ Research has observed that a significant number of victim organizations come from the manufacturing, healthcare, and technology industries.
Agenda operates a dedicated Tor-based data leak site, which the group uses to demonstrate proof of compromise. This is done to incentivize payment, apply extortion pressure through countdown timers and staged data releases, and publish stolen victim data when ransom demands are unmet.
Ransom demands vary significantly based on victim size, sector, and perceived ability to pay. Multi-million-dollar demands are commonly observed in publicly disclosed incidents involving large enterprises and critical infrastructure.
Agenda became one of the most prolific ransomware operations in 2025, with almost 1,400 disclosed victims on its leak site. It boasted a 538% year-over-year increase in victims from 2024.
Its activity suggests that the group is just getting started. TrendAI™ Research monitoring and data suggest that the Agenda ransomware group is also building its network: The group was linked to several notable threat actors and groups in 2025.
In March 2025, the North Korean state-sponsored threat actor known as Moonstone Sleet was observed deploying the Agenda ransomware in limited and targeted operations. This marked a notable intersection of nation-state and cybercriminal activities.
Following the operational disruption of RansomHub ransomware in mid-2025, assessment of threat intelligence and research indicate that its affiliates migrated to the Agenda ransomware infrastructure based on timing correlations, tactical overlaps, and leak-site activity patterns.
On Sept. 15, 2025, DragonForce announced the formation of a strategic alliance with the Agenda and LockBit ransomware groups in a post on a Russian-language underground forum. This coalition potentially enables shared resources, tactics, and infrastructure across three major ransomware operations.
These connections to other threat actor groups emphasize that organizations should equip themselves with systems that provide early detection and mitigation to secure against dangerous groups such as the Agenda ransomware group.
Attack chain and techniques
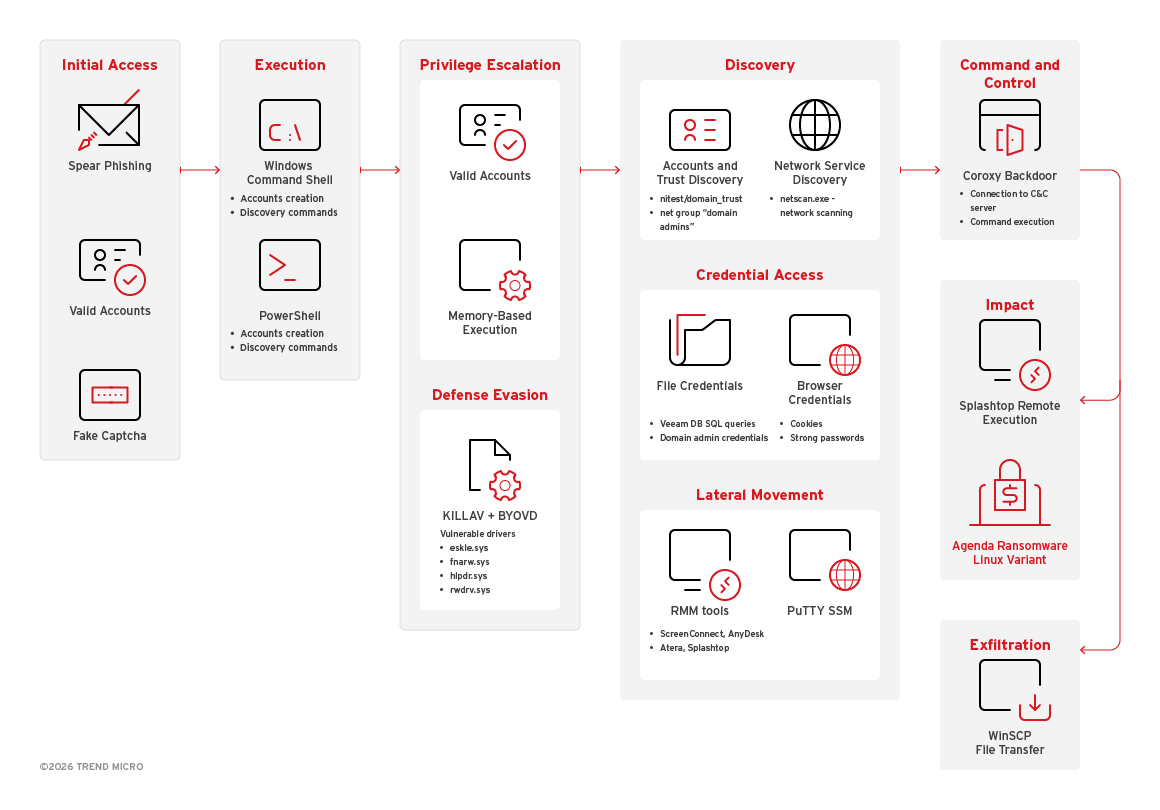
Figure 1. Agenda ransomware attack chain as of October 2025
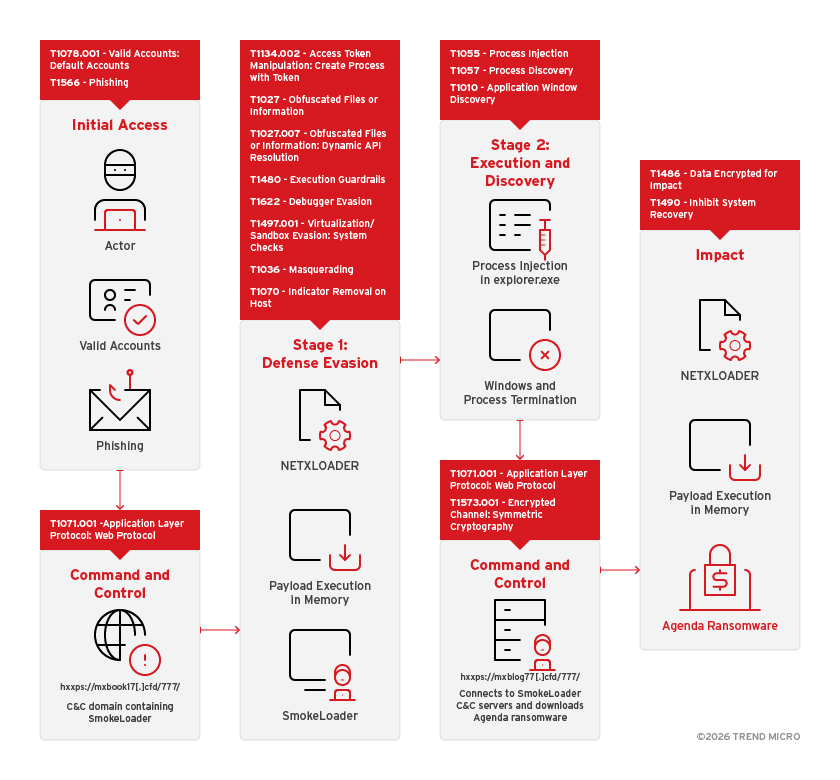
Figure 2. Agenda ransomware attack chain where the threat actors used SmokeLoader and NETXLOADER
Initial Access
- In its early operational stages, the Agenda ransomware group primarily relied on initial access brokers (IABs) to establish a foothold in victim networks.
- The group was also observed logging in to systems using stolen credentials and then leveraging process token impersonation to elevate privileges and facilitate lateral movement.
- In recent campaigns, it used fake captcha social engineering for ransomware deployment.
Execution
- The Agenda ransomware is typically executed via the command line. It accepts a wide range of parameters to customize encryption behavior, propagation, and privilege escalation. These arguments vary across its Go, Rust, and Linux variants. (These are discussed in the “Additional information” section.)
- The ransomware has been observed to use PowerShell to manage network connections and restart the LanmanWorkstation service after modifying share settings.
- In domain environments, Agenda leverages PowerShell and Active Directory (AD) commands to enumerate computers. This allows the ransomware to propagate through vCenter and ESXi environments, or terminate virtual machine (VM) clusters.
- Newer Rust-based variants are known to embed PsExec within the binary. When propagation arguments are used, the malware drops PsExec into the temporary directory to execute the ransomware on remote hosts via service execution.
- It also employs BYOVD tactics.
Persistence
- Earlier samples of the Agenda ransomware were observed to utilize various techniques for persistence such as creating a RunOnce registry entry, modifying and disabling the Volume Shadow Copy Service, modifying the ImagePath registry value for service persistence, and installing a scheduled task.
Privilege Escalation
- The Agenda ransomware uses process token impersonation by parsing configuration accounts to log in and create new malicious processes with high-level user tokens.
- It also leverages Group Policy modifications across administrative shares to enforce malicious behaviors and maintain control over the entire domain.
- It also creates backdoor administrative accounts, such as “Supportt,” to provide a persistent and elevated entry point into the system.
Lateral Movement
- The Agenda ransomware enables RDP connections by modifying registry keys and firewall settings to facilitate remote access across the network.
- It also writes programs to network shares and executes commands on remote systems using the PsExec utility to propagate.
- The ransomware deploys Cobalt Strike to move laterally across the network using Server Message Block (SMB) and Windows administrative shares to deliver additional malicious payloads.
- It also utilizes administrative shares to distribute malware and secondary tools across numerous network endpoints simultaneously.
- It enables SSH for command and control (C&C), using tools like PuTTY to establish connections, transfer files, upload payloads, and execute the ransomware on target Linux and Windows hosts.
Discovery
- The Agenda ransomware enumerates network shares for encryption using HRSword and built-in commands. It also identifies remote systems and domain controllers with nltest, and performs port scanning, lists TCP connections, and checks processes on specific ports using PC Hunter and YDArkPass.
- The ransomware also collects system details (such as operating system details, CPU count, and information on memory capacity) and enumerates installed products using Windows Management Instrumentation (WMI) and commands. It then discovers and terminates specific processes using SmokeLoader and retrieves user group details and active sessions via whoami and a query session.
- The Agenda ransomware also obtains Active Directory computer lists and then propagates using PowerShell scripts. It collects domain administrator group members via net group commands and tools like PC Hunter. The Agenda ransomware Rust variant also enumerates ESXi hosts during propagation.
Exfiltration
- The Agenda ransomware uses the cloud sync service MEGAsync to exfiltrate files to a remote cloud server via HTTP POST.
- It also employs WinSCP for file exfiltration from victim environments.
- The ransomware also uses Coroxy/SystemBC to retrieve the victim’s username and then encrypts it with RC4 before sending it to the ransomware’s C&C server as part of initial registration.
- The ransomware also uses the s5cmd tool to authenticate to cloud object storage and systematically exfiltrate targeted documents, emails, images, and database files from compromised systems.
Defense Evasion
- The Agenda ransomware terminates antivirus-related services and processes to evade detection and protection.
- It employs the BYOVD technique to terminate security processes, enhancing its ability to evade detection.
- The ransomware disguises PuTTY as a legitimate application or renames it to mimic system processes and then uses Thread Local Storage (TLS) callbacks to stealthily execute malicious payloads.
- The ransomware is then loaded via process injection using NETXLOADER, which is packed with .NET Reactor v6 for obfuscation and software packing.
Credential Access
- The Agenda ransomware extracts stored Veeam backup credentials by querying the credentials database table.
Command and Control
- The Agenda ransomware uses SmokeLoader and Coroxy/SystemBC to communicate with the C&C infrastructure over HTTP/HTTPS using direct TCP connections and proxy-based channels.
- It also uses Coroxy/SystemBC to establish encrypted external and multi-hop proxy tunnels, including Tor. It is also capable of receiving and executing attacker-delivered payloads.
- It also abuses Mongoose Web Server, which uses HTTP via a legitimate browser process to blend C&C traffic with normal web activity.
- It also abuses MeshAgent, the endpoint client of MeshCentral, to transfer and execute ransomware by deploying Linux ransomware binaries onto a Windows host. MeshAgent establishes C&C communication with the MeshCentral server via WebSocket over HTTPS (wss://).
- The ransomware deploys the open-source remote control and remote scripting solution Remotely to maintain persistent access and control over compromised systems.
Impact
- The Agenda ransomware encrypts files using AES-256 with RSA-2048 key protection, which supports intermittent and multi-threaded encryption, and selectively targets files and systems based on configuration.
- It generates the key and IV that was used for encryption using the function generateKye, using the API rand_read(). It then uses AES256 for its file encryption using the randomly generated key. It then encrypts the key using RSA-2048 using the embedded public key from the config file, from the function encryptSymmetricKey.
- It terminates and disables system services to disrupt normal operations.
- It also deletes shadow copies and overwrites data to prevent system recovery.
- It then displays its ransom note by changing the desktop wallpaper and modifying system login messages.
- It also removes user access by changing account passwords on affected systems, including vCenter and ESXi hosts.
- It deletes virtual machine disks and snapshots on ESXi environments that cause permanent data loss.
- Early samples of the Agenda ransomware have been observed to be ready for intermittent encryption, adding the -n, -p, fast, skip, and step flags on its configurations.
Additional information on the Agenda ransomware and its different variants
Agenda ransomware Go variant
- The Agenda ransomware’s Go variant accepts the following parameters:
- -alter {int} – This is a port for the service flag child process.
- -encryption {value} – This allows threat actors to redefine embed encryptor config to custom.
- -ips {IP address} – This allows threat actors to provide IP addresses.
- -min-size {value} – This determines the minimal file size to encrypt (1 KB, 1 MB, 1 GB, 666 KB, etc.)
- -no-proc – This means processes will not be killed when the protocol driver is not attached.
- -no-services – This means services will not be killed.
- -password {string} – This requires a password for execution, which also functions as the login credential for the ransomware group’s support chat site.
- -path {directory} – This determines from which path to parse directories.
- -safe – This prompts the machine to boot into safe mode.
- -stat – This prints stab config end exit.
- It appends the following extension pattern to the file name of each encrypted file (it should be noted that exact extensions may vary because they have been observed to be configured per victim or affiliate build):
- {Original filename}.{Original Extension}.{Random 10 Characters}
- It avoids encrypting files with file names that have the strings specified here.
- It avoids encrypting files with extensions specified here.
- It encrypts files found in the folders specified here.
- It displays the following ransom note:
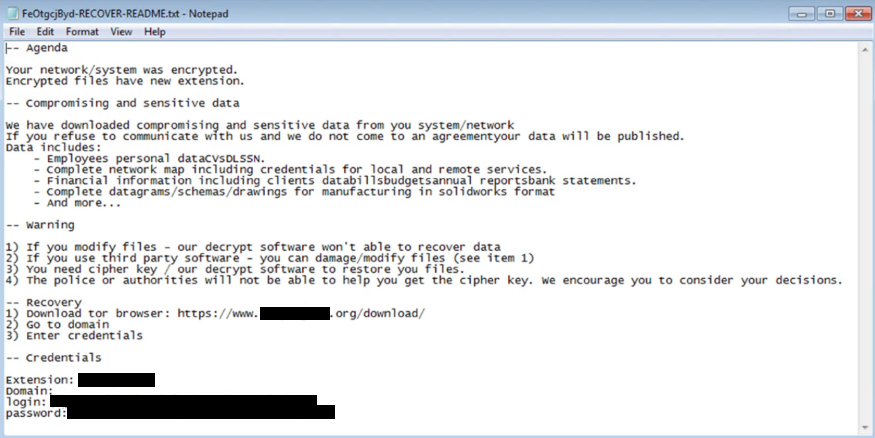
Figure 3. Agenda ransomware Go variant ransom note
Agenda ransomware Rust variant
- In December 2022 and February 2023, we encountered a new version of the Agenda ransomware containing more command-line arguments. As of February 2024, the Agenda ransomware’s Rust variant has been observed to contain the command-line arguments specified here.
- The Agenda ransomware’s Rust variant appends the following extension patterns to the file name of each encrypted file (it should be noted that exact extensions may vary because they have been observed to be configured per victim or affiliate build):
- {Original filename}.{Original Extension}.{Random 10 Characters}
- {Original filename}.{Original Extension}.{Random 10 Characters}.{Random}
- .{Random 2 Characters}-{Random 7 Characters}
- It avoids encrypting files with file names that have the strings specified here.
- It avoids encrypting files with extensions specified here.
- It encrypts files found in the folders specified here.
- It displays the following ransom note:
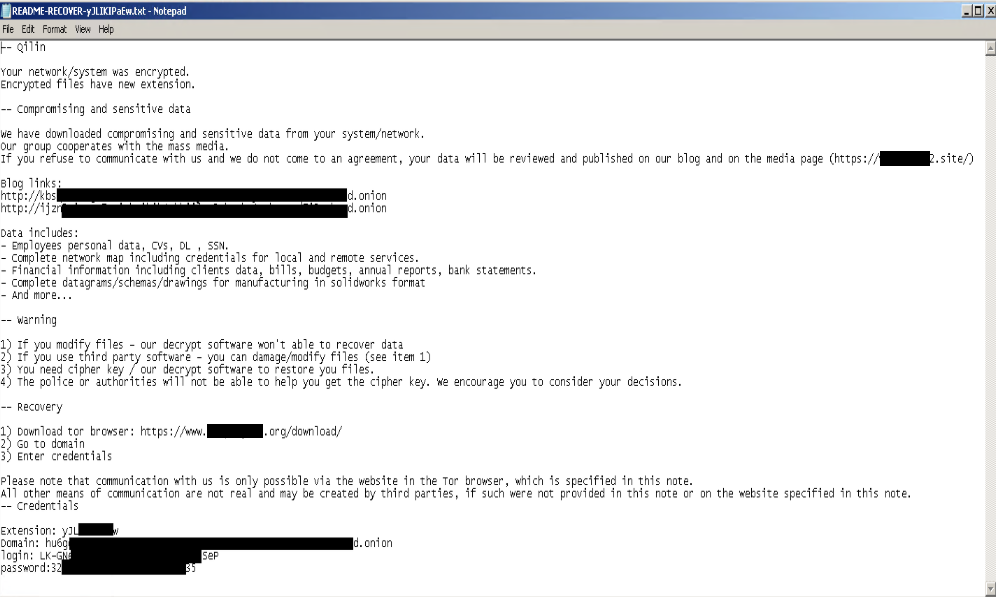
Figure 4. Agenda ransomware Rust variant ransom note
- It also changes the infected machine’s wallpaper to the following:
Figure 5. Wallpaper used by the Agenda ransomware Rust variant
Agenda ransomware Linux variant
- The Agenda ransomware’s Linux variant accepts the following parameters:
- -d | --debug – This enables debug mode (logging level set to DEBUG, disables backgrounding).
- --dry-run – This performs a scan for files to be processed but does not modify them.
- -h | --help – This displays a list of commands.
- -l | --log-level {number} – This sets logging level in values from 0 for FATAL up to 5 for DEBUG.
- --no-df – This ignores configured allowlists/blocklists of directories.
- --no-ef – This ignores configured allowlists/blocklists of extensions.
- --no-ff – This ignores configured allowlists/blocklists of files.
- --no-proc-kill – This disables process kill.
- -R | --no-rename – This disables the renaming of completed files.
- --no-snap-rm – This disables snapshot deletion.
- --no-vm-kill – This disables VM kill.
- -p | --path {string} – This specifies the top-level directory for files search.
- --password {string} – This enters the password for startup.
- -r | --rename – This enables the renaming of completed files (default).
- -t | --timer {number} – This enables timed delay before encryption (seconds).
- -w | --whitelist – This uses allowlists for inclusion instead of blocklists for exclusion (default behavior).
- -y | --yes– This assumes answer 'yes' on all questions (script mode).
- It appends the following extension patterns to the file name of each encrypted file (it should be noted that exact extensions may vary because they have been observed to be configured per victim or affiliate build):
- {Random 2 Characters}_{Random 7 Characters}
- It avoids encrypting files with file names that have the strings specified here.
- It avoids encrypting files with file paths that have the strings specified here.
- It avoids encrypting files with extensions specified here.
- It encrypts files with extensions specified here.
- It displays the following ransom note:
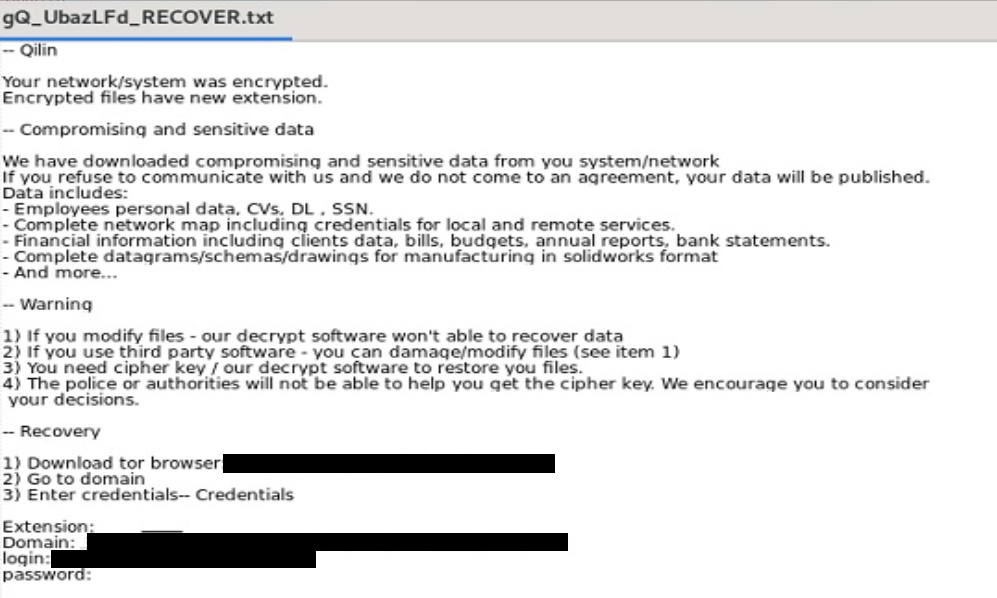
Figure 6. Agenda ransomware Linux variant ransom note
MITRE tactics and techniques
| Initial Access | Execution | Persistence | Privilege Escalation | Defense Evasion | Credential Access | Discovery | Lateral Movement | Exfiltration | Command and Control | Impact |
|---|---|---|---|---|---|---|---|---|---|---|
T1189 - Drive-by Compromise T1091 - Replication Through Removable Media T1078 - Valid Accounts T1566.002 - Phishing: Spearphishing Link | T1059 - Command and Scripting Interpreter T1059.001 - Command and Scripting Interpreter: PowerShell T1569.002 - System Services: Service Execution T1569.002 - System Services: Service Execution T1129 - Shared Modules | T1547.001 - Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder T1543.003 - Create or Modify System Process: Create or Modify System Process: Windows Service T1547.0001 - Boot or Logon Autostart Execution: Registry Run Keys/ Startup Folder T1053 - Scheduled Task/Job | T1134.001 - Access Token Manipulation: Token Impersonation/Theft T1055 - Process Injection T1484.001 - Domain or Tenant Policy Modification: Group Policy Modification T1078 - Valid Accounts: Local Accounts T1098 - Account Manipulation | T1562 - Impair Defenses T1562.001 - Impair Defenses: Disable or Modify Tools T1480 - Execution Guardrails T1070.001 - Indicator Removal: Clear Windows Event Logs T1222.001 - File and Directory Permissions Modification: Windows File and Directory Permissions Modification T1562.009 - Impair Defenses: Safe Mode Boot T1070.004 - Indicator Removal: File Deletion T1497.001 - Virtualization/Sandbox Evasion: System Checks T1134.005 - Access Token Manipulation: SID- History Injection T1497.003 - Virtualization/Sandbox Evasion: Time Based Evasion T1564 - Hide Artifacts T1222.002 - File and Directory Permissions Modification: Linux and Mac File and Directory Permissions Modification T1140 - Deobfuscate/Decode Files or Information T1027.002 - Obfuscated Files or Information: Software Packing T1055.002 - Process Injection: Portable Executable Injection T1553.002 - Subvert Trust Controls: Code Signing T1055 - Process Injection: Thread Local Storage | T1081 - Credentials in Files | T1057 - Process Discovery T1135 - Network Share Discovery T1082 - System Information Discovery T1083 - File and Directory Discovery T1033 - System Owner/User Discovery T1087.001 - Account Discovery: Local Account T1087 - Account Discovery Domain Account T1087.002 - Account Discovery: Domain Account T1018 - Remote System Discovery T1049 - System Network Connections Discovery T1046 - Network Service Discovery T1010 - Application Window Discovery | T1021 - Remote Services Remote Desktop Protocol T1021 - Remote Services SMB/Windows Admin Shares T1021.004 - Remote Services: SSH | T1567.002 - Exfiltration to Cloud Storage T1567.002 - Exfiltration Over Web Service: Exfiltration to Cloud Storage T1041 - Exfiltration Over C2 Channel | T1071 - Application Layer Protocol: Web Protocols T1090 - Proxy: External Proxy T1105 - Ingress Tool Transfer T1188 - Multi-hop Proxy T1219 - Remote Access Tools | T1490 - Inhibit System Recovery T1486 - Data Encrypted for Impact T1489 - Service Stop T1491.001 - Defacement: Internal Defacement T1531 - Account Access Removal T1561.001 - Disk Wipe: Disk Content Wipe T1496 - Resource Hijacking |
Tactics and tools used
| Tactic | Tools |
|---|---|
| Execution | PsExec |
| BYOVD | |
| Lateral Movement | PsExec |
| Cobalt Strike | |
| PuTTY | |
| Discovery | HRSword |
| PC Hunter | |
| YDArkPass | |
| SmokeLoader | |
| Exfiltration | MEGAsync |
| WinSCP | |
| Coroxy/SystemBC | |
| s5cmd | |
| Defense Evasion | BYOVD |
| PuTTY | |
| NETXLOADER | |
| Command and Control | Coroxy/SystemBC |
| Mongoose Web Server | |
| MeshAgent | |
| Remotely |
Top affected countries and industries based on TrendAI™ threat intelligence
According to TrendAI™ threat intelligence, there were 715 attack attempts by Agenda ransomware from January to December 2025 across systems covered by TrendAI™.
Organizations in the US received by far the highest number of attack attempts, with 209 detections. Organizations in Italy, Taiwan, Argentina, and Malaysia also recorded attack attempts from the group.
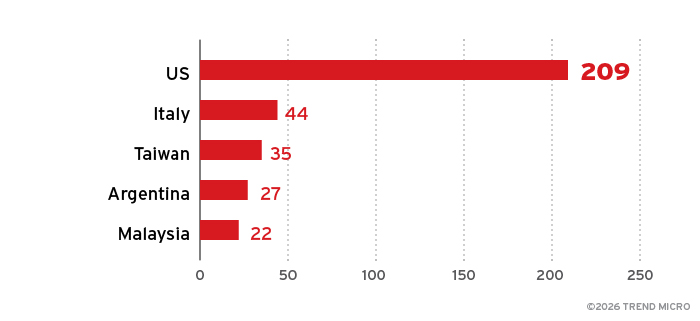
Figure 7. Top five countries or regions by number of Agenda ransomware attack attempts from January to December 2025 across systems covered by TrendAI™, based on TrendAI™ threat intelligence
Organizations in the manufacturing industry received the most attack attempts from the Agenda ransomware, followed by those in financial services, healthcare, and government.
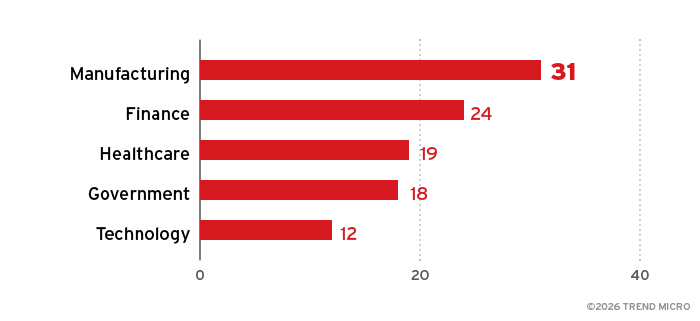
Figure 8. Top five industries by number of Agenda ransomware attack attempts from January to December 2025 across systems covered by TrendAI™, based on TrendAI™ threat intelligence
Top affected countries and industries according to the Agenda ransomware’s leak site
This section looks at data based on attacks recorded on the Agenda ransomware leak site, monitored with TrendAI™ open-source intelligence (OSINT) research from Oct. 17, 2022 to Jan. 31, 2026.
Based on the gathered intelligence, the Agenda ransomware group has claimed 1,377 victim organizations, with 751 (55%) located in North America, 321 (23%) in Europe, and 158 (11%) in the Asia-Pacific region.
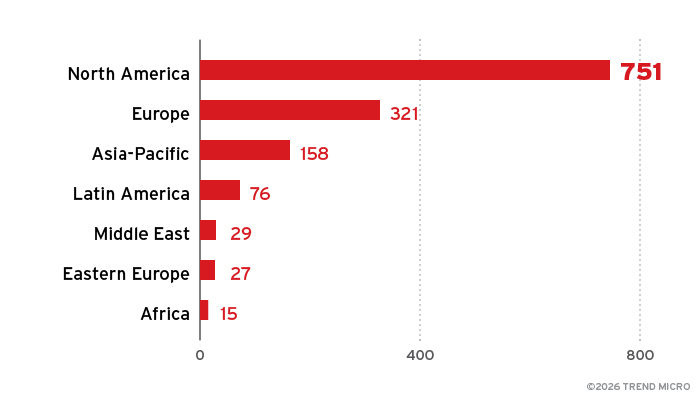
Figure 9. Breakdown by region of the Agenda ransomware’s victim organizations based on its leak site, as monitored by TrendAI™ OSINT from October 2022 to January 2026
The Agenda ransomware group has claimed 670 victim organizations in the US, by far the highest of any country, with only tens of victim organizations each in Canada, France, the UK, and Germany. The remaining victims not listed in the country breakdown in Figure 10 are labeled as “others” in the ransomware group’s leak site, that is, their specific countries have not been identified.
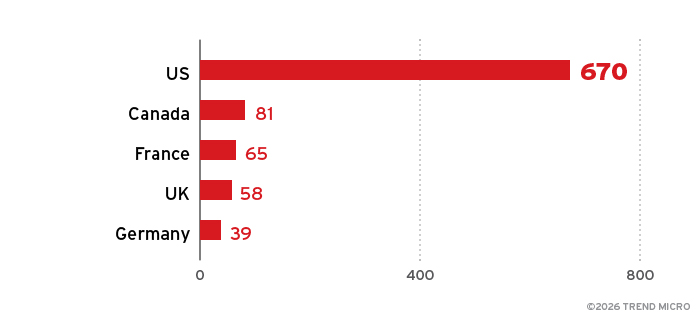
Figure 10. Top five countries by number of Agenda ransomware victim organizations based on the ransomware group’s leak site, as monitored by TrendAI™ OSINT from October 2022 to January 2026
The Agenda ransomware group has claimed the highest number of victims in the manufacturing industry, with 187 organizations affected. The remaining victims not included in the industry breakdown in Figure 11 are labeled as “others” in the ransomware group’s leak site, that is, their specific industries have not been identified.
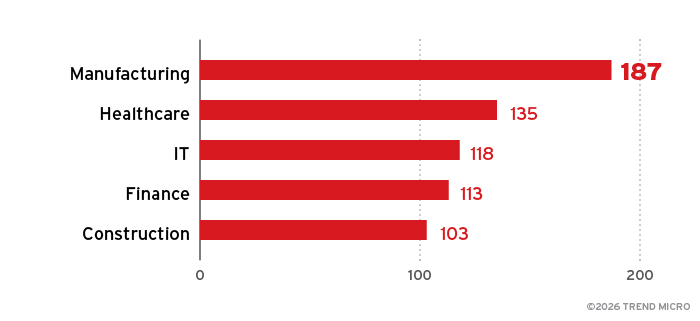
Figure 11. Top five industries by number of Agenda ransomware victim organizations based on the ransomware group’s leak site, as monitored by TrendAI™ OSINT from October 2022 to January 2026
A majority of the Agenda ransomware group’s claimed victims are small businesses. The group has likely taken advantage of the lack of complex security systems and security operations centers (SOCs) that is usually exhibited in small enterprises.
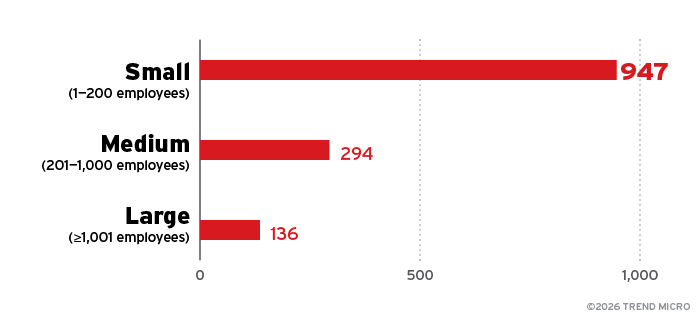
Figure 12. Breakdown by enterprise size of the Agenda ransomware’s victim organizations based on the ransomware group’s leak site, as monitored by TrendAI™ OSINT from October 2022 to January 2026
TrendAI Vision One™ Threat Intelligence
To stay ahead of evolving threats, TrendAI™ customers can access a range of intelligence reports and threat insights in TrendAI Vision One™. Intelligence reports and threat insights help customers stay ahead of cyberthreats before they happen and be better prepared for emerging threats. These provide comprehensive information on threat actors, their malicious activities, and the techniques they use. By leveraging this information, customers can take proactive steps to protect their systems, mitigate risks, and respond effectively to threats.
TrendAI Vision One™ Intelligence Reports App (IoC sweeping)
The following can be searched in the TrendAI Vision One™ Intelligence Reports dashboard for indicators-of-compromise (IoC) sweeping:
TrendAI Vision One™ Threat Intelligence Hub App
Threat actors:
Emerging threats
- Agenda Ransomware Continues Cross-Platform Attacks with New Open-Source Tools for Remote Control and Exfiltration
- Agenda Ransomware Deploys Linux Variant on Windows Systems through Remote Management Tools and BYOVD Techniques
- Agenda deploying Linux Ransomware on Windows using MeshAgent
- Agenda Ransomware's Evolution: Unveiling the SmokeLoader Connection and NetXLoader Obfuscation
- Agenda Ransomware Expands its Arsenal, Adopts TrueSightKiller to Evade Detection
- Agenda Ransomware's Tactics: Using Signed Executable to Deploy EDRSandblast BYOVD
- Evolving Agenda Ransomware: First .NET Binary with Advanced Evasion and Encryption Techniques
- Agenda Ransomware Propagates to vCenters and ESXi via Custom PowerShell Script
- Agenda Ransomware attack deployed using CobaltStrike and uses EDRSandblast BYOVD for ANTI AV
- New Agenda Ransomware Targets ESXi Environment
TrendAI Vision One™ Hunting Queries
TrendAI Vision One™ customers can use the Search App to match or hunt the malicious indicators mentioned in this feature with data in their environments.
More hunting queries are available for TrendAI Vision One™ customers with the Threat Intelligence Hub Entitlement enabled.
Agenda ransomware malware detections
(malName: *QILIN* OR malName: *AGENDA*) AND eventName: MALWARE_DETECTION AND LogType: detection
Conclusion and recommendations
The Agenda ransomware group has shown a capability for rapid evolution and has grown into one of the most prolific and dangerous ransomware operations just over three years after its first detection.
The group combines technical sophistication with aggressive extortion tactics. Its ability to deploy customizable Go- and Rust-based variants across Windows, Linux, and ESXi environments, coupled with advanced lateral movement techniques and defense evasion strategies, demonstrates a high level of adaptability.
Its operational expansion, alliances with other major ransomware operators, and even observed collaboration with nation-state threat groups underscore its growing influence and reach.
With almost 1,400 disclosed victims as of January 2026 and multi-million-dollar ransom demands targeting critical industries like manufacturing, healthcare, and technology, the Agenda ransomware poses a severe risk to enterprise resilience. Organizations must prioritize early detection, proactive defense, and incident response readiness to mitigate the escalating threat posed by this increasingly networked and resourceful adversary.
TrendAI™ recommends that enterprises be highly vigilant against the Agenda ransomware and maximize resources available in the TrendAI Vision One™ platform.
The following are some best practices that organizations can consider to help protect themselves from ransomware attacks.
Audit and
inventory
- Take an inventory of assets and data.
- Identify authorized and unauthorized devices and software.
- Audit event and incident logs.
Configure and
monitor
- Manage hardware and software configurations.
- Grant admin privileges and access only when necessary to an employee’s role.
- Monitor network ports, protocols, and services.
- Activate security configurations on network infrastructure devices such as firewalls and routers.
- Establish a software allowlist that executes only legitimate applications.
Patch and
update
- Conduct regular vulnerability assessments.
- Perform patching or virtual patching for operating systems and applications.
- Update software and applications to their latest versions.
Protect and
recover
- Implement data protection, backup, and recovery measures.
- Enable multifactor authentication (MFA).
Secure and
defend
- Employ sandbox analysis to block malicious emails.
- Deploy the latest versions of security solutions to all layers of the system, including email, endpoint, web, and network.
- Discover early signs of an attack, such as the presence of suspicious tools in the system.
- Use advanced detection technologies such as those powered by AI and machine learning.
Train and
test
- Regularly train and assess employees on security skills.
- Conduct red-team exercises and penetration tests.
A multilayered approach can help organizations secure possible entry points into their system (endpoint, email, web, and network). Security solutions can detect malicious components and suspicious behavior, helping protect enterprises from threats.
TrendAI Vision One™ provides multilayered protection and behavior detection, which help block questionable behavior and tools early on before ransomware can do irreversible damage to the system.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- The Hidden Risk in Your AI Rollout: Your Endpoints
- When AI Becomes a Zero-Day Machine: What Public Sector Organizations Need to Know
- A Data-Driven View of Cyber Risk Structure: How Attack Pressure and Exposure Shape Damage
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised


 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation