Spam
XTRAT and DUNIHI Backdoors Bundled with Adwind in Spam
We discovered a spam campaign that delivers the notorious cross-platform remote access Trojan (RAT) Adwind a.k.a. jRAT alongside another well-known backdoor called XTRAT a.k.a XtremeRAT. The spam campaign also delivered the info-stealer Loki.
Updated on April 22, 2018, 11:15 P.M. PDT to provide SHA-256 hashes instead of SHA-1 hashes.
We discovered a spam campaign that delivers the notorious cross-platform remote access Trojan (RAT) Adwind a.k.a. jRAT (detected by Trend Micro as JAVA_ADWIND.WIL) alongside another well-known backdoor called XTRAT a.k.a XtremeRAT (BKDR_XTRAT.SMM). The spam campaign also delivered the info-stealer Loki (TSPY_HPLOKI.SM1).
DUNIHI (VBS_DUNIHI.ELDSAVJ), a known VBScript with backdoor and worm capabilities, was also seen being dropped with Adwind via spam mail in a separate incident. Notably, cybercriminals behind the Adwind-XTRAT-Loki and Adwind-DUNIHI bundles abuse the legitimate free dynamic DNS server hopto[.]org. The delivery of different sets of backdoors is believed to be a ploy used to increase the chances of system infection: If one malware gets detected, the other malware could attempt to finish the job.
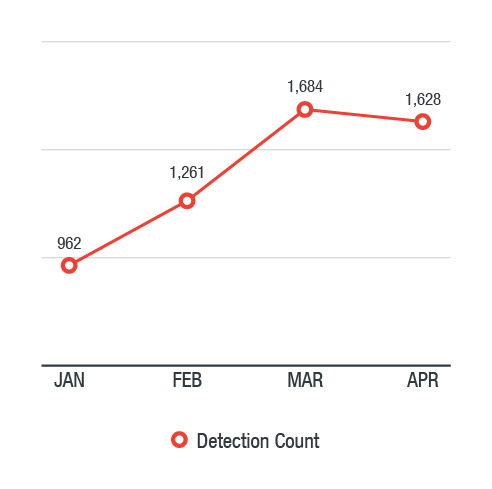
This year, we saw 5,535 unique detections of Adwind between January 1 and April 17. The U.S., Japan, Australia, Italy, Taiwan, Germany, and the U.K. were found to be the most affected regions.
Figure 1. Adwind detections between January 1 and April 17, 2018
Adwind, XTRAT, and Loki
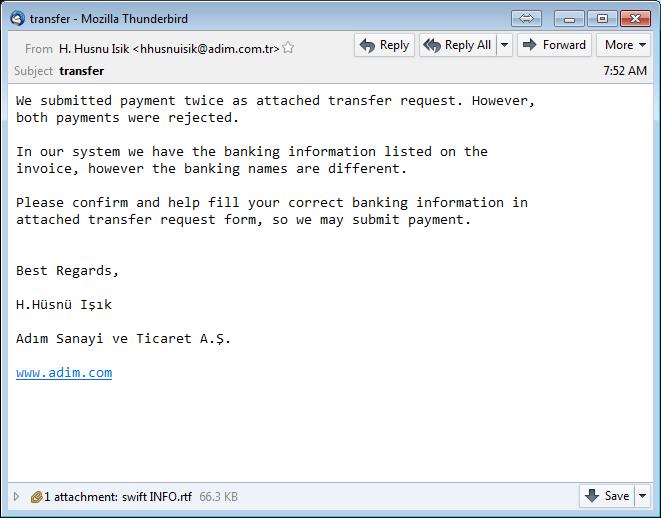
The exploited RTF document (TROJ_CVE201711882.UHAOBGG) seen below delivered the bundled set of Adwind, XTRAT, and Loki.
Figure 2. RTF document that carries Adwind, XTRAT, and Loki
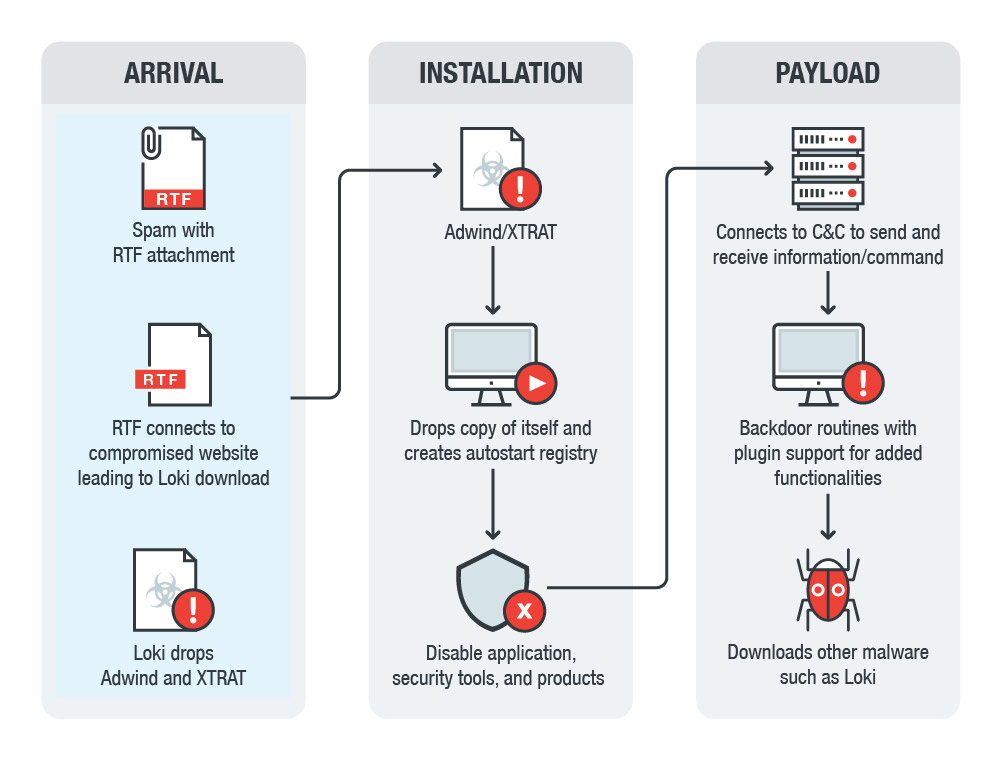
When the exploited RTF document is executed, it downloads Loki from a compromised website (hxxp://steamer10theatre[.]org/wp-admin/js/ehe[.]exe). Loki, a Trojan dropper, drops Adwind and XTRAT.
Figure 3. Infection chain of the spam that delivers Adwind, XTRAT, and Loki
The dropped files are effective RATs with multiple backdoor capabilities, anti-VM, anti-AV, and are highly configurable. Notably, Adwind and XTRAT connect to the same C&C server: junpio70[.]hopto[.]org. Adwind, which has been in the wild since 2013, can run on all major operating systems (Windows, Linux, MacOSX, Android) with Java and is known for its diverse backdoor capabilities such as (but not limited to):
- Information theft
- File and registry management
- Remote desktop
- Remote shell
- Process management
- Uploading, downloading, and executing files
XTRAT shares similar capabilities with Adwind, such as information theft, file and registry management, remote desktop, etc. It is also capable of the following:
- Screen capture desktop
- Recording via webcam or microphone
- Upload and download files
- Registry manipulation (read, write and manipulate)
- Process manipulation (execute and terminate)
- Service manipulation (stop, start, create and modify)
- Perform remote shell and control victim’s system
Like Adwind, it also uses an encrypted configuration file that contains C&C information. The information in this file includes the name of the dropped binary backdoor file, install directory of dropped backdoor file, name of injected process (where it would inject its code), autostart registry entries to use, malware ID, malware group name, malware version, malware mutex, and File Transfer Protocol (FTP) information (server, username, password) for the server to which it will send stolen keystroke data.
Adwind will download the malware Loki from another compromised website (hxxp://lauramoretongriffiths[.]com/wp-content/uploads/2013/09/ieei[.]exe). Last seen in December 2017, Loki was known as a password and cryptocurrency wallet stealer sold in hacking forums. Loki is also capable of harvesting data from FTP clients like Filezilla, web browsers such as Mozilla Firefox, Google Chrome and Safari, and email clients such as Microsoft Outlook and Mozilla Thunderbird. In addition, it steals from IT administration tools like PuTTY—a terminal emulator, system console, and network file transfer application. It also functions as a malware loader that is capable of recording keystrokes.
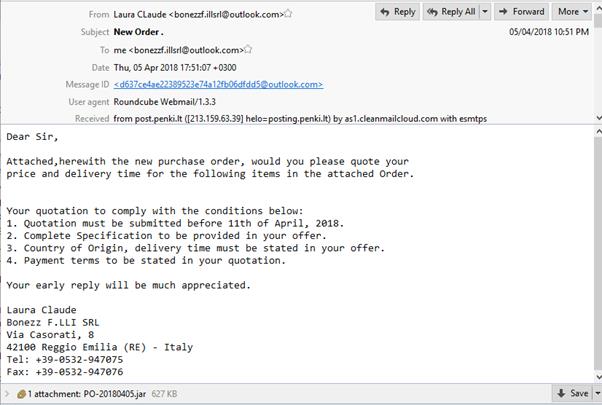
Adwind and DUNIHI
A variant of Adwind was also found in another malware bundle, but with DUNIHI. A JAR dropper (JAVA_JRAT.DRP) that ships a VBS dropper (VBS_JRAT.DRP) arrives via spam mail, and then the latter drops and executes both DUNIHI and Adwind. It is important to note that the VBS dropper checks if the affected system has the Java Runtime Environment (JRE) installed, and if not, it downloads and installs a JRE in the affected system. This eliminates the immunity point for Adwind since not having a JRE installed prevents Adwind from running.
Figure 4. Spam mail that carries Adwind and DUNIHI
Adwind has the same routine mentioned above, while DUNIHI has the following backdoor capabilities:
- Executing files
- Updating itself
- Uninstalling itself
- Downloading files
- Uploading files
- Enumerating drivers
- Enumerate files and folders
- Enumerating processes
- Executing Shell commands
- Deleting files and folders
- Terminating processes
- Sleeping
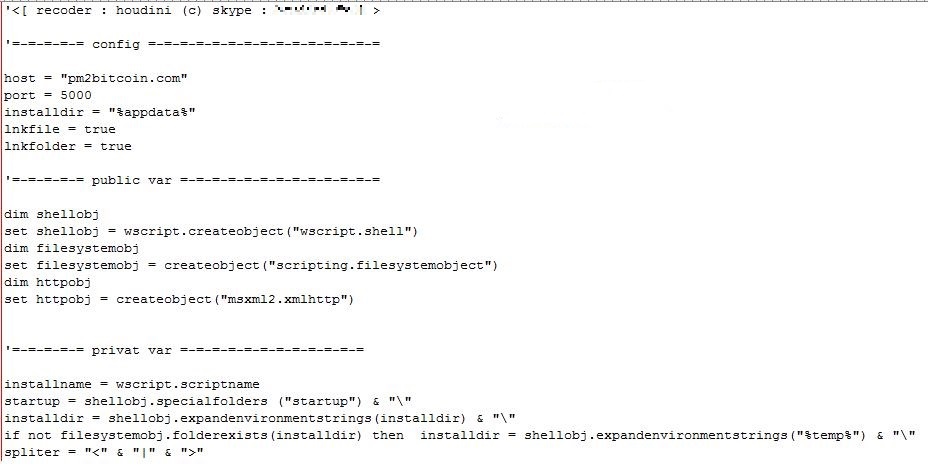
Figure 5. The decoded script of DUNIHI
DUNIHi connects to pm2bitcoin[.]com:62103, while the Adwind/jRAT variant that goes along with it connects to badnulls[.]hopto[.]org:3011.
Mitigation and solutions
A multilayered approach to security is needed to protect the gateway, endpoints, networks, servers, and mobile devices from cross-platform threats like Adwind, which is now being shipped alongside other malware by cybercriminals in an attempt to produce successful results. IT administrators should regularly keep networks and systems patched and updated.
Both variants of Adwind arrive via email, so it is imperative to secure the email gateway to mitigate threats that abuse email as an entry point to the system and network. Since social engineering is a crucial tool of the above-mentioned spam campaign/s, the workforce should have a security mindset to avoid falling for cybercriminal tricks. Businesses should commit to training employees, review company policies, and develop good security habits. Trend Micro offers a free phishing simulation and user training service to help employees be aware.
Businesses can also take advantage of Trend Micro™ endpoint solutions such as Trend Micro Smart Protection Suites and Worry-Free™ Business Security. Both solutions can protect users and businesses from threats by detecting malicious files, and spammed messages as well as blocking all related malicious URLs. Trend Micro Deep Discovery™ has an email inspection layer that can protect enterprises by detecting malicious attachment and URLs.
Trend Micro™ Email Security is a no-maintenance cloud solution that delivers continuously updated protection to stop spam, malware, spear phishing, ransomware, and advanced targeted attacks before they reach the network. It protects Microsoft Exchange, Microsoft Office 365, Google Apps, and other hosted and on-premises email solutions. Trend Micro™ OfficeScan™ with XGen™ endpoint security infuses high-fidelity machine learning with other detection technologies and global threat intelligence for comprehensive protection against advanced malware.
Indicators of Compromise (IoCs)
| SHA256s | Detection Names |
| 074a9e38883bf9cc0a951af0fd21052e2c85be4ff26ce213ad81e380c9c2377f | TSPY_HPLOKI.SM1 |
| 1add8a999e40c22b58ec1ac65c4a3dbdfcb163503e8cdcafbef5723f7b5293a1 | JAVA_JRAT.DRP |
| 1b39d9f79ef2bcbf55d3cbe8217c73077f2a8bf4b326263231bce96100fe3c19 | TSPY_HPLOKI.SM1 |
| 360bae0c2eb596e9030ea4d25567389c26805c4ae34073c9aba741d51ac0a0f6 | JAVA_ADWIND.WIL |
| 40c0532f5255e633a13dc4e5db9dda1be5a3733a152793e2d893ab8207c6acd6 | TROJ_CVE201711882.UHAOBGG |
| 7dd5566194b03b22df48af236193fb1853f6fd27205e31657440f640f85d4d76 | BKDR_XTRAT.SMM |
| ad043adce6ada399adab8fc3e767d8292284a8b926f0a33c398825738eacf018 | VBS_JRAT.DRP |
| c200fb4c0e20cf8f7e8ca58b7e8b71f5d967dc0a02938086679b9defa9171567 | VBS_DUNIHI.ELDSAVJ |
| d86fecb9ebf242dfedfbd8a062f67771c2250e542c5a6d25c9d596ad6d609793 | JAVA_ADWIND.WIL |
| C&C servers |
| badnulls[.]hopto[.]org:3011 |
| junpio70[.]hopto[.]org |
| pm2bitcoin[.]com:62103 |