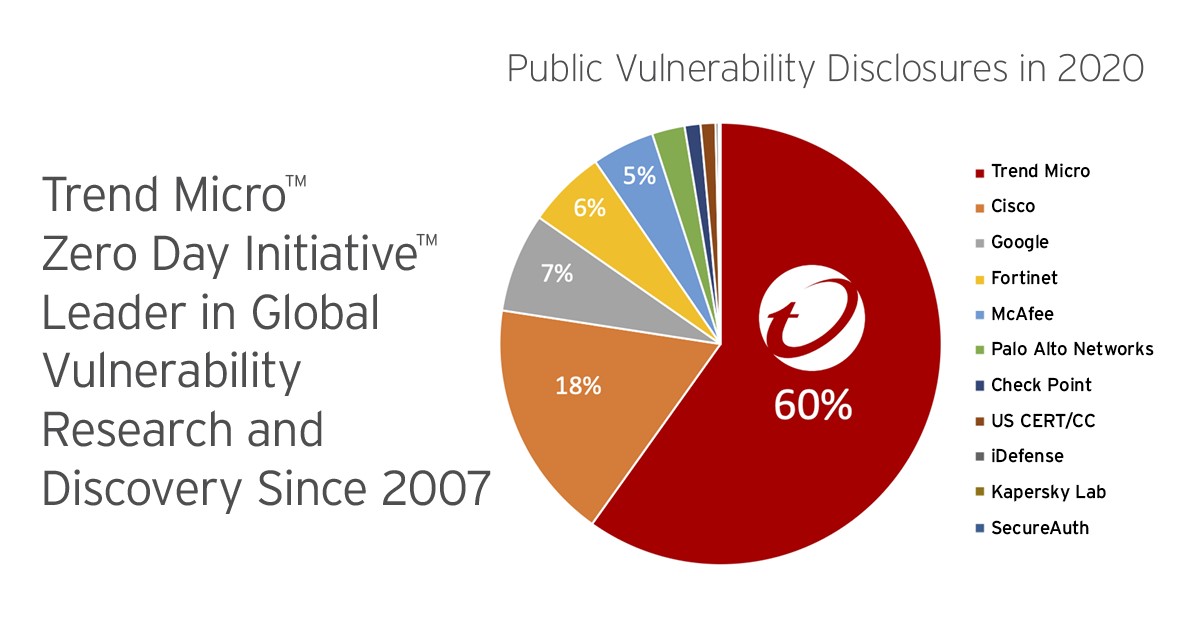
The Trend Micro Zero Day Initiative (ZDI) again dominated the number of disclosed vulnerabilities for the 13th year in a row based on Omdia’s research into the vulnerability disclosure market.
Of 11 vendors, ZDI disclosed 60.5% of the bugs in 2020. This continued leadership has ensured our customers have the best vulnerability research in the industry backing them up against the use of exploits in attacks coming from malicious actors.
Omdia dove into all the vulnerabilities disclosed by the 11 vendors and identified 1,378 of them in 2020, of which ZDI disclosed 825.
Omdia Research: 2021
Digging deeper into the reported vulnerabilities, the ZDI bug bounty program also disclosed the most vulnerabilities in every severity level, critical, high, medium and low.
More impressive is that of the 825 total bugs, 633 were critical or high severity ratings. This shows the value of having 10,000 external researchers who are part of the bug bounty program submitting high-value bugs to the program. This ensures the vendor of popular enterprise software with operating systems and applications that are affected can provide patches to their customers so malicious actors are less able to exploit these bugs.
Overall, all vendors have improved their support for higher severity bugs, as the overall average CVSS score was just over 7.6 – right in the “high” rating.
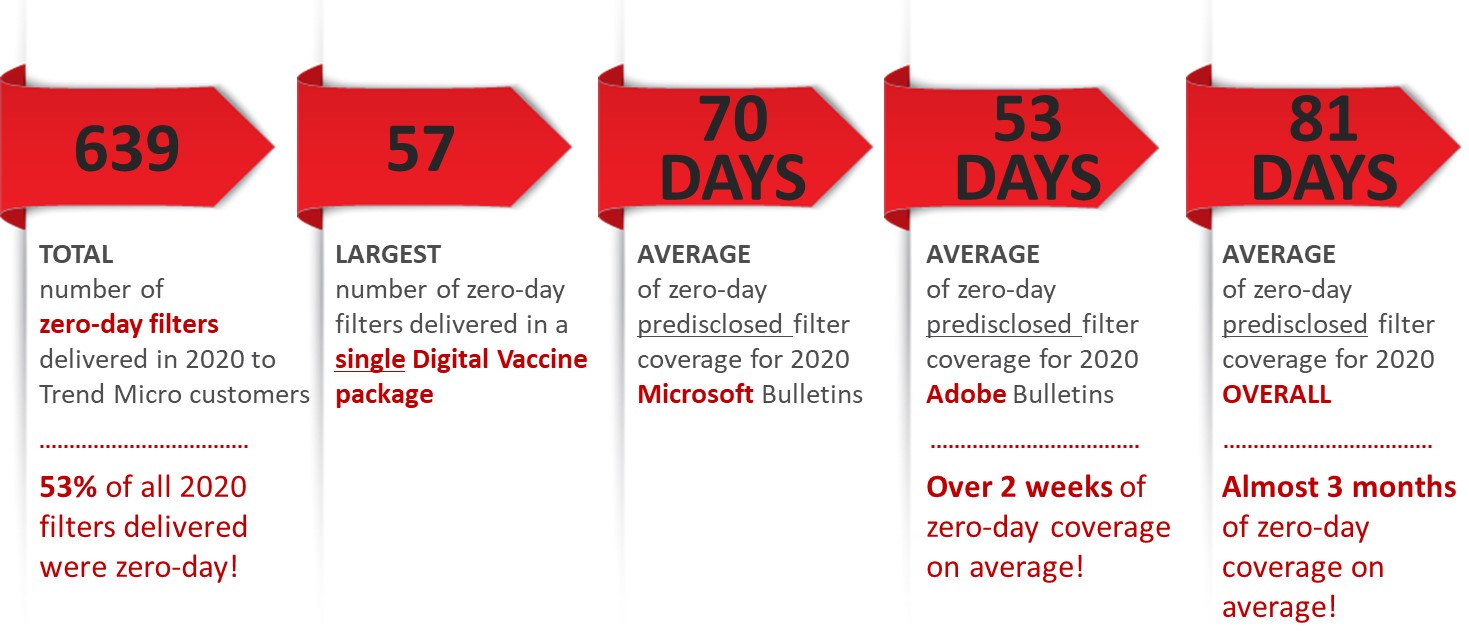
One reason Trend Micro customers benefit from the ZDI is through internal sharing of vulnerability details, which allow IPS filters to be written for a number of solutions, including TippingPoint, Cloud One, Apex One, and Worry-Free Business Security.
An added benefit to our TippingPoint customers: IPS filters for bugs submitted to the ZDI receive earlier protection than anyone else. In 2020, that meant an average of 81 days before a vendor patch was released, TippingPoint customers were protected from exploits of these bugs.
Besides pre-disclosed vulnerability support, Trend Micro Research includes experts in post-disclosure vulnerability researchers who identify many of the critical bugs disclosed over the year. This team also reverse engineers and analyzes ways they can be exploited to develop IPS filter rules for customers.
This combination gives Trend Micro unprecedented and unmatched research around vulnerabilities and exploits.
ZDI will continue to improve its program to ensure our customers and the world is safe from exploited vulnerabilities now and in the future.

