Back to School: A Crash Course on Cybersecurity
 View Infographic: Back to School: A Crash Course on Cybersecurity
View Infographic: Back to School: A Crash Course on Cybersecurity
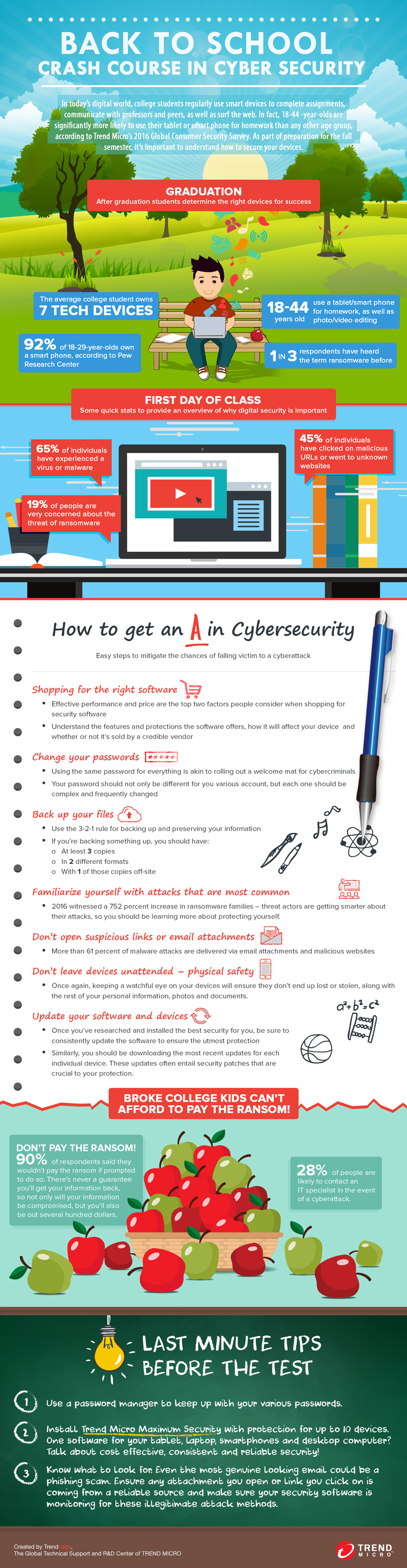
A previous consumer survey by Trend Micro found that an average college student owns seven tech devices ranging from personal computers and laptops to tablets, smartphones and IoT gadgets. But for an age group that’s known for being tech-savvy, most aren’t paying much attention to securing their privacy and personal information.
College lifestyle, too, tends to expose students to threats. Even a seemingly innocuous bit of personal data you give when filing for classes, handing over schoolwork, or setting up your online college account can be used as doorways to infect your devices with malware.
Your smartphone is more valuable than you might think—it can be a cybercriminal goldmine of contacts, messages, credentials, financial and personal data, browsing history, and more. Personally identifiable information and credentials pulled from it can be sold in cybercriminal underground marketplaces, used to fake your identity, or rack up fraudulent purchases in your name.
The same survey revealed that 65% of surveyed individuals have experienced getting their devices infected with malware, while a further 45% have clicked on malicious URLs or visited unknown/suspicious websites in the past. Indeed, while the rest will see young adults preparing for the next semester and college campus-bound, cybercriminals see them as fresh meat.
What can incoming students do to improve their cybersecurity?
Cover your bases and adopt best practices. Ransomware is as widespread as ever, and has, in fact, affected a number of colleges and universities worldwide. So practice security hygiene: regularly back up your files and keep your devices patched and updated. Social media scams abound; strengthen your passwords, and be more prudent when handling unknown or unsolicited emails or text messages. And of course, ensure the physical safety of your devices. Investing in security solutions that can seamlessly manage your data while protecting them from malware can also help.
Like it? Add this infographic to your site:
1. Click on the box below. 2. Press Ctrl+A to select all. 3. Press Ctrl+C to copy. 4. Paste the code into your page (Ctrl+V).
Image will appear the same size as you see above.
Recent Posts
- TrendAI™ and CleanDNS: From Blocking Attacker Infrastructure to Removing It From the Internet
- A Hidden Vulnerability in Healthcare: Exposed DICOM Servers and the Risk to Patient Data
- Update on Exposed MCP Servers: The Threat Widens to the Cloud
- From Stealers to Systems: The New Model of Credential Theft
- Edge Under Siege: How State-Sponsored Actors Exploit Your Perimeter

 Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report
Fault Lines in the AI Ecosystem: TrendAI™ State of AI Security Report It’s By Design: The Use-After-Free of Azure Cloud
It’s By Design: The Use-After-Free of Azure Cloud Ransomware Spotlight: Agenda
Ransomware Spotlight: Agenda Guarding LLMs With a Layered Prompt Injection Representation
Guarding LLMs With a Layered Prompt Injection Representation