Cybercriminals targeting gamers are nothing new. We’ve reported many similar incidents in the past, from fake game apps to real-money laundering through online game currencies. Usually the aim is simple: to steal personal information and monetize it. And usually, for that purpose the game itself is abused.
In the particular scenario we are describing in this blog post, however, it is not the game that is being abused by the cybercriminals, but rather one of the communication tools used by the game players. We’re referring to Discord, a new-generation chat platform that gamers frequently use, with a user base of more than 45 million registered members.
ROBLOX
This attack scenario involves ROBLOX, a highly popular massively multiplayer game with more than 178 million registered accounts and more than 12 million monthly active users. ROBLOX relies heavily on user-created content to thrive; it allows its players to create their own mini games and environments within the ROBLOX game world that other players can then play and share. ROBLOX also has a social networking element that encourages users to socialize, play and create content together, and take part in the earning and spending of ROBUX — the game’s own virtual currency that can be traded for real cash.
The Devious Vulnerability in Discord
How does Discord figure into the modus operandi of cybercriminals in attacking ROBLOX players? Through our research, we have discovered that cybercriminals are abusing a built-in feature of the chat platform — namely, its application programming interface (API), which enables it to run user-created code and apps. In doing so, cybercriminals can steal browser cookies containing ROBLOX login credentials from a targeted system that also uses Discord. More specifically, the feature being abused is the ability of Discord to use webhooks. A webhook, simply put, is a feature that allows the chat program to send a message to a specified channel or user when a certain requirement of a specified app or program is fulfilled. In this manner, Discord is really being used as an information exfiltration channel.
This particular abuse method using webhooks can be broken down into the following steps:
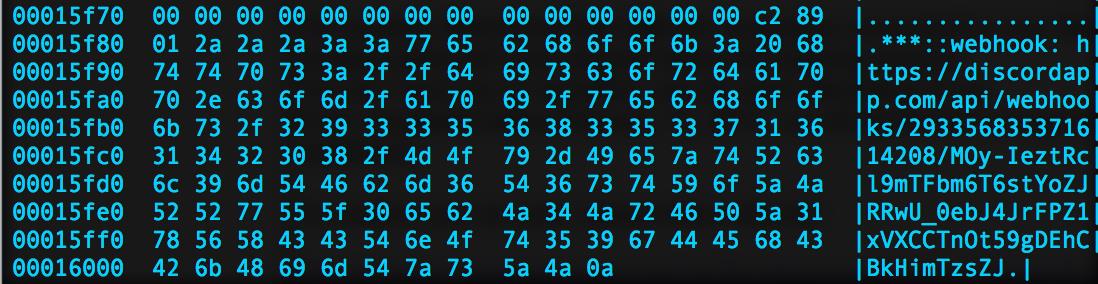
- The targeted system is infected with malware – in this case, one that Trend Micro detected as TSPY_RAPID.A. It was originally seen on a gaming forum, where the user who posted it claimed it was a “cheat application” that would allow players to modify their characters and therefore gain unfair advantage over other players. This malware has a Discord webhook coded into it, as shown below (SHA256: a983e78219bf3c711c21c7dc23f03dca621ed5861578a8848a954ad9ac9f20e5.)
Figure 1. Screenshot of malware code with Discord webhook appended at the end
- The malware waits until it detects ROBLOX in the victim system. Once it does, it steals the user’s game account cookie.
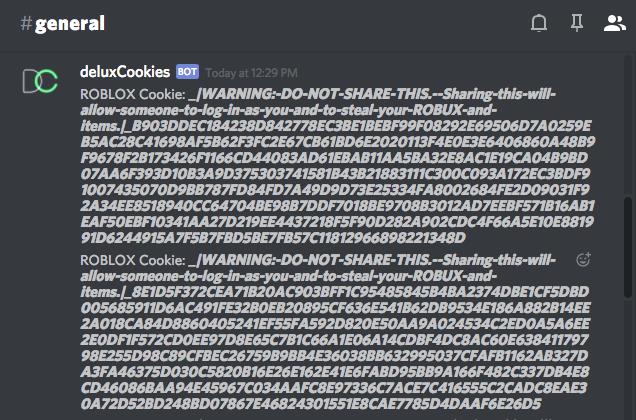
- The malware uses Discord to send the stolen cookie to a specified channel or user also connected to Discord.
- The stolen cookie is then used to log into the compromised ROBLOX account to steal the ROBUX stored within, presumably to be traded for real cash.
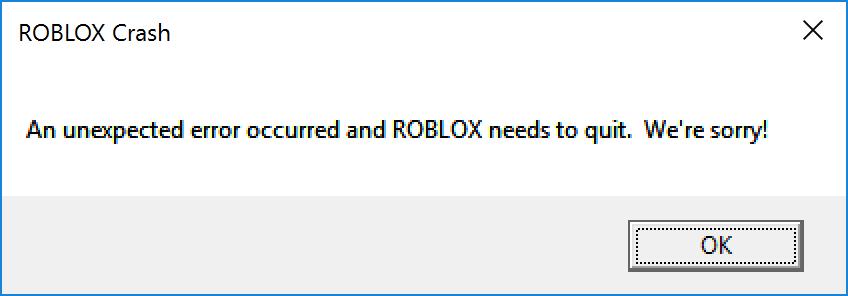
A variant of this malware, TSPY_RAPID.D, has been detected to run persistently on the affected system, making it possible to obtain new game account cookies whenever the system executes ROBLOX (and thus rendering password changes useless). This is in contrast to TSPY_RAPID.A, which runs only once. It also replaces the ROBLOX executable with a malicious version, just as it displays a fake message informing the victim that the ROBLOX process has crashed.
Figure 2. The fake ROBLOX crash notification message box
Figure 3. Screenshot of Stolen ROBLOX browser cookie
This isn’t the only malicious routine that cybercriminals can force Discord (or any similar chat platform) to carry out by abusing its API. In fact, our analysis shows that with only some modifications, creative cybercriminals can possibly turn it into a command-and-control (C&C) infrastructure, allowing them to communicate with their malware without having to expend the resources for a home-brewed alternative.
We detailed other examples and case studies of such abuse in Discord in our in-depth research paper on the matter, titled “How Cybercriminals Abuse Chat Program APIs as Command-and-Control Infrastructure.” Users can peruse the paper to know more about this particular security issue and to learn how to address it at home and in the workplace.
Solutions and Countermeasures
The significant catch about this particular security risk involving Discord is that there is no easy solution against it. Discord’s API feature is key to how the chat platform functions, and “sanitizing” it for the purpose of protection effectively kills its functionality, thereby rendering the app useless. This presents a scenario where the only time the user is made aware of the security issue is when the attack has already taken place, and the malware is already in the system using Discord as a C&C server. For this reason, users need to consider if continuing to use the chat platform is worth the risk.
The fact that cybercriminals are targeting players of specific games in gaming forums is something to take note of, as well.
To help make the chat platform safer, we have also worked extensively with Discord to identify and remove such threats lingering in its network.
Of course, a set of best practices should always be emphasized and adopted no matter what security issue is at hand. Here are our recommendations for users of Discord (and users of any chat platform, for that matter):
- Always keep a security solution installed and updated on your system to prevent malware infection, such as the pieces of malware cited here (TSPY_RAPID.A and TSPY_RAPID.D).
- Never click on suspicious links, even those sent by someone on your friends list.
- Never download any suspicious files, even those sent by someone on your friends list.
- Never reveal any personal information over the internet, even when you’re being asked by someone in your friends list.
- Always view messageboard posts, especially those asking you to try out cheat applications, with heavy skepticism.