Back numbers
- Part 1: Importance of the Protocol Gateway
- Part 2: Vulnerability Allowing Stealth Attacks on Industrial Control Systems
A protocol gateway is a small network device, also called a "protocol converter" or "IoT gateway." It is similar to an "interpreter" in the digital word, and acts as a communications intermediary between different protocols. As the integration of networks accelerates with IoT, protocol conversion grows increasingly important. However, the security of protocol gateways has not been fully verified so far. Focusing on potential protocol gateway security risks, Trend Micro released a white paper summarizing these risks on August 6, 2020. In this blog series, based on the results of this research, we will analyze the impacts of the serious vulnerabilities detected in the protocol gateways essential when shifting to smart factories, and we will propose the security countermeasures that security administrators in those factories must take. In the final of this series, Part 3 describes a stealth attack method that abuses a vulnerability as well as inform you of a vital point of security measures required for the future ICS environment.
Stealth Attack Method Abusing Vulnerability of Bypassing Protocol Conversion
Trend Micro has found protocol gateways allowing invalid Modbus TCP packets to pass through in this research. This vulnerability has been reported to vendors as "ZDI-CAN-10485" by the Zero Day Initiative, the vulnerability specialized organization of Trend Micro.
Although this vulnerability itself is no more than simple packet transfer, it has been demonstrated that a stealth attack on field devices would be allowed by abusing it in conjunction with a certain type of packet. Fig. 1 is a schematic of a stealth attack. It is possible for attackers to issue unauthorized instructions to field devices such as PLC without being noticed by ICS administrators, by generating packets which are invalid Modbus TCP packets but are valid and meaningful to Modbus RTU.
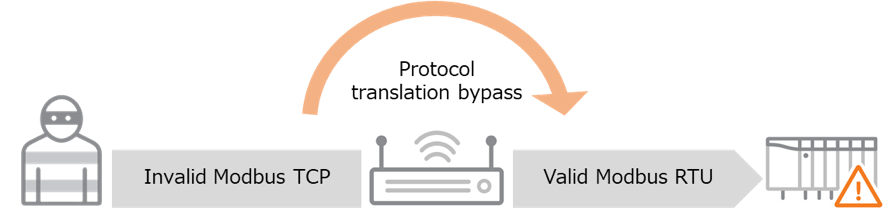
<Fig. 1> Schematic of Stealth Attack Abusing Vulnerability of Bypassing Protocol Conversion
Method: Packets for Attack Abusing Vulnerability
In order to realize the attack scenario mentioned above, the research team of Trend Micro tried to generate packets which meet the following conditions:
- Packets which trigger bypassing protocol conversion.
- Packets which are input into protocol gateways as Modbus TCP are also valid as Modbus RTU.
- Packets whose instruction contents at the time of being read as Modbus RTU are entirely different from those at the time of being generated as Modbus TCP packets.
The trial was successful and multiple packets which meet the conditions described above were generated. The following numeric value is an example of the packets. Note that all the following code and numerical values in the figures are represented in hexadecimal
010F000000110304D1CE0070
While this instruction code has a meaning of "read" instruction as Modbus TCP, it becomes a "write" instruction as Modbus RTU. Let's take a detailed look. If this packet is analyzed based on the protocol specifications of Modbus TCP, it will be interpreted as the instruction "read and input register (function code 0x04)" for "Unit ID 3" (Fig. 2).
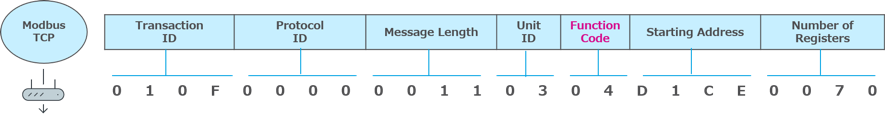
<Fig. 2> Turns to "Read" instruction under protocol specifications of Modbus TCP.
However, the data this packet contains has problems. Because even though the Message Length of the Modbus TCP header is 17 bytes (0x0011), the payload is only 6 bytes. Therefore this instruction code should have been basically discarded as a packet which does not conform to the protocol specifications. But protocol gateways with the vulnerability do not discard this packet and would transfer it to PLC as Modbus RTU.
Then what problems would happen if this packet is transferred to PLC as Modbus RTU We shall take a look at Fig. 3.
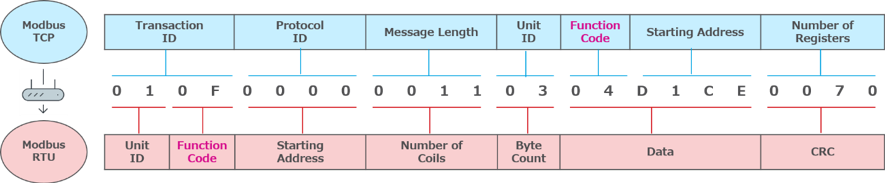
<Fig. 3> Even the same instruction code would turn to "write" under the protocol specifications of Modbus RTU.
Fig. 3 shows the implication when the previous instruction code of Modbus TCP passes through a protocol gateway, and is interpreted as an instruction code of Modbus RTU. The vulnerability of protocol gateways allows it to be sent as a command of Modbus RTU as it is without removing the header portions of Modbus TCP (Transaction ID, Protocol ID, and Message Length) which should be unnecessary essentially. As a result, this packet has worked as "correct" instruction code in the specifications of Modbus RTU.
The red portion in Fig. 3 represents the specifications of Modbus RTU. When the protocol specifications of Modbus RTU are applied to this packet, it is interpreted as "write to multiple coils (function code 0x0F)" for "Unit ID 1". This means that what was originally a "read" instruction as Modbus TCP is replaced with a "write" instruction via a protocol gateway. This attack abuses the vulnerability where a protocol gateway allows packets to pass through without filtering them and the feature that specific instruction codes have different meanings for Modbus TCP and Modbus RTU, so this attack can be considered as an advanced attack method. That is because although there are many environments which have introduced industrial firewalls that restrict writing to protocol gateways, blocking can be avoided by using this attack method. It can be considered as a new stealth attack method for attackers with advanced skills.
Protect ICS Environments from Advanced Cyber Attacks: Recommended Security Measures
ICS environments have gained complexity in response to the flow of smartification. There is a diversification of communication protocols as one side of the complexity. Along with this complexity and diversification, the importance of the role of protocol gateways seems to be increasing. However, the security risk in the protocol conversion process seems a topic which not only the security community but also people in OT or engineering region seem to have overlooked.
Manage protocol gateways as important assets
Protocol gateways which have not been attracted much notice until today should be recognized and managed as important OT assets, this is the message we want to convey the most to ICS environment administrators through this research. Protocol gateways are, by their nature, deployed in environments which need to relay important data and instructions in a timely and proper manner. They are important social infrastructure systems such as waterworks, gas, and electricity as well as smart factories. First it is important to understand and visualize the protocol gateways installed in ICS environment that you yourself manage.
Select protocol gateways with a packet filtering function.
This is the most effective countermeasure for the stealth attack method described in this part. The packet filtering function mentioned here refers to the function to detect, discard, or modify input values not conforming to the protocol specifications. As revealed in this research, there are two types of protocol gateways; one has a proper packet filtering function and the other does not. When procuring a product, we recommend proceeding through the selection process by considering the security side described in the latter half of this research paper.
Introduce industrial firewalls supporting the OT protocol
Industrial firewalls supporting the OT protocol can help in two ways; packets not conforming to the protocol specifications can be detected, and access to protocol gateways can be limited to authorized end points. Using an ICS firewall can ensure traffic consistency while implementing secure access from authorized devices. EdgeIPS and EdgeFire, which are industrial network security products provided by Trend Micro, also provide similar security functions. EdgeIPS, which is transmissive network equipment, can be introduced into the uplink side of the protocol gateway with a vulnerability and utilize a protocol filtering function to enforce measures without changing the network settings of the existing environment. EdgeFire can separate segments of a network including protocol gateways and use a protocol filtering function to resolve problems. However, an ICS firewall covers only the Ethernet side of a network. As far as we know, a serial-based industrial firewall does not exist in the market. Therefore it is recommended that mission critical facilities should introduce monitoring tools into the serial side to ensure the consistency of control commands and data according to risk assessment and security requirements.
We would be pleased if this research can help to enhance security in ICS environments. The appendix of this research paper presents specific security measures against other vulnerabilities which are not described sufficiently in this blog series. Please take a look at this as well.

