Ransom.Win32.JEST.A
Gen:Heur.Ransom.Imps.1 (BITDEFENDER); Trojan:Win32/Dynamer!rfn (MICROSOFT)
Windows

Tipo di minaccia informatica:
Ransomware
Distruttivo?:
No
Crittografato?:
Sì
In the wild::
Sì
Panoramica e descrizione
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Dettagli tecnici
Detalles de entrada
It arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Instalación
Infiltra los archivos siguientes:
- %All Users Profile%\chk.dat
- %All Users Profile%\MSWINSCK.OCX
- %All Users Profile%\encryptedfiles.eco --> list of encrypted files
- %Windows%\Logs\WindowsBackup\Wbadmin.0.etl
- %Public%\Desktop\README - Decryption Note.lnk
- %Public%\Desktop\Decryptor.lnk
- %All Users Profile%\note.ini --> Ransomnote
- %All Users Profile%\1.bmp
- %Windows%\Web\Wallpaper\Windows\img0.jpg
- %User Temp%\MpCmdRun.log
(Nota: %Windows% es la carpeta de Windows, que suele estar en C:\Windows o C:\WINNT).
. %User Temp% es la carpeta Temp del usuario activo, que en el caso de Windows 2000(32-bit), XP y Server 2003(32-bit) suele estar en C:\Documents and Settings\{nombre de usuario}\Local Settings\Temp y en el case de Windows Vista, 7, 8, 8.1, 2008(64-bit), 2012(64-bit) y 10(64-bit) en C:\Users\{nombre de usuario}\AppData\Local\Temp).)Infiltra y ejecuta los archivos siguientes:
- %All Users Profile%\{Malware name}.exe
- %All Users Profile%\x86.exe --> deleted after, (drops %All Users Profile%\x64.exe if executed on a 64-bit machine)
- %All Users Profile%\recover.exe --> deleted after, copy of itself
- %All Users Profile%\rps.exe --> deleted after, used for propagation through SMB bruteforce attacks.
Agrega los procesos siguientes:
- "%System%\vssadmin.exe" delete shadows /all /quiet
- "%System%\wbem\WMIC.exe" shadowcopy delete
- "%System%\wbadmin.exe" delete catalog -quiet
- "%System%\bcdedit.exe" /set {default} bootstatuspolicy ignoreallfailures
- "%System%\bcdedit.exe" /set {default} recoveryenabled no
- "%System%\icacls.exe" %Windows%\Web\Wallpaper\Windows\img0.jpg /grant Users:F
- "%System%\WindowsPowerShell\v1.0\powershell.exe" -Enc {Base 64 code} -ExecutionPolicy Bypass -W Hidden -NonI --> for deleting system logs
- "%Program Files%\Windows Defender\mpcmdrun.exe" -removedefinitions -all --> for removing Windows Defender Signatures
- %All Users Profile%\x86.exe go::inc get::pwz token::getsys read::samz exit --> for executing mimikatz instance
- "%System%\cmd.exe" /c logoff{0-80}
(Nota: %System% es la carpeta del sistema de Windows, que en el caso de Windows 98 y ME suele estar en C:\Windows\System, en el caso de Windows NT y 2000 en C:\WINNT\System32 y en el caso de Windows 2000(32-bit), XP, Server 2003(32-bit), Vista, 7, 8, 8.1, 2008(64-bit), 2012(64bit) y 10(64-bit) en C:\Windows\System32).
. %Windows% es la carpeta de Windows, que suele estar en C:\Windows o C:\WINNT).. %Program Files% es la carpeta Archivos de programa predeterminada, que suele estar en C:\Archivos de programa).)Técnica de inicio automático
Agrega las siguientes entradas de registro para permitir su ejecución automática cada vez que se inicia el sistema:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\Run
BWGBXD = "%All Users Profile%\{Malware name}.exe" -ui
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Run
BWGBXD = "%All Users Profile%\{Malware name}.exe" -ui
Otras modificaciones del sistema
Agrega las siguientes entradas de registro:
HKEY_LOCAL_MACHINE\BCD00000000\Objects\
{GUID}\Elements\250000e0
Element = 01 00 00 00 00 00 00 00
HKEY_LOCAL_MACHINE\BCD00000000\Objects\
{GUID}\Elements\16000009
Element = 00
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
ThreadingModel = Apartment
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
"" = %All Users Profile%\MSWINSCK.OCX
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
"" = Microsoft WinSock Control, version 6.0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock
"" = Microsoft WinSock Control, version 6.0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock\CLSID
"" = {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock\CurVer
"" = MSWinsock.Winsock.1
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock.1
"" = Microsoft WinSock Control, version 6.0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock.1\CLSID
"" = {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\VersionIndependentProgID
"" = MSWinsock.Winsock
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\ProgID
"" = MSWinsock.Winsock.1
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
"" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Version
"" = 1.0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\MiscStatus
"" = 0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\MiscStatus\
1
"" = 132497
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\ToolboxBitmap32
"" = %All Users Profile%\MSWINSCK.OCX, 1
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD897-BB45-11CF-9ABC-0080C7E7B78D}
"" = Winsock General Property Page Object
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD897-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
"" = %All Users Profile%\MSWINSCK.OCX
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0
"" = Microsoft Winsock Control 6.0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\
FLAGS
"" = 2
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\
0\win32
"" = %All Users Profile%\MSWINSCK.OCX
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\
HELPDIR
"" = IMSWinsockControl
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid
"" = {00020424-0000-0000-C000-000000000046}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid32
"" = {00020424-0000-0000-C000-000000000046}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
"" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
Version = 1.0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}
"" = DMSWinsockControlEvents
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid
"" = {00020420-0000-0000-C000-000000000046}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid32
"" = {00020420-0000-0000-C000-000000000046}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
"" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
Version = 1
HKEY_CURRENT_USER\Control Panel\Desktop
TileWallpaper = 0
HKEY_CURRENT_USER\Control Panel\Desktop
WallpaperStyle = 10
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = %All Users Profile%\1.bmp
HKEY_CURRENT_USER\Control Panel\Desktop
OriginalWallpaper = %All Users Profile%\1.bmp
HKEY_CURRENT_USER\Control Panel\Desktop
ConvertedWallpaper = %All Users Profile%\1.bmp
Otros detalles
Agrega las siguientes entradas de registro como parte de la rutina de instalación:
HKEY_LOCAL_MACHINE\BCD00000000\Objects\
{GUID}\Elements\250000e0
HKEY_LOCAL_MACHINE\BCD00000000\Objects\
{GUID}\Elements\16000009
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock\CLSID
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock\CurVer
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock.1
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
MSWinsock.Winsock.1\CLSID
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\VersionIndependentProgID
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\ProgID
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Version
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories\
{40FC6ED5-2438-11CF-A3DB-080036F12502}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Programmable
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Control
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\MiscStatus
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\MiscStatus\
1
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\ToolboxBitmap32
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories\
{40FC6ED4-2438-11CF-A3DB-080036F12502}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories\
{0DE86A57-2BAA-11CF-A229-00AA003D7352}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories\
{0DE86A53-2BAA-11CF-A229-00AA003D7352}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories\
{0DE86A52-2BAA-11CF-A229-00AA003D7352}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD897-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
CLSID\{248DD897-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\
FLAGS
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\
0
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\
0\win32
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\
HELPDIR
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid32
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid32
HKEY_LOCAL_MACHINE\SOFTWARE\Classes\
Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
Cifra los archivos con las extensiones siguientes:
- .3fr
- .ACCDB
- .ACCDE
- .ACCDR
- .ACCDT
- .ai
- .arw
- .asp
- .aspx
- .bac
- .kupdb
- .bak
- .bas
- .bay
- .cdr
- .cer
- .cfg
- .class
- .conf
- .config
- .cpp
- .cr2
- .crt
- .crw
- .cs
- .css
- .db
- .dbf
- .dcr
- .cder
- .dng
- .doc
- .docb
- .docm
- .docx
- .dot
- .dotm
- .dotx
- .dwg
- .dxf
- .dxg
- .edb
- .eps
- .erf
- .flt
- .htm
- .html
- .indd
- .java
- .jpe
- .jpeg
- .jpg
- .kdc
- .log
- .mdb
- .mdf
- .mef
- .mrw
- .ned
- .nef
- .nrp
- .nrw
- .ntm
- .odb
- .odb
- .odp
- .ods
- .odt
- .orf
- .ost
- .ov
- .p12
- .p7b
- .p7c
- .pdd
- .pef
- .pem
- .pfx
- .php
- .png
- .pot
- .potm
- .potx
- .ppam
- .pps
- .ppsm
- .ppsx
- .ppt
- .pptm
- .proj
- .psd
- .pst
- .py
- .pyc
- .r3d
- .rar
- .raw
- .rtf
- .rw2
- .rwl
- .sld
- .sldx
- .sln
- .sql
- .srf
- .srw
- .txt
- .vb
- .v,dk
- .vmx
- .wb2
- .wpd
- .wps
- .xla
- .xlam
- .xlk
- .xll
- .xlm
- .xls
- .xlsb
- .xlsm
- .xlsx
- .xlt
- .xltm
- .xltx
- .xlw
- .xml
- .zip
Hace lo siguiente:
- It encrypts files in all fixed and removable drives.
- It is capable of propagating in the local network via the following means:
- SMB Bruteforcing
- Dumping Windows Domain Credentials using any of the following techniques/tools:
- Mimikatz
- It executes the following commands to terminate processes:
- "%System%\taskkill.exe" /F /IM MSExchange*
- "%System%\taskkill.exe" /F /IM Microsoft.Exchange.*
- "%System%\taskkill.exe" /F /IM vmware*.exe
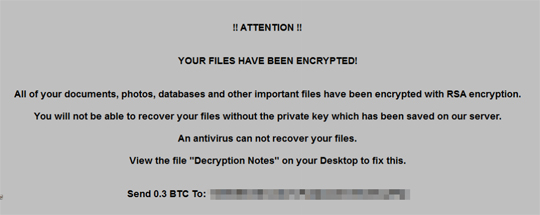
- It restarts the machine after execution and displays a GUI after startup:
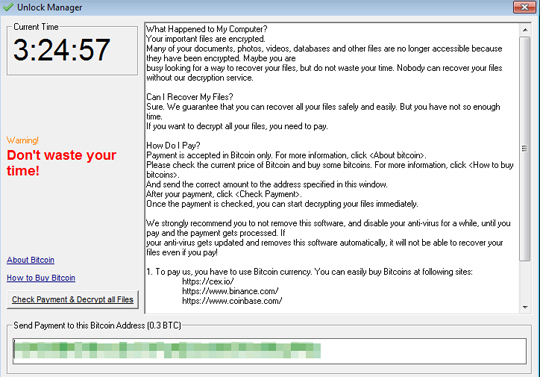
- It changes the desktop background:
Soluzioni
Step 1
Los usuarios de Windows ME y XP, antes de llevar a cabo cualquier exploración, deben comprobar que tienen desactivada la opción Restaurar sistema para permitir la exploración completa del equipo.
Step 2
Identificar y terminar los archivos detectados como Ransom.Win32.JEST.A
- Para los usuarios de Windows 98 y ME, puede que el Administrador de tareas de Windows no muestre todos los procesos en ejecución. En tal caso, utilice un visor de procesos de una tercera parte (preferiblemente, el Explorador de procesos) para terminar el archivo de malware/grayware/spyware. Puede descargar la herramienta en cuestión aquí.
- Si el archivo detectado aparece en el Administrador de tareas o en el Explorador de procesos, pero no puede eliminarlo, reinicie el equipo en modo seguro. Para ello, consulte este enlace para obtener todos los pasos necesarios.
- Si el archivo detectado no se muestra en el Administrador de tareas o el Explorador de procesos, prosiga con los pasos que se indican a continuación.
Step 3
Reiniciar en modo seguro
Step 4
Eliminar esta clave del Registro
Importante: si modifica el Registro de Windows incorrectamente, podría hacer que el sistema funcione mal de manera irreversible. Lleve a cabo este paso solo si sabe cómo hacerlo o si puede contar con ayuda de su administrador del sistema. De lo contrario, lea este artículo de Microsoft antes de modificar el Registro del equipo.
- In HKEY_LOCAL_MACHINE\BCD00000000\Objects\{GUID}\Elements
- 250000e0
- 250000e0
- In HKEY_LOCAL_MACHINE\BCD00000000\Objects\{GUID}\Elements
- 16000009
- 16000009
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID
- {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- InprocServer32
- InprocServer32
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes
- MSWinsock.Winsock
- MSWinsock.Winsock
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock
- CLSID
- CLSID
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock
- CurVer
- CurVer
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes
- MSWinsock.Winsock.1
- MSWinsock.Winsock.1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock.1
- CLSID
- CLSID
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- VersionIndependentProgID
- VersionIndependentProgID
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- ProgID
- ProgID
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- TypeLib
- TypeLib
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- Version
- Version
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- Implemented Categories
- Implemented Categories
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories
- {40FC6ED5-2438-11CF-A3DB-080036F12502}
- {40FC6ED5-2438-11CF-A3DB-080036F12502}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- Programmable
- Programmable
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- Control
- Control
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- MiscStatus
- MiscStatus
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\MiscStatus
- 1
- 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- ToolboxBitmap32
- ToolboxBitmap32
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories
- {40FC6ED4-2438-11CF-A3DB-080036F12502}
- {40FC6ED4-2438-11CF-A3DB-080036F12502}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories
- {0DE86A57-2BAA-11CF-A229-00AA003D7352}
- {0DE86A57-2BAA-11CF-A229-00AA003D7352}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories
- {0DE86A53-2BAA-11CF-A229-00AA003D7352}
- {0DE86A53-2BAA-11CF-A229-00AA003D7352}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Implemented Categories
- {0DE86A52-2BAA-11CF-A229-00AA003D7352}
- {0DE86A52-2BAA-11CF-A229-00AA003D7352}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID
- {248DD897-BB45-11CF-9ABC-0080C7E7B78D}
- {248DD897-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD897-BB45-11CF-9ABC-0080C7E7B78D}
- InprocServer32
- InprocServer32
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib
- {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- 1.0
- 1.0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0
- FLAGS
- FLAGS
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0
- 0
- 0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\0
- win32
- win32
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0
- HELPDIR
- HELPDIR
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface
- {248DD892-BB45-11CF-9ABC-0080C7E7B78D}
- {248DD892-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}
- ProxyStubClsid
- ProxyStubClsid
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}
- ProxyStubClsid32
- ProxyStubClsid32
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}
- TypeLib
- TypeLib
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}
- ProxyStubClsid
- ProxyStubClsid
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}
- ProxyStubClsid32
- ProxyStubClsid32
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}
- TypeLib
- TypeLib
Step 5
Eliminar este valor del Registro
Importante: si modifica el Registro de Windows incorrectamente, podría hacer que el sistema funcione mal de manera irreversible. Lleve a cabo este paso solo si sabe cómo hacerlo o si puede contar con ayuda de su administrador del sistema. De lo contrario, lea este artículo de Microsoft antes de modificar el Registro del equipo.
- In HKEY_LOCAL_MACHINE\BCD00000000\Objects\{GUID}\Elements\250000e0
- Element = 01 00 00 00 00 00 00 00
- Element = 01 00 00 00 00 00 00 00
- In HKEY_LOCAL_MACHINE\BCD00000000\Objects\{GUID}\Elements\16000009
- Element = 00
- Element = 00
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
- ThreadingModel = Apartment
- ThreadingModel = Apartment
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
- "" = %All Users Profile%\MSWINSCK.OCX
- "" = %All Users Profile%\MSWINSCK.OCX
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- "" = Microsoft WinSock Control, version 6.0
- "" = Microsoft WinSock Control, version 6.0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock
- "" = Microsoft WinSock Control, version 6.0
- "" = Microsoft WinSock Control, version 6.0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock\CLSID
- "" = {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- "" = {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock\CurVer
- "" = MSWinsock.Winsock.1
- "" = MSWinsock.Winsock.1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock.1
- "" = Microsoft WinSock Control, version 6.0
- "" = Microsoft WinSock Control, version 6.0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSWinsock.Winsock.1\CLSID
- "" = {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- "" = {248DD896-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\VersionIndependentProgID
- "" = MSWinsock.Winsock
- "" = MSWinsock.Winsock
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\ProgID
- "" = MSWinsock.Winsock.1
- "" = MSWinsock.Winsock.1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
- "" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- "" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\Version
- "" = 1.0
- "" = 1.0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\MiscStatus
- "" = 0
- "" = 0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\MiscStatus\1
- "" = 132497
- "" = 132497
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD896-BB45-11CF-9ABC-0080C7E7B78D}\ToolboxBitmap32
- "" = %All Users Profile%\MSWINSCK.OCX, 1
- "" = %All Users Profile%\MSWINSCK.OCX, 1
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD897-BB45-11CF-9ABC-0080C7E7B78D}
- "" = Winsock General Property Page Object
- "" = Winsock General Property Page Object
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{248DD897-BB45-11CF-9ABC-0080C7E7B78D}\InprocServer32
- "" = %All Users Profile%\MSWINSCK.OCX
- "" = %All Users Profile%\MSWINSCK.OCX
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0
- "" = Microsoft Winsock Control 6.0
- "" = Microsoft Winsock Control 6.0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\FLAGS
- "" = 2
- "" = 2
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\0\win32
- "" = %All Users Profile%\MSWINSCK.OCX
- "" = %All Users Profile%\MSWINSCK.OCX
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{248DD890-BB45-11CF-9ABC-0080C7E7B78D}\1.0\HELPDIR
- "" = IMSWinsockControl
- "" = IMSWinsockControl
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid
- "" = {00020424-0000-0000-C000-000000000046}
- "" = {00020424-0000-0000-C000-000000000046}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid32
- "" = {00020424-0000-0000-C000-000000000046}
- "" = {00020424-0000-0000-C000-000000000046}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
- "" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- "" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD892-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
- Version = 1.0
- Version = 1.0
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}
- "" = DMSWinsockControlEvents
- "" = DMSWinsockControlEvents
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid
- "" = {00020420-0000-0000-C000-000000000046}
- "" = {00020420-0000-0000-C000-000000000046}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\ProxyStubClsid32
- "" = {00020420-0000-0000-C000-000000000046}
- "" = {00020420-0000-0000-C000-000000000046}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
- "" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- "" = {248DD890-BB45-11CF-9ABC-0080C7E7B78D}
- In HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{248DD893-BB45-11CF-9ABC-0080C7E7B78D}\TypeLib
- Version = 1
- Version = 1
- In HKEY_CURRENT_USER\Control Panel\Desktop
- TileWallpaper = 0
- TileWallpaper = 0
- In HKEY_CURRENT_USER\Control Panel\Desktop
- WallpaperStyle = 10
- WallpaperStyle = 10
- In HKEY_CURRENT_USER\Control Panel\Desktop
- Wallpaper = %All Users Profile%\1.bmp
- Wallpaper = %All Users Profile%\1.bmp
- In HKEY_CURRENT_USER\Control Panel\Desktop
- OriginalWallpaper = %All Users Profile%\1.bmp
- OriginalWallpaper = %All Users Profile%\1.bmp
- In HKEY_CURRENT_USER\Control Panel\Desktop
- ConvertedWallpaper = %All Users Profile%\1.bmp
- ConvertedWallpaper = %All Users Profile%\1.bmp
- In HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- BWGBXD = "%All Users Profile%\{Malware name}.exe" -ui
- BWGBXD = "%All Users Profile%\{Malware name}.exe" -ui
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- BWGBXD = "%All Users Profile%\{Malware name}.exe" -ui
- BWGBXD = "%All Users Profile%\{Malware name}.exe" -ui
Step 6
Buscar y eliminar estos archivos
- %All Users Profile%\{Malware name}.exe
- %All Users Profile%\chk.dat
- %All Users Profile%\MSWINSCK.OCX
- %All Users Profile%\encryptedfiles.eco
- %Windows%\Logs\WindowsBackup\Wbadmin.0.etl
- %Public%\Desktop\README - Decryption Note.lnk
- %Public%\Desktop\Decryptor.lnk
- %All Users Profile%\note.ini
- %All Users Profile%\1.bmp
- %Windows%\Web\Wallpaper\Windows\img0.jpg
- %User Temp%\MpCmdRun.log
- %All Users Profile%\x86.exe
- %All Users Profile%\recover.exe
- %All Users Profile%\rps.exe
- %All Users Profile%\{Malware name}.exe
- %All Users Profile%\chk.dat
- %All Users Profile%\MSWINSCK.OCX
- %All Users Profile%\encryptedfiles.eco
- %Windows%\Logs\WindowsBackup\Wbadmin.0.etl
- %Public%\Desktop\README - Decryption Note.lnk
- %Public%\Desktop\Decryptor.lnk
- %All Users Profile%\note.ini
- %All Users Profile%\1.bmp
- %Windows%\Web\Wallpaper\Windows\img0.jpg
- %User Temp%\MpCmdRun.log
- %All Users Profile%\x86.exe
- %All Users Profile%\recover.exe
- %All Users Profile%\rps.exe
Step 7
Reinicie en modo normal y explore el equipo con su producto de Trend Micro para buscar los archivos identificados como Ransom.Win32.JEST.A En caso de que el producto de Trend Micro ya haya limpiado, eliminado o puesto en cuarentena los archivos detectados, no serán necesarios más pasos. Puede optar simplemente por eliminar los archivos en cuarentena. Consulte esta página de Base de conocimientos para obtener más información.
Step 8
Restore encrypted files from backup.
Sondaggio

