Internet of Things (IoT) malware researchers are familiar with the struggle of pivoting from a particular malware sample to another. IoT malware samples are tricky to handle and categorize, as they are usually compiled for multiple architectures. Also, there is a lack of tools and techniques to investigate these types of files.
To help IoT and Linux malware researchers in general to investigate attacks containing Executable and Linkable Format (ELF) files, we created Trend Micro ELF Hash (aka telfhash). Telfhash is an open-source clustering algorithm that helps effectively cluster Linux IoT malware samples. Simply put, it can be understood as a concept similar to import hashing (aka ImpHash) for ELF files, although there are some crucial differences between telfhash and a symbol table hash.
We first released the algorithm to the public in April this year. Today, we are thrilled to announce that telfhash is now officially supported on VirusTotal!

After hours and hours of meticulous coding and thorough testing (not to mention finding a bug in Go compiler during the process), we are now making telfhash more widely accessible to security researchers worldwide. VirusTotal has always been a valuable tool for threat research. Now, with telfhash, users of the VirusTotal Intelligence platform can also start pivoting from one ELF file to others.
As it deals with ELF files, telfhash is beneficial for IoT research and beyond; this clustering algorithm can also be used for any Linux-related malware research such as analysis for some attacks concerning Docker containers, Windows Subsystem for Linux (WSL), cryptominer, rootkits, and many more. It can also be especially helpful in cases where variants of malware become cross-platform threats.
How telfhash can help in malware investigations
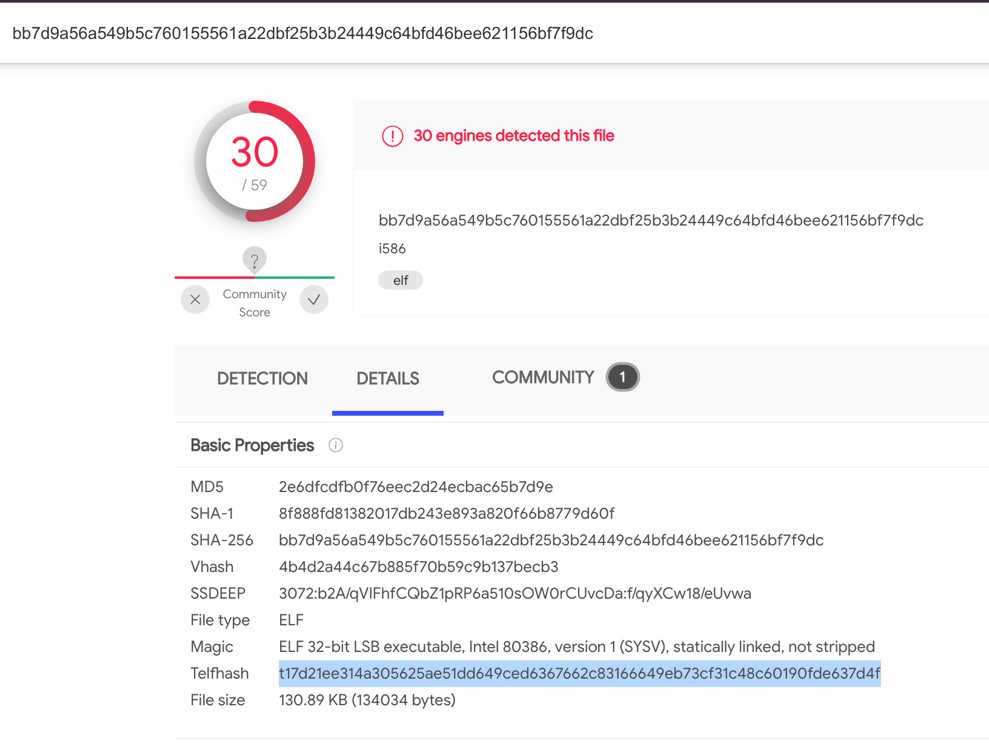
Consider the SHA-256 hash of a sample: bb7d9a56a549b5c760155561a22dbf25b3b24449c64bfd46bee621156bf7f9dc. The sample is a 32-bit ELF executable associated with Mirai IoT malware. After using the hash for the search, the telfhash value was found in the “Details” portion of the search result.
VirusTotal Intelligence users can click on this value to search for ELF files matching this telfhash. Upon performing this step for this particular sample, the search returned seven other files:
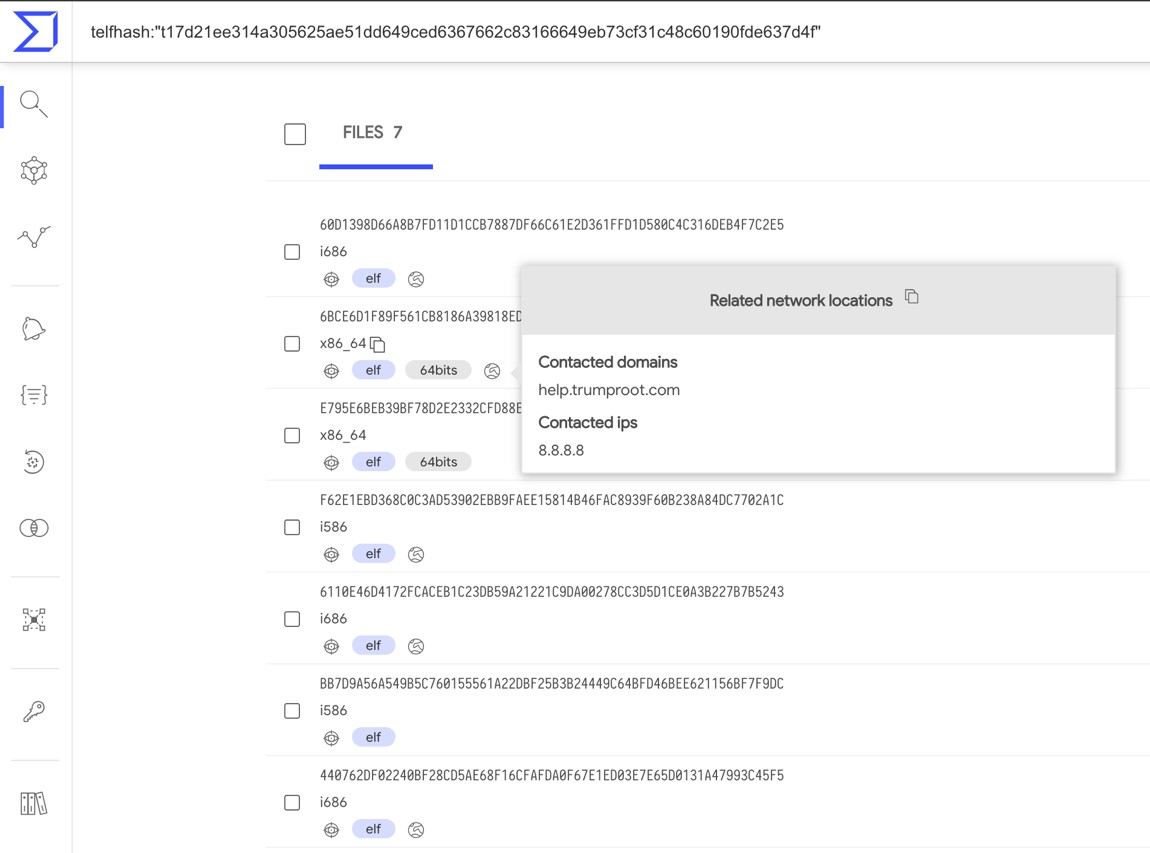
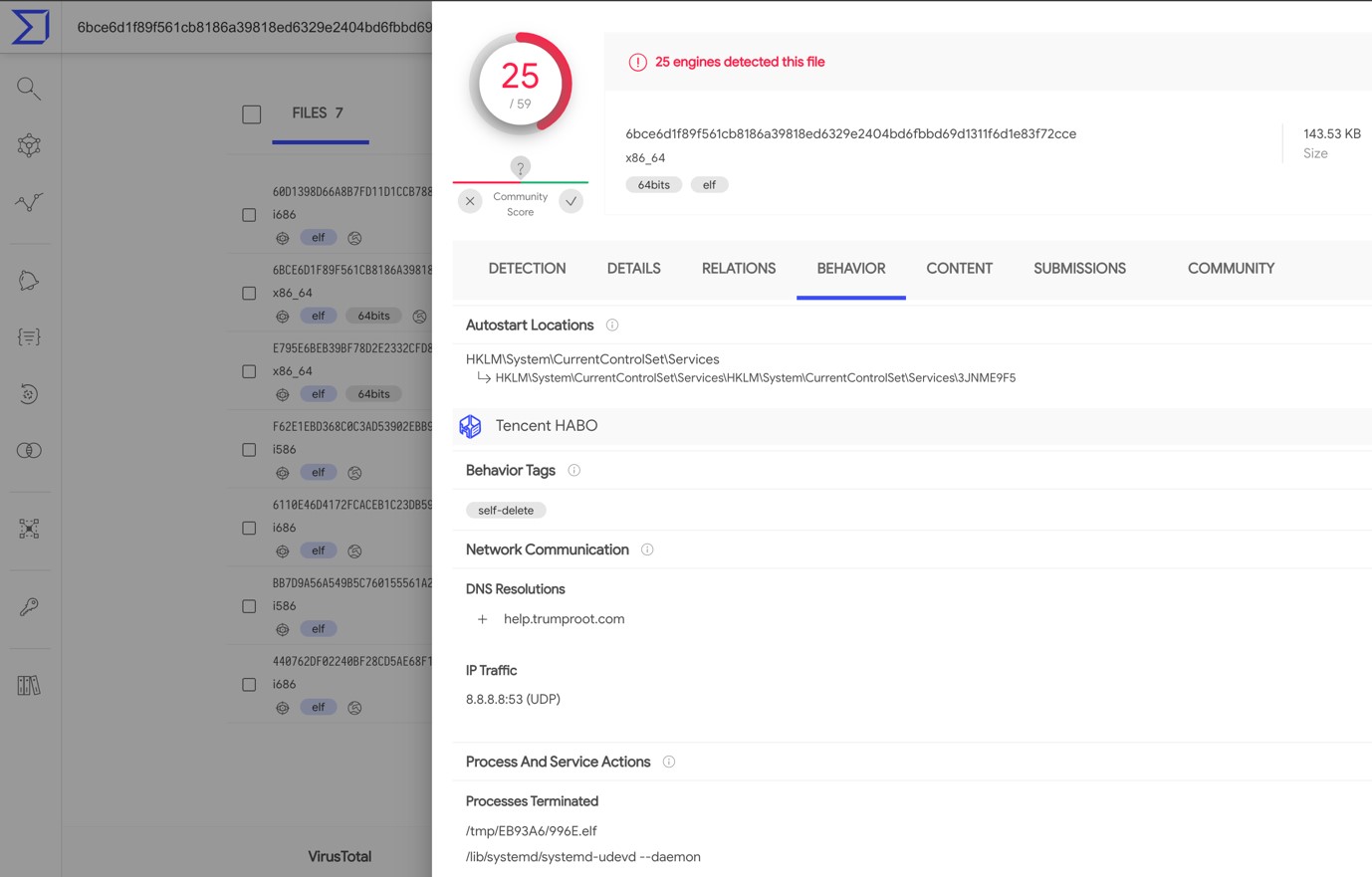
The “Behavior” tab features useful information on the found samples. The uncovered data includes IP addresses contacted and command and control (C&C) URLs, revealing network indicators that are usually extremely relevant to an investigation. This is an example of successfully pivoting from a single IoT malware hash to seven others.
Notice that the result also includes 64-bit ELF files. This is because telfhash is architecture-agnostic. More details on this can be found in our previous blog where we discuss this clustering algorithm.
Telfhash is also available via VirusTotal API. With this, we hope to equip the industry better in its ongoing battle against IoT malware. We wish good elf hunting to all security researchers out there!

