Best Practices: How to Secure Your Social Media Accounts
The most popular social media platforms have billions of users, and the number keeps getting bigger every year. The juggernauts of the field—Facebook, YouTube and Instagram to name a few—have gone beyond their initial purpose of sharing, entertainment, and communication. Now, enterprises see them as valid advertising tools and users have built careers out of sharing content. Not only that, other applications are using major social media accounts to validate user identity—you can sign up for different apps and games just using your Facebook or Twitter account. And employers now routinely check prospective employees on social media, using it as a type of character check.
Because of the multi-purpose aspect of social media platforms, they become valuable tools that the average person spends approximately 116 minutes on every day, according to a recent study. Because they are such ubiquitous platforms, and being linked to an increasing number of applications on phones and other devices, it becomes even more necessary to secure them.
Below are some best practices for social media management for users and enterprises.
Securing your personal social media accounts
What can hackers do with a compromised account?
Mine personal information—social media accounts can lead to shopping accounts or even have banking information
Gain access to corporate networks— hackers could compromise enterprise networks if your social media is linked to your work email
Steal identity—one account can be used to register on another site
Blackmail user—in extreme cases, hackers can use sensitive information to harass the victim
The different social media platforms have security features that you should take advantage of. Here are some tips for keeping your accounts secure:
- Close the accounts that you’re not using. Forgotten social media accounts may be compromised without being noticed. Hackers can leverage these and access other accounts linked to it, like your email.
- Check what apps are connected to your social media. Do you use Facebook or Google to sign in for any other applications? Assess if this type of access is necessary.
- Practice good password hygiene. Use different passwords for your social media accounts, and also make sure each password is complex and unusual. Enabling 2FA for all your accounts can prevent unauthorized parties from accessing your accounts.
- Keep your mobile apps updated. Make sure you have the latest version of the platform you’re using. Security patches protect you from the newest known threats.
- Use a unique email for your social media accounts. If possible, create a whole new email specifically for social media accounts so that if you are compromised, the hackers won’t have access to any valuable information.
Securing corporate accounts
Social media is also used as the public face of enterprises or even entrepreneurs who use it as an advertising tool or an avenue to establish their brand. Hackers sometimes take over a company’s social media to promote their own brand, gain followers, or even spread a specific message. This form of hacktivism is an ongoing problem, especially with Twitter accounts.
Here are some tips to keep corporate social media accounts secure:
- Monitor your social media regularly—keep an eye on what’s happening on all your social media platforms.
- Limit access to only the necessary people—the fewer people with access, the better. This makes it easier to control the posts and avoid any deliberate sabotage.
- Separate what is personal and what is professional—you don’t want to accidentally post something personal on a corporate account.
- Audit which tools have access to your accounts—regulate tools that help with posting since they might be vulnerable to attacks.
- Be aware of the latest security solutions—some platforms might be moving away from passwords soon, or they may be implementing a new security feature that you may want to implement.
- Like all users, practice good password hygiene and also implement strict policies about patching and updating.
Protecting yourself from fake news and misinformation
One of the biggest issues facing social media platforms is their role in the distribution of fake news. Some platforms have already started addressing the subject and are working to stop the issue, but there are still a lot of ways to use social media for spreading fake news. Cyberpropaganda has been around for years, but 24/7 social media platforms allowed opportunistic hackers to manipulate public perception quickly and efficiently. Twitter bots push fake stories in campaigns that are big enough to sway public opinion, fake Facebook stories are designed to catch likes and spread news, and popular platforms in other countries deploy similar tactics as well. News is easily created but difficult to verify.
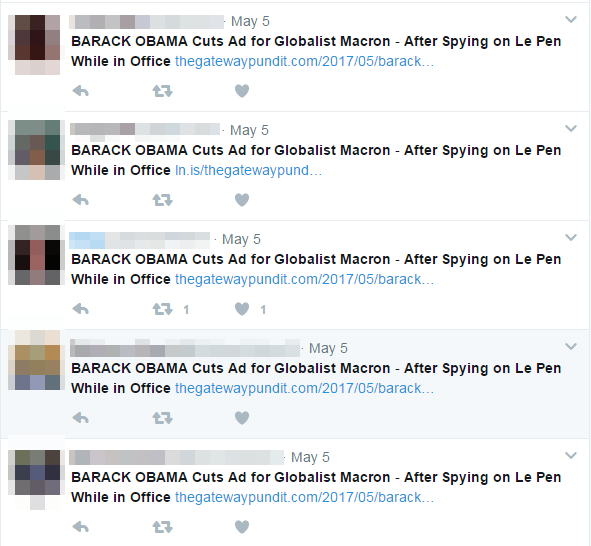
Figure 1. Example of Twitter bots disguised as different users pushing the same message
[READ: Fake News and Cyber Propaganda: The Use and Abuse of Social Media]
Because the platforms themselves are having a hard time managing fake news, users become the first line of defense. You have to protect yourself from being a victim of fake news, and also work to stop spreading misinformation.
How can you tell if it’s fake news?
The use of hyperbolic and clickbait headlines
Spoofed websites that mimic legitimate sites
Misspellings, errors in grammar and an unprofessional-looking website
Doctored images
Lack of author, sources, and data
To check if a story is real, do the following:
- Verify the story on other reputable media outlets
- Check the sources of the article and look at the links carefully—make sure that they are from legitimate sites
- Research on the author, and also the time and place of publishing
- Check if the commenters on the story are real people or just bots—are the posts verbatim from another person? Is it detailed or just a generic message?
- Read news from a broader range of titles—sometimes similar publications share stories so check outside of your normal sources
Of course, there is always a chance that you could be compromised by a hacker—even after following best practices. Secure your social media accounts with comprehensive and multilayered protection. Effective and comprehensive security solutions can help you enjoy your digital life safely. Trend Micro™ Maximum Security secures multiple devices, helps manage passwords, and guards against the most prevalent online threats.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- Hunt Them All: An AI-Powered Vulnerability Sweep of 19,000 MCP Servers
- Pwning Agentic AI Part I: Your AI Agent Is Already Compromised
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation