Smart Home
Device Vulnerabilities in the Connected Home
In the past year, we took a closer look at the security of IoT devices around the world. We tested devices widely used in the Japan market and available in different Amazon regions to find out whether remote code execution (RCE) is possible.
If there is anything to be learned from the massive attacks that have been seen on connected devices, it is that the internet of things (IoT) is riddled with vulnerabilities. We have seen this time and again with how botnets are created from system weaknesses and have harnessed poor basic security to disrupt many devices and services.
In the past year, we embarked on a closer look at the security of IoT devices around the world. We chose devices that are available in different Amazon regions and are widely used in the Japan market, and tried to find out whether remote code execution (RCE) is possible. What we ended up finding out was more than that.
After months of finding bugs, reporting issues, and awaiting manufacturer responses, we found vulnerabilities from different device manufacturers. Some of these vulnerabilities are easy to take advantage of, while others are less risky. The bottom line, however, is that an attacker can eventually gain unauthorized remote control of any of the affected devices, which can lead to full compromise or even damage of the device.
| Manufacturer | Model | Device Type | Vulnerability | RCE | Status |
| Belkin | NetCam HD+ WiFi Camera | IP camera | SSRF + LCE | Yes | Fixed |
| Belkin | WeMo® LED Lighting Starter Set | Smart light bulbs | Unauthorized SYSEVENT service | Yes | Fixed |
| Belkin | WeMo® | Different devices | Denial of Service | No | Fixed |
| Buffalo | WSR-300HP | Router | Command Injection | Yes | Fixed |
| D-Link | DCS825L EyeOn Baby Monitor | Baby monitor | Command Injection | Yes | Fixed |
| D-Link | DCS825L EyeOn Baby Monitor | Baby monitor | Stack Overflow | Yes | Fixed |
| Dahua | IP Camera and PTZ Camera | IP camera | Predictable Recovery Password | No | Fixed |
Table 1. IoT devices found with vulnerabilities
Note: We have reached out to the affected manufacturers and we have yet to receive a response from Buffalo. WeMo’s denial of service vulnerability affects all WeMo devices. Per D-Link, a beta firmware is available and the company's U.S. technical support may be contacted via 1-877-453-5465. Dahua’s vulnerability also affects its OEM products, and while the vulnerability is not capable of RCE, it can be taken advantage of with Telnet to facilitate RCE.
We found a three-year-old vulnerability in Buffalo that is similar to the vulnerability exploited in the TR-69 SOAP RCE attack in 2016, which an attacker may find easy to take advantage of and create a botnet from. We also found security holes in Belkin devices. A Belkin WeMo® device, for instance, can be taken down by one POST HTTP request to cause a stack overflow on the critical service, which the device may find difficult to recover from.
D-Link has a built-in service on its device that offers multiple functions. We found that an attack can take advantage of this service to cause an extra stack overflow point with a crafted UDP packet and cause RCE with root permission. Dahua, for its part, has a password recovery mechanism that helps users if they forgot their credentials. We found that an attacker can take advantage of this function to take over a legitimate user’s device.
At least in the latter two cases, it seems that the same convenience afforded by the devices has also held back supposed security protections in place.
The lack of appropriate security presents a predicament, since any experienced or motivated attacker can dig for more weaknesses and exploit the ecosystem, as exemplified by the widely reported Mirai and Satori botnet campaigns.
During our research, we disclosed the discovered vulnerabilities to Zero Day Initiative (ZDI) and Information-technology Program Agency (IPA) in Japan, in accordance with their vulnerability disclosure policies. Technical details and other information on the discovered IoT vulnerabilities can be found in this technical brief.
Recommendations and solutions against IoT vulnerabilities
Security issues related to IoT are not the concern of users alone. Manufacturers should shoulder some, if not most, of the responsibility and make sure that the devices they roll out are secure and always updated. They should ensure device integrity, confidentiality, identification, and operational continuity in their IoT implementations. They should have the mindset that devices, once connected to the internet, become open to abuse.
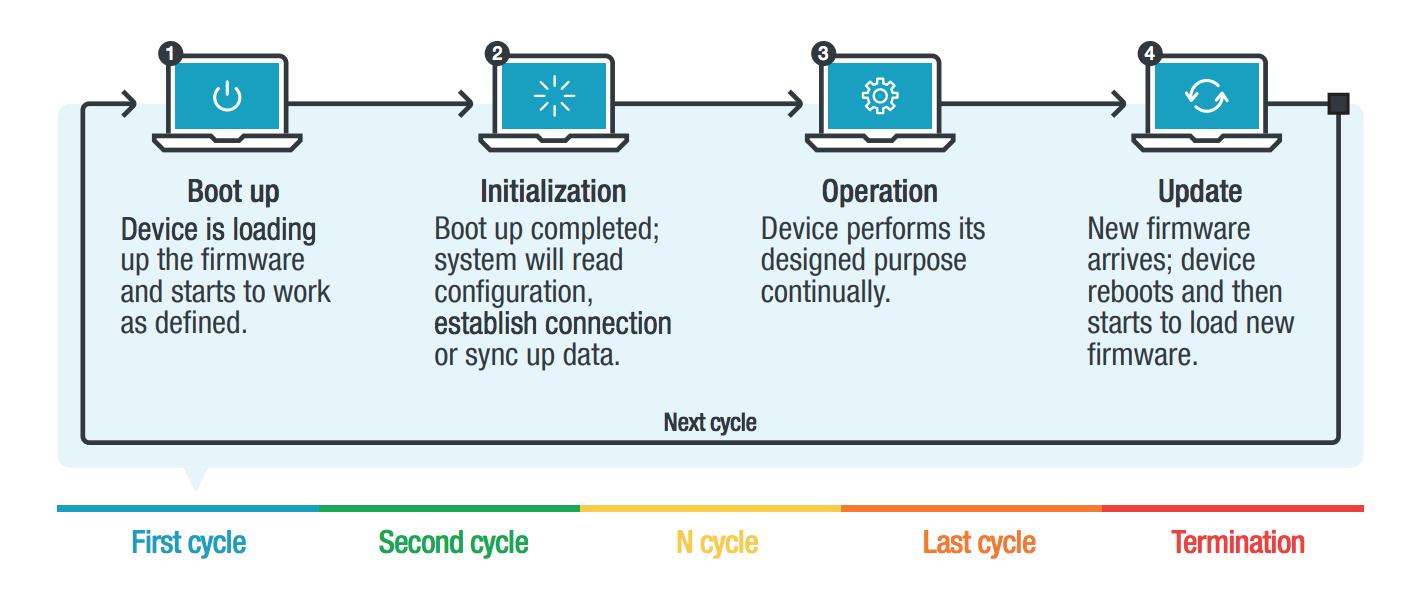
It is important to plan around the life cycle of devices – to be able to provide system protection against potential hacking and intrusion throughout their service lives. As early as the design stage, penetration testing and regular risk assessments should be prioritized. Mechanisms like recovery password generation and default factory settings, while designed for easy user access, shouldn’t have to be what users will stumble over in terms of security.
Figure 1. IoT device life cycle
The current reality is that not all devices have built-in security and some device mechanisms can be taken advantage of by attackers. Users, for their part, should therefore take steps in securing the way they set up their networks and regularly updating their devices with the latest firmware to minimize the risk of exploited vulnerabilities.
In addition to the aforementioned best practices, users can look into employing comprehensive protections such as the Trend Micro™ Security and Trend Micro™ Internet Security solutions, which offer effective safeguards against threats to IoT devices through features that can detect malware at the endpoint level. Moreover, connected devices can be protected by security software such as the Trend Micro™ Home Network Security, which can check internet traffic between the router and all connected devices. Enterprises can also monitor all ports and network protocols for advanced threats and be protected from targeted attacks with the Trend Micro™ Deep Discovery™ Inspector network appliance.
Trend Micro™ Home Network Security customers are protected from particular vulnerabilities via these rules:
- 1134520 WEB Belkin NetCam WEMO API Remote Code Execution
- 1134517 EXPLOIT Belkin Syseventd Link Remote Code Execution
- 1134521 WEB Belkin Devices WEMO API Denial of Service
- 1134286 WEB Realtek SDK Miniigd UPnP SOAP Command Execution (CVE-2014-8361)
- 1134518 WEB D-Link DCS-825L verify.cgi Command Injection -1
- 1134519 WEB D-Link DCS-825L verify.cgi Command Injection -2
- 1134525 EXPLOIT D-Link DCS-825L Buffer Overflow -1