Ransomware Spotlight: Rhysida
Top affected countries and industries according to Trend Micro data
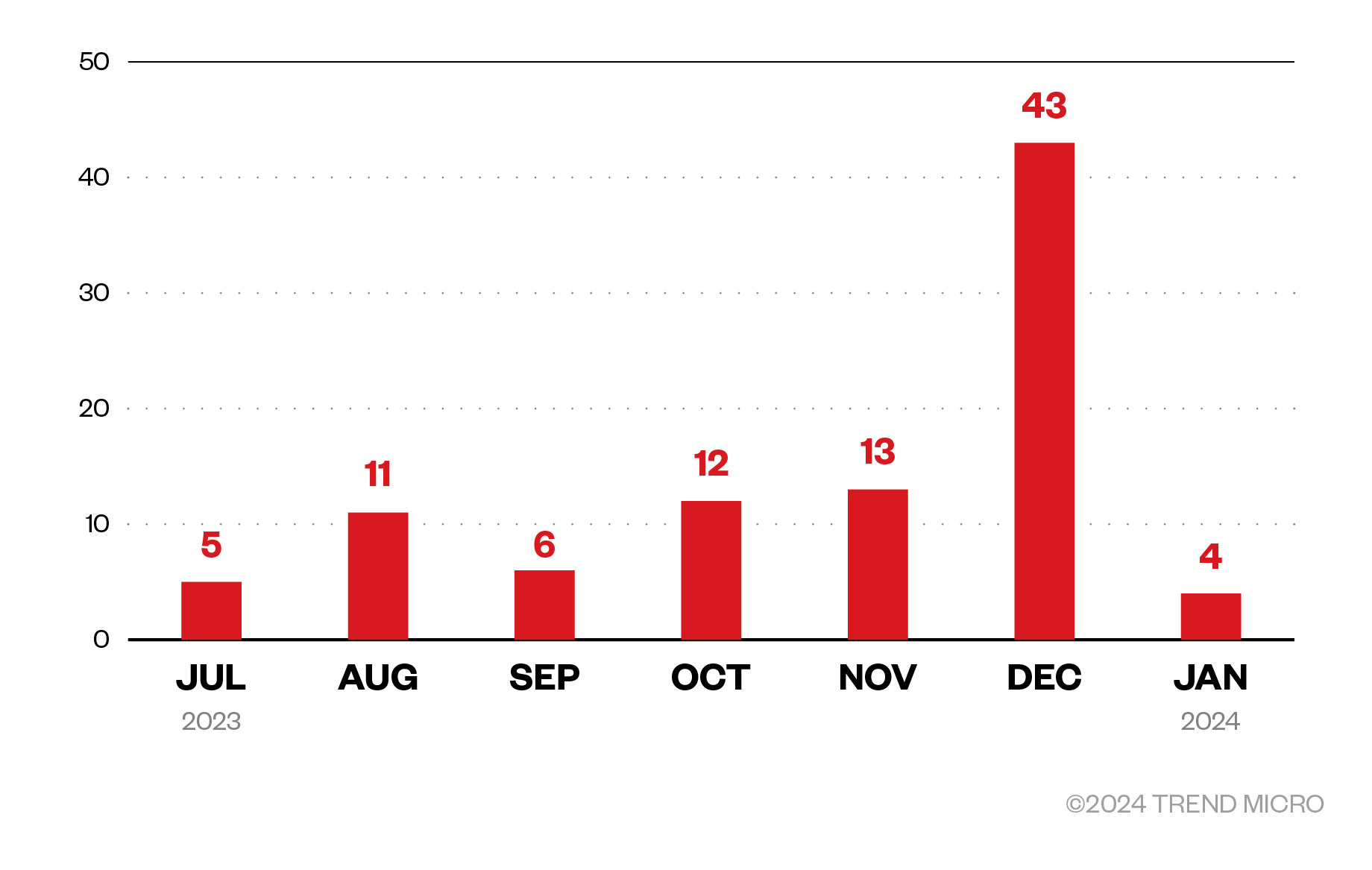
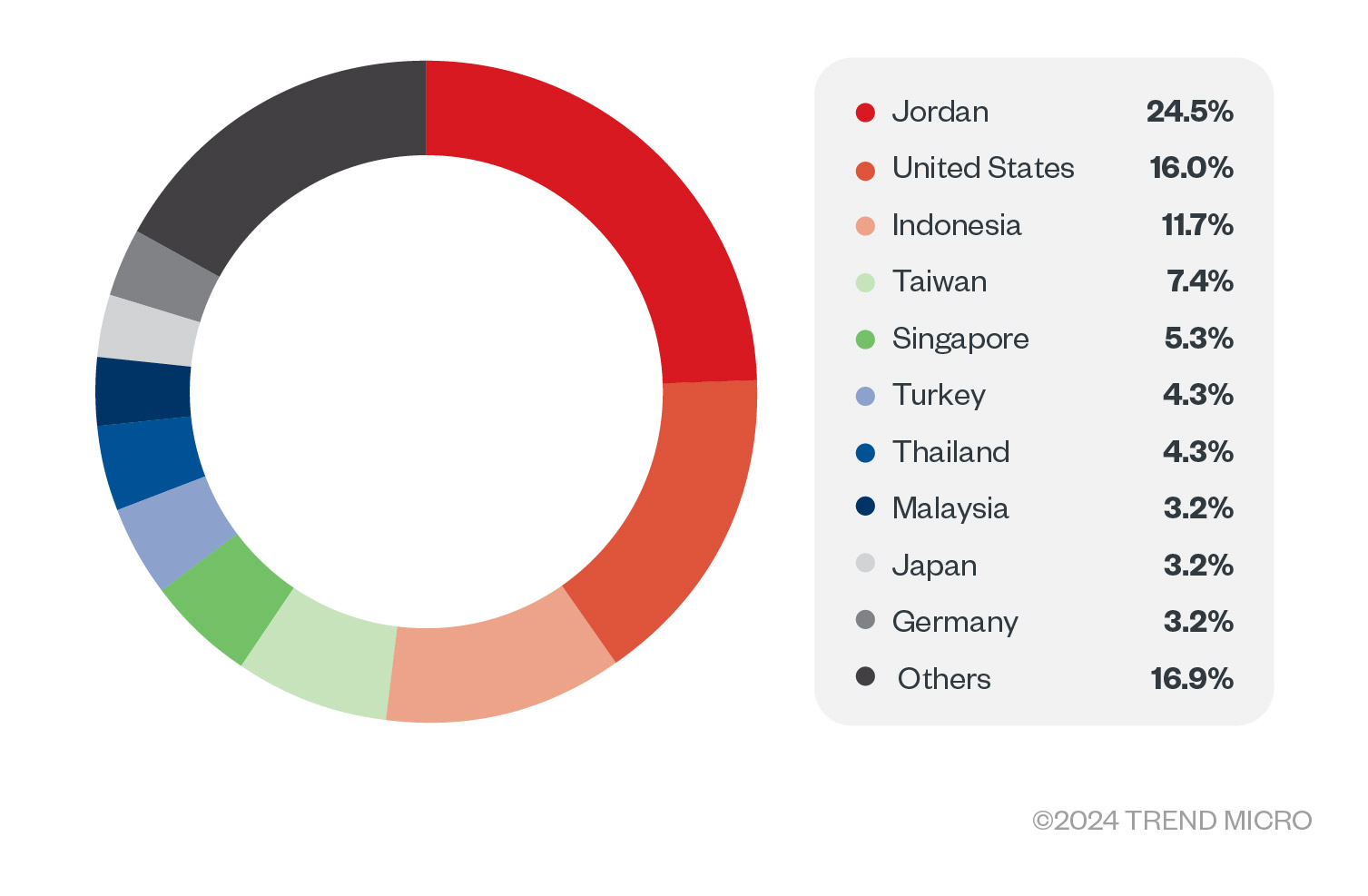
This section discusses Trend Micro™ Smart Protection Network™ data on Rhysida’s attempts to compromise organizations. Although Rhysida activity was first spotted in May 2023, these detections were collected from January 2023 to January 2024 and pertain only to Trend customers. In this period, Rhysida attack attempts climbed steadily, peaking in December 2023 before a steep decline the following month.
Jordan topped the list of Rhysida attack detections at 24.5%, with the United States and Indonesia following at 16% and 11.7%, respectively. Taiwan and Singapore rounded up the top five countries targeted by Rhysida over this period of activity.
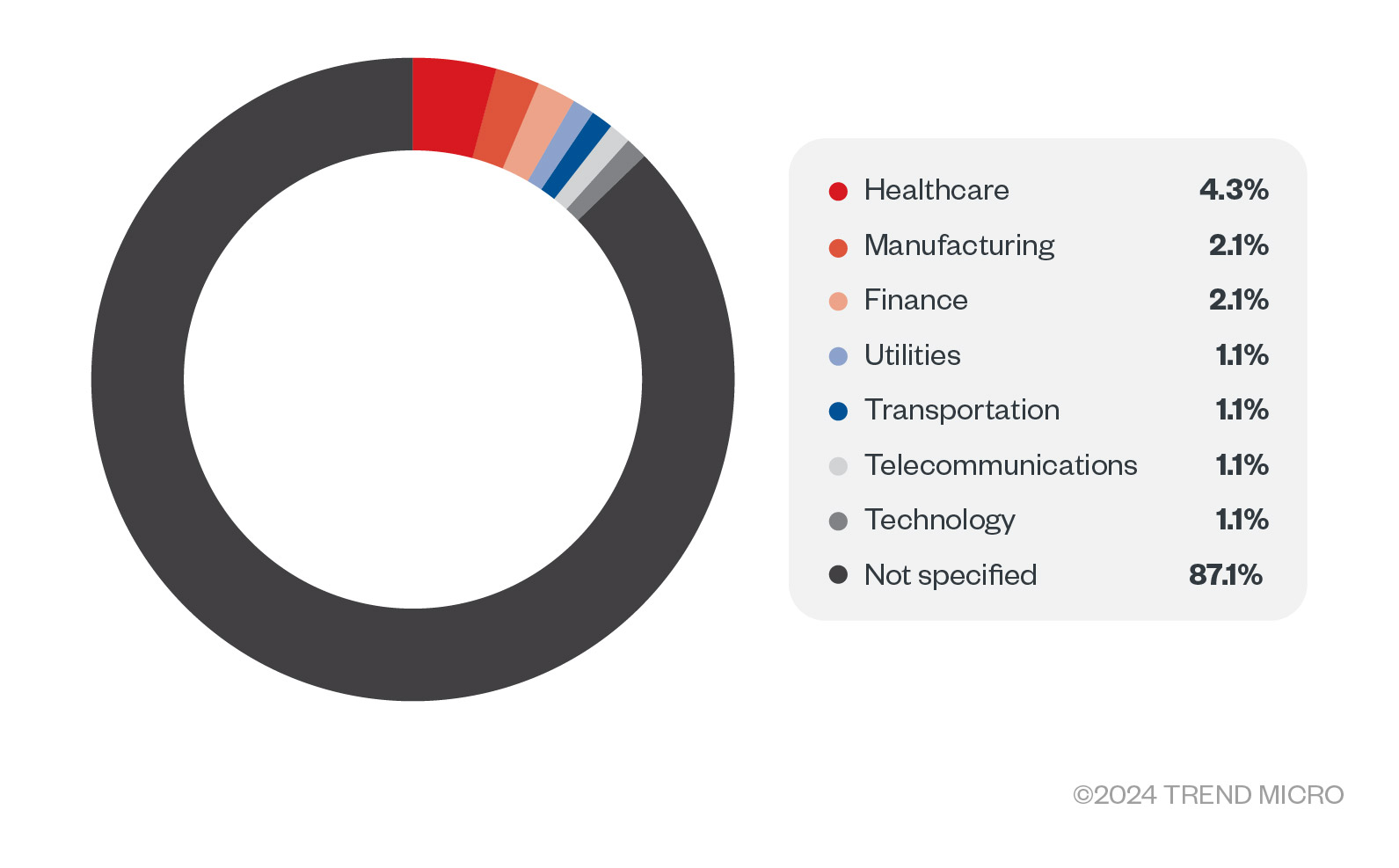
Based on feedback from Trend customers who specified their industries, the cybercriminals behind the Rhysida ransomware set their sights on many healthcare organizations, with these attack attempts composing 4.8% of total detections. Rhysida also targeted enterprises in the manufacturing and finance industries.
Targeted regions and industries according to Rhysida’s leak site
This section examines data observed on the Rhysida ransomware's leak site from June 7, 2023 to Jan. 13, 2024. Based on Trend’s open-source intelligence (OSINT) research and our investigation of the leak site within this period, the Rhysida ransomware compromised a total of 71 organizations that refused to pay the ransom demand as of this writing.
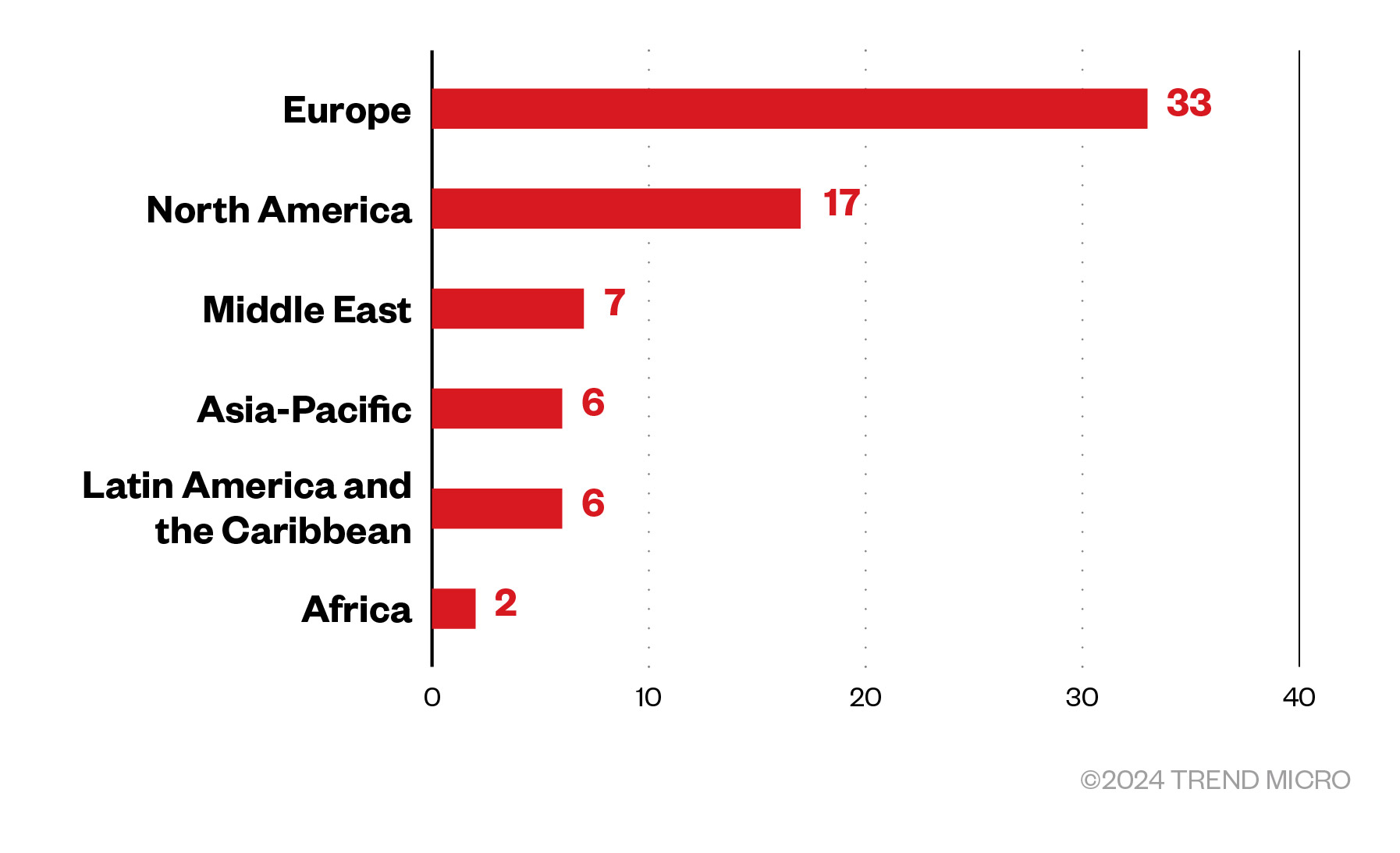
European organizations made up the lion's share of victims identified in Rhysida’s leak site at 46.5%, followed by 23.9% of organizations that were operating from North America. Those in the Middle East were also at the receiving end of Rhysida attacks at 9.9%.
Figure 4. The distribution by region of Rhysida ransomware’s victim organizations (June 7, 2023 – Jan. 13, 2024)
Sources: Rhysida ransomware’s leak site and Trend’s OSINT research
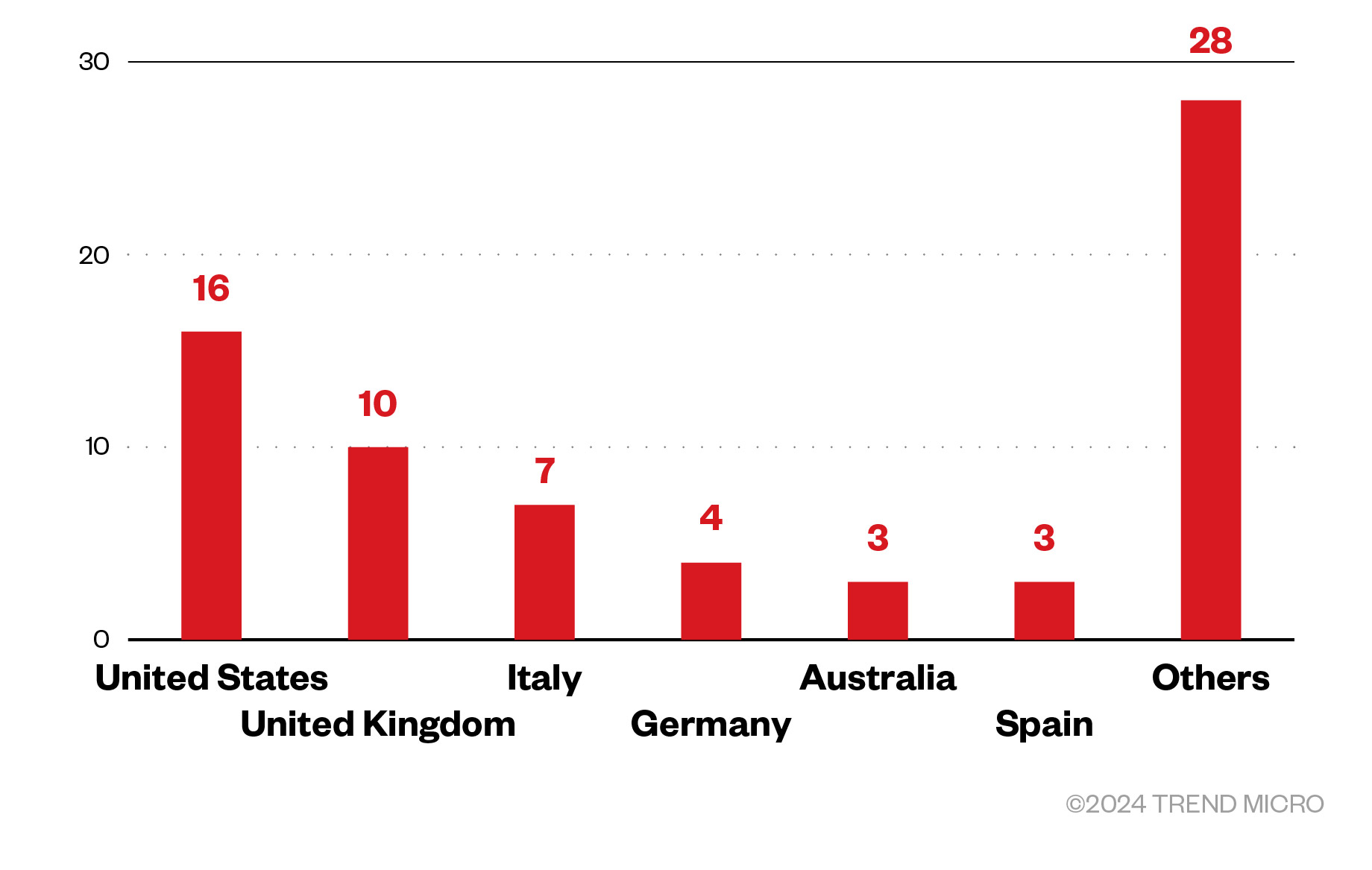
However, the United States topped the list of countries targeted by Rhysida attacks, composing 22.5% of the victim organizations. Those from the United Kingdom accounted for 14.1% of Rhysida victims, while organizations based in Italy made up 9.9%.
Figure 5. The distribution by country of Rhysida ransomware’s victim organizations (June 7, 2023 – Jan. 13, 2024)
Sources: Rhysida ransomware’s leak site and Trend’s OSINT research
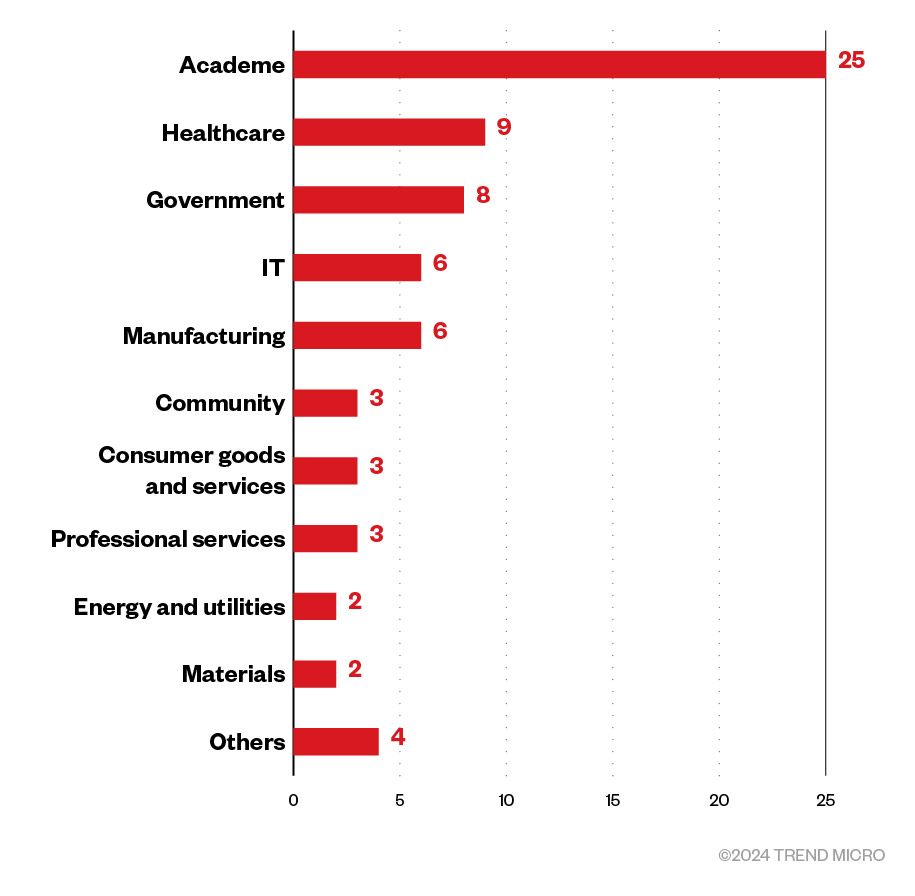
According to the leak site data, the academe was the most heavily targeted industry by Rhysida ransomware attacks at 35.2%. Healthcare organizations and the government sector were also affected, at 12.7% and 11.3%, respectively.
Figure 6. The distribution by industry of Rhysida ransomware’s victim organizations (June 7, 2023 – Jan. 13, 2024)
Sources: Rhysida ransomware’s leak site and Trend’s OSINT research
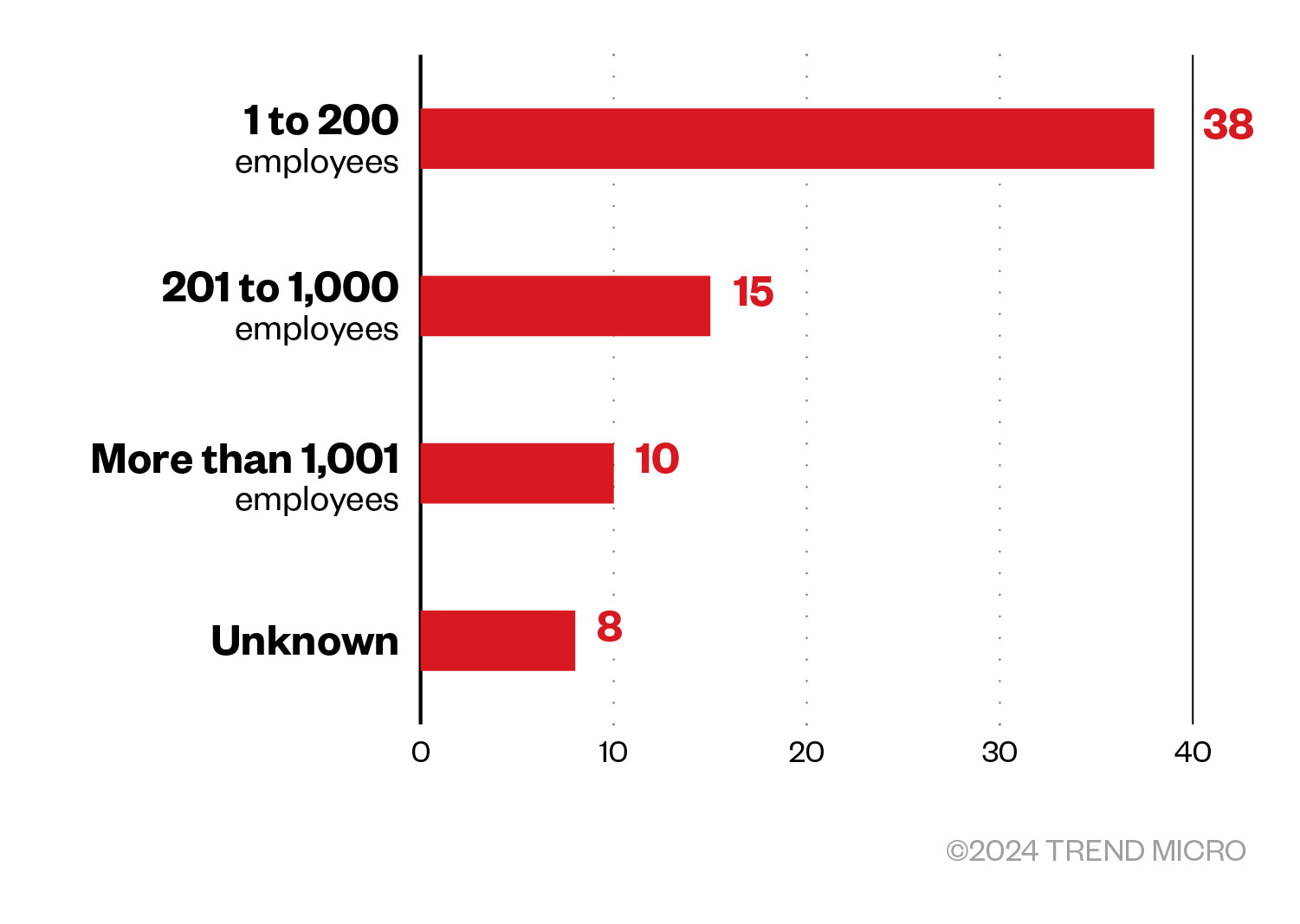
Rhysida focused primarily on small-sized businesses that had one to 200 employees and which composed more than half of the targeted organizations at 53.5%. Mid-sized businesses were a distant second at 21.1%, with enterprises trailing behind at 14.1%.
Figure 7. The distribution by organization size of Rhysida ransomware’s victim organizations (June 7, 2023 – Jan. 13, 2024)
Sources: Rhysida ransomware’s leak site and Trend’s OSINT research
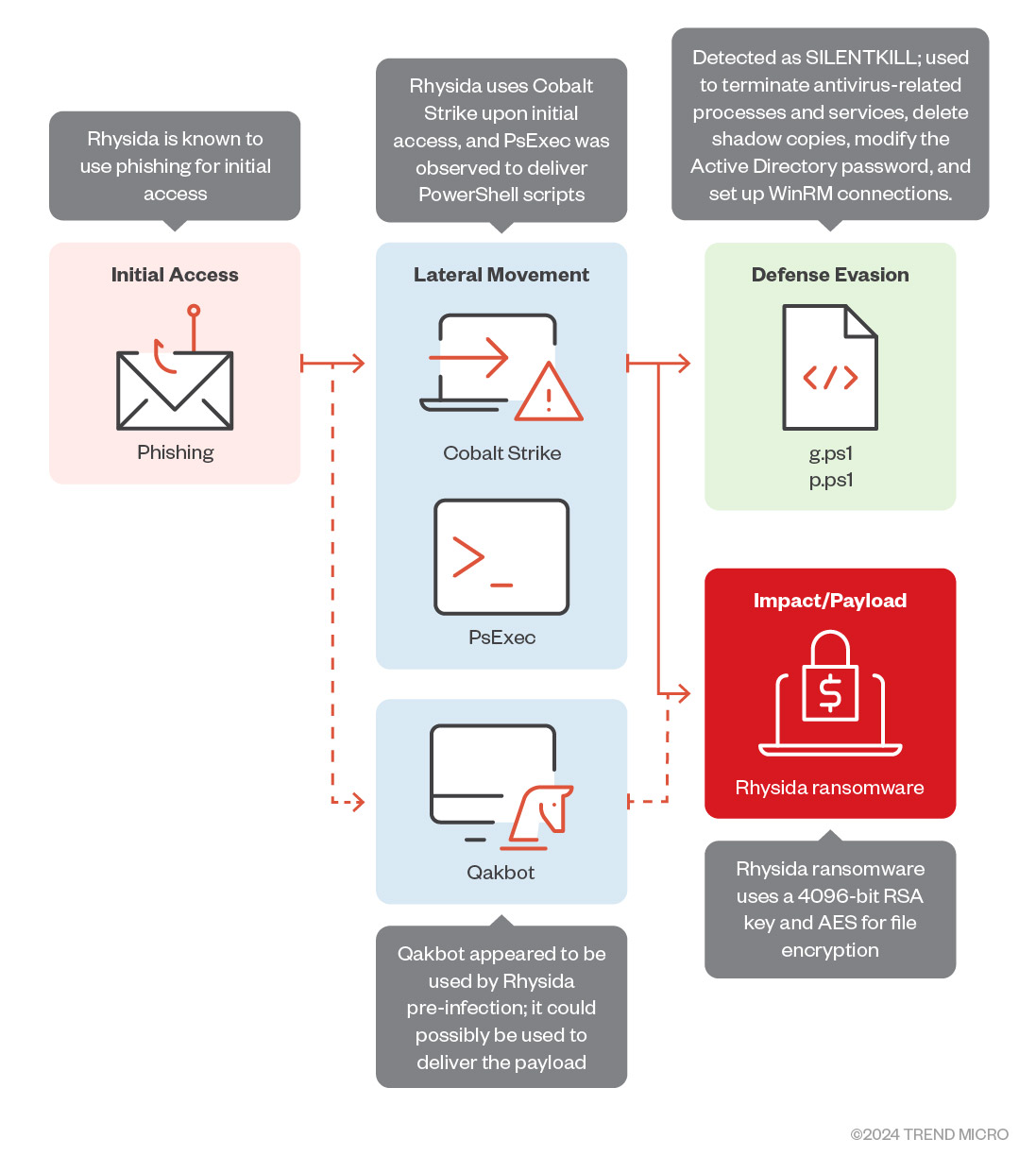
Initial Access
- Rhysida’s threat actors allegedly use phishing for initial access.
Defense Evasion, Discovery
- The Rhysida ransomware drops PowerShell scripts (detected as SILENTKILL) to terminate antivirus-related processes and services, delete shadow copies, and modify Active Directory passwords. These scripts are also used to set up WinRM connections.
Lateral Movement
- Rhysida operators use Cobalt Strike beacons upon initial access. Additionally, they have been observed using PsExec to deploy the PowerShell scripts and the ransomware binary.
Impact
- The Rhysida ransomware uses a 4096-bit RSA key and AES for file encryption.
Other technical details
- Rhysida’s binaries accept the following command-line arguments:
- -d {path to encrypt} – Used to specify directory to encrypt
- -sr – Used to delete itself after encryption
- nobg – Used to disable modification of desktop wallpaper after encryption
- -md5
- -S – Executes the following:
— Avoids ransomware routine
— Creates scheduled tasks named “Rhsd”
- The Rhysida ransomware contains a list of strings of files and directories to avoid.
The Windows version avoids encrypting directories with these strings in their file path:
- $Recycle.Bin
- Boot
- Documents and Settings
- PerfLogs
- ProgramData
- Recovery
- System Volume Information
- Windows
- $RECYCLE.BIN
- ApzData
The Linux version avoids encrypting directories with these strings in their file path:
- /boot
- /cdrom
- /dev
- /etc
- /lib
- /lib32
- /lib32
- /lib64
- /libx32
- /lost+found
- /media
- /opt
- /proc
- /run
- /sbin
- /sbin
- /snap
- /srv
- /sys
- /tmp
- /usr
The Linux version avoids encrypting this file:
- boot.cfg
- The Rhysida ransomware also contains a list of extensions of files to avoid.
The Windows version avoids encrypting files with the following extensions:
- .bat
- .bin
- .cab
- .cmd
- .com
- .cur
- .diagcab
- .diagcfg
- .diagpkg
- .drv
- .dll
- .exe
- .hlp
- .hta
- .ico
- .msi
- .ocx
- .ps1
- .psm1
- .scr
- .sys
- .ini
- Thumbs.db
- .url
- .iso
The Linux version avoids encrypting files with the following extensions:
- .sf
- .b00
- .v00
- .v01
- .v02
- .v03
- .v04
- .v05
- .v06
- .v07
- .t00
- .tgz
- .z
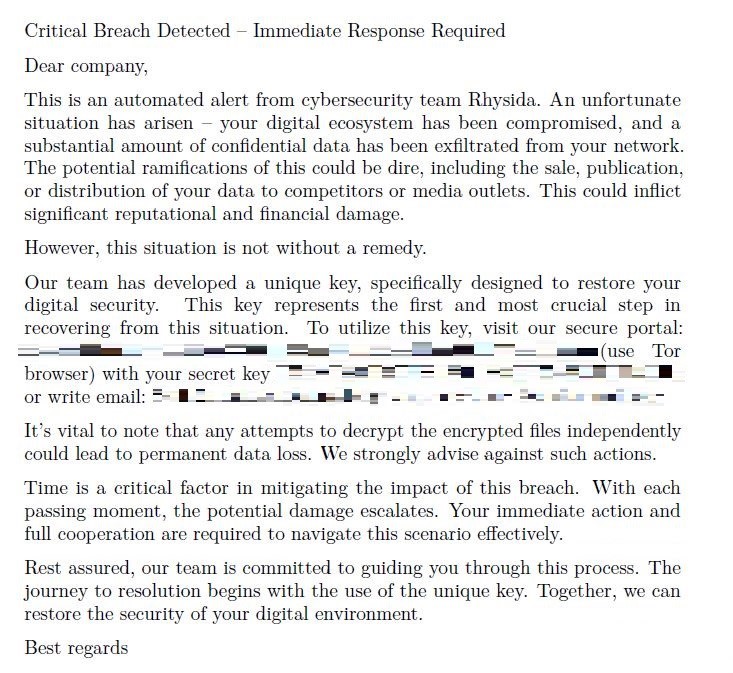
- The Rhysida ransomware drops a ransom note:
Figure 9. Rhysida ransomware’s ransom note
- Encryption method: The ransomware uses a 4096-bit RSA key and AES for file encryption.
MITRE tactics and techniques
| Persistence | Defense Evasion | Discovery | Impact |
|---|---|---|---|
T1053.005 - Scheduled Task/Job: Scheduled Task | T1070.004 - Indicator Removal: File Deletion T1222.002 - File and Directory Permissions Modification: It uses chmod to modify permissions of files it modifies to display the ransom note. | T1083 - File and Directory Discovery T1082 - System Information Discovery | T1486 - Data Encrypted for Impact T1490 - Inhibit System Recovery T1491.001 - Internal Defacement |
Trend Micro Vision One hunting query
Trend Vision One customers can use the following hunting query to search for Rhysida ransomware within their system:
processCmd:"powershell.exe*\\*$\?.ps1" OR (objectFilePath:"?:*\\??\\psexec.exe" AND
processCmd:"*cmd.exe*\\??\\??.bat")
Summary of malware, tools, and exploits used
| Initial Access | Lateral Movement | Defense Evasion | Impact |
|---|---|---|---|
|
|
|
|
| |||
|
Security recommendations
Although the Rhysida ransomware has kept a low profile so far, its ties to other ransomware groups and the ruse with which it lures in victims only stress the importance of staying vigilant in the face of insidious cyberattacks. The evolution of ransomware threats like Rhysida is a clarion call for organizations to bolster their security posture and develop a solid defense strategy. We list security best practices that businesses can adopt to better protect themselves and their data from the risk of Rhysida ransomware infection here:
Audit and inventory
- Take an inventory of assets and data.
- Identify authorized and unauthorized devices and software.
- Make an audit of event and incident logs.
Configure and monitor
- Manage hardware and software configurations.
- Grant admin privileges and access only when necessary to an employee’s role.
- Monitor network ports, protocols, and services.
- Activate security configurations on network infrastructure devices such as firewalls and routers.
- Establish a software allowlist that executes only legitimate applications.
Patch and update
- Conduct regular vulnerability assessments.
- Perform patching or virtual patching for operating systems and applications.
- Update software and applications to their latest versions.
Protect and recover
- Implement data protection, backup, and recovery measures.
- Enable multifactor authentication (MFA).
Secure and defend
- Employ sandbox analysis to block malicious emails.
- Deploy the latest versions of security solutions to all layers of the system, including email, endpoint, web, and network.
- Detect early signs of an attack such as the presence of suspicious tools in the system.
- Use advanced detection technologies such as those powered by artificial intelligence (AI) and machine learning (ML).
Train and test
- Regularly train and assess employees in security skills.
- Conduct red-team exercises and penetration tests.
- A multilayered approach can help organizations guard possible entry points into the system (endpoint, email, web, and network). Security solutions that can detect malicious components and suspicious behavior can also help protect enterprises.
A multilayered approach can help organizations guard possible entry points into the system (endpoint, email, web, and network). Security solutions that can detect malicious components and suspicious behavior can also help protect enterprises.
- Trend Vision One™ provides multilayered protection and behavior detection, which helps block questionable behavior and tools early on before ransomware can do irreversible damage to the system.
- Trend Micro Cloud One™ – Workload Security protects systems against both known and unknown threats that exploit vulnerabilities. This protection is made possible through techniques such as virtual patching and machine learning.
- Trend Micro™ Deep Discovery™ Email Inspector employs custom sandboxing and advanced analysis techniques to effectively block malicious emails, including phishing emails that can serve as entry points for ransomware.
- Trend Micro Apex One™ offers next-level automated threat detection and response against advanced concerns such as fileless threats and ransomware, ensuring the protection of endpoints.
Indicators of compromise (IOCs)
The IOCs for the threat discussed in this article can be found here. Actual indicators might vary per attack.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter


 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation