Black Basta, a new ransomware gang, has swiftly risen to prominence in recent weeks after it caused massive breaches to organizations in a short span of time.
On April 20, 2022, a user named Black Basta posted on underground forums known as XSS.IS and EXPLOIT.IN to advertise that it intends to buy and monetize corporate network access credentials for a share of the profits. The advertisement also specified that it was looking for organizations based in the United States, Canada, United Kingdom, Australia, and New Zealand, which are all English-speaking countries. A report noted that malicious actors acquired stolen credentials from some darknet websites that peddle an enormous amount of exfiltrated data to the underground market.
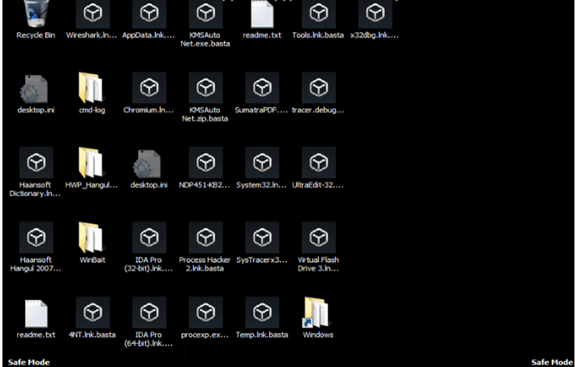
On April 26, Twitter user PCrisk tweeted about the new Black Basta ransomware that appends the extension .basta and changes the desktop wallpaper.
This blog entry takes a closer look at the Black Basta ransomware and analyzes this newcomer’s familiar infection techniques.
The infection routine
Black Basta ransomware needs administrator rights to run. It otherwise displays a command prompt message as shown on Figure 1.
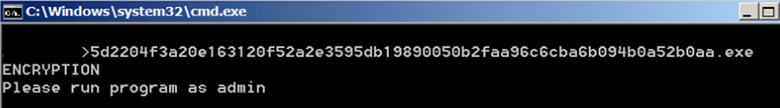
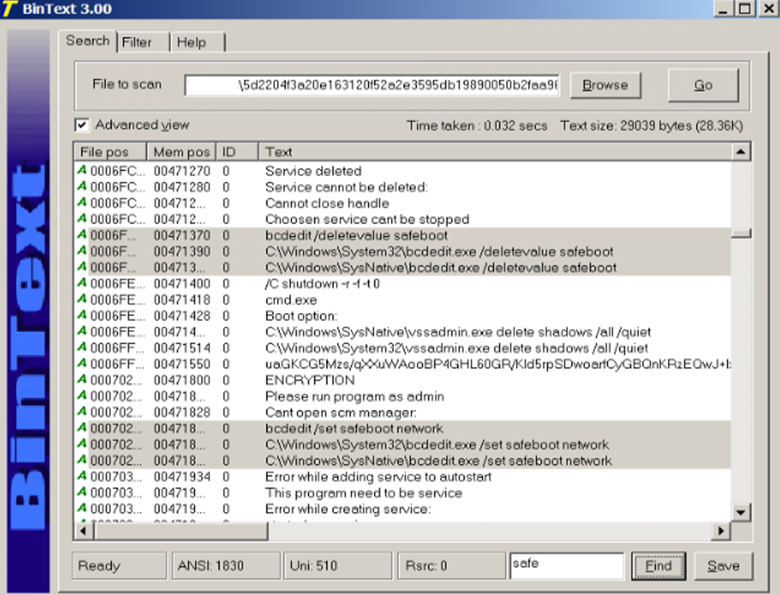
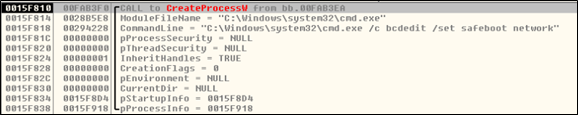
After running the ransomware as administrator, it removes shadow copies, disables Windows recovery and repair, and boots the PC in safe mode.
- C:\Windows\SysNative\vssadmin.exe delete shadows /all /quiet
- C:\Windows\SysNative\bcdedit.exe /deletevalue safeboot
- C:\Windows\SysNative\bcdedit /set safeboot networkChanges
It also drops the following files, which will be used later when changing the desktop wallpaper and icons for encrypted files:
- %Temp%\fkdjsadasd.ico
- %Temp%\dlaksjdoiwq.jpg
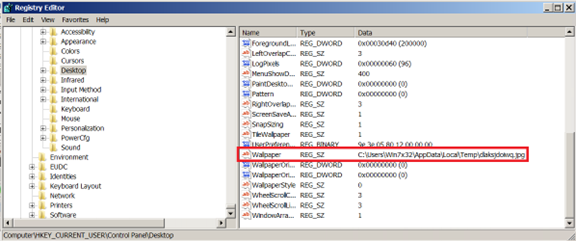
Before booting the infected device into safe mode, it changes the desktop wallpaper by dropping the .jpg file into the %temp% folder and creating the following registry entry:
- Key: HKCU\Control Panel\Desktop; Value: Wallpaper; Data:%Temp%\dlaksjdoiwq.jpg;
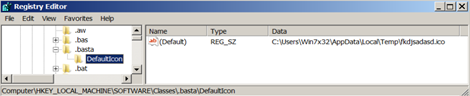
After changing the desktop wallpaper, it then adds the following registry keys to change the icon of the encrypted files with the .basta extension:
- HKLM\SOFTWARE\Classes\.basta
- HKLM\SOFTWARE\Classes\.basta\DefaultIcon data: %TEMP%\fkdjsadasd.ico
The ransomware proceeds to encrypt files while the device is in safe mode, appending all encrypted files with the .basta extension. The ransom note is found in all the folders the ransomware has affected.
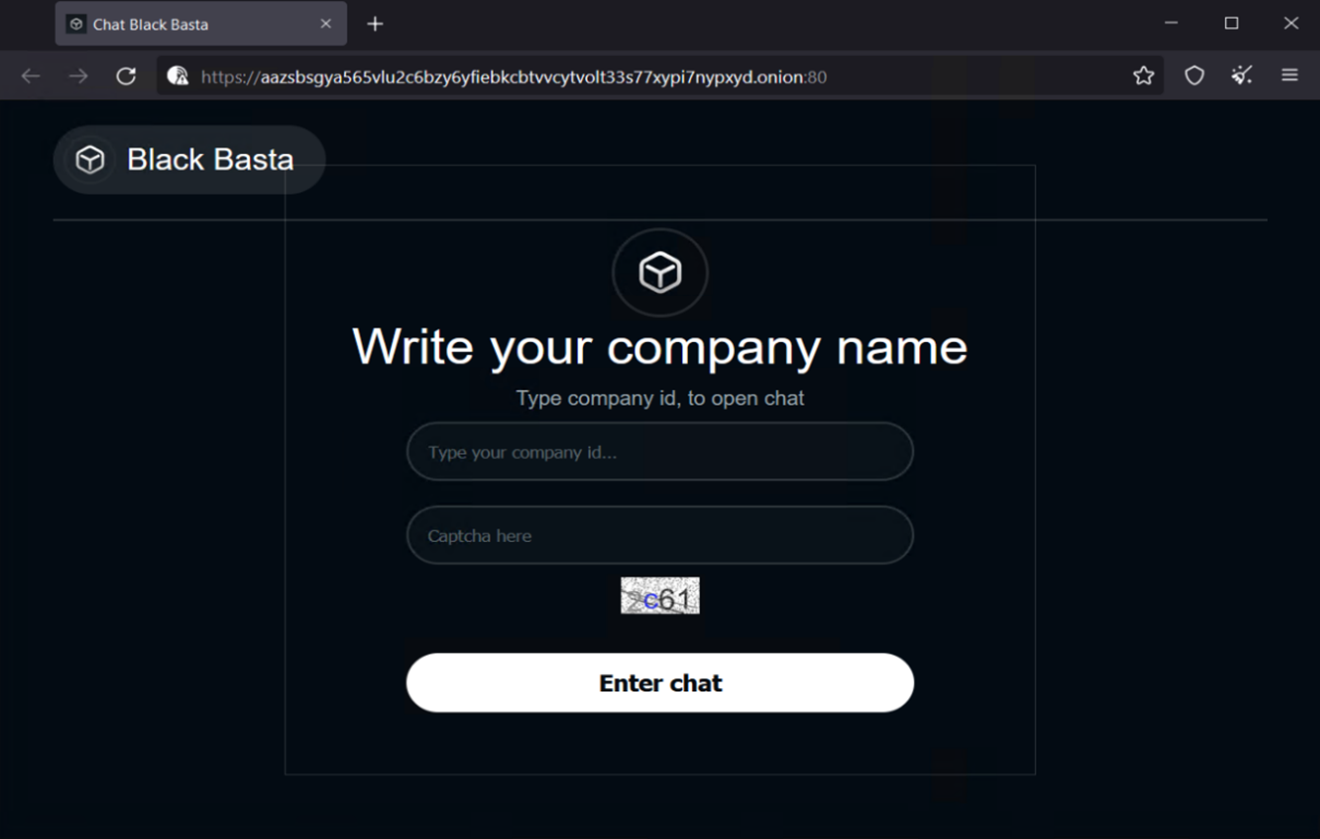
The ransom note indicates the malicious actor’s onion site and a company ID. Despite running the same ransomware (SHA256 hash: 5d2204f3a20e163120f52a2e3595db19890050b2faa96c6cba6b094b0a52b0aa) on different virtual machines, the company ID the gang provides is the same across all devices.
Using another binary (SHA256 hash: 7883f01096db9bcf090c2317749b6873036c27ba92451b212b8645770e1f0b8a), a different company ID is shown on the ransom note. The files are likewise appended with the .basta extension.
Analyzing the infection routine
Black Basta’s recent entry to the cybercrime world suggests that information about their operations is still limited. According to a report, the gang has neither started marketing its operations nor has it begun recruitment of affiliates in underground forums. Based on advertisements they posted before the attacks, the malicious actor likely uses stolen credentials — purchased in darknet websites or underground forums — to get into an organization’s system.
We probed further and found that the company ID written in the ransom note is hardcoded in the binary file.
Black Basta attempts to delete shadow copies using vssadmin.exe and boots the device in safe mode using bcdexit.exe from different paths, specifically, %SysNative% and %System32%.

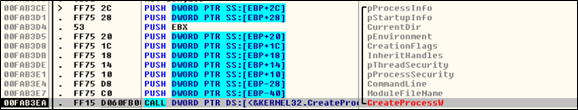
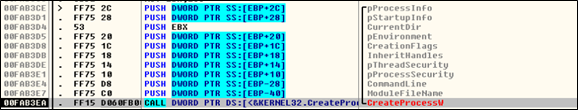
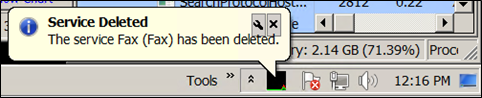
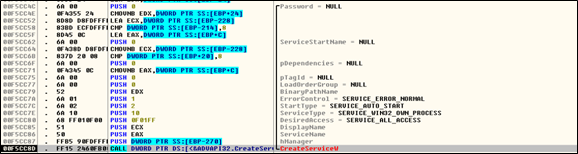
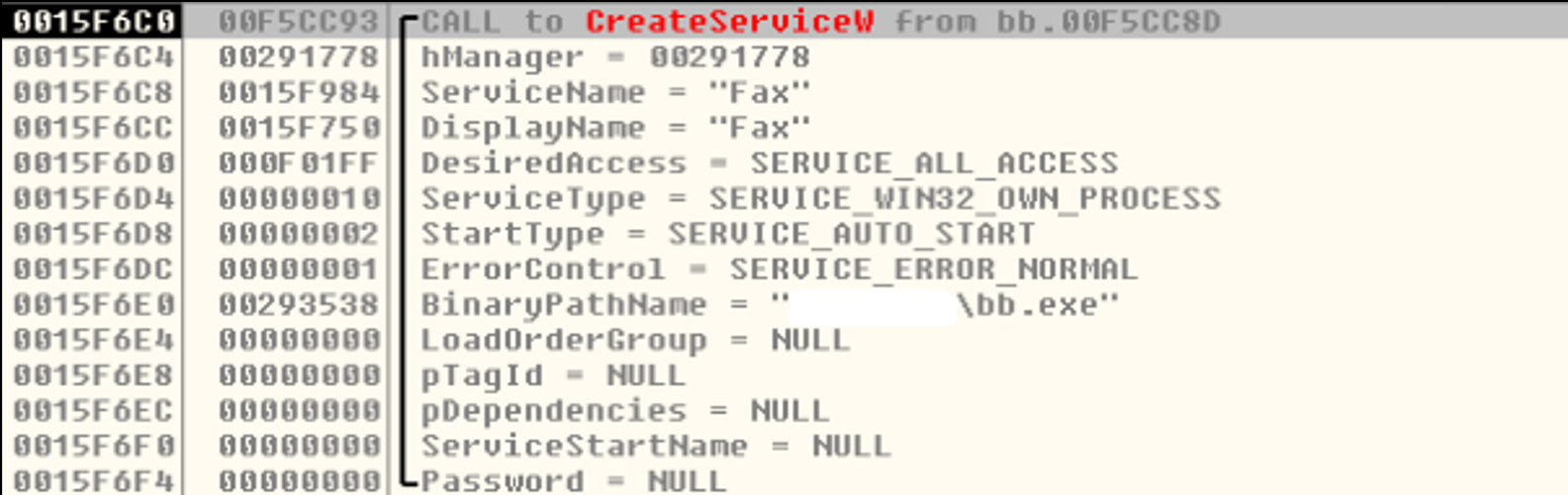
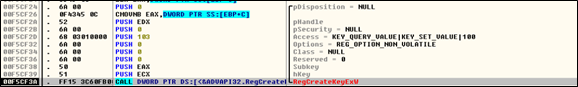
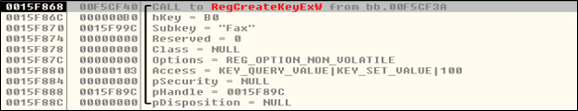
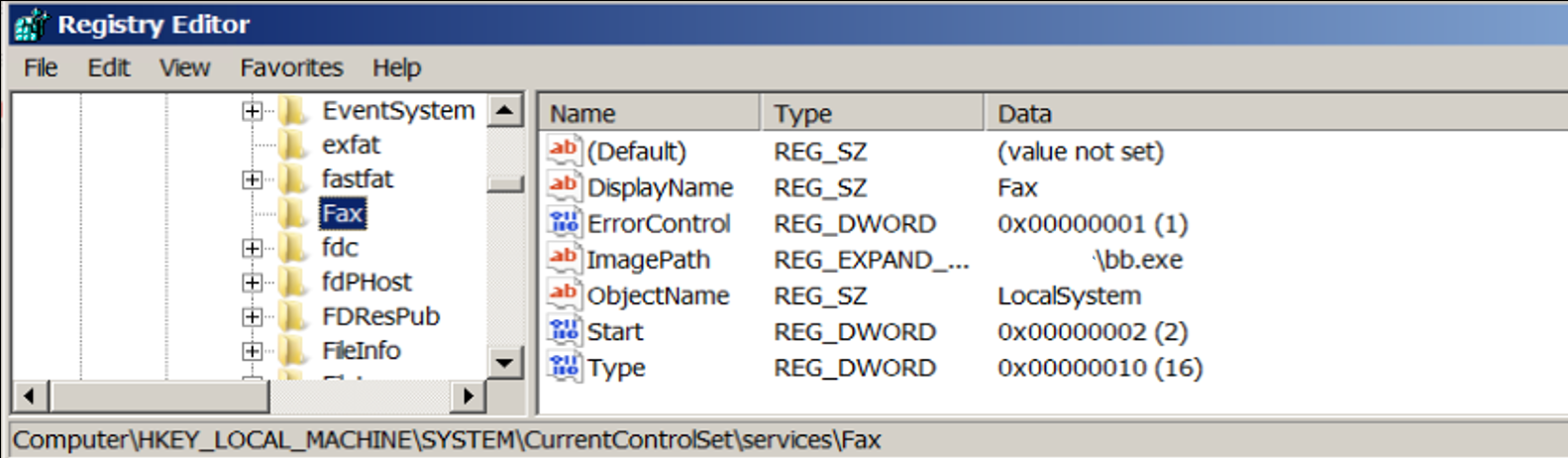
At this stage, the ransomware deletes the service named Fax, and creates a new one with the same name using the malware’s path and adds it to the registry for persistence.
It then uses ShellExecuteA to shut down and restart the victim’s machine.

Extortion phase
For a newcomer in the field, Black Basta is quite prolific for having compromised at least a dozen organizations in just a few weeks. The group’s first known attack using the Black Basta ransomware occurred in the second week of April 2022. But an earlier sample was also spotted back in February 2022 with the ransomware name “no_name_software,” which appends the extension “encrypted” to encrypted files. According to some threat researchers, it appears that Black Basta has been in development since early February 2022.
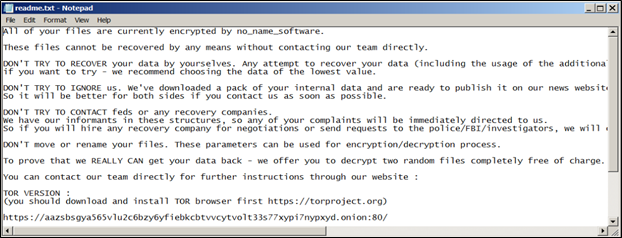
Like other enterprise-focused ransomware operations, Black Basta employs a double extortion scheme that involves exfiltrating confidential data before encryption to threaten victims with public release of the stolen data.
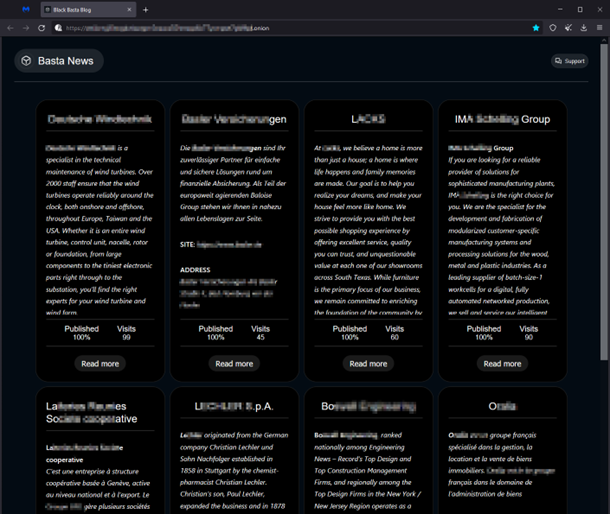
The gang carries out the extortion phase of its attacks on its Tor site, Basta News, which contains a list of all the victims who have not paid the ransom.
Possible relation to an APT
Security researchers exchanged speculations on Twitter that Black Basta is possibly a rebranding of the Conti ransomware operation. MalwareHunterTeam pointed out many similarities in its leak site, payment site, and negotiation style to those of Conti’s. Twitter user Arkbird echoed the same observation. Lawrence Abrams of BleepingComputer also mentioned that the malicious actors behind Black Basta seem like they are exerting a lot of effort to avoid any resemblance to their previous identity.
We have also noticed some similarities between the Black Basta and Black Matter payment sites. Like Black Matter, Black Basta implements user verification on its Tor site. However, the leak site does not implement a session key.

New findings: QAKBOT possibly related to Black Basta
Based on our analysis of another set of samples monitored within a 72-hour timeframe, we discovered a possible correlation between QAKBOT and Black Basta ransomware. We observed the following:
- As with QAKBOT, the malware is downloaded and executed from a malicious Excel file. Similar to the typical routine of the QAKBOT binary, it then executes certain PowerShell commands as part of its staging phase.
- From information gathered in our telemetry, we found the presence of the Black Basta ransomware within the 72-hour period in which it encrypted files on victims’ machine. Trend Micro detects this as Ransom.Win32.BASTACRYPT.YACEDT.
- Other researchers pointed out that QAKBOT deploys its version of the exploit PRINTNIGHTMARE (aka QUAKNIGHTMARE) during the same timeframe. We also observed the presence of the weaponized exploit. This, in turn, executes another binary with escalated privilege. Unfortunately, we were unable to find the presence of the file pointed by the hardcoded path. string to complete the attack chain. Trend Micro detects this as Trojan.Win64.QUAKNIGHTMARE.YACEJT.
Malicious actors also use certain tools as seen through our sensors, but we were unable to obtain the complete kit. We have so far gathered paths related to the tools themselves that include the following:
- AdwareCleaner (C:\AdwCleaner\*)
- Either PC-Cleaner or Pervasive PSQL/SQL (C:\pvsw\*)
The structure of the ransomware loader is also different from the external article. In this case, instead of dropping and executing the ransomware itself, the loader downloads to the device’s memory then uses reflective loading to launch the ransomware.
The information we have collected so far indicates that the malicious actor behind Black Basta possibly used QAKBOT as a new means to deliver the ransomware.
Insights
The malicious actors could be using a unique binary for each organization that they target. This can be seen from the ransom note that they drop, which is hardcoded in the malware itself. A ransomware typically creates a unique ID for each victim despite being infected by the same executable. Their choice of target organizations also suggests this to be the case. They buy corporate network access credentials in underground markets, which could mean that they do not distribute their malware sporadically. Instead, they use a certain kind of binary or variant for a specific organization.
Recommendations
Threat researchers suggest that the recent attacks by Black Basta can be seen as early manifestations of Conti’s rebranding efforts. True or not, organizations should keep a watchful eye against ransomware threats. An organization’s thorough assessment of its security posture and its implementation of solid cybersecurity defenses give it a better fighting chance against such threats.
To protect systems against similar attacks, organizations can establish security frameworks that allocate resources systematically for establishing a strong defense strategy against ransomware. Here are some best practices that organizations can consider:
Audit and inventory
- Take an inventory of assets and data
- Identify authorized and unauthorized devices and software
- Audit event and incident logs
Configure and monitor
- Manage hardware and software configurations
- Grant admin privileges and access only when necessary to an employee’s role
- Monitor network ports, protocols, and services
- Activate security configurations on network infrastructure devices such as firewalls and routers
- Establish a software allowlist that only executes legitimate applications
Patch and update
- Conduct regular vulnerability assessments
- Perform patching or virtual patching for operating systems and applications
- Update software and applications to their latest versions
Protect and recover
- Implement data protection, backup, and recovery measures
- Enable multifactor authentication (MFA)
Secure and defend
- Employ sandbox analysis to block malicious emails
- Deploy the latest versions of security solutions to all layers of the system, including email, endpoint, web, and network
- Detect early signs of an attack such as the presence of suspicious tools in the system
- Use advanced detection technologies such as those powered by AI and machine learning
Train and test
- Regularly train and assess employees in security skills
- Conduct red-team exercises and penetration tests
A multilayered approach can help organizations guard possible entry points into their system (endpoint, email, web, and network). Security solutions can detect malicious components and suspicious behavior, which can help protect enterprises.
- Trend Micro Vision One™ provides multilayered protection and behavior detection, which helps block questionable behavior and tools before the ransomware can do any damage.
- Trend Micro Cloud One™ – Workload Security protects systems against both known and unknown threats that exploit vulnerabilities. This protection is made possible through techniques such as virtual patching and machine learning.
- Trend Micro™ Deep Discovery™ Email Inspector employs custom sandboxing and advanced analysis techniques to effectively block malicious emails, including phishing emails that can serve as entry points for ransomware.
- Trend Micro Apex One™ offers next-level automated threat detection and response against advanced concerns such as fileless threats and ransomware, ensuring the protection of endpoints.
Indicators of compromise (IOCs)
| SHA256 | Trend Micro Detection |
| 5d2204f3a20e163120f52a2e3595db19890050b2faa96c6cba6b094b0a52b0aa | Ransom.Win32.BASTACRYPT.THDBGBB |
| 7883f01096db9bcf090c2317749b6873036c27ba92451b212b8645770e1f0b8a | Ransom.Win32.BASTACRYPT.YXCD2 |
| ae7c868713e1d02b4db60128c651eb1e3f6a33c02544cc4cb57c3aa6c6581b6e | Ransom.Win32.BASTACRYPT.THDBIBB |
| 17205c43189c22dfcb278f5cc45c2562f622b0b6280dcd43cc1d3c274095eb90 | Ransom.Win32.BASTACRYPT.YXCD2 |
| a54fef5fe2af58f5bd75c3af44f1fba22b721f34406c5963b19c5376ab278cd1 | Ransom.Win32.BASTACRYPT.THDBGBB |
| 1d040540c3c2ed8f73e04c578e7fb96d0b47d858bbb67e9b39ec2f4674b04250 | Ransom.Win32.BASTACRYPT.YXCD2 |
| 2967e1d97d32605fc5ace49a10828800fbbefcc1e010f6004a9c88ef3ecdad88 | Ransom.Win32.BASTACRYPT.YXCD2.note |
| f088e6944b2632bb7c93fa3c7ba1707914c05c00f9491e033f78a709d65d7cff | Ransom.Win32.BASTACRYPT.YXCD2.note |
For QAKBOT-related samples:
| SHA256 | Trend Micro Detections |
| a48ac26aa9cdd3bc7f219a84f49201a58d545fcebf0646ae1d676c7e43c6ac3e | TrojanSpy.Win32.QAKBOT.YACEDT |
| 82c73538322c8b90c25a99a7afc2fafcd7e7e03fe920a3331ef0003300ac10b8 | TrojanSpy.Win32.QAKBOT.YACEDT |
| 82c73538322c8b90c25a99a7afc2fafcd7e7e03fe920a3331ef0003300ac10b8 | TrojanSpy.Win32.QAKBOT.YACEDT |
| 2083e4c80ade0ac39365365d55b243dbac2a1b5c3a700aad383c110db073f2d9 | TrojanSpy.Win32.QAKBOT.YACEDT |
| 2e890fd02c3e0d85d69c698853494c1bab381c38d5272baa2a3c2bc0387684c1 | TrojanSpy.Win32.QAKBOT.YACEDT |
| 2d906ed670b24ebc3f6c54e7be5a32096058388886737b1541d793ff5d134ccb | TrojanSpy.Win32.QAKBOT.YACEDT |
| 72fde47d3895b134784b19d664897b36ea6b9b8e19a602a0aaff5183c4ec7d24 | TrojanSpy.Win32.QAKBOT.YACEDT |
| ffa7f0e7a2bb0edf4b7785b99aa39c96d1fe891eb6f89a65d76a57ff04ef17ab | TrojanSpy.Win32.QAKBOT.YACEDT |
| 1e7174f3d815c12562c5c1978af6abbf2d81df16a8724d2a1cf596065f3f15a2 | TrojanSpy.Win32.QAKBOT.YACEDT |
| 130af6a91aa9ecbf70456a0bee87f947bf4ddc2d2775459e3feac563007e1aed | Trojan.Win64.QUAKNIGHTMARE.YACEJT |
| 81a6c44682b981172cd85ee4a150ac49f838a65c3a0ed822cb07a1c19dab4af5 | Ransom.Win32.BASTACRYPT.YACEDT |
| 94428d7620fff816cb3f65595978c6abb812589861c38052d30fa3c566e32256 | Ransom.Win32.BASTACRYPT.YACEDT |
| c9df12fbfcae3ac0894c1234e376945bc8268acdc20de72c8dd16bf1fab6bb70 | Ransom.Win32.BASTACRYPT.YACEJT |
| 0d3af630c03350935a902d0cce4dc64c5cfff8012b2ffc2f4ce5040fdec524ed | Trojan.Win32.BLACKBASTA.YXCEJ |
| 3fe73707c2042fefe56d0f277a3c91b5c943393cf42c2a4c683867d6866116fc | Trojan.Win32.BLACKBASTA.YXCEJ |
| 3fe73707c2042fefe56d0f277a3c91b5c943393cf42c2a4c683867d6866116fc | Trojan.Win32.BLACKBASTA.YXCEJ |
| 0e2b951ae07183c44416ff6fa8d7b8924348701efa75dd3cb14c708537471d27 | Trojan.Win32.BLACKBASTA.YXCEJ |
| 8882186bace198be59147bcabae6643d2a7a490ad08298a4428a8e64e24907ad | Trojan.Win32.BLACKBASTA.YXCEJ |
| df35b45ed34eaca32cda6089acbfe638d2d1a3593d74019b6717afed90dbd5f8 | Trojan.Win32.BLACKBASTA.YXCEJ |
| b8aa8abac2933471e4e6d91cb23e4b2b5a577a3bb9e7b88f95a4ddc91e22b2cb | TrojanSpy.VBS.KEYLOAD.A |
| fb3340d734c50ce77a9f463121cd3b7f70203493aa9aff304a19a8de83a2d3c9 | TrojanSpy.VBS.KEYLOAD.A |
| 5ab605b1047e098638d36a5976b00379353d84bd7e330f5778ebb71719c36878 | TrojanSpy.VBS.KEYLOAD.A |
| 9707067b4f53caf43df5759fe40e9121f832e24da5fe5236256ad0e258277d88 | TrojanSpy.VBS.KEYLOAD.A |
| 9707067b4f53caf43df5759fe40e9121f832e24da5fe5236256ad0e258277d88 | TrojanSpy.VBS.KEYLOAD.A |
| d7580fd8cc7243b7e16fd97b7c5dea2d54bcba08c298dc2d82613bdc2bd0b4bf | TrojanSpy.VBS.KEYLOAD.A |
| 919d1e712f4b343856cb920e4d6f5d20a7ac18d7386673ded6968c945017f5fd | TrojanSpy.VBS.KEYLOAD.A |
| 012826db8d41ff4d28e3f312c1e6256f0647bf34249a5a6de7ecac452d32d917 | TrojanSpy.VBS.KEYLOAD.A |
| d36a9f3005c5c24649f80722e43535e57fd96729e827cdd2c080d17c6a53a893 | TrojanSpy.VBS.KEYLOAD.A |
| 580ce8b7f5a373d5d7fbfbfef5204d18b8f9407b0c2cbf3bcae808f4d642076a | Backdoor.Win32.COROXY.YACEKT |

